운영 회복탄력성을 위한 자동화된 물리적 시스템 복구 | Cristie 사례 연구

Cristie 소프트웨어가 영국 글로벌 은행에 자동화된 물리적 시스템 복구를 제공한 방법 영국 은행, 자동화된 물리적 시스템 복구를 위해 Cristie 소프트웨어에 의존 영국의 선도적인 글로벌 은행은 재해 복구 준비 상태를 입증하고 엄격한 금융 규정을 준수해야 할 때 엔터프라이즈 규모의 운영 복원력을 위해 자동화된 물리적 시스템 복구를 구현하기 위해 Cristie 소프트웨어를 선택했습니다. 이 은행의 목표는 8,000개가 넘는 물리적 서버의 복구 시간을 며칠에서 단 몇 시간으로 단축하여 완전한 운영 회복탄력성을 달성하는 것이었습니다. 과제: 8,000대 이상의 물리적 서버에서 신속한 시스템 복구 보장 이 은행은 Windows 및 Linux 플랫폼을 아우르는 8,000대 이상의 물리적 서버에서 업계 규정을 충족하기 위해 시스템 복구 기능을 개선하고 입증해야 했습니다. 이전에는 며칠이 걸리던 이질적인 물리적 시스템의 방대한 복구를 단 몇 시간 내에 달성하는 것은 상당한 도전 과제였습니다. 금융 기관을 위한 대규모 자동화된 시스템 복구 금융 시스템은 상호 의존적인 서버 및 스토리지 구성이 복잡하며, 시스템 및 애플리케이션 소프트웨어의 수동 개입과 재설치 및 구성이 필요하기 때문에 대규모 물리적 시스템 복구가 어렵습니다. Cristie 복구 소프트웨어는 전체 프로세스를 완전히 자동화하여 물리적 시스템과 가상 머신으로 구성된 전체 시스템을 복구합니다. 이러한 수준의 복구 자동화는 DORA 및 SOX와 같은 규정 준수가 필수인 부문에서 매우 중요합니다. 다운타임 없는 검증된 복구: 금융 규정 준수 표준 충족 Cristie Software는 수천 개의 물리적 시스템을 병렬로 복구할 수 있는 기능을 제공하기 위해 Rubrik용 Cristie RBMR을 배포했습니다. 또한 시스템 복구는 다운타임 없이 실시간 뱅킹 서비스에 대한 간섭 없이 검증할 수 있습니다. 솔루션의 주요 기능 빠른 병렬 물리적 시스템 복구 자동화 운영 시스템에 영향을 주지 않는 복구 시뮬레이션 플랫폼에 구애받지 않는 범위(Windows, Linux, AIX, Solaris) 규정 준수를 위한 감사 준비 보고 "우리는 고객이 다운타임 없이 8,000개가 넘는 시스템의 복구 가능성을 검증할 수 있도록 지원했습니다. Cristie확장성과 신뢰성에 대한 진정한 증거였습니다."- Cristie 프로젝트 책임자 Cristie RBMR: 복구 보증을 위한 Rubrik과의 원활한 통합 Cristie 복구 소프트웨어는 주요 백업 솔루션과 원활하게 통합되어 운영 체제, 애플리케이션, 사용자 구성 및 데이터를 사용 가능한 모든 복구 시점으로 쉽게 복구할 수 있도록 지원합니다. 추가적인 인프라나 관리가 필요하지 않으며, 모든 복구 작업을 Cristie VA 콘솔을 통해 구성하고 제어할 수 있습니다. Cristie Recovery는 Rubrik, Cohesity, IBM, Dell Technologies의 백업 솔루션과 원활하게 통합됩니다. Cristie 복구는 독립형 백업 및 복구 솔루션으로도 작동할 수 있습니다. 결과: 은행권의 규제 준비 및 운영 복원력 성공적인 구축으로 측정 가능한 이점을 얻었습니다: 물리적 시스템의 복구 워크플로 간소화 다운타임 없이 전체 복구 검증 완료 감사 준비 문서로 규정 준수 태세 강화 치명적인 장애를 견디고 복구하는 검증된 기능 글로벌 운영 전반에서 비즈니스 연속성을 보장하는 안심할 수 있는 기능 금융 부문에서 자동화된 물리적 복구가 중요한 이유 금융 부문에서는 운영 복원력이 필수적입니다. DORA, SOX, PRA/FRA와 같은 규제 프레임워크는 입증 가능한 재해 복구 계획을 요구합니다. Cristie 통해 은행은 이제 내부 위험 표준과 외부 규정 준수 감사를 모두 충족하는 신뢰할 수 있는 솔루션을 갖추게 되었습니다. Cristie 소프트웨어: 규제 산업을 위한 검증된 복구 이 사례는 플랫폼에 구애받지 않는 대규모 시스템 복구 및 복구 검증을 원활하고 안전하게 제공하는 Cristie능력을 보여줍니다. 운영 복원력이 필요한 모든 금융 기관 또는 기타 산업을 위해 Cristie Software는 신뢰할 수 있는 검증된 복구를 제공합니다. 재해 복구 계획 감사를 받을 준비가 되었나요? Cristie자동화된 물리적 시스템 복구가 금융 기관이 규정 준수 요건을 충족하고 자신 있게 복구하는 데 어떻게 도움이 되는지 알아보세요. Cristie 복구 제품군을 살펴보거나 맞춤형 데모를 요청하세요. 조직 내 시스템 복구 및 복제를 개선하거나 시스템 복제 및 IBM, Dell Technologies, Rubrik, Cohesity를 비롯한 주요 공급업체의 백업 솔루션과의 시스템 복구 통합에 대해 자세히 알아보려면 Cristie 소프트웨어 팀에 문의하세요. 마지막으로 사용 사례 페이지에서 더 많은 기업이 시스템 복구를 현대화하는 데 어떻게 도움을 주고 있는지 알아보세요.
시스템 복구 동향: 새로운 기술 및 혁신

System Recovery Trends: Emerging Technologies and Innovations In today’s rapidly evolving digital landscape, the stakes for data protection and system recovery have never been higher. As organizations face increasing cyber threats, hardware failures, and human errors, the need for robust and automated system recovery solutions has become paramount. But what does the future hold for system recovery, and how is Cristie Software paving the way for innovation? In this article, we’ll explore system recovery trends shaping the future of disaster recovery and highlight how Cristie Software’s cutting-edge solutions are empowering businesses to stay resilient. 1. The Rise of AI and Machine Learning in Automated Recovery Solutions Artificial intelligence (AI) and machine learning (ML) are transforming the way recovery solutions operate. By analyzing patterns of failures and predicting potential risks, AI-driven tools can preemptively address vulnerabilities before they lead to downtime. Cristie Software integrates intelligent automation into its solutions, enabling proactive automated system recovery that streamlines complex recovery workflows. This innovation reduces the margin for error and speeds up the recovery process. Key Benefits of AI-Powered Recovery Solutions: Predictive Recovery: Early detection of system anomalies including potential malware. Self-Healing Systems: Automated response protocols to fix issues. Faster Recovery Times: Reduced reliance on manual intervention. Cristie Software’s Innovation: Cristie Software harnesses AI to enhance its recovery solutions with predictive analytics and intelligent decision-making capabilities. The platform continually learns from historical recovery scenarios, optimizing future processes. By integrating advanced automation tools and ML-driven workflows, Cristie’s solutions not only identify vulnerabilities but also take proactive measures to mitigate potential failures. 2. Cloud-Native and Hybrid Recovery Models The future of system recovery is closely linked to the rise of cloud-native and hybrid environments. Organizations are increasingly adopting hybrid IT strategies to ensure flexibility and scalability. Cristie Software’s solutions support seamless recovery across on-premises, cloud, and hybrid infrastructures. Whether recovering critical workloads from a private data center or restoring systems in the cloud, Cristie’s technology ensures consistent, secure, and efficient recovery processes. Emerging Trends in Cloud-Based Recovery: Multi-Cloud Resilience: Support for multiple cloud service providers. Cloud Automation: Orchestration tools to automate failover and failback. Disaster Recovery as a Service (DRaaS): Scalable recovery services for greater agility. Cristie Software’s Innovation: Cristie Software provides cloud-optimized recovery solutions that integrate seamlessly with leading cloud providers, ensuring rapid recovery regardless of the deployment environment. By leveraging advanced orchestration, Cristie’s technology enables smooth transitions between on-premises and cloud resources, allowing organizations to implement hybrid recovery strategies without compromising performance or security. 3. Bare-Metal Recovery for Diverse Platforms As IT environments grow more diverse, encompassing physical, virtual, and cloud-native systems, the demand for platform-agnostic bare-metal recovery solutions is rising. Key Advancements: Support for dissimilar hardware recovery. Integration with containerized and microservices-based environments. Cristie Software’s Innovation: Cristie Software’s BMR (Bare Machine Recovery) supports full system recovery across physical, virtual, and cloud platforms, ensuring hardware-independent restorations and compatibility with evolving infrastructure. 4. Real-Time System Replication and Continuous Data Protection (CDP) Organizations are moving from traditional backup schedules to continuous data protection (CDP) to minimize Recovery Point Objectives (RPOs) and ensure that data loss is virtually eliminated. Key Advancements: Continuous system snapshots to maintain up-to-date replicas. Real-time replication to ensure synchronized recovery points. Cristie Software’s Innovation: With CloneManager, Cristie enables real-time replication of systems, allowing businesses to maintain consistent recovery points and quickly fail over to backup systems during disruptions. 5. Recovery Solutions Tailored for Compliance and Regulation Regulatory frameworks like GDPR, DORA, SOX, HIPAA, and NIST mandate stringent data protection and recovery practices. As regulations evolve, system recovery solutions must adapt to ensure compliance without sacrificing performance. Cristie Software provides comprehensive audit trails and reporting features to support regulatory compliance. Its automated system recovery solutions are designed to meet the needs of highly regulated industries, ensuring that recovery processes align with legal and industry standards. Key Compliance Features: Automated Documentation: Detailed recovery logs for compliance reporting. Data Sovereignty: Control over where recovery data is stored. Testing and Validation: Regular, automated recovery tests to ensure preparedness. Cristie Software’s Innovation: Cristie Software’s compliance-focused solutions simplify regulatory adherence by automating recovery documentation and validation processes. Detailed logs and audit trails provide visibility into every recovery event, supporting compliance reporting with minimal effort. Furthermore, Cristie’s solutions include customizable testing schedules to ensure that recovery plans remain effective and compliant. 6. Disaster Recovery as a Service (DRaaS) The rise of DRaaS is reshaping how businesses approach disaster recovery. DRaaS offers a cost-effective, subscription-based model that offloads the complexity of maintaining recovery infrastructure. Key Advancements: On-demand system recovery services. Reduced capital expenses and simplified DR operations. Cristie Software’s Innovation: Cristie’s solutions integrate seamlessly with managed service providers, enabling organizations to leverage DRaaS capabilities for flexible, scalable disaster recovery options. 7. Cybersecurity-Driven Recovery Strategies Cyberattacks, particularly ransomware, have highlighted the importance of recovery solutions that are not just fast but secure. The next wave of innovation in system recovery focuses on integrating robust security protocols directly into recovery plans. Cristie Software’s solutions prioritize cyber-resilient recovery, with secure automated system recovery workflows that ensure minimal risk of reinfection during restoration. By combining encryption, multi-factor authentication (MFA), and tamper-proof recovery points, Cristie helps organizations bounce back from cyber incidents with confidence. Security-Focused Recovery Features: Immutable Backups: Prevent unauthorized changes to backup data. Zero-Trust Architecture: Verify every recovery action to mitigate insider threats. Ransomware Rollback: Rapid recovery to pre-attack states. Cristie Software’s Innovation: Cristie Software integrates end-to-end security measures into every stage of the recovery process. From encrypted backups to automated validation protocols, Cristie ensures that recovery workflows meet zero-trust standards. Additionally, Cristie’s solutions provide automated ransomware detection features, enabling businesses to recover quickly and securely from even the most sophisticated cyberattacks. 8. Faster Recovery Through Automation and Orchestration The demand for faster recovery times is driving the adoption of advanced automation and orchestration platforms. Manual recovery processes are slow, error-prone, and resource-intensive, making them unsuitable for modern enterprises. Cristie Software has long been at the forefront of automated system recovery, offering solutions that reduce downtime
2025년에 기업이 사이버 보안 태세를 개선할 수 있는 방법: 2024년 트렌드에서 얻은 인사이트

How Businesses Can Improve Their Cybersecurity Posture in 2025: Insights from 2024 Trends In an increasingly interconnected world, improving cybersecurity remains a critical priority for businesses of all sizes. The year 2024 has seen a surge in cyberattacks, with threat actors leveraging more sophisticated methods to exploit vulnerabilities. As we look to 2025, it’s clear that a proactive and adaptive approach to improving cybersecurity is essential. Drawing from 2024 trends, this article explores key recommendations for improving cybersecurity posture in the year ahead. 1.Improving cybersecurity with AI-Driven Threat Detection During 2024, AI-driven cyberattacks became more prevalent, with adversaries using AI to craft more convincing phishing attempts and automate attacks at scale. Businesses can fight fire with fire by adopting AI-driven threat detection tools. These systems analyze vast datasets in real-time, identifying anomalies that may signal a breach. Recommendation:• Invest in AI-powered security platforms which provide real-time detection and automated responses. Cristie Software included Advanced Anomaly Detection driven by machine learning (ML) algorithms. This can be run at any time to compare snapshots of system backups to detect and provide early warning of suspicious file encryption.• Ensure staff receive training to understand and operate these systems effectively. 2024 Insight: According to a report by Gartner, AI-driven security solutions have reduced threat response times by up to 60%. 2. Zero Trust Architecture (ZTA) Implementation “Trust no one” became a fundamental principle for improving cybersecurity in 2024. The Zero Trust model verifies every user and device attempting to access a network, reducing the risk of insider threats and compromised credentials. Recommendation:• Adopt Zero Trust principles by segmenting networks, enforcing multi-factor authentication (MFA), and continually verifying user identity.• Utilize solutions like Microsoft’s Zero Trust framework and tools from companies like Zscaler and Okta. 2024 Insight: In a survey by Forrester, organizations that implemented ZTA reported a 45% reduction in security incidents. 3. Strengthen Endpoint Security with Extended Detection and Response (XDR) Endpoints (laptops, mobile devices, and IoT devices) remain one of the primary targets for attackers. In 2024, the integration of Extended Detection and Response (XDR) tools helped consolidate endpoint, network, and server security into a single cohesive system for improving cybersecurity. Recommendation:• Deploy XDR solutions like SentinelOne, Sophos, or Trend Micro to achieve unified threat detection and response.• Regularly update endpoint security protocols and conduct frequent security audits.• Incorporate system recovery solutions from Cristie Software to ensure quick recovery from endpoint failures or cyber incidents, minimizing downtime and data loss. 2024 Insight: IBM Security’s X-Force Threat Intelligence Index indicated that endpoint-related breaches accounted for 48% of all incidents in 2024. 4. Focus on Awareness Training to Improve Cybersecurity Human error remains one of the leading causes of security breaches. In 2024, phishing and social engineering attacks increased by 30%, underscoring the need for robust employee training to improve cybersecurity awareness. Recommendation:• Conduct regular cybersecurity awareness training sessions to help employees recognize phishing attempts, ransomware, and social engineering tactics.• Use platforms like KnowBe4 or Proofpoint for simulated phishing campaigns and educational modules. 2024 Insight: A Verizon Data Breach Investigations Report found that 68% of breaches involved a non-malicious human element, like a person falling victim to a social engineering attack or making an error. 5. Adopt Continuous Monitoring and Incident Response Plans Continuous monitoring of your IT environment ensures that threats are detected early. An effective Incident Response (IR) plan ensures quick action when breaches occur, improving cybersecurity resilience. Recommendation:• Implement 24/7 Security Operations Center (SOC) monitoring through in-house teams or Managed Security Service Providers (MSSPs) like Arctic Wolf and Rapid7.• Develop a comprehensive IR plan and conduct regular tabletop exercises to ensure readiness.• Utilize Cristie Software’s system recovery solutions to enable swift recovery in the aftermath of a cyber incident. The simulated recovery feature of our software enables organizations to ensure correct functionality of their recovery jobs without interrupting ongoing protection. In addition, our isolated network recovery mechanism allows systems to be recovered into a cleanroom environment for cyber forensics and integrity verification following an attack. 2024 Insight: Companies with well-documented IR plans reduced breach recovery times by 35%, according to a Ponemon Institute study. 6. Enhance Cloud Security Measures With cloud adoption increasing, cloud security breaches in 2024 highlighted the importance of improving cybersecurity measures for data stored in cloud environments. Recommendation:• Use cloud security solutions such as those offered by AWS, Microsoft Azure, and Google Cloud Platform (GCP) to enforce strong access controls, encryption, and threat detection.• Ensure compliance with frameworks like the Cloud Security Alliance (CSA) Cloud Controls Matrix.• Integrate Cristie Software’s recovery solutions to ensure cloud workloads can be restored quickly in the event of data loss or a breach. Our recovery and replication software provides the capability to recovery or replicate system to a variety of cloud platforms. CloneManager our replication software provides a simple way to automate and accelerate cloud onboarding or to utilize the cloud as a failover target. 2024 Insight: According to Cloud Security Alliance’s 2024 report, 67% of cloud security breaches were caused by misconfigurations. 7. Regularly Update and Patch Systems Unpatched vulnerabilities remain a favorite entry point for cybercriminals. In 2024, attacks exploiting known vulnerabilities increased dramatically, emphasizing the importance of improving cybersecurity through timely updates. Recommendation:• Implement an automated patch management system.• Prioritize patching critical vulnerabilities and ensure all software and firmware are up-to-date.• Consider using Cristie Software’s system recovery solutions to quickly revert to secure states in case of a compromised patch. 2024 Insight: CISA’s Known Exploited Vulnerabilities Catalog reported a 52% rise in attacks targeting unpatched systems in 2024. Conclusion As we move into 2025, businesses must adapt to an evolving threat landscape shaped by the trends of 2024. By investing in AI-driven detection, implementing Zero Trust, enhancing endpoint security, and prioritizing cybersecurity awareness, organizations can focus on improving cybersecurity posture. Incorporating system recovery solutions from Cristie Software ensures businesses can recover swiftly and efficiently from potential cyber incidents. Proactive measures and continuous improvement will be key to protecting assets, maintaining customer trust, and ensuring business continuity in the
자동화된 시스템 복구의 중요성 응집력 보고서가 뒷받침하는 인사이트
The Importance of Automated System Recovery: Insights Backed by the 2024 Cohesity Global Cyber Resilience Report In today’s increasingly hostile cyber landscape, the ability to quickly recover systems after an attack or failure is more crucial than ever. Subsequently Automated system recovery is not just a convenience—it’s a necessity for maintaining business continuity, minimizing downtime, and protecting critical data. At Cristie Software, we understand that fast, reliable system recovery can mean the difference between a minor disruption and a catastrophic business failure. Recent reports from Cohesity highlight the rising challenges organizations face in managing system recovery after a cyber incident. These insights underline why automation is key to ensuring resilience and recovery readiness. Therefore let’s explore the importance of automated system recovery and how it can protect your business from costly disruptions. The Growing Threat of Cyberattacks and Downtime According to the 2024 Cohesity Global Cyber Resilience Report, an alarming 67% of organizations have experienced ransomware attacks in the past year. More troubling is the fact that many of these organizations struggle to recover efficiently after such incidents. Recovery delays can result in: • Prolonged Downtime: Businesses can take anywhere from 1 to 3 days or more to fully recover operations, leading to financial losses and reputational damage. • Data Loss: Inefficient recovery processes can lead to incomplete restoration, resulting in lost data that can be critical for operations. • Increased Costs: The longer the downtime, the higher the cost. Accordingly the report estimates that downtime can cost enterprises thousands of dollars per minute. This underscores the need for a robust, automated system recovery solution that can restore operations quickly and accurately, mitigating these risks. Why Manual Recovery Processes Are No Longer Viable Traditional, manual recovery processes are time-consuming, error-prone, and often incapable of meeting the demands of modern IT environments. Manual recovery typically involves: 1. Locating and Validating Backups: Ensuring that the backups are current, uncorrupted, and usable. 2. Manual Reconfiguration: Rebuilding servers, re-installing operating systems, and reconfiguring applications. 3. Coordination Challenges: Synchronizing various teams to execute recovery steps in the correct sequence. Cohesity’s research shows that 78% of IT professionals believe that manual recovery processes are a major bottleneck during disaster recovery. In an environment where every second counts, manual methods simply cannot keep up. The Benefits of Automated System Recovery Automated system recovery provides a streamlined, reliable, and efficient solution to these challenges. Here’s why automation is critical: 1. Speed and Efficiency When recovery processes are automated recovery times can be reduced from hours or days to mere minutes. By leveraging tools that automate the restoration of systems, applications, and configurations, businesses can resume operations faster, minimizing the impact of downtime. 2. Accuracy and Consistency Automation eliminates human error by following pre-defined recovery workflows. Each step of the recovery process is executed consistently, ensuring that systems are restored accurately every time. 3. Regular Testing and Validation Cristie Software automated recovery solutions allow for regular testing without disrupting production systems. Consequently this ensures that your recovery plans are always up-to-date and ready for deployment. Cohesity’s reports emphasize the importance of frequent testing to maintain recovery readiness. 4. Scalability As IT environments grow more complex, automated recovery solutions can scale to handle multiple systems simultaneously, whether on-premises, in the cloud, or in hybrid environments. This ensures comprehensive protection regardless of infrastructure size. 5. Reduced Costs By minimizing downtime and the resources needed for manual intervention, automated recovery reduces the overall cost of system recovery. Faster recovery means fewer losses and lower risk of compliance penalties. How Cristie Software Delivers Automated System Recovery We provide advanced recovery solutions designed to meet the needs of modern businesses. Our automated system recovery tools offer: • Bare Metal Recovery: Recover entire systems, including operating systems, applications, and configurations, directly to new hardware or virtual environments. Our Bare Metal recovery for Cohesity (CoBMR) works seamlessly to provide automated recovery for any machine within Cohesity Data Protect. • Cross-Platform Compatibility: Support for physical, virtual, and cloud-based infrastructures. • Regular Testing and Validation: Automated testing capabilities ensure your recovery plans are always ready for deployment. • Integration with Leading Data Management Solutions: Our solutions seamlessly integrate with platforms like Cohesity to enhance your overall cyber resilience. Cohesity’s Insights: The Need for Resilient Automated System Recovery The research from Cohesity paints a clear picture: cyber threats are not going away, and businesses must be prepared to respond effectively. Automated system recovery is a cornerstone of resilience, enabling organizations to recover faster, reduce errors, and maintain business continuity. By combining Cristie Software’s automated recovery solutions with robust data protection platforms like Cohesity, businesses can achieve a comprehensive defense strategy that ensures they can recover swiftly from any incident. Conclusion In conclusion, backups are essential, but without automated system recovery, they fall short of providing true business resilience. As cyber threats grow more sophisticated and downtime becomes more costly, automation is no longer optional—it’s a necessity. At Cristie Software, we’re committed to helping businesses safeguard their critical systems and data with automated recovery solutions that work when you need them most. Don’t leave your recovery to chance. Learn how Cristie Software can enhance your resilience by visiting www.cristie.com/solutions/ today. Be resilient. Be ready. Automate your recovery. Contact the Cristie Software team if you are looking to improve system recovery and replication within your organization, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity. Finally, learn how we are helping companies modernize system recovery in our Use Case pages.
시스템 복구 실패의 주요 원인 5가지와 이를 방지하는 방법
The Top 5 Causes of System Recovery Failure and How to Avoid Them In today’s always-on business environment, system recovery is more than just a technical safeguard, it’s a critical component of business continuity. When a system recovery plan fails, the consequences can include extended downtime, lost revenue, and damaged reputation. At Cristie Software, we specialize in providing advanced recovery solutions that minimize these risks. To help you strengthen your recovery strategy, let’s examine the top five causes of system recovery failure and how to address them effectively. 1. Lack of Regular System Recovery Testing The most common reason for system recovery failure is insufficient testing. Even a meticulously designed recovery plan can fall short if it hasn’t been tested under realistic conditions. Without testing, unforeseen issues, such as misconfigured backups or incompatible systems, often remain undetected. How to Avoid This: • Test Regularly: Schedule routine recovery drills to ensure that your system recovery plan is functional and up-to-date.• Simulate Real-World Scenarios: Use tools like Cristie Software’s recovery testing solutions to simulate disaster events and verify system behavior.• Document Results: Record the outcomes of tests to identify weak points and fine-tune the recovery process. 2. Outdated System Recovery Plans A system recovery plan that doesn’t account for changes in IT infrastructure or business operations is a recipe for failure. Many organizations fail to update their recovery plans after implementing new software, expanding storage capacities, or adopting hybrid cloud environments. How to Avoid This: • Establish a Review Schedule: Update your system recovery plan whenever there’s a significant change in your IT environment.• Centralize Documentation: Use Cristie’s solutions to automate system recovery and centralize the documentation of system configurations, ensuring alignment with the latest setup.• Assign Ownership: Designate a recovery team responsible for maintaining and updating the plan. 3. Incomplete or Corrupt System Backups System recovery depends on the availability of accurate and complete backups. Partial backups or data corruption during the backup process can make recovery impossible, leading to prolonged downtime and data loss. How to Avoid This: • Automate Backups: Leverage automated backup tools that ensure consistency and completeness across all systems.• Use Backup Validation: Cristie’s solutions offer system recovery simulation to confirm that data is intact and accessible before an issue arises.• Adopt Redundancy: Store backups across multiple locations, including offsite and cloud-based storage, to mitigate risks. The 3-2-1 backup rule is a widely recognized data protection strategy that recommends maintaining three copies of your data: the original and two backups. These copies should be stored on two different types of media, with one copy kept off-site to safeguard against data loss due to hardware failures, cyberattacks, or natural disasters 4. Hardware and Software Incompatibility When recovering systems, hardware and software incompatibilities can create bottlenecks. For example, legacy recovery tools may struggle with modern IT environments, causing delays or outright failures. Problems very often arise when recovering to dissimilar hardware due to device driver incompatibilities. Cristie Software system recovery tools can overcome this issue with Dissimilar Hardware Technology that can automatically insert missing or alternative device drivers during the recovery process, eliminating the need for manual intervention. How to Avoid This: • Upgrade Tools Regularly: Use Cristie’s state-of-the-art recovery solutions, which are designed to handle modern, hybrid, and legacy systems seamlessly.• Standardize Your Environment: Reduce variability by standardizing hardware and software configurations wherever possible.• Test Compatibility: Test your recovery tools with existing and updated systems to avoid surprises during critical recovery operations. 5. Human Error Leading to System Recovery Failure Even the most robust recovery plans can be derailed by human error. Missteps such as skipping critical steps, applying incorrect configurations, or misunderstanding recovery procedures can result in significant delays. How to Avoid This: • Provide Training: Ensure that your IT staff is trained in executing the system recovery plan effectively.• Create Step-by-Step Guides: Use Cristie’s tools to generate clear and automated recovery workflows, minimizing reliance on manual input.• Embrace Automation: Cristie Software recovery tools can automate repetitive recovery tasks to reduce the risk of mistakes and accelerate recovery times. For more complex recovery workflows our software offers recovery orchestration which allows specific recovery tasks to be defined and processed in a user defined sequence. How Cristie Software Enhances System Recovery At Cristie Software, we understand the complexities of system recovery and have built our solutions to help businesses avoid the pitfalls that lead to recovery failures. Our tools focus on: • Rapid Recovery: Minimize downtime with solutions that restore systems in minutes, not hours.• Comprehensive Testing: Simulate recovery scenarios to validate your plan without disrupting daily operations.• Cross-Platform Compatibility: Seamlessly recover systems across diverse IT environments, including physical, virtual, and cloud. Whether you’re recovering a single server or an entire data center, Cristie Software provides the confidence and reliability you need to protect your business. Conclusion Avoiding system recovery failures requires proactive planning, regular testing, and the right tools. By addressing common pitfalls such as outdated plans, incomplete backups, and human error, businesses can ensure resilience and continuity in the face of disruptions. At Cristie Software, we’re here to help you build and maintain a recovery strategy that works when you need it most. Learn more about our advanced recovery solutions by visiting www.cristie.com/solutions/ Secure your business, minimize downtime, and ensure operational continuity with Cristie Software. Contact the Cristie Software team if you are looking to improve system recovery and replication within your organization, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity. Learn how we are helping companies modernize system recovery in our Use Case pages.
미국 제약업계의 사이버 범죄 규모

미국 제약 업계의 사이버 범죄 규모 제약 업계의 사이버 범죄는 고가의 지적 재산(IP), 민감한 환자 데이터, 의료 서비스에서 필수적인 역할로 인해 미국에서 매우 두드러지게 나타나고 있습니다. 몇 가지 주요 요인과 사건에서 알 수 있듯이 이 분야에서 사이버 범죄의 규모는 상당합니다: 제약 및 의료 분야에서 사이버 공격의 만연 높은 침해 발생률: 보고서에 따르면 미국 제약 회사 전반에서 데이터 유출이 눈에 띄게 증가한 것으로 나타났습니다. 민감한 데이터 노출은 악의적인 사이버 공격과 우발적인 유출 모두와 연관되어 있으며, 종종 상당한 규제 조사와 벌금으로 이어지기도 합니다. IBM Security의 2024 데이터 유출 비용 보고서는 데이터 유출이 의료 및 제약 등 산업에 미치는 재정적 영향을 강조하며, 미국 의료 및 제약 부문은 유출 건당 비용이 가장 높은 산업으로 각각 1위와 6위를 차지했습니다. (IBM 데이터 유출로 인한 2024년 비용 보고서 읽기) 광범위한 취약성: 2021년 Reposify의 조사에 따르면 조사 대상 제약 기업의 92%가 적어도 하나의 데이터베이스가 노출되어 있었고, 99%는 적어도 하나의 원격 액세스 플랫폼이 인터넷에 노출되어 있어 심각한 취약점을 가지고 있는 것으로 나타났습니다. 제약 회사에 대한 사이버 위협의 유형 지적 재산 도난: 연구 개발에 막대한 투자를 하는 미국 제약 회사는 독점적인 의약품 공식, 임상시험 데이터 및 연구를 훔치려는 사이버 범죄자들의 표적이 되는 경우가 많습니다. 이러한 IP 도난은 심각한 재정적 손실과 경쟁 우위 약화로 이어질 수 있습니다. 랜섬웨어 공격: 이러한 유형의 공격은 특히 미국에서 우려스러운데, 주요 제약회사를 표적으로 삼아 필수 데이터를 암호화하고 해제를 위해 금전을 요구하는 랜섬웨어 사고가 발생하여 운영에 차질을 빚고 있습니다. 피싱 및 소셜 엔지니어링: 사이버 범죄자들이 기밀 시스템과 데이터에 무단으로 액세스하기 위해 사용하는 소셜 엔지니어링 공격의 피해자는 미국에 본사를 둔 제약 회사의 많은 직원들입니다. 사이버 범죄가 제약 부문에 미치는 재정적 영향 침해로 인한 높은 비용: 미국 제약업계의 데이터 유출로 인한 평균 비용은 모든 업계 중 가장 높은 수준이며, 500만 달러를 초과하는 경우가 많습니다. 신속한 대응과 복구의 필요성은 특히 임상시험과 의약품 승인에 적극적으로 관여하는 기업의 경우 재정적 압박을 가중시킵니다. 미국 제약 부문에서 주목할 만한 사이버 보안 사고 머크에 대한 낫페트야 공격(2017): 이 랜섬웨어 공격은 미국의 주요 제약 회사인 Merck에 막대한 영향을 미쳐 운영 중단과 약 8억 7천만 달러로 추정되는 금전적 손실을 초래했습니다. 이 공격은 Merck의 생산 및 유통 역량에 영향을 미쳤으며, 대규모 사이버 장애에 대한 이 분야의 취약성을 강조했습니다. 화이자 및 모더나 피싱 공격(2020년): 코로나19 백신 개발 기간 동안 미국 제약업계의 두 주요 기업인 화이자와 모더나가 피싱 공격과 침해 시도의 표적이 되었습니다. 이러한 공격은 백신 관련 데이터를 손상시키는 것을 목표로 했으며, 이는 중요하고 시간에 민감한 연구에 대한 위험성을 강조합니다. 미국 제약 분야의 사이버 범죄 발생 요인 디지털 혁신: 디지털 시스템으로의 전환과 미국 제약 회사 내 상호 연결성 증가로 인해 공격 표면이 확장되어 사이버 위협의 진입 지점이 더 많아졌습니다. 써드파티 위험: 써드파티 공급업체 및 공급망 파트너에 대한 의존도는 취약성을 초래할 수 있습니다. 예를 들어, 미국에 기반을 둔 공급업체에 대한 공격은 제약회사 운영에 간접적으로 영향을 미쳤습니다. 규제 과제: 미국 제약 회사는 HIPAA와 같이 진화하는 여러 사이버 보안 및 개인정보 보호 규정을 준수해야 합니다. 규정을 위반하거나 위반할 경우 벌금이 부과되고 사이버 공격에 대한 취약성이 높아질 수 있습니다. 이전 글에서 이 규정의 적용을 받는 기업의 시스템 복구 요건을 구체적으로 자세히 설명하는 HIPPA의 섹션을 강조했습니다. 결론 요약하면, 미국에 기반을 둔 제약 회사는 사이버 범죄로 인한 높은 위험에 직면해 있습니다. 이러한 위협을 해결하기 위해서는 엄격한 사이버 보안 조치를 구현하고 시스템 복구 솔루션의 현대화를 통해 민감한 데이터를 보호하고 운영 연속성을 보장하며 공중 보건을 보호해야 합니다. 제약 및 의료 분야에서 시스템 복구 및 복제를 개선하거나 시스템 복제 및 IBM, Dell Technologies, Rubrik, Cohesity 등 주요 공급업체의 백업 솔루션과의 시스템 복구 통합에 대해 자세히 알아보려면 Cristie 소프트웨어 팀에 문의하세요. 사용 사례 페이지에서 제약 및 헬스케어 기업의 시스템 복구 현대화를 어떻게 지원하고 있는지 알아보세요.
커넥티드 제조의 새로운 위협

Manufacturing is facing a new era of cybercrime Ransomware in manufacturing is rising fast. Manufacturing companies face a growing array of challenges related to cybercrime, largely due to the evolving nature of their IT systems and their reliance on operational technology (OT). These challenges stem from the convergence of IT and OT environments, the complexity of supply chains, and the shift towards more digital and connected manufacturing processes (Industry 4.0). In many cases, there is a need for modernization of system recovery and data protection technologies to combat threats that have emerged for a more connected OT environment. Below are some key challenges: 1. Convergence of IT and OT IT/OT Integration: In modern manufacturing, IT systems (information technology) handle business functions like finance, inventory, and communications, while OT (operational technology) systems control physical processes such as machinery, robotics, and production lines. These two environments are increasingly integrated for improved efficiency, but they have different security requirements. OT systems are often older and not designed with cybersecurity in mind, making them vulnerable when connected to the broader IT network. Extended Lifecycle OT Systems: Many manufacturing plants use equipment with extended lifecycles that cannot be easily updated or patched. These systems, while operationally critical, were often designed without consideration for modern cyber threats, leading to vulnerabilities. Cristie Software system recovery provides support for legacy operating systems including Windows 7 desktop systems and Windows Server 2008 R2 enterprise platforms. Microsoft’s virtualization platform Hyper-V is supported from Hyper-V 2012 plus all editions of Microsoft Azure and Microsoft Azure Stack HCI. Cristie Software system recovery and replication solutions for Red Hat Linux platforms cater for the very latest editions with support extending back to Red Hat Enterprise Linux 5. 2. Ransomware and Disruptions to Production Ransomware Attacks: Ransomware has become a major threat to manufacturers. Attackers can lock down critical systems or encrypt data, halting production processes and causing significant financial losses. For instance, if a ransomware attack disables a factory’s production control systems, it could lead to downtime, missed deadlines, and reputational damage. Production Downtime: Even brief production stoppages can have a large financial impact, particularly in industries where just-in-time (JIT) manufacturing is crucial. Cyberattacks that disrupt OT systems can lead to costly downtime as plants scramble to restore operations. 3. Supply Chain Vulnerabilities Third-Party Risk: Manufacturing companies often rely on extensive global supply chains, working with multiple suppliers and contractors. These third-party relationships can introduce vulnerabilities, as cybercriminals may target less secure suppliers to gain access to larger manufacturers. The attack on Target in 2013, for example, occurred when hackers accessed the company’s systems through a third-party HVAC vendor. Supply Chain Attacks: Cybercriminals may inject malware into software or hardware components within the supply chain, compromising the final product delivered to customers. Supply chain attacks are difficult to detect and can propagate through an entire ecosystem of partners. 4. Intellectual Property Theft Targeting Trade Secrets: Manufacturing companies often possess valuable intellectual property (IP), including patents, product designs, and proprietary production methods. Cybercriminals, particularly those engaging in corporate espionage or state-sponsored attacks, seek to steal this IP for competitive or geopolitical advantage. For example, hackers may target a company’s R&D department to access confidential product designs. Data Breaches: Cybercriminals may breach IT systems to steal sensitive information about products, processes, and customers. Loss of intellectual property can result in competitive disadvantages and legal consequences, especially in highly competitive industries like automotive or aerospace. 5. Vulnerabilities in Industrial IoT (IIoT) Devices Increased Attack Surface: The rise of Industrial Internet of Things (IIoT) devices has introduced new vulnerabilities. Connected sensors, controllers, and devices in factories can be exploited if not properly secured. Many IIoT devices lack built-in security features or use default passwords, making them prime targets for cyberattacks. Real-Time Monitoring and Control Risks: IIoT enables real-time data collection and monitoring, improving operational efficiency. However, it also means that an attack on these devices could disrupt real-time control systems, potentially leading to unsafe conditions, equipment damage, or production errors. 6. Phishing and Social Engineering Targeted Phishing Attacks: Manufacturing companies are not immune to phishing, and employees in these organizations may be targeted through deceptive emails designed to steal login credentials or introduce malware into the system. Spear-phishing attacks may be highly customized, impersonating suppliers or partners to trick recipients into clicking malicious links. Human Error: Social engineering attacks, such as phishing, exploit human vulnerabilities, often bypassing even well-established cybersecurity protocols. In environments where employees are managing both IT and OT systems, a single mistake could lead to a system-wide breach. 7. Lack of Cybersecurity Awareness and Training Skill Gaps: Many manufacturing employees, especially those working in OT environments, may lack sufficient training in cybersecurity. The focus is often on ensuring the smooth operation of machinery and production lines, with less emphasis on understanding how cybersecurity impacts these systems. This creates an environment where staff may not recognize the signs of a cyberattack. Cybersecurity Culture: Some manufacturing environments may prioritize production efficiency over security practices, leading to a culture of neglect when it comes to cybersecurity. This can manifest as poor password management, delayed system patches, and a lack of proper network segmentation. 8. Regulatory and Compliance Challenges Compliance with Security Standards: Depending on the industry and the countries they operate in, manufacturers must comply with various cybersecurity standards and regulations. These can include the NIST Cybersecurity Framework in the U.S. or ISO 27001 globally. In the EU, regulations like the General Data Protection Regulation (GDPR) can come into play if the cyberattack results in the loss of personal data. Managing Multiple Standards: The challenge for manufacturing companies is that they often have to comply with multiple cybersecurity and safety regulations across different regions. Maintaining compliance can be difficult, particularly when IT and OT systems have different requirements. Conclusion Manufacturing companies must navigate a new and complex cybersecurity landscape where threats come from many directions. The integration of IT and OT systems, increased use of IIoT, and reliance on third-party suppliers make the sector highly vulnerable
미국 의료 부문에 대한 사이버 범죄의 고통스러운 대가

The painful cost of Cybercrime to the US Healthcare Sector In February 2024, UnitedHealth Group’s subsidiary, Change Healthcare, suffered a significant cybersecurity breach, which has had far-reaching consequences across the U.S. healthcare system. The attack, attributed to the ALPHV/BlackCat ransomware group, compromised both personally identifiable information (PII) and protected health information (PHI) for many individuals. Early estimates suggest that the breach affected a substantial portion of the U.S. population, with roughly 4 terabytes of data stolen. This breach disrupted UnitedHealth Group key operations, including the processing of medical claims and payments, which in turn affected hospitals, pharmacies, and other healthcare providers nationwide. As a result, some individuals were unable to use their insurance to access prescriptions, and healthcare providers faced financial strain due to frozen payments. UnitedHealth Group confirmed that the attack caused major outages, which they expected to fully resolve by the end of March 2024. In response to the attack, Change Healthcare resorted to manual processes to maintain business operations while working to restore its digital systems. The company paid an initial ransom of $22 million, but the costs related to recovery, system reconstitution, and business disruption could exceed $2.9 billion. Why Healthcare sector System Recovery needs an urgent upgrade This breach has raised broader concerns about the vulnerabilities within the healthcare sector, prompting discussions about the need for stricter cybersecurity regulations. Lawmakers are considering new policies to strengthen defenses and ensure that healthcare providers are better equipped to handle such attacks in the future. Although the HIPAA (Health Insurance Portability and Accountability Act) regulations outline specific requirements for System Recovery which we covered in a previous article, the act itself dates to 1996 with HIPAA’s Privacy Rule and Security Rule, which focus on the protection of personal health information (PHI) and electronic PHI (ePHI), being implemented several years after the act was introduced. The Privacy Rule became effective in 2003, and the Security Rule in 2005. Of course, much has changed in the world of cybercrime and data protection over the two decades since these rules became effective, but many healthcare organizations are still maintaining legacy systems supported by legacy backup and cybersecurity tools. Cristie Software can modernize System Recovery for the Healthcare sector Traditional backup and restore applications were originally designed to protect against system outages caused by hardware failures and natural disasters, they did not offer specific protection against cybercrime, or tools to assist with cyber recovery following an attack. Modern data protection applications have been designed from the ground up to secure data and aid cyber recovery with features such as immutable storage and isolated recovery. Cristie Software integrates seamlessly with modern data protection applications and takes cyber recovery many steps further by adding features such as multi-cloud disaster recovery support, advanced anomaly detection and cleanroom recovery to facilitate cyber forensics and backup integrity verification. Our system recovery software integrates with backup solutions from leading providers such as Rubrik, Cohesity, Dell Technologies and IBM. What should the US Healthcare sector focus on to improve Cyber Resilience? To reduce cybercrime, the U.S. healthcare sector must focus on strengthening its cybersecurity infrastructure, adopting mandatory standards, and investing in advanced technology. Key strategies include implementing robust encryption, multi-factor authentication, and a zero-trust architecture, which limits access to sensitive data unless explicitly verified. Regular vulnerability assessments and third-party risk management are also critical to addressing gaps in security. Additionally, comprehensive cybersecurity training for healthcare employees is essential to prevent human errors that can lead to breaches. Cyber Resilience through the adoption of AI and improved collaboration Healthcare providers should invest in AI-driven security tools and automation to detect and respond to threats in real-time. Cristie Software has incorporated features driven by Machine Learning (ML) into their software suite to provide early warning of malicious file encryption plus intelligent automated system recovery remediation which can solve many common system recovery failure scenarios without manual intervention. Collaboration between government agencies, like the Cybersecurity and Infrastructure Security Agency (CISA), and private sector organizations can improve information sharing and coordinated responses to attacks. Public-private partnerships, coupled with federal regulations that enforce minimum cybersecurity standards, could significantly strengthen defenses against cybercrime. Such measures would not only protect patient data but also ensure continuity in critical healthcare services. Conclusion In conclusion, reducing cybercrime in the U.S. healthcare sector requires a comprehensive approach involving a modernization of data security infrastructures, regular audits, and mandatory cybersecurity standards. By investing in AI-driven tools and enhancing collaboration between public and private entities, the sector can better protect sensitive data and maintain operational resilience. Implementing these strategies will be critical to safeguarding patient information, preventing disruptions in care, and ensuring the long-term security of the healthcare system against evolving cyber threats. Contact the Cristie Software team if you are looking to improve system recovery and replication for critical healthcare systems, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
의료 분야의 Cristie 소프트웨어

Cristie Software in Healthcare: Balancing Patient Data Security with Rapid Recovery The healthcare industry faces a unique challenge: safeguarding sensitive patient data while ensuring rapid system recovery in the event of failures or cyber incidents. With healthcare providers increasingly reliant on digital systems to manage patient records, treatment plans, and communication, the need to maintain uninterrupted access while protecting sensitive information is paramount. This is where Cristie Software solutions come into play, offering a comprehensive approach to both data security and system recovery that aligns with HIPAA (Health Insurance Portability and Accountability Act) compliance. Cristie Software supporting HIPAA Compliance and Data Security: The Cornerstone of Patient Trust HIPAA sets strict standards for protecting patient health information (PHI). Healthcare providers must ensure that all systems handling PHI are secure, with measures in place to prevent unauthorized access, breaches, or data loss. Non-compliance can result in heavy fines and reputational damage, making compliance not only a legal obligation but also a fundamental part of maintaining patient trust. Cristie Software solutions directly support HIPAA compliance by providing robust system recovery measures to safeguard systems holding PHI. Cristie CloneManager® and Cristie Recovery software integrate seamlessly with existing healthcare IT infrastructures to ensure that PHI systems as fully protected. These tools automate backup processes, ensure data encryption both in transit, provide early warning of malicious file encryption and provide audit trails to prove compliance during regulatory assessments. The Crucial Role of System Recovery In a healthcare environment, downtime can be life-threatening. Access to critical systems, including electronic health records (EHR) and patient management systems, must be restored as quickly as possible in the event of an outage or disaster. Whether it’s caused by hardware failure, cyberattacks, or human error, healthcare providers need to recover systems rapidly to minimize the impact on patient care. Cristie Software’s solutions are designed to provide automated and efficient recovery for these critical systems. Cristie recovery and replication software offers near-instant recovery of entire systems, allowing healthcare organizations to return to full operation without losing vital data. The suite’s replication and recovery capabilities ensure minimal downtime, allowing for a seamless transition to backup systems while the primary systems are restored. With Cristie’s Bare Machine Recovery (BMR) solutions, healthcare providers can restore entire servers in a matter of minutes, ensuring that patient services continue uninterrupted. BMR capabilities allow IT teams to recover not just data, but entire operating environments, including the configurations and settings necessary to bring systems back online without additional setup. Cristie Software – Combining HIPPA Compliance with Speed One of the most valuable aspects of Cristie Software’s solutions is the ability to balance HIPAA compliance with efficient recovery processes. Cristie CloneManager® allows healthcare organizations to create synchronized, real-time system clones that can be activated when the primary system goes down. These clones replicate not only the data but also system configurations, ensuring a complete, compliant backup that can be easily restored. The synchronization data transmitted between primary and secondary systems can also be encrypted during transit for added security. This functionality means healthcare IT teams can test and validate their recovery processes, ensuring they meet the stringent data security and availability requirements mandated by HIPAA. Staying Ahead with Regular Audits and Testing Cristie Software’s focus on continuous testing and validation further strengthens compliance efforts. HIPAA mandates regular risk assessments, including testing the effectiveness of backup and disaster recovery systems. Cristie’s tools enable healthcare providers to regularly test recovery procedures without disturbing the live environment, offering real-time verification that their recovery plans meet both regulatory requirements and internal service level agreements (SLAs). These proactive measures not only provide peace of mind but also help healthcare providers avoid costly downtime and potential HIPAA violations. The ability to perform live tests without impacting system availability is particularly valuable, as it allows organizations to validate their recovery processes without disrupting ongoing patient care. Conclusion Cristie Software solutions empower healthcare providers to strike a balance between data security and rapid recovery, ensuring that they remain compliant with HIPAA regulations while also minimizing system downtime. With automated, efficient recovery tools and robust data protection features, Cristie Software helps healthcare organizations maintain the availability and security of critical patient data—key to delivering high-quality care in today’s digital healthcare landscape. Contact the Cristie Software team if you are looking to improve system recovery and replication for critical healthcare systems, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
클라우드 기반 재해 복구

Cloud-Based Disaster Recovery with Cristie Software: Benefits and Considerations In today’s digital-first world, disaster recovery (DR) is no longer an afterthought for organizations—it’s a critical component of business continuity. Whether it’s natural disasters, cyberattacks, or hardware failures, unforeseen events can have devastating effects on company operations. Cloud-based disaster recovery (DR) has emerged as a reliable solution, providing organizations with a flexible, scalable, and cost-effective approach to safeguarding their data and systems. However, as with any technology, it comes with both benefits and considerations. In this article, we’ll explore the advantages and potential limitations of cloud-based disaster recovery and discuss how Cristie Software helps clients leverage these solutions to ensure uninterrupted business operations. The Advantages of Cloud-Based Disaster Recovery & Cristie Software Cloud-based DR solutions have transformed the way organizations approach disaster preparedness. Here are some key benefits: Cost Efficiency One of the main advantages of cloud-based disaster recovery is cost efficiency. Traditional DR solutions often require significant investments in duplicate hardware, data centers, and infrastructure. By moving DR to the cloud, organizations can eliminate the need for maintaining costly secondary sites. Instead, they only pay for the cloud resources they use, typically on a pay-as-you-go basis. Cristie Software’s solutions provide clients with a predictable, cost-effective pricing model, ensuring they only pay for the recovery, replication or migration licences they need, while still having access to a full suite robust disaster recovery features. Scalability and Flexibility Cloud-based DR solutions are inherently scalable. As organizations grow and their data needs expand, they can easily increase their storage capacity in the cloud without worrying about hardware constraints. This flexibility allows organizations to customize their disaster recovery solutions based on their evolving needs. Cristie Software’s solutions are designed to integrate with a wide range of cloud platforms, enabling clients to scale their disaster recovery plans effortlessly. Whether a business is expanding rapidly or undergoing periods of change, Cristie ensures that DR capabilities keep pace with operational demands. Faster Recovery Times The goal of any disaster recovery plan is to minimize downtime, and cloud-based DR solutions excel in this area. Cloud infrastructure allows organizations to replicate their systems offsite, ensuring they can recover their data and applications within minutes after a disruption. This rapid recovery capability is essential for businesses that need to maintain high availability and minimize the risk of lost revenue or productivity. Cristie Software provides clients with solutions that offer near-instant recovery, ensuring that systems can be up and running quickly in the event of a failure. Fast recovery capabilities are particularly critical for industries such as healthcare, finance, and manufacturing, where downtime can lead to significant operational and reputational damage. Automation and Reduced Complexity Traditional disaster recovery processes can be labor-intensive, requiring manual intervention and frequent testing. Cloud-based DR solutions simplify this by automating many of the processes involved in data backup, replication, and recovery. This reduces the risk of human error and ensures that businesses can maintain a high level of readiness without dedicating excessive resources to managing their DR environments. Cristie’s recovery solutions provide powerful automation features such as automated cloud target system provisioning which can save significant time when migrating multiple systems to the cloud for redundancy as part of a DR strategy. Geographic Redundancy A key advantage of cloud-based DR is the ability to store data across geographically dispersed locations. This geographic redundancy ensures that even if a disaster impacts a particular region, data remains safe and accessible from another location. By spreading data across multiple cloud data centers, organizations significantly reduce the risk of complete data loss in the event of a localized disaster. Cristie Software is used by many clients to ensure that their cloud-based DR solutions include geographic redundancy, guaranteeing that data is available no matter where a disaster may strike. Considerations for Cloud-Based Disaster Recovery with Cristie Software While cloud-based disaster recovery offers numerous advantages, there are important considerations that organizations need to account for when implementing these solutions. Data Transfer Speeds and Bandwidth One of the potential limitations of cloud-based DR is the reliance on network connectivity for data transfer. Large volumes of data may require significant bandwidth, and slow data transfer speeds could impact the efficiency of the backup and recovery process. Organizations need to ensure that they have sufficient bandwidth to handle their data replication and recovery needs, especially during a disaster. Cristie Software can help clients to optimize data transfer speeds with features such as changed block tracking, file compression and bandwidth throttling, ensuring that recovery and replication processes are efficient and effective, even when large datasets are involved. Security and Compliance While cloud providers often offer robust security measures, organizations are still responsible for ensuring that their disaster recovery strategies meet industry-specific compliance requirements. Data encryption, access controls, and regulatory compliance (such as HIPAA, GDPR, or PCI DSS) must be incorporated into any cloud-based DR plan. Cristie Software helps clients navigate these security and compliance challenges by providing end-to-end encryption for replica synchronization, secure access controls, and solutions that comply with industry regulations. This ensures that client data remains protected throughout the disaster recovery process. Vendor Lock-In Choosing a cloud provider for disaster recovery can sometimes lead to vendor lock-in, where switching providers becomes difficult or costly due to proprietary formats or systems. Organizations should carefully evaluate their options and seek flexible solutions that allow for portability between different cloud platforms. Cristie’s recovery solutions integrate with a wide range of virtual and cloud platforms, giving clients the freedom to choose or switch between cloud providers as their needs change, without being tied to a specific vendor. Ongoing Management and Monitoring While cloud-based DR solutions reduce much of the complexity of traditional DR, organizations still need to manage and monitor their systems to ensure they’re functioning correctly. Regular testing and monitoring are essential to ensure that the recovery process will work as expected when disaster strikes. Cristie Software provides clients with tools for ongoing monitoring, testing, and reporting, ensuring that their DR environments are always ready for deployment.
금융 서비스 핀테크 시대를 위한 재해 복구
Financial Services: Disaster Recovery for the Age of FinTech The financial services industry has undergone a digital revolution driven by FinTech (financial technology). With innovations like blockchain, mobile banking, AI-powered financial tools, and payment gateways, the sector has become more efficient but also more vulnerable to disruptions, including cyberattacks, system failures, and natural disasters. The rise of real-time transactions and digital ecosystems means that downtime can be devastating, both financially and reputationally. This highlights the critical importance of a reliable disaster recovery (DR) strategy. Exploring Unique Challenges and Solutions for System Recovery in the Evolving FinTech Landscape. In the financial services industry, disaster recovery isn’t just a safeguard—it’s a legal and operational requirement. Regulatory standards such as DORA, GDPR, NIS2, SOX, PCI-DSS, and FCA/PRA Operational Resilience directives in the UK mandate strict guidelines on data protection and recovery, with severe penalties for non-compliance. As FinTech accelerates innovation, firms must adapt their DR strategies to ensure business continuity, maintain data integrity, and comply with these regulations. Cristie Software provides a robust solution for this challenge through its recovery and replication software, helping financial firms protect their critical data. Key Challenges in FinTech Disaster Recovery. Real-time Transactions and 24/7 Availability In the FinTech era, consumers expect 24/7 access to financial services, whether for mobile banking, online payments, or stock trading. Any disruption, even for a few minutes, can lead to massive financial losses and a loss of customer trust. This poses a unique challenge in disaster recovery. Traditional backup systems, which perform nightly backups or periodic data snapshots, may not be sufficient. Cristie Software’s continuous data replication and near-instant recovery capabilities address this challenge by enabling real-time protection. This ensures that, in the event of a disaster, businesses can restore their operations rapidly minimizing real-time data loss, downtime and financial risk. Complex IT Infrastructures FinTech companies often operate on complex, hybrid IT infrastructures that include on-premises systems, cloud platforms, and third-party services. These infrastructures are often interwoven, making it difficult to coordinate disaster recovery efforts across multiple environments. Any failure in these systems could disrupt workflows and customer service. Cristie’s DR solutions are designed to work across heterogeneous environments, offering seamless recovery for both cloud-based and on-premises systems. Our server replication and recovery software helps ensure that both primary and secondary systems are synchronized, enabling organizations to recover quickly across all environments. Regulatory Compliance In financial services, regulatory compliance is non-negotiable. Financial firms must adhere to strict data protection laws, such as the General Data Protection Regulation (GDPR), DORA, NIS2, Sarbanes-Oxley Act (SOX), and Payment Card Industry Data Security Standard (PCI-DSS), all of which mandate stringent disaster recovery procedures to protect sensitive customer data. Cristie Software’s automated system recovery testing capabilities allow financial institutions to regularly validate their recovery plans without manual intervention. This ensures compliance with regulatory requirements while also providing audit-ready reports, ensuring firms remain in full control of their data protection strategies. Cybersecurity and Ransomware Threats The increase in cybercrime, particularly ransomware attacks, is a significant concern for the financial services industry. FinTech firms are prime targets due to the sensitive nature of the data they handle. If an attack compromises core systems, it could take days or weeks to fully recover unless the firm has a robust cybersecurity and DR plan in place. Cristie’s data protection solutions advanced anomaly detection providing early warning of malicious file encryption plus cleanroom recovery to facilitate cyber forensics within an isolated environment. Additionally, point-in-time recovery options available within the backup solutions we support from vendors such as IBM, Rubrik, Cohesity and Dell Technologies allow firms to restore data to an exact moment before the attack occurred, avoiding further disruption. Client Trust and Reputation Management Any downtime or data breach can significantly damage a financial institution’s reputation. In the world of FinTech, where competition is fierce, maintaining client trust is crucial. Customers expect seamless service and absolute protection of their personal and financial data. Cristie Software helps mitigate the risk of reputation damage by offering rapid recovery and replication solutions that ensure continuous uptime and data integrity. Our bare-metal recovery capabilities enable organizations to restore entire systems, including applications and databases, in minutes, allowing firms to minimize client impact and maintain service continuity during disasters. Key Solutions from Cristie Software for FinTech Disaster Recovery. 1. Automated Recovery and TestingCristie offers automated disaster recovery testing without interrupting live systems. This feature allows financial firms to test their DR plans frequently, ensuring their systems are ready to respond to any crisis. Regular DR testing helps businesses meet regulatory compliance standards while providing peace of mind that systems can be recovered swiftly in the event of a disaster. 2. Bare Metal Recovery (BMR)One of Cristie Software’s standout features is bare metal recovery (BMR). This technology allows organizations to recover entire systems, from hardware configurations to software applications, onto entirely new hardware. This is especially useful in the financial sector where physical machines are prevalent, and where a failed server could contain critical trading applications or transaction logs. Cristie’s BMR enables rapid restoration to minimize downtime, even on dissimilar hardware. 3. Continuous ReplicationTo handle the high availability demands of FinTech, Cristie’s continuous replication feature allows for near-instantaneous recovery points. By continuously replicating data to secondary systems, financial firms can be assured that their backup data is always up-to-date. This level of real-time protection is essential in minimizing data loss and ensuring fast failover. 4. Scalable and Flexible SolutionsCristie Software’s recovery solutions are designed to be scalable and flexible, meeting the needs of both small FinTech startups and large financial enterprises. Whether a firm is using on-premises infrastructure, cloud-based environments, or a hybrid of both, Cristie’s solutions ensure seamless integration and compatibility across all platforms. The scalability of these solutions means that as the firm grows, its DR capabilities can grow with it. Conclusion: Future-Proofing Disaster Recovery in the FinTech Era. The FinTech revolution has created both opportunities and challenges for financial services. While technology has introduced innovative services, it has also heightened the
재해 복구 및 사이버 복구 현황, 2024-2025년

IDC/Zerto – The State of Disaster Recovery and Cyber-Recovery, 2024–2025. IDC recently published the white paper “The State of Disaster Recovery and Cyber-Recovery, 2024–2025: Factoring in AI” sponsored by Zerto which highlights current trends in disaster protection strategies in the face of growing cybercrime. The paper also presents survey results regarding the adoption of artificial intelligence (AI) within data protection and cyber-resilience solutions. Here we examine the key findings of this report and discuss how system recovery solutions from Cristie Software can help users of backup solutions such as Zerto to address the gaps reported by the respondents to this report. Backup and recovery alone are insufficient for fast, effective Disaster Recovery (DR) or Cyber Recovery (CR). While backup and recovery (B/R) are foundational to data recovery, a complete disaster recovery solution needs to include the recovery of systems and underlying infrastructure, which in a modern IT environment, invariably involves a hybrid of physical, virtual and cloud platforms. Effective DR may involve moving application services and data to a second site using asynchronous or synchronous data replication, replicated infrastructure, plus application failover/failback processes between these diverse operating environments. CR builds upon B/R and DR processes with additional requirements for malware detection, forensic analysis, cleanroom recovery, and more. For this reason, backup modernization was among the top 3 IT initiatives for respondents to the survey over the next 12 months. When asked about the most important criteria when selecting backup and DR tools, the top response was “breadth of solution” indicating that companies are looking to modernize their entire B/R and DR toolset and processes. How does Cristie Software help with B/R, DR and CR modernization? Cristie Software recovery and replication solutions complement B/R solutions like Zerto and other leading solutions from vendors such as IBM, Dell Technologies, Rubrik and Cohesity. Our software works seamlessly with B/R solutions to deliver many benefits. Physical system recovery automation: Physical systems present the biggest system recovery administration overhead due to the frequent need for manual intervention. Cristie Software can automate the physical system recovery workflow eliminating manual intervention and facilitating automated physical system recovery at scale. Physical, virtual or cloud recovery & replication, in any direction: Although modern B/R solutions can utilize both on-prem and cloud targets, the addition of Cristie Software provides complete omni-directional system recovery between physical, virtual and cloud targets with features such as automated resource provisioning and dissimilar hardware technology. With many companies looking to move DR to the cloud, having complete flexibility over source and target system direction is a vital feature to include in any B/R modernization plan. Cleanroom recovery: The addition of Cristie Software allows recovery to isolated networks to assist cyber forensics or facilitate backup integrity verification in isolation from the production environment. Human factors impacting B/R, DR and CR: Staff availability, skills shortages and human error. The IDC survey highlights that IT personnel time and resource availability plus IT skills are in the top 3 biggest challenges organizations face with respect to disaster recovery. Human error was shown to be the biggest reason for data loss. Cristie Software can help to address each of these human factors through features such as automation, recovery orchestration, and the ongoing use of predictive AI. Recovery automation: By eliminating manual intervention IT resources can be spared and at the same time human error can be reduced. Recovery orchestration: More complex recovery workflows can be implemented through orchestration jobs further reducing IT administration overhead. Recovery failure remediation through machine learning (ML) and AI: Cristie are implementing ML and AI to provide automated recovery job failure remediation plus AI driven administrator guidance within the Cristie Virtual Appliance (VA) to reduce the need for specialist IT system recovery skills. Organizations need solutions to meet SLAs and provide the fastest recovery with the least data loss. System recovery time objectives (RTO) differ between organizations and business applications but rarely does system downtime does not equate to revenue loss, therefore the desire to reduce system recovery times featured highly in the survey responses. Meeting internal and external SLAs may require very specific RTOs with regulated industries such as financial services and healthcare having SLAs that incur may penalties if not met. To ensure that system recovery processes are capable of meeting SLAs testing should be a core component of every DR plan. Cristie Software provides several features to assist in recovery testing and verification. Recovery simulations: The simulation of any recovery job can be scheduled to provide a clear indication of the recovery time that the supporting infrastructure is able to deliver. This can provide early warning of network, storage and processing resources that may need need upgrades to meet specific RTOs. Recovery reporting: The Cristie VA serves as the single interface for all tasks and provides comprehensive reporting on recovery and replication job status. These extensive reports can help meet self-assessment and testing requirements that are often mandatory within industry regulations. Summary The findings within this report correlate with our experience as customers look to modernize their B/R solutions to support hybrid cloud architectures and multi-cloud environments. Despite the widespread adoption of virtualization, physical systems are still prevalent where application performance is vital, or to support legacy applications, therefore the automation of physical system recovery is an essential feature that organizations should include in their modernization plan. Read the full IDC report sponsored by Zerto here. Contact the Cristie Software team if you are in the process of addressing any of the challenges highlighted in this article, or to learn more about system replication and our system recovery integration with leading B/R solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
미국 제조업 부문의 사이버 범죄로 인한 실제 비용

The True Cost of Cybercrime in the Manufacturing Sector: Impact, Case Studies, and Mitigation Ransomware is a rapidly growing threat causing the cost of cybercrime to US manufacturing to extend far beyond financial losses. As more manufacturing companies embrace digital transformation, they expose themselves to vulnerabilities in their IT and operational technology (OT) systems. The economic impact of cyberattacks on this industry includes direct costs from ransom payments, lost productivity, disrupted operations, and reputational harm, alongside indirect costs such as regulatory fines and increased security expenses. This article explores the cost of cybercrime in the manufacturing sector, highlighting specific examples from the United States and outlining strategies manufacturers can adopt to mitigate these risks. 1. The Financial Burden of Cybercrime on Manufacturing Manufacturers face considerable financial losses from cyberattacks. According to a recent report by IBM, the average cost of a data breach in the manufacturing industry is approximately $4.24 million. Costs associated with cyber incidents include: Direct Financial Losses: Immediate costs such as ransom payments and recovery expenses can quickly amount to millions. Operational Downtime: Attacks on critical systems can halt production, leading to significant losses in productivity and delayed orders. Legal and Compliance Costs: Manufacturers may face fines for breaches that expose customer or supplier data, particularly under regulations such as GDPR and CCPA. Reputational Damage: Customer trust and brand reputation can suffer after an attack, potentially resulting in lost contracts and diminished market share. Security Costs: Companies often face increased costs for enhanced cybersecurity measures and insurance following a breach. 2. High-Profile Cyberattacks on U.S. Manufacturers Several recent cyber incidents in the United States reveal the devastating impact of cybercrime on manufacturing: Norsk Hydro (2019): Although Norsk Hydro is based in Norway, its U.S. operations suffered from a ransomware attack that disrupted production for days, costing the company nearly $50 million. The attack impacted IT systems and OT environments, forcing the company to switch to manual operations temporarily. Honda (2020): A cyberattack on Honda’s U.S. manufacturing systems halted production at several plants. The attack, reportedly carried out by a ransomware group, caused significant downtime and affected Honda’s ability to meet market demand. While Honda did not disclose exact figures, such disruptions likely resulted in millions of dollars in lost productivity and recovery costs. JBS USA (2021): The world’s largest meat supplier, JBS, fell victim to a ransomware attack that forced the company to shut down plants across the United States. JBS paid an $11 million ransom to resume operations, highlighting the high-stakes nature of attacks on critical manufacturing infrastructure. Kaseya Supply Chain Attack (2021): Although Kaseya itself is not a manufacturer, the ripple effects of the attack impacted numerous U.S. manufacturers who relied on its IT management software. This supply chain attack affected thousands of companies, underscoring the vulnerabilities in interconnected manufacturing supply chains. 3. Why the Manufacturing Sector is Vulnerable Several factors make manufacturing particularly susceptible to cybercrime: Convergence of IT and OT Systems: The integration of IT systems with OT creates vulnerabilities, as OT systems were not originally designed with cybersecurity in mind. Complex Supply Chains: Manufacturers rely on a web of suppliers, making them vulnerable to third-party risks from compromised partners or software. Aging Infrastructure: Many manufacturers still use legacy systems that are difficult to secure, making them attractive targets for cybercriminals. Industry 4.0 Adoption: As manufacturers move toward digital and automated processes, including the Internet of Things (IoT) and robotics, they introduce additional entry points for attackers. 4. The Indirect Costs of Cybercrime in Manufacturing While direct costs such as ransom payments and repair expenses are substantial, the indirect costs of cybercrime are equally significant: Supply Chain Disruptions: A cyberattack can halt operations for days, leading to delayed shipments and disrupted supply chains. These disruptions create ripple effects, affecting downstream customers and other suppliers. Customer and Partner Trust: Breaches can erode trust with clients and partners who expect secure handling of proprietary information. Increased Insurance Premiums: After a cyberattack, companies may face higher insurance premiums or additional costs for cyber insurance. 5. Mitigating Cyber Risks in Manufacturing Manufacturers can protect themselves from cybercrime by adopting a multi-layered security approach, leveraging advanced technologies, and ensuring ongoing employee training. Here are a few best practices: Do no overlook full System Recovery: Having a regular backup schedule for application data is commonplace for most organizations, but many overlook the steps needed to achieve full system recovery in the event of a disaster or cyberattack. Physical systems are inherently more time consuming to recover following an incident, especially if systems need to be recovered to dissimilar hardware. Cristie Software recovery solutions can overcome these challenges with advanced automation features, reducing recovery times and eliminating user intervention. Invest in Endpoint Protection and Network Monitoring: Protecting endpoint devices and continuously monitoring network traffic can help detect anomalies early, enabling rapid response to potential threats. Adopt a Zero Trust Model: Zero Trust requires all users and devices to be authenticated and authorized continuously, minimizing risks from compromised credentials. Segment IT and OT Networks: By separating IT from OT environments, manufacturers can reduce the chances of a single attack spreading across both systems. Regular Security Audits and Penetration Testing: Conducting routine security assessments can help identify vulnerabilities before attackers exploit them. Employee Training on Phishing and Social Engineering: Employees are often targeted through phishing emails and other tactics; regular training can improve awareness and reduce the chances of successful attacks. Looking Forward: Strengthening Resilience in Manufacturing As cyber threats continue to grow, the manufacturing sector must prioritize cybersecurity alongside other operational needs. With cybercriminals becoming more sophisticated and targeting critical industries, investment in cybersecurity and system recovery is not just a defensive measure but a strategic imperative. By adopting stronger security practices, manufacturers can better protect their operations and maintain resilience in the face of evolving cyber threats. Investing in cybersecurity is essential to safeguarding the future of manufacturing and ensuring the industry can continue to innovate without the shadow of cybercrime undermining its progress. Contact the Cristie Software team
가장 필요할 때까지 시스템 복구 계획을 방치하지 마세요.

가장 필요할 때까지 시스템 복구 계획을 미루지 마세요 시스템 복구는 종종 간과되는 경우가 많습니다. 많은 조직이 애플리케이션 데이터 백업과 함께 강력한 시스템 복구 계획을 세우는 것의 중요성을 너무 늦을 때까지 깨닫지 못합니다. 사고, 자연재해, 하드웨어 고장, 멀웨어 공격은 언제든지 발생할 수 있으며, 적절한 시스템 복구 계획이 없다면 이러한 사고는 심각한 데이터 손실과 다운타임으로 이어질 수 있습니다. 다음은 시스템 복구를 간과하는 몇 가지 이유입니다: 인식 부족: 많은 조직이 정기적인 데이터 백업과 함께 시스템 복구 계획이 없을 때 발생할 수 있는 위험에 대해 인식하지 못하고 있습니다. 과신: 일부 조직에서는 시스템이 너무 안전해서 문제가 발생해도 영향을 받지 않는다고 생각하는 경우가 있습니다. 복잡성: 정기적인 데이터 백업과 더불어 시스템 복구 계획을 수립하고 유지하는 일은 복잡하고 시간이 많이 소요되는 것처럼 보일 수 있습니다. 하지만 시스템 복구를 소홀히 하면 그 결과는 심각할 수 있습니다. 시스템 다운타임과 데이터 손실은 개인과 기업에 막대한 영향을 미쳐 금전적 손실, 생산성 문제, 평판 손상으로 이어질 수 있습니다. 따라서 시스템 복구의 우선순위를 정하고 데이터를 호스팅하는 중요한 인프라를 보호하기 위한 사전 조치를 취하는 것이 중요합니다. 즉, 애플리케이션 데이터 외에 정기적인 시스템 백업을 생성하고, 시스템 복구 계획을 테스트하며, 보안 패치를 최신 상태로 유지해야 합니다. Cristie 소프트웨어가 IT 시스템 복구를 간소화하는 방법 Cristie 소프트웨어는 IT 시스템 복구 프로세스를 간소화 및 자동화하도록 설계된 도구 모음을 제공합니다. 시스템 복구를 간소화하는 10가지 방법을 소개합니다: 자동화된 백업 및 복구: Cristie 소프트웨어는 시스템 복구 프로세스를 자동화하여 수동 단계를 줄이고 다운타임을 최소화합니다. 당사의 솔루션을 사용하면 장애 또는 재해 발생 후 전체 시스템, 애플리케이션 및 데이터를 신속하게 복구할 수 있습니다. 베어 메탈 복구(BMR): CristieBMR 솔루션은 운영 체제, 구성, 애플리케이션, 데이터를 포함한 전체 시스템을 서로 다른 하드웨어 또는 가상 환경으로 복구할 수 있습니다. 따라서 소프트웨어를 수동으로 재설치할 필요가 없어 시간을 절약하고 오류를 줄일 수 있습니다. 주요 백업 솔루션과의 호환성: Cristie도구는 Cohesity, Rubrik, Dell Technologies, IBM과 같은 주요 공급업체의 인기 백업 솔루션과 원활하게 통합되어 데이터 보호 및 복구에 대한 통합된 접근 방식을 제공합니다. 크로스 플랫폼 지원: Cristie 소프트웨어는 물리적, 가상, 클라우드 환경 등 다양한 플랫폼에서 복구를 지원합니다. 이러한 유연성 덕분에 다양한 IT 인프라에 쉽게 적응할 수 있습니다. 이기종 하드웨어 복구: Atlassian의 기술을 통해 수동 개입 없이 다양한 하드웨어 플랫폼으로 복구할 수 있어 유연성과 연속성을 보장합니다. 가상 및 클라우드 마이그레이션: Cristie 솔루션은 물리적, 가상, 클라우드 환경 간에 시스템을 원활하게 마이그레이션할 수 있어 비즈니스 연속성을 유지하고 변화하는 인프라 요구사항에 쉽게 적응할 수 있습니다. 테스트 및 검증: Cristie소프트웨어를 사용하면 복구 계획을 쉽고 중단 없이 테스트할 수 있습니다. 사용자는 라이브 시스템에 영향을 주지 않고 재해 복구 기능을 검증할 수 있어 다운타임 없이 대비할 수 있습니다. 신속한 복구 시간: Cristie IT 환경 복구 프로세스를 간소화함으로써 기업이 복구 시간(RTO)을 단축하여 운영에 미치는 영향을 최소화하고 복원력을 개선할 수 있도록 지원합니다. 중앙 집중식 관리: Cristie관리 콘솔은 백업, 마이그레이션, 복구 프로세스를 관리하는 단일 인터페이스를 제공하여 IT 시스템의 전반적인 관리와 모니터링을 간소화합니다. 고급 이상 징후 탐지: 크리스티 소프트웨어는 멀웨어 파일 암호화의 시작을 감지하여 랜섬웨어 활동에 대한 사전 경고를 제공합니다. Cristie 소프트웨어는 기본적으로 기업이 인프라와 데이터를 보호하고 중단의 영향을 최소화하는 데 도움이 되는 자동화되고 통합된 효율적인 솔루션을 제공하여 IT 시스템 복구를 간소화합니다. Cristie 솔루션과 사용 사례를 살펴보고 다른 기업들이 Cristie 복구 및 복제를 통해 IT 시스템 복구를 간소화하고 있는 방법을 알아보세요. 시스템 복구, 복제에 대해 자세히 알아보고 시스템 복구를 자동화하여 복구 시간을 개선하고 전체 재해 복구 워크플로우를 간소화하는 방법에 대해 알아보려면 Cristie 소프트웨어 팀에 문의하세요.
랜섬웨어 복구: 종합 가이드

랜섬웨어 복구: 랜섬웨어 복구: 종합 가이드 랜섬웨어 공격은 점점 더 많은 기업과 조직에 피해를 입히는 위협입니다. 이러한 악성 프로그램은 데이터를 암호화하여 몸값을 지불하고 통제권을 되찾을 때까지 데이터를 액세스할 수 없게 만듭니다. 안타깝게도 몸값을 지불한다고 해서 데이터 복구가 보장되는 것은 아니며, 이는 사이버 범죄 산업에 활력을 불어넣습니다. 이 종합 가이드에서는 랜섬웨어 공격을 예방하는 전략과 Cristie 소프트웨어가 공격을 받은 조직이 신속하게 복구할 수 있도록 지원하는 방법을 살펴봅니다. 랜섬웨어 공격 예방하기: 첫 번째 방어선은 직원 교육입니다: 피싱 이메일은 랜섬웨어의 일반적인 진입 지점입니다. 직원들이 피싱 시도를 인식하고 의심스러운 링크나 첨부파일을 클릭하지 않도록 교육하세요. 시스템을 정기적으로 패치하세요: 패치되지 않은 취약점은 해커에게 네트워크에 대한 백도어를 제공할 수 있습니다. 소프트웨어와 운영 체제를 최신 보안 패치로 정기적으로 업데이트하세요. 강력한 비밀번호와 다단계 인증(MFA)을 구현하세요: 강력한 비밀번호를 요구하고 MFA를 활성화하여 해커가 시스템에 액세스하기 어렵게 만들어 보안을 한층 더 강화하세요. 데이터를 정기적으로 백업하세요: 별도의 안전한 시스템에 데이터를 정기적으로 백업하세요. 이렇게 하면 랜섬웨어 공격이 발생했을 때 데이터를 신속하게 복구할 수 있습니다. 네트워크를 세분화하세요: 네트워크를 세분화하여 중요한 데이터에 대한 액세스를 제한하면 랜섬웨어 공격이 초기 방어를 우회할 경우 그 영향을 최소화할 수 있습니다. 바이러스 백신 및 맬웨어 방지 소프트웨어를 활용하세요: 멀웨어가 시스템을 감염시키는 것을 탐지하고 방지할 수 있는 평판이 좋은 보안 소프트웨어를 사용하세요. Cristie 소프트웨어: 랜섬웨어 복구 파트너 최고의 예방 전략이 있더라도 랜섬웨어 공격이 성공할 가능성은 여전히 존재합니다. 바로 이때 Cristie 소프트웨어가 필요합니다: 더 빠른 시스템 복구: Cristie베어 메탈 복구(BMR) 솔루션은 물리적 및 가상 머신 복구를 자동화하여 가동 중단 시간을 최소화하고 비즈니스를 신속하게 온라인 상태로 되돌릴 수 있습니다. 안전하고 검증 가능한 데이터 복구: Cristie 복구 솔루션은 시스템을 다시 온라인 상태로 만들기 전에 복구된 데이터가 완전하고 안전한지 확인할 수 있습니다. 격리된 네트워크 복구 기능을 통해 생산 시스템을 라이브 환경으로 복원하기 전에 데이터 무결성 테스트를 위해 전체 시스템을 클린룸 환경으로 복구할 수 있습니다. 백업 환경과 통합된 포괄적인 복구 및 복제: Cristie솔루션은 Cohesity, Rubrik, Dell Technologies, IBM과 같은 주요 공급업체의 백업 솔루션과 원활하게 통합되어 추가적인 오버헤드 없이 시스템과 데이터를 효율적으로 복원할 수 있습니다. 재해 복구 오케스트레이션: Cristie 재해 복구 워크플로우를 자동화하여 인적 오류를 줄이고 공격에 대한 조율된 신속한 대응을 보장합니다. 상세한 보고 및 감사: 복구 활동에 대한 포괄적인 보고서를 생성하여 포렌식 조사 및 공격 후 분석을 용이하게 합니다. Cristie 소프트웨어 사용의 이점: 다운타임 최소화: 신속한 시스템 복구로 비즈니스를 신속하게 복구하고 운영하세요. 데이터 보안 유지: 복구 프로세스 중에 데이터의 무결성과 보안을 보장합니다. 비용 절감: 데이터를 빠르고 효율적으로 복구하여 몸값 지불로 인한 재정적 부담을 피하세요. 안심할 수 있습니다: 랜섬웨어 공격에 대응할 수 있는 강력한 솔루션을 갖추고 있다는 확신을 가질 수 있습니다. Cristie 솔루션과 사용 사례를 살펴보고 다른 기업들이 Cristie 복구 및 복제를 통해 사이버 복구 및 사이버 복원력을 강화하는 방법을 알아보세요. 시스템 복구, 복제, 클린룸 복구 및 사이버 공격을 예방하고 복구하는 데 도움이 되는 고급 이상 징후 탐지 등의 기능에 대해 자세히 알아보려면 Cristie 소프트웨어 팀에 문의하세요.
DR 및 시스템 복구 요구 사항이 엄격한 산업 분야

Industries with Stringent DR and System Recovery Requirements Several industries face stringent regulations regarding disaster recovery and computer system recovery time objectives. These regulations aim to ensure business continuity and protect sensitive data in the event of disruptions. Here are some prominent examples: Financial Services Banking: Banks are subject to strict regulations, such as the Dodd-Frank Act in the US and the Digital Operational Resilience Act (DORA) and Second Payment Services Directive (PSD2) in the EU, which mandate robust disaster recovery plans. Insurance: Insurance companies must comply with regulations like Solvency II (EU) and the NAIC Cybersecurity Model Law (US), requiring strong data protection and business continuity measures. Capital Markets: Stock exchanges and other financial market participants face regulatory oversight through bodies such as the Securities Commission, often requiring specific data recovery and business continuity standards. Healthcare HIPAA: The Health Insurance Portability and Accountability Act (HIPAA) in the US imposes strict data privacy and security rules, including requirements for disaster recovery planning. GDPR: The General Data Protection Regulation (GDPR) in the EU mandates data protection and recovery measures, especially for healthcare organizations handling sensitive patient data. Energy FERC: The Federal Energy Regulatory Commission (FERC) in the US requires electric power companies to maintain reliable operations and have robust cyber security and recovery plans. NCPA: The National Cybersecurity Preparedness Act (NCPA) in the US mandates critical infrastructure entities, including energy companies, to implement cybersecurity best practices. Transportation FAA: The Federal Aviation Administration (FAA) in the US has strict regulations governing the cybersecurity and resilience of aviation systems. DOT: The Department of Transportation (DOT) in the US imposes cybersecurity requirements on various transportation modes, including railways and highways. Government NIST: The National Institute of Standards and Technology (NIST) provides cybersecurity frameworks and guidelines that government agencies must follow. CISA: The Cybersecurity and Infrastructure Security Agency (CISA) in the US mandates critical infrastructure organizations, including government agencies, to implement cybersecurity best practices. These are just a few examples of industries with stringent disaster recovery and system recovery requirements. The specific regulations and standards vary by jurisdiction and industry sector. Industries with Stringent DR and System Recovery Requirements: How Cristie Software Can Help Several industries face stringent regulations regarding disaster recovery and computer system recovery time objectives (RTOs) and system recovery verification (SRV). These regulations aim to ensure business continuity and protect sensitive data in the event of disruptions. We explored above certain key industries facing such regulations. Now, let’s delve into how Cristie Software empowers organizations in these sectors to improve their system recovery capabilities and meet regulatory compliance. Strengthening System Recovery in Regulated Industries Challenges Faced: Organizations in regulated industries often struggle with: Meeting RTOs: Ensuring critical systems are back online within regulatory timeframes can be challenging. Data Security and Integrity: Balancing rapid recovery with data security and verification procedures can be complex. Compliance Management: Keeping pace with evolving regulations and demonstrating compliance can be time-consuming and resource-intensive. Cristie Software Solutions: Cristie Software offers a comprehensive suite of solutions to address these challenges and enhance system recovery capabilities: Cristie BMR (Bare Metal Recovery): This software automates physical and virtual machine recovery, streamlining the process and minimizing downtime. Backup Integration: Cristie BMR seamlessly integrates with leading backup solutions from vendors such as Cohesity, Rubrik, Dell Technologies and IBM, enabling efficient data restoration and recovery. Automated Disaster Recovery Orchestration: Cristie’s solutions automate disaster recovery workflows, reducing human error and facilitating faster response times. Data Verification and Validation: Cristie software ensures recovered data is complete and consistent before bringing systems back online, meeting regulatory requirements for data integrity. Comprehensive Reporting and Auditing: Cristie provides detailed reports on recovery activities, facilitating compliance audits and demonstrating adherence to regulations. Benefits for Regulated Businesses By leveraging Cristie Software, organizations can: Achieve Faster RTOs: Faster system restoration with automation translates to minimized downtime and improved operational resilience. Ensure Data Security and Integrity: Robust data verification procedures safeguard sensitive data during recovery, meeting regulatory compliance. Simplify Compliance Management: Detailed reports and automated workflows streamline compliance efforts and reduce administrative burdens. Industry-Specific Solutions Cristie Software caters to diverse industry needs: Financial Services: Cristie’s solutions help financial institutions meet regulations like DORA, PSD2, and Solvency II, ensuring business continuity and data security. Healthcare: Cristie helps healthcare providers comply with HIPAA and GDPR, protecting patient data and ensuring rapid recovery of critical systems. Government and Critical Infrastructure: Cristie empowers government agencies and critical infrastructure entities to adhere to NIST, CISA, and other regulations, safeguarding sensitive data and national security. Ready to take control of your system recovery process and achieve regulatory compliance? Investing in Cristie Software solutions not only enhances system recovery capabilities but also positions organizations within regulated industries for long-term success by meeting compliance requirements and achieving optimal business continuity. Explore our solutions and use cases to discover how they can help your organization navigate the complexities of disaster recovery in today’s regulatory landscape. Contact the Cristie Software team to learn more about system recovery, replication and recovery testing to meet the requirements of industry regulation.
NIS2: 조직을 위한 IT 시스템 복구의 기준을 높입니다.

NIS2: 조직을 위한 IT 시스템 복구의 기준 높이기 EU의 네트워크 및 정보 시스템 보안 지침 2(NIS2)는 다양한 산업에서 사이버 보안에 대한 기준을 높입니다. 그 중 중요한 분야 중 하나는 IT 시스템 복구로, 조직에 보다 능동적이고 강력한 접근 방식을 요구하고 있습니다. 이 문서에서는 NIS2가 IT 시스템 복구에 미치는 영향과 Cristie 소프트웨어가 조직이 이러한 과제를 해결할 수 있도록 지원하는 방법을 살펴봅니다. NIS2와 IT 시스템 복구 의무 NIS2는 필수 부문의 조직이 운영 복원력의 우선 순위를 정하도록 의무화합니다. 이는 사이버 공격이나 시스템 장애가 발생했을 때와 그 이후에도 필수 서비스를 계속 운영할 수 있도록 보장하는 것을 의미합니다. NIS2가 IT 시스템 복구에 미치는 구체적인 영향은 다음과 같습니다: 필수 사고 대응 및 복구 계획: 사고에 대응하고 영향을 받은 시스템을 복구하기 위한 절차를 설명하는 세부 계획은 더 이상 선택 사항이 아닙니다. 테스트 및 준비: 이러한 계획을 정기적으로 테스트하여 실제 시나리오에서 효과적으로 작동하는지 확인해야 합니다. 시스템 백업 및 복구: 신속한 시스템 복구를 위해서는 안정적으로 자주 시스템을 백업하는 것이 중요합니다. 비즈니스 연속성 관리: 조직은 운영 중단 중에도 중요한 운영을 유지할 수 있는 전략이 있어야 합니다. 공급망 보안: IT 시스템의 복원력은 타사 공급업체에 대한 종속성까지 확장됩니다. Cristie 소프트웨어: NIS2 규정 준수 파트너 Cristie 소프트웨어는 조직이 이러한 NIS2 관련 문제를 극복할 수 있는 도구와 전문 지식을 제공합니다: 간소화된 시스템 복구: Cristie솔루션은 강력한 시스템 보호 및 복구 기능을 제공하여 중단 중에도 비즈니스 연속성을 보장합니다. 전문가 안내: 대규모 시스템 복구 및 복구 테스트 전략 구현에 대한 귀중한 조언을 제공하는 시스템 복구 전문가를 통해 NIS2 규정 준수를 달성할 수 있습니다. 자동화 이점: 시스템 복구 프로세스를 자동화하면 인적 오류를 최소화하고 운영을 간소화하여 효율성을 보장합니다. Cristie 소프트웨어와 함께 NIS2 요구 사항 충족 Cristie 소프트웨어와의 파트너십을 통해 조직은 다음을 수행할 수 있습니다: IT 시스템 복구 강화: NIS2 요구 사항을 충족하거나 능가하는 강력한 복구 전략을 구현합니다. 전반적인 복원력 향상: 사이버 공격과 시스템 장애를 자신 있게 견딜 수 있는 조직의 역량을 강화하세요. 규정 준수 간소화: Cristie전문 지식과 솔루션을 활용하여 NIS2 규정 준수를 위한 과정을 간소화하세요. IT 시스템 복구를 관리할 준비가 되셨나요? Cristie 소프트웨어는 조직이 NIS2의 복잡성을 해결하고 보다 탄력적인 IT 인프라를 구축할 수 있도록 지원합니다. 당사의 솔루션과 사용 사례를 살펴보고 규제 요건을 효과적으로 해결하고 IT 시스템을 보호할 수 있는 방법을 알아보세요. Cristie 소프트웨어 팀에 문의하여 시스템 복구, 복제 및 복구 테스트를 통해 NIS2의 요구 사항을 충족하는 방법에 대해 자세히 알아보세요.
MSP, CloneManager로 멀티 테넌트 시스템 마이그레이션 간소화
Cristie 소프트웨어로 MSP의 시스템 마이그레이션 과제 해결 Cristie 소프트웨어의 시스템 복제 및 마이그레이션 도구를 활용하면 MSP의 시스템 마이그레이션의 복잡성을 크게 완화할 수 있습니다. CristieCloneManager 소프트웨어를 사용하면 MSP는 고객에게 시스템 마이그레이션을 서비스로 쉽게 제공할 수 있습니다. Cristie솔루션이 특정 문제를 해결하는 방법은 다음과 같습니다: 다양한 IT 환경: 플랫폼 불가지론: Cristie도구는 물리적, 가상, 클라우드 환경을 포함한 다양한 시스템을 지원합니다. 따라서 다양한 클라이언트 인프라에서 여러 마이그레이션 솔루션을 사용할 필요가 없습니다. 마이그레이션 전 평가: 도구는 마이그레이션을 시작하기 전에 소스 시스템을 분석하여 잠재적인 호환성 문제를 파악할 수 있습니다. 데이터 마이그레이션 및 보안: 자동화된 복제: Cristie소프트웨어는 데이터 복제를 자동화하여 수동 개입을 최소화하면서 일관되고 안전한 데이터 전송을 보장합니다. 멀티 테넌트 지원: Cristie 가상 어플라이언스(VA) 내에서 여러 테넌트를 쉽게 생성할 수 있습니다. 테넌트는 완전히 격리되어 다른 테넌트와 상호 작용하거나 다른 테넌트의 데이터를 볼 수 없습니다. 암호화된 전송: 보안 데이터 전송 프로토콜이 마이그레이션 중 민감한 정보를 보호합니다. 애플리케이션 호환성: 라이브 테스트 환경: Cristie VA를 통해 MSP는 전체 마이그레이션 전에 대상 시스템의 애플리케이션 기능을 평가하기 위해 격리된 테스트 환경을 만들 수 있습니다. 애플리케이션 시밍: 개발자는 수정 사항을 적용하여 애플리케이션이 새로운 환경에서 작동하도록 조정할 수 있으므로 광범위한 수정의 필요성을 줄일 수 있습니다. 예를 들어, Microsoft Windows 애플리케이션 호환성 인프라/프레임워크 애플리케이션 쉬밍 기능을 사용하면 개발자가 Windows XP용으로 만들어진 애플리케이션에 수정 사항을 적용하여(코드를 다시 작성하지 않고) 이후 버전의 Windows에서 작동할 수 있도록 할 수 있습니다. 프레임워크 내에서 심은 프로그램과 Windows OS 사이의 버퍼 역할을 하기 위해 만들어집니다. CristieCloneManager와 Cristie VA를 사용한 격리된 네트워크 마이그레이션은 애플리케이션 쉬밍의 기능 및 보안을 테스트할 수 있는 환경을 제공합니다. 다운타임 관리: 다운타임 최소화: Cristie솔루션은 다운타임이 거의 없는 마이그레이션을 지원하여 고객의 서비스 중단을 최소화합니다. 단계적 마이그레이션: 단계적 마이그레이션: 도구를 통해 단계적 마이그레이션 접근 방식을 촉진하여 점진적이고 통제된 방식으로 새 시스템으로 전환할 수 있습니다. 비용 최적화 자동화 및 효율성: 자동화된 프로세스와 간소화된 워크플로를 통해 마이그레이션 속도를 높여 전체 프로젝트 비용을 절감할 수 있습니다. 리소스 소비 감소: 소프트웨어의 자동화 기능을 활용하여 수작업에 대한 의존도를 최소화하세요. 인력 및 전문성: 사용자 친화적인 도구: Cristie솔루션은 사용자 친화적으로 설계되어 MSP 팀 내 마이그레이션 전문 지식에 대한 의존도를 낮춥니다. 교육 및 지원: Cristie MSP가 마이그레이션 도구를 능숙하게 사용할 수 있도록 교육 및 지원 리소스를 제공합니다. 고객 커뮤니케이션 및 관리: 상세한 보고: 도구는 마이그레이션 진행 상황에 대한 통찰력 있는 보고서를 제공하여 프로세스 전반에 걸쳐 고객과 명확하게 소통할 수 있도록 합니다. 실시간 모니터링: 마이그레이션 프로세스를 실시간으로 모니터링하여 사전 예방적인 문제 해결 및 고객과의 커뮤니케이션을 가능하게 합니다. 요약 결론적으로 Cristie Software는 시스템 마이그레이션의 복잡성을 효율적이고 안전하게 해결할 수 있는 강력한 도구 모음을 MSP에 제공합니다. Cristie솔루션을 활용함으로써 MSP는 고객에게 새로운 기술로 보다 원활하게 전환하고 클라우드 온보딩을 간소화하는 동시에 다운타임을 최소화하고 비용을 최적화하여 궁극적으로 가치 제안을 강화할 수 있습니다. 시스템 마이그레이션 사용 사례에서 MSP가 CristieCloneManager를 어떻게 활용하고 있는지 알아보세요. Cristie 소프트웨어 팀에 문의하여 CloneManager를 통한 시스템 마이그레이션, 자동화 및 격리 호환성 테스트에 대해 자세히 알아보세요.
최신 Windows 버전으로 업그레이드하는 것이 중요한 이유
최신 Windows 버전으로 업그레이드하는 것이 중요한 이유 Windows 기반 서버를 최신 버전으로 업데이트하는 것은 종종 간과되지만, 시스템의 보안, 성능 및 전반적인 기능을 유지하는 데 매우 중요합니다. 주요 OS 버전 간의 업그레이드 프로세스를 간소화하고 애플리케이션 호환성을 평가할 수 있는 샌드박스 테스트 환경을 제공하는 CristieCloneManager 복제 및 마이그레이션 소프트웨어로 Windows OS 업데이트를 자동화할 수 있습니다. 최신 OS 버전으로 업그레이드하는 것이 왜 중요한지 먼저 살펴보겠습니다. 위협에 대한 보안 보호 강화: 랜섬웨어, 맬웨어, 바이러스와 같은 최신 위협은 끊임없이 진화하고 있습니다. Microsoft는 이러한 위협을 해결하기 위해 정기적으로 업데이트를 배포하여 시스템과 데이터를 보호합니다. 보안 격차 해소: 이전 Windows 버전에는 최신 버전에서 패치된 취약점이 있을 수 있습니다. 업그레이드를 통해 이러한 보안 허점을 효과적으로 차단할 수 있습니다. 최신 하드웨어에 최적화된 성능 향상: 최신 Windows 버전은 최신 하드웨어를 활용하도록 설계되어 부팅 시간이 빨라지고 성능이 원활해지며 애플리케이션 호환성이 향상됩니다. 리소스 관리: 업데이트에는 메모리 관리, CPU 사용량 및 기타 시스템 리소스에 대한 최적화가 포함되어 있어 시스템 응답성이 향상되는 경우가 많습니다. 손끝에서 새로운 기능 혁신에 액세스: Windows 업데이트는 사용자 환경을 개선하기 위한 새로운 기능을 도입합니다. 여기에는 생산성 향상 도구부터 혁신적인 멀티미디어 기능까지 다양한 기능이 포함됩니다. 최신 응용 프로그램과의 호환성: 많은 최신 애플리케이션이 최적으로 작동하려면 최신 Windows 버전이 필요합니다. 업그레이드를 통해 호환성을 보장하고 잠재적인 문제를 예방할 수 있습니다. 지원 및 호환성 확장 지원: Microsoft는 특정 기간 동안 지원 및 업데이트를 제공합니다. 오래된 시스템은 중요한 패치 및 보안 수정 사항을 놓칠 수 있습니다. 하드웨어 및 소프트웨어 호환성: 최신 Windows 버전은 최신 하드웨어 및 소프트웨어와의 호환성이 향상되어 원활한 통합을 보장합니다. 안전하고 체계적으로 시스템을 업그레이드하고 백업하는 방법: 업그레이드하기 전에 전체 시스템 백업을 만들어 잠재적인 데이터 손실을 방지하세요. 호환성 확인: 하드웨어 및 소프트웨어가 새 Windows 버전과 호환되는지 확인하세요. 드라이버 업데이트: 업그레이드 후 드라이버를 업데이트하여 최적의 성능과 호환성을 보장하세요. 클론매니저 CristieWindows OS 업데이트 및 호환성 테스트 간소화 클라우드 기반 샌드박스 환경에서 안전하게 Windows OS 업그레이드를 테스트할 수 있는 클론매니저를 사용하세요. 이를 통해 업그레이드된 이미지를 프로덕션 시스템에 배포하기 전에 호환성을 보장할 수 있습니다. 초기 이미지 마이그레이션 후 Microsoft Windows OS 업데이트 자동화 CloneManager®는 초기 이미지를 대상 시스템으로 전송한 후 Microsoft Windows OS를 자동으로 업데이트하는 기능을 제공합니다. 이 옵션을 선택하면 대상 시스템 내에 복제 샌드박스가 설정되어 변경 사항을 수신하고 부팅 가능한 테스트 인스턴스로 사용할 수 있는 씬 프로비저닝된 Copy-on-Write 계층을 위해 마이그레이션된 이미지의 스냅샷을 생성합니다. 시스템이 부팅되면 Microsoft OS의 업그레이드 프로세스가 시작됩니다. 업그레이드 후 필요한 모든 OS 라이선스는 사용자가 직접 신청해야 합니다. 시스템 업그레이드가 완료되면 애플리케이션 유효성 검사를 위해 시스템을 새 운영 체제로 부팅하거나, 필요한 경우 최신 버전에 도달하기 위해 추가 업그레이드를 수행할 수 있습니다. 자동 업그레이드를 통해 시스템을 최신 Windows OS로 업그레이드할 수 있으므로 수동으로 개입할 필요가 없습니다. 그러나 필요한 애플리케이션 업그레이드는 최종 이미지에 수동으로 적용해야 합니다. 요약 결론적으로 최신 Windows 버전으로 업그레이드하는 것은 단순히 새로운 기능을 얻는 것만이 아니라 시스템을 보호하고 성능을 향상시키며 최신 기술과의 호환성을 보장하기 위한 것입니다. 이러한 업데이트에 우선순위를 두면 시스템의 장기적인 상태와 보안에 투자하는 것입니다. 기억하세요: 업데이트를 유지하는 것이 중요하지만, 시스템을 크게 변경하기 전에 항상 전체 시스템 수준의 백업 이미지를 만들어야 합니다. Cristie 소프트웨어 팀에 문의하여 CloneManager를 통한 OS 업그레이드 자동화 및 격리 호환성 테스트에 대해 자세히 알아보세요.
시스템 복구 소프트웨어 사용자에게는 빠른 CrowdStrike 복구가 현실이 되어야 합니다.

Fast CrowdStrike Recovery should be a reality for users of System Recovery software CrowdStrike recovery is an activity and topic of focus for many organizations following the CrowdStrike bug that caused a global IT outage on July 18th and 19th, 2024. The number of users effected is unknown, however, we can glean some insights from news reports: Widespread Disruption: News articles describe the outage as widespread, disrupting airlines, financial institutions, hospitals, and businesses. Large Organizations: The affected entities suggest a significant number of users, potentially impacting thousands or even millions of devices. It is clear the CrowdStrike update bug caused significant disruption for many organizations. What caused the CrowdStrike Falon update outage? The outage was caused by a faulty update for the Windows version of their Falcon sensor.Here’s a breakdown of the issue: Falcon Sensor: This is a core component of the CrowdStrike Falcon platform that runs locally on user devices and scans them for potential malware threats. Faulty Update: A specific update for the Windows version of the Falcon sensor contained a defect. System Crash: This defect triggered a “logic error” that caused the affected systems to crash and enter a continuous restart loop, often referred to as the “Blue Screen of Death” (BSOD) on Windows machines. Here’s some additional information: Limited Scope: The issue only affected the Windows version of the Falcon sensor, not Mac or Linux systems. Recovery: CrowdStrike identified the issue and deployed a fix. However, restarting the affected systems multiple times might have been necessary to complete the recovery process. It’s important to note that CrowdStrike has not released any official reports detailing the exact cause of the bug within the update. However, based on the available information, it appears to be a software error within the update itself that caused the system crashes. How would Cristie Software customers recover faster from the CrowdStrike update crash? CrowdStrike recovery presents a perfect use case for automated system recovery. In this explainer video, Sky News business correspondent Paul Kelso outlines the laborious manual process required to recover systems to a state that allows for deletion of the disruptive CrowdStrike driver file. Users with large server estates that do not utilize automated system recovery or boot management tools would face a significant amount of manual intervention and downtime in order to facilitate driver removal from all effected machines. Cristie Software bare machine recovery (BMR) provides system recovery from leading backup solutions such as Rubrik Security Cloud, Cohesity DataProtect, IBM Storage Protect and Dell Technologies backup solutions Avamar and Networker. Using Cristie recovery software automation, the following steps would be required to recover effected machines to a point before the disruptive CrowdStrike driver was applied: Reboot in DR environment: Reboot systems into DR environment (this can be automated using boot management tools with our web-boot ISOs). Recover systems to last known good point in time: Trigger recovery from backup server (Rubrik, Cohesity, IBM or Dell). Reboot system: Machines would reboot to the last known good state prior to the application of the disruptive driver. What is the manual CrowdStrike update recovery process? The recovery process for the CrowdStrike Falcon update bug depended on the severity of the issue and your access to the affected system. Here are the two main approaches taken from online research. Users effected by the CrowdStrike update bug should conduct their own due diligence and refer to CrowdStrike support services to verify the procedure for their specific environment: Booting into Safe Mode or Windows Recovery Environment (WinRE):This method was recommended by CrowdStrike for situations where the system continuously rebooted into a loop (BSOD). Here’s how it worked:• Boot into Safe Mode: This can be achieved through various methods depending on your system configuration. One common approach is to repeatedly press the F8 key during system startup.• OR Boot into WinRE: If Safe Mode is inaccessible, you can try booting into the Windows Recovery Environment (WinRE). This may involve using a bootable USB drive or recovery media provided by your system manufacturer.• Navigate to the Target Directory: Once in Safe Mode or WinRE, locate the folder containing the problematic CrowdStrike files. The specific path might vary, but it’s typically something like C:WindowsSystem32driversCrowdStrike.• Delete the Faulty File: Look for a file named “C-00000291*.sys” (the asterisk represents any wildcard characters) and delete it.• Reboot Normally: After deleting the file, attempt to reboot your system normally. If the issue was resolved, the system should boot up successfully. Detaching the Disk from a Virtual Server (Advanced Users):This option was suitable for virtualized environments where the affected system was running on a virtual machine (VM). It’s important to note that this method requires technical expertise and should only be attempted by experienced users. Here’s a simplified overview:1. Detach Disk: Detach the virtual disk volume from the impacted virtual server. Create a backup or snapshot of the disk volume as a precaution.2. Mount Disk on Another Server: Attach or mount the detached disk volume to a separate virtual server with a working CrowdStrike installation.3. Access and Delete File: Follow steps similar to the Safe Mode method to access the C:WindowsSystem32driversCrowdStrike directory and delete the “C-00000291*.sys” file.4. Reattach Disk and Reboot: Detach the disk from the temporary server, reattach it to the original impacted virtual server, and attempt a normal reboot. Additional Tips: Consult CrowdStrike Support: If you are unsure about the recovery process or encounter difficulties, it’s advisable to reach out to CrowdStrike support for assistance. Test Functionality: Once your system boots up successfully, verify that your CrowdStrike Falcon sensor is functioning correctly. Remember: These are general guidelines taken from online resources. The specific steps may vary depending on your system configuration and the severity of the issue. It’s always best to consult with a qualified IT professional if you are unsure about any of the recovery procedures. Conclusion The CrowdStrike driver update failure has demonstrated how vulnerable enterprises are to system level driver changes that have the ability to disrupt the boot process of any operating system. Most companies invest
복귀 조율하기: 자동화를 통해 시스템 복구를 간소화하는 방법

복구 조율하기: 자동화를 통해 시스템 복구를 간소화하는 방법 오늘날의 디지털 환경에서 다운타임은 치명적인 결과를 초래할 수 있습니다. 시스템이 오프라인 상태가 되는 매 순간은 생산성, 매출, 나아가 고객 신뢰의 손실로 이어집니다. 기업들은 재해, 시스템 중단 또는 사이버 공격이 발생했을 때 다운타임을 최소화하고 신속하게 복구할 수 있는 방법을 끊임없이 모색하고 있습니다. 바로 이 지점에서 복구 프로세스의 자동화 및 오케스트레이션이 중요한 역할을 합니다. 시스템 복구의 자동화 및 오케스트레이션이란 무엇인가요? 잘 연습된 오케스트라가 각 악기들이 완벽한 하모니를 이루며 각자의 역할을 수행하고 있다고 상상해 보세요. 이는 자동화된 복구와 유사합니다. IT 담당자에게 알림, 영향을 받은 시스템 격리, 데이터 복원 시작 등 복구 프로세스 내의 개별 작업은 사전 정의된 워크플로우를 사용하여 자동화됩니다. 오케스트레이션은 한 단계 더 나아가 이러한 자동화된 작업의 실행을 올바른 순서로 조율하여 원활하고 효율적인 복구를 달성합니다. 복구 프로세스 자동화 및 오케스트레이션의 이점 - 더 빠른 복구 시간 일상적인 작업을 자동화하면 사람의 개입이 최소화되어 복구 시간이 훨씬 빨라집니다. 따라서 다운타임을 최소화하고 중요한 시스템을 더 빨리 온라인 상태로 되돌릴 수 있습니다. - 오류 감소 수동 복구 프로세스에는 인적 오류가 발생하기 쉽습니다. 자동화는 이러한 오류를 제거하여 항상 일관되고 안정적인 복구를 보장합니다. - 효율성 향상 IT 직원은 반복적인 작업에서 벗어나 중단의 근본 원인을 조사하고 예방 조치를 구현하는 등 보다 전략적인 이니셔티브에 집중할 수 있습니다. - 일관성 향상 자동화된 워크플로는 복구를 수행하는 개인에 관계없이 복구 절차를 일관되게 따르도록 보장합니다. - 비용 절감 복구 시간이 단축되고 효율성이 향상되면 상당한 비용을 절감할 수 있습니다. - 확장성 자동화된 복구 프로세스는 변화하는 IT 환경, 대규모 서버 자산, 증가하는 데이터 볼륨에 맞춰 쉽게 확장할 수 있습니다. - 향상된 규정 준수 자동화를 통해 조직은 데이터 복구 및 재해 대비에 대한 규정 준수 요건을 충족할 수 있습니다. 자동화를 효과적으로 활용하기: - 포괄적인 복구 계획 수립 복구 프로세스를 자동화하기 전에 잘 정의된 복구 계획을 수립하는 것이 중요합니다. 이 계획에는 다양한 유형의 중단 및 재해로부터 복구하는 데 필요한 단계가 간략하게 설명되어 있어야 합니다. - 자동화 기회 파악 현재 복구 절차를 분석하고 자동화할 수 있는 작업을 파악하세요. 이러한 작업은 일반적으로 단계가 잘 정의된 반복적인 수동 작업입니다. - 올바른 도구에 투자하세요 기존 IT 인프라와 원활하게 통합되고 필요한 기능을 제공하는 솔루션을 선택하세요. Cristie 소프트웨어 시스템 복구 솔루션은 Rubrik, Cohesity, IBM, Dell Technologies의 주요 백업 솔루션과 통합되며, 필요한 경우 독립형 자동 시스템 복구 기능도 제공합니다. - 테스트 및 개선 자동화된 복구 워크플로우를 정기적으로 테스트하여 예상대로 작동하는지 확인하세요. 이를 통해 실제 재해가 발생하기 전에 잠재적인 문제를 식별하고 해결할 수 있습니다. 결론 오늘날과 같이 빠르게 변화하는 디지털 세상에서 다운타임은 선택 사항이 아닙니다. 복구 프로세스를 자동화하고 오케스트레이션하면 중단이나 공격이 발생했을 때 더 빠르고 효율적이며 안정적인 복구를 보장할 수 있습니다. 이는 다운타임 감소, 효율성 향상, 궁극적으로 보다 탄력적인 IT 인프라로 이어집니다. 재해가 닥칠 때까지 기다리지 말고 지금 바로 복구 프로세스를 자동화하여 성공적인 복귀를 준비하세요. 재해 및 사이버 복구 전략에 시스템 복구 자동화 및 오케스트레이션을 포함하는 방법을 알아보려면 Cristie 소프트웨어 팀에 문의하세요.
시스템 복구를 위한 HIPPA 요구 사항

HIPAA (Health Insurance Portability and Accountability Act) specific requirements for System Recovery HIPAA has specific regulations regarding system recovery within the healthcare sector, particularly under the Security Rule, which focuses on safeguarding electronic protected health information (ePHI). While HIPAA doesn’t prescribe specific technical solutions, it establishes guidelines that healthcare providers and related entities must follow to ensure the confidentiality, integrity, and availability of ePHI during system recovery scenarios. Here are the key components relevant to system recovery: Contingency Planning Requirements The HIPAA Security Rule mandates that covered entities (healthcare providers, health plans, clearinghouses) and their business associates (including IT service providers handling ePHI) develop a Contingency Plan to ensure the continuity of access to ePHI during emergencies, including system failures. This is outlined in 45 CFR § 164.308(a)(7) and includes five key implementation specifications: Data Backup Plan – Requirement: Covered entities must establish a data backup plan that includes creating and maintaining retrievable, exact copies of ePHI. This ensures that, in the event of a system failure, ePHI can be recovered and restored from secure backups. – Purpose: To prevent data loss and ensure ePHI is available for patient care and other essential functions after an emergency or system malfunction. Disaster Recovery Plan – Requirement: A disaster recovery plan must be in place to restore any loss of data due to an emergency or disaster (such as hardware failure, cyberattacks, or natural disasters). – Focus on System Recovery: This plan specifically addresses how to restore and recover ePHI and essential systems to operational status after a disruption. Healthcare organizations must ensure their systems can recover within a reasonable time frame to avoid prolonged downtime, which could affect patient care. Emergency Mode Operation Plan – Requirement: This involves establishing procedures to ensure the continuation of critical business processes and security measures to protect ePHI while operating in emergency mode. – Relevance to System Recovery: If a system failure occurs, healthcare providers need to continue functioning in a secure manner, which could involve alternative methods for accessing or handling ePHI while the primary systems are restored. Testing and Revision Procedures – Requirement: HIPAA mandates regular testing and updating of the contingency plans to ensure they work effectively when needed. – System Recovery Testing: Healthcare organizations should routinely test their backup and recovery systems to confirm that they can successfully recover ePHI, and that the recovery processes are efficient and reliable. Any weaknesses identified during testing should be addressed and revised in the plan. Applications and Data Criticality Analysis – Requirement: Organizations must assess and prioritize the most critical systems and data that need to be restored first in the event of a system failure. – Recovery Prioritization: This analysis helps determine which systems must be recovered first, ensuring that the most important functions (e.g., patient care applications) are prioritized during the recovery process. Risk Management Under HIPAA’s Security Rule (45 CFR § 164.306(b)(2)), healthcare entities must conduct risk assessments to identify vulnerabilities that could impact the availability of ePHI and implement appropriate security measures to mitigate those risks. System recovery is a crucial component of managing the risk of potential data loss or breaches due to system failure. Encryption and Safeguards HIPAA encourages the use of encryption for ePHI, particularly in transit and at rest. While not mandatory, if ePHI is encrypted and inaccessible during a breach or system failure, it provides an additional layer of protection. If encrypted systems are being recovered, encryption keys and security protocols must be part of the recovery process to ensure that data remains secure. Business Associate Agreements (BAAs) If a healthcare provider outsources data hosting, backup, or disaster recovery services, the provider must ensure that the business associate complies with HIPAA’s system recovery and contingency plan requirements. This is outlined in the Business Associate Agreement (BAA), which specifies the responsibilities of third-party vendors in protecting ePHI, including system backup and recovery. Reporting and Breach Notification If a system failure results in the unauthorized access, use, or disclosure of ePHI, HIPAA requires that it be treated as a breach. This could trigger the Breach Notification Rule (45 CFR § 164.400-414), which mandates that covered entities notify affected individuals, the U.S. Department of Health and Human Services (HHS), and possibly the media, depending on the scale of the breach. Effective system recovery can help minimize the likelihood and impact of such breaches. Conclusion Under HIPAA, system recovery is a critical component of ensuring the security and availability of ePHI. Healthcare organizations must have contingency plans in place, including data backup, disaster recovery, and emergency mode operations, to ensure that ePHI can be quickly restored and securely managed after a system failure or disaster. These processes are essential not only for compliance but also for protecting patient information and maintaining the continuity of care during unforeseen events. Contact the Cristie Software team if you are looking to improve system recovery and replication for critical healthcare systems, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
림보에 갇히다: 사이버 공격으로부터 복구하는 데 시간이 오래 걸리는 이유
림보에 갇히다: 사이버 공격으로부터 복구하는 데 시간이 오래 걸리는 이유 사이버 공격은 디지털 시대의 냉혹한 현실입니다. 침해로 인한 초기 충격도 충분히 심각하지만, 진정한 고통은 나중에 시스템 다운타임이 장기화되는 데서 비롯될 수 있습니다. 이로 인해 비즈니스가 마비되고 고객 신뢰가 약화되며 수백만 달러의 매출 손실이 발생할 수 있습니다. 그렇다면 사이버 공격 후 온라인 상태로 돌아가는 데 시간이 오래 걸리는 이유는 무엇일까요? 주요 원인을 분석해 보면 다음과 같습니다. 인프라 손상: 사이버 공격은 종종 중요한 인프라, 서버, 네트워크, 데이터베이스를 표적으로 삼습니다. 이러한 필수 시스템은 손상되거나 암호화되거나 심지어 파괴되어 광범위한 수리 또는 완전한 재구축이 필요할 수 있습니다. 2. 데이터 검증: 백업에서 복원하는 것은 일반적인 복구 전략이지만 완벽한 방법은 아닙니다. 해커는 백업을 조작할 수 있으므로 시스템을 다시 온라인 상태로 만들기 전에 데이터 무결성을 철저하게 검증해야 합니다. 이 까다로운 과정은 매우 느릴 수 있습니다. 게다가 많은 기업이 DR 계획에서 시스템 복구를 소홀히 하고 애플리케이션 데이터 백업에만 과도하게 집중합니다. 데이터는 기본 시스템과 인프라 없이는 아무 소용이 없습니다. 3. 연쇄 반응: 최신 IT 환경은 서로 연결된 시스템으로 이루어진 복잡한 그물망입니다. 한 시스템에 대한 공격은 연쇄적인 영향을 미쳐 광범위한 중단을 초래할 수 있으며, 모든 시스템이 다시 제대로 작동하도록 하려면 복잡한 단계별 복구 프로세스가 필요합니다. 시스템 복구 이미지 또는 애플리케이션 데이터 백업에 멀웨어가 의심되는 경우 격리된 네트워크 복구가 필수적입니다. 4. 보안 우려: 멀웨어 잔존에 대한 두려움은 복구 지연의 주요 원인입니다. 조직은 시스템을 네트워크에 다시 연결하기 전에 시스템이 깨끗하다는 것을 절대적으로 확신해야 합니다. 여기에는 종종 광범위한 보안 감사 및 스캔이 포함되므로 복구 일정에 귀중한 시간(또는 며칠)이 추가됩니다. 클린룸 환경으로 시스템을 복구하는 것은 추가 시스템과 네트워크에 대한 지속적인 오염 위험 없이 사이버 포렌식 분석을 수행할 수 있는 필수적인 기능입니다. 5. 준비 부족: 안타깝게도 많은 조직이 사이버 공격에 대비하지 못하고 있는 것이 현실입니다. 부적절한 백업, 전체 시스템 복구 도구의 부족, 오래된 복구 계획, 숙련된 IT 인력의 부족으로 인해 대응 및 복구 프로세스가 상당히 느려질 수 있습니다. 결론 사이버 공격은 피할 수 없지만 다운타임이 오래 지속될 필요는 없습니다. 데이터 보안에 우선순위를 두고, 강력한 백업 및 시스템 복구 전략을 구현하고, 정기적으로 복구 계획을 테스트함으로써 조직은 복원력을 크게 향상시키고 공격으로부터 더 빠르게 회복할 수 있습니다. 디지털 세상에서는 오프라인 상태의 1분 1초가 큰 손실로 이어질 수 있습니다. Cristie 소프트웨어 팀에 문의하여 시스템 복구, 클린룸 복구 및 고급 파일 이상 탐지를 사이버 복구 전략에 포함시키는 방법을 알아보세요.
하이브리드 환경에서의 복구 탐색: 물리적 시스템 대 가상 머신

Navigating Recovery in a Hybrid World: Physical Systems vs. Virtual Machines In the aftermath of a cyberattack or system outage, restoring critical systems quickly and effectively is paramount for minimizing downtime and returning to business as usual. However, modern IT infrastructures often include a blend of physical servers and virtual machines (VMs). This hybrid environment presents unique challenges when it comes to disaster recovery strategies. Physical System Recovery: Hardware Headaches Hardware Dependencies: Physical servers are inextricably linked to their underlying hardware components. In a recovery scenario, hardware might need to be sourced, configured, and have an operating system installed before restoring data. This process can be time-consuming, especially if specific hardware models are required. Legacy Systems: Older physical systems may rely on outdated operating systems or specialized software configurations, adding complexity to the recovery. Restoring these systems often needs meticulous planning and compatibility testing. Single Point of Failure: Physical servers represent a single point of failure. If the hardware itself is damaged or compromised, recovery becomes even more challenging, potentially requiring a complete rebuild from scratch. Virtual Machine Recovery: Flexibility with Caveats Virtualization Benefits: VMs offer inherent advantages in disaster recovery. They are encapsulated files that can be moved, copied, and restored with greater ease than their physical counterparts. Snapshots and backups also simplify point-in-time restoration. Resource Competition: During a widespread outage, the very resources that VMs rely on (compute, storage, networking) may be strained. Recovery of numerous VMs can put additional stress on an already compromised infrastructure, slowing down restoration efforts. Hypervisor Vulnerabilities: While virtualization offers flexibility, it’s not impervious. Vulnerabilities in the hypervisor (the software layer managing VMs) can expose multiple virtual machines to compromise. Robust hypervisor security and patching are essential. A Tailored Approach to Recovery The best approach to disaster recovery in a hybrid environment is a multi-faceted one, considering the specific needs of both physical and virtual systems. Here’s a breakdown of key areas to focus on: Prioritization: Identify mission-critical systems, regardless of whether they are physical or virtual. These should be prioritized in your recovery plans. Backup Strategies: Maintain comprehensive backups for both physical and virtual systems. Consider off-site or cloud-based backups for resilience against localized disasters. Hardware Compatibility: If recovering critical physical systems, maintain a spare hardware inventory or have established relationships with suppliers to expedite replacements when necessary. VM Resource Planning: Have a clear understanding of resource requirements for restoring large numbers of VMs. Build in redundancy and scalability to avoid resource bottlenecks during recovery. Testing and Drills: Regularly test your recovery procedures for both physical and virtual systems. Identify and address any shortcomings proactively. 10 Ways Cristie Software Solves Hybrid System Recovery Challenges Dissimilar Hardware Technology: Cristie recovery software can automate the insertion of drivers when restoring systems to dissimilar platforms. This removes manual intervention to ensure that recovery can take place without interruptions. Legacy System Support: With system support back to Windows 2000 and many early editions of popular Linux distributions customers can confidently protect legacy systems. Bulk System Discovery: System recovery at scale presents many challenges including bulk system discovery which the Cristie Virtual Appliance (VA) can support in many ways including CSV input and API integration. Physical, Virtual & Cloud Recovery in any Direction: Cristie recovery and replication offers complete platform type flexibility between source and targets machines. Automated Provisioning: Systems can me migrated to new target platforms with automatic resource provisioning based on source machine parameters or adapted within the Cristie VA. Elimination of Manual Intervention: Cristie recovery automation features can eliminate manual interventions from the recovery workflow which are the most common cause of prolonged downtime following any disaster recovery scenario. Recovery Direct from Native Backups: Cristie recovery provides full system recovery directly from Rubrik, Cohesity, IBM and Dell Technologies native backups. Cost Effective Offline Replication: Cristie CloneManager replication software offers the choice of replicating systems to live running systems or to offline virtual machine image files which only require storage space. Offline system images can be mounted in the event of a disaster providing cost-effective protection for systems that do not need real-time failover. Cleanroom Recovery: The ability to restore systems to an isolated compute and network environment is a vital asset during a suspected cyberattack as it provides a cleanroom for cyber forensics and recovery image integrity testing, without risk of potential spread of malware to other production systems. Simulated Recovery Testing: Disaster recovery testing is vital to ensure you have confidence that your system recovery process will work when you need it most. Simulated recoveries can be scheduled through the Cristie VA to both monitor recovery success and measure recovery times to ensure that Recovery Time Objectives (RTO) can be met. The Evolving Landscape of Recovery As IT landscapes continue their shift towards cloud-based and highly virtualized environments, recovery strategies must also adapt. However, physical systems will continue to have their place in many organizations due to performance, legacy requirements, or security concerns. Understanding the distinct challenges of recovering both physical and virtual machines is crucial for ensuring effective disaster response in modern IT environments. It’s about preparedness, adaptability, and thorough understanding of your system’s unique dependencies that will pave the way for a swift and successful recovery, no matter the nature of the disruption. With Cristie Software many of these challenges can be resolved with advanced automation and recovery orchestration features within the Cristie VA. Download a free software trial to see the capabilities first hand for your backup environment.
재해 복구 계획의 상위 5가지 격차를 줄이는 방법

How to close the Top 5 Disaster Recovery Plan Gaps. A disaster recovery (DR) plan is an essential part of any organization’s risk management strategy. It outlines the steps that need to be taken in order to recover from natural disasters, cyber-attacks, or any other unexpected event that could disrupt normal operations. However, even with the best intentions, many disaster recovery plans often contain gaps that can hinder the organization’s ability to effectively respond to a crisis. Here are the top five gaps commonly found in disaster recovery plans with guidance on effective ways to ensure these gaps are closed for your organization: 1. Insufficient backup procedures: Data is often an organization’s most valuable asset, yet many disaster recovery plans have insufficient data backup procedures in place. Organizations should regularly back up their data and ensure that it is stored in a secure location. Without adequate data backup procedures, an organization’s ability to recover from a disaster is severely compromised. However, data is of little value without the supporting infrastructure and systems that enable critical business applications to utilize that data. Many organizations take regular data backups but overlook the protection and recovery of the underlying systems that must be recovered before any data can be processed. It is system recovery that very often presents the biggest challenge and primary reason for downtime following any DR scenario. The recovery of physical systems is inherently more complex and likely to involve manual intervention than virtual systems. Cristie Software recovery and replication solutions can eliminate manual intervention from physical system recovery and facilitate automated recovery at scale regardless of platform type. 2. Lack of regular testing: One of the most common gaps in disaster recovery plans is the lack of regular testing. Many organizations create a plan and then never revisit it until a disaster strikes. Without regular testing, it is impossible to know if the plan will work in a real-life scenario. Regular testing helps identify weaknesses in the plan and allows for adjustments to be made before a disaster occurs. The Cristie Virtual Appliance (VA) provides the ability to schedule regular simulated recoveries of complete systems to check recovery image and recovery process integrity. Simulated recovery will also verify recovery time performance to ensure that the recovery infrastructure can support Recovery Time Objectives (RTO). In addition, simulated recoveries can be made within a Cleanroom Recovery environment using the Isolated Networks Recovery feature of the VA. This provides a secure and safe environment for system recovery testing which is vital if a cyberattack is suspected. Systems can be analysed in the cleanroom recovery environment without risk of any contaminating production systems and networks. 3. Failure to account for cyber-attacks: While many disaster recovery plans focus on natural disasters, cyber-attacks are becoming increasingly common and can have a major impact on an organization’s operations. A gap in many plans is the failure to adequately address the potential for cyber-attacks and how to respond to them. The main attack vector involves encryption of vital data files and can take place rapidly once a malware payload is executed. Early detection of malicious file encryption is vital to limit damage and the spread of malware to other machines on the network. Cristie Software system recovery provides Advanced Anomaly Detection through the VA which can analyse the file structure of running systems against their last backup and detect any file structure changes which are characteristic of malicious encryption. This feature can be scheduled to run at any time and is external to the main system recovery workflow. If Advanced Anomaly Detection indicates that a system or systems have been compromised, effected systems can be restored to a cleanroom environment for cyber forensic analysis. 4. Inadequate communication protocols: Communication is key during a disaster, yet many plans fail to outline clear communication protocols. This can lead to confusion and delays in getting the appropriate information to the necessary stakeholders. Organizations should establish clear channels of communication and ensure that all employees are aware of the protocols. Identifying and understanding the various audiences that need to be reached during a DR scenario is a key aspect of developing a crisis communication strategy. This includes communicating with employees, IT staff, customers, vendors, suppliers, investors, government officials, industry regulators, and media throughout the event and recovery phases. The communication plan should outline the specific needs of each audience and designate appropriate spokespersons within the organization to effectively communicate with them. 5. Lack of stakeholder engagement: A successful disaster recovery plan requires the engagement of all stakeholders, including employees, customers, suppliers, and regulatory agencies. Many plans fail to adequately engage all stakeholders, leading to confusion and delays in the response to a disaster. Organizations should involve all relevant parties in the planning process and ensure that everyone understands their role in the event of a crisis. In conclusion, it is important for organizations to regularly review and update their disaster recovery plans to ensure that they are comprehensive and effective. The recovery of infrastructure and in particular physical systems is an area often overlooked and omitted from regular testing plans. By addressing these common gaps, organizations can better prepare themselves to respond to any unexpected event that may arise. Contact the Cristie Software team for more information on system recovery and replication to ensure that your organization has the best possible DR protection.
고급 이상 징후 탐지 및 클린룸 복구를 통한 사전 예방적 랜섬웨어 테스트
Proactive ransomware testing with Advanced Anomaly Detection & Cleanroom Recovery Having early warning of malicious file encryption is vital to limit the damage potential from a ransomware attack. Cristie Software Advanced Anomaly Detection can identify suspicious file structure changes by comparing live systems against meta data held from the most recent backup. Any changes that resemble malware encryption are flagged through the Cristie Virtual Appliance (VA) allowing system images for both physical, virtual, or cloud-based machines to be restored within a cleanroom environment for further analysis. Advanced Anomaly Detection runs separately to ongoing system recovery and replication schedules. Isolated Network Recovery for physical, virtual and cloud system integrity verification Cristie Software provide the ability to perform cleanroom recovery for any physical, virtual, or cloud-based system to an isolated network so that testing can be performed without impacting production systems and networks. This functionality is provided through the Cristie VA which implements an intermediary virtual machine to route traffic between the production network and any VLAN networks configured on the Isolated Networks Gateway within the VA. In the unfortunate event of a suspected cyber-attack, recovering system images to an isolated network established as a cleanroom environment becomes a critical step in the cyber forensic investigation process. This isolation serves several vital purposes, ensuring the integrity of the investigation and aiding in the identification and analysis of the attack. Preventing Further Damage with Cleanroom Recovery Cyber-attacks often involve malware or other malicious code designed to spread and cause further damage. By recovering systems to an isolated network, the risk of inadvertently activating or spreading the malware is minimized. This isolation prevents any potential reinfection of the network, protecting other systems and data from further harm. Enhancing Incident Response The recovery of systems to an isolated network also plays a crucial role in the incident response process. By analyzing the recovered system images, organizations can identify the root cause of the attack, assess the extent of the damage, and develop effective remediation strategies. This information is invaluable for preventing future attacks and strengthening overall cybersecurity measures. Physical machine recovery with Dissimilar Hardware technology The recovery of physical systems following an incident is often more challenging than virtual machines due to the tight coupling with underlying hardware. Differences between source and target physical machines can present device driver discrepancies that may hinder the boot process and require manual intervention. Cristie Software recovery solves this challenge with Dissimilar Hardware technology which automates the insertion of necessary drivers eliminating manual intervention. Physical machines can also be recovered to virtual or cloud targets and vice versa providing complete flexibility. Validating Recovery Time Objectives (RTO) An additional function of isolated network recovery is the measurement of RTO for specific systems to ensure that the current recovery infrastructure and processes can meet internal or external system recovery time objectives. This form of testing is particularly important within highly regulated industries such as financial services where critical business services may have maximum permitted outage periods before penalties are incurred. Simulated recoveries for RTO confidence and recovery image integrity testing Within the Cristie VA simulated recoveries can be scheduled automatically with comprehensive reporting on recovery performance plus notification of any irregularities which may impact system recovery during a disaster recovery scenario. The Cristie VA applies machine learning algorithms to analyze recovery log files to provide automated problem resolution where possible, and resolution guidance through the VA dashboard. Non-intrusive operating system and application upgrade verification Aside from measuring recovery performance, the use of an isolated network provides a test environment to verify operating system (OS) and application patches without impacting the production environment. Conclusion Recovering systems to an isolated network is an essential practice for organizations that need to ensure RTOs for critical systems meet internal and external benchmarks. For cyber forensics it provides a cleanroom recovery environment which ensures the integrity of the investigation, prevents further damage, facilitates thorough analysis, and enhances incident response. By following this best practice, organizations can effectively meet regulatory compliance, verify system upgrades outside of the production environment, respond to cyber-attacks, and strengthen their overall cybersecurity posture. Contact the Cristie Software team for a live demo of isolated network recovery and testing.
시스템 다운타임의 파급 효과: 기술이 흔들릴 때 산업이 무너지는 방법

시스템 다운타임의 파급 효과: 기술이 무너지면 산업이 무너지는 방법 오늘날과 같이 상호 연결된 세상에서 기업은 운영, 거래, 커뮤니케이션을 위해 기술에 크게 의존하고 있습니다. 이러한 중요한 시스템이 중단되면 그 결과는 심각하고 다방면에 걸쳐 나타날 수 있습니다. 시스템 다운타임의 영향은 단순한 불편함을 넘어 다양한 산업에 독특한 방식으로 파급되며 충격파를 불러일으킵니다. 헬스케어: 생명과 직결된 환자 진료에 차질을 빚다: 전자 건강 기록(EHR), 의료 기기, 통신 시스템은 의료 분야의 생명선입니다. 다운타임은 중요한 환자 데이터에 대한 액세스를 방해하고 진단을 지연시키며 치료 계획을 손상시킬 수 있습니다. 운영상의 혼란: 진료 예약부터 의약품 재고 관리까지, 의료 시설은 기능적인 IT 시스템에 의존합니다. 다운타임은 이러한 프로세스를 방해하여 잠재적으로 안전 위험으로 이어질 수 있습니다. 금융: 혼란에 빠진 시장은 거래를 놓치고 기회를 놓칩니다: 금융 시장은 매우 빠른 속도로 움직입니다. 다운타임은 거래 기회를 놓치고, 부정확한 금융 정보로 인해 궁극적으로 막대한 금전적 손실을 초래할 수 있습니다. 규제 준수: 업계 규제 당국은 중요한 서비스가 사전 정의된 영향 허용 범위 내에서 운영되기를 기대합니다. 운영 중단이 장기화되면 운영 복원력 지침을 위반하여 벌금이 부과될 수 있습니다. 침식된 신뢰: 투자자와 고객은 자신의 자금과 포트폴리오에 24시간 내내 안전하게 액세스할 수 있기를 기대합니다. 장기간의 시스템 중단은 금융 기관의 평판을 심각하게 훼손하고 고객 이탈을 초래할 수 있습니다. 소매 및 이커머스: 매출 손실로 인한 매출 손실: 온라인 상점이나 POS(Point-of-Sale) 시스템에 장애가 발생하면 소매업체는 소중한 거래를 놓쳐 직접적인 금전적 손실과 고객 불만을 초래하게 됩니다. 공급망 중단: 재고 관리, 주문 추적, 배송 스케줄링은 통합 시스템에 의존하는 경우가 많습니다. 다운타임은 공급망에 병목 현상을 일으켜 제품 부족과 배송 지연으로 이어집니다. 제조: 생산 라인이 멈춰 비용이 많이 드는 지연: 제조업체는 생산, 조립 및 품질 관리를 위해 고도로 자동화된 시스템을 사용하는 경우가 많습니다. 다운타임으로 인해 조립 라인이 중단되면 비용이 많이 드는 지연이 발생하고 납기를 놓칠 수 있습니다. 예측적 유지보수 방해: 많은 최신 공장에서는 장비가 고장 나기 전에 수리를 예약하는 예측 유지보수 시스템을 활용합니다. 다운타임은 이러한 예방 조치를 방해하여 예기치 않은 고장의 위험을 증가시킵니다. 운송: 환승 항공편 지연 및 취소로 인한 혼란: 항공사는 예약, 승객 체크인, 항공기 운항을 위해 전산 시스템에 크게 의존합니다. 시스템 장애는 비행기를 착륙시켜 승객을 발이 묶고 전 세계 항공편 스케줄에 차질을 빚을 수 있습니다. 물류 체증: 물류 회사는 배송 추적, 경로 최적화, 재고 관리를 위해 정교한 시스템을 사용합니다. 다운타임은 사각지대를 발생시켜 배송 지연, 잘못된 배송, 고객 불만족으로 이어집니다. 도미노 효과와 숨겨진 비용 시스템 다운타임은 단절된 공간에 존재하지 않습니다. 그 영향은 종종 산업 전반에 걸쳐 연쇄적으로 발생하여 공급망을 교란하고 경제 전반에 파급 효과를 일으킵니다. 또한 기업은 다음과 같은 숨겨진 비용에 직면하게 됩니다: 브랜드 손상: 운영 중단은 대중의 신뢰를 약화시켜 기업의 평판을 해칠 수 있습니다. 직원 사기 저하: 다운타임은 직원들의 불만과 생산성 저하로 이어질 수 있습니다. 사이버 보안 취약성: 재해 복구 노력으로 인해 사이버 범죄자가 악용할 수 있는 새로운 취약점이 발생할 수 있습니다. 복원력의 필수 요소 시스템 다운타임은 비즈니스 전반에 걸쳐 항상 존재하는 위험입니다. 안정적인 시스템 복구 솔루션, 탄력적인 IT 인프라, 사전 예방적 유지관리, 강력한 재해 복구 계획에 투자하는 것은 더 이상 선택 사항이 아니라 디지털 환경에서 운영을 보호하고 손실을 최소화하며 경쟁력을 확보하는 데 필수적입니다. 다운타임 완화를 위한 시스템 복구 및 복제 솔루션에 대해 자세히 알아보려면 Cristie 소프트웨어 팀과 상담하세요!
운영 복원력: 주요 규정 준수 보호 장치로서의 시스템 복구
운영 복원력: 핵심 규정 준수 보호 장치로서의 시스템 복구 운영 복원력은 현대 금융 산업 규정의 초석으로 부상했습니다. 이제 기업은 운영 중단을 방지할 뿐만 아니라 불가피한 문제가 발생했을 때 중요한 기능을 신속하게 복구할 수 있어야 합니다. 바로 이 점이 강력한 시스템 복구 전략의 핵심입니다. 컴플라이언스 영향 허용 범위에서 시스템 복구가 중요한 이유: 규제 당국은 기업이 가장 필수적인 서비스에 대해 엄격한 복구 시간 목표(RTO)와 복구 지점 목표(RPO)를 설정할 것을 기대합니다. 시스템 복구 솔루션은 이러한 까다로운 일정을 준수하고 데이터 손실을 최소화하는 데 매우 중요합니다. 시스템 복잡성: 최신 금융 시스템은 서로 연결된 애플리케이션, 플랫폼, 네트워크의 웹입니다. 효과적인 시스템 복구는 모든 중요한 구성 요소가 올바른 순서로 복원되고 종속성을 고려하도록 보장합니다. 복구 테스트: 단순히 계획을 세우는 것만으로는 충분하지 않습니다. 규제 기관은 복구 절차가 작동한다는 구체적인 증거를 요구합니다. 이를 입증하려면 테스트 및 시뮬레이션 기능을 갖춘 시스템 복구 도구가 필수적입니다. 써드파티 위험: 금융 업계에서 공급업체 의존은 현실입니다. 시스템 복구 전략은 타사 공급업체까지 확장하여 해당 공급업체가 복원력 요건을 준수할 수 있도록 해야 합니다. 시스템 복구 솔루션이 복원력을 보장하는 방법 다음은 운영 복원력 규정 준수를 위해 시스템 복구 솔루션에서 살펴봐야 할 몇 가지 주요 기능입니다: 자동화: 수동 복구 프로세스는 속도가 느리고 오류가 발생하기 쉬우며 복잡한 IT 환경에서는 적합하지 않습니다. 중요한 복구 단계를 자동화하는 솔루션은 신속한 대응과 안정적인 결과를 보장합니다. 유연성: 획일적인 접근 방식으로는 한계가 있습니다. 각 중요 서비스의 특정 요구 사항에 맞게 복구 프로세스를 조정할 수 있는 솔루션을 찾아 가장 중요한 시스템에 우선적인 관심을 기울여야 합니다. 적용 범위: 복구 솔루션은 환경의 다양성에 맞게 다양한 플랫폼(물리적, 가상, 클라우드), 레거시 시스템 및 운영 체제를 지원해야 합니다. 보고 및 문서화: 상세한 로그와 보고는 규제 기관에 복구 목표를 달성하고 선제적으로 테스트를 수행하고 있음을 입증하는 데 매우 중요합니다. 규정 준수 그 이상: 안심할 수 있는 시스템 복구: 규정 준수가 원동력이 될 수도 있지만, 시스템 복구는 단순히 규정 상자를 체크하는 것 이상의 이점을 제공합니다: 다운타임 최소화: 복구 속도가 빠를수록 고객에게 더 빨리 서비스를 제공하고, 평판을 보호하며, 손실을 방지할 수 있습니다. 사이버 위험 감소: 샌드박스 복구 옵션을 사용하면 공격 후 시스템을 안전하게 검증하여 재감염의 위험을 최소화할 수 있습니다. 비즈니스 연속성: 시스템 복구는 광범위한 재해 복구 전략의 핵심입니다. 핵심 사항: 강력한 시스템 복구 솔루션에 투자하는 것은 단순히 규정을 준수하기 위한 것이 아니라 모든 종류의 중단으로부터 조직을 미래에 대비하기 위한 것입니다. 시스템 복구를 운영 복원력 목표에 맞추는 방법에 대해 자세히 알아보고 싶으신가요? 지금 바로 문의하세요!
BMR 대 복제: RTO를 기준으로 재해 복구 경로 선택하기

BMR 대 복제: RTO를 기준으로 재해 복구 경로 선택 재해 복구와 관련하여 시스템을 복구할 수 있는 속도(종종 복구 시간 목표(RTO)로 정의)는 다운타임과 관련 비용을 최소화하는 데 매우 중요합니다. Cristie 소프트웨어는 RTO 목표를 달성할 수 있는 두 가지 강력한 도구를 제공합니다: 베어 머신 복구(BMR): 운영 체제, 애플리케이션, 데이터를 포함한 이미지 기반 백업에서 전체 시스템을 복원합니다. BMR은 Rubrik, Cohesity, Dell Technologies 또는 IBM의 기존 백업 솔루션에 추가할 수 있으며, 또는 독립형 옵션(CBMR)으로 완벽한 백업 및 복구 솔루션을 제공할 수 있습니다. CloneManager 복제: 실행 중인 시스템을 지속적으로 복제하여 신속한 페일오버를 위해 실시간에 가까운 사본을 제공합니다. 소스 시스템과 대상 시스템은 물리적, 가상, 클라우드 등 모든 플랫폼 유형이 가능합니다. 어떤 것이 나에게 적합할까요? 최적의 선택은 특정 RTO와 비즈니스 우선순위에 따라 달라집니다: BMR을 선택해야 하는 경우: 덜 공격적인 RTO: 복구 중 약간의 다운타임(몇 초가 아닌 몇 분)을 감내할 수 있는 경우. 비용에 민감한 경우: BMR은 대기 시스템을 가동할 필요가 없는 오프라인 복제를 제공하지만, 연속 복제 솔루션에 비해 예산 친화적인 옵션이 될 수 있습니다. 유연성: 필요한 경우 다른 하드웨어나 플랫폼으로 복원할 수 있어 복구 프로세스 중에 다양한 활용성을 제공합니다. CloneManager 복제를 선택해야 하는 경우: 까다로운 RTO: 단 1초의 다운타임이 중요한 경우, 복제는 실시간에 가까운 페일오버를 제공하여 비즈니스 연속성을 보장합니다. 중요 시스템: 다운타임이 길어질 수 없는 우선순위가 높은 시스템을 보호하세요. 자동화된 페일오버: 자동화된 페일오버 기능으로 수동 개입을 최소화하고 복구 속도를 높입니다. 고려 사항: 데이터 손실 허용 범위: 복제는 일반적으로 복구 목표 시점(RPO)이 낮기 때문에 재해 발생 시 데이터 손실을 최소화합니다. 비용 대 다운타임: 지속적인 복제 비용과 가동 중단 시간 연장으로 인한 잠재적인 재정적 영향을 비교 검토하세요. 하이브리드 접근 방식: 많은 조직에서 대규모 시스템 복구를 위해 BMR을 가장 중요한 시스템에 대한 복제와 함께 사용하여 보호와 비용 효율성의 균형을 맞추고 있습니다. 물리적 시스템은 일반적으로 복구 중에 수동 개입이 필요하므로 대규모로 물리적 시스템을 복구하려고 할 때 다운타임이 상당히 늘어날 수 있습니다. Cristie 소프트웨어는 물리적 시스템 복구에서 수동 개입을 제거할 수 있는 자동화 기능을 통해 이 문제를 해결했습니다. Cristie 차별화: Cristie두 솔루션 모두 다음과 같은 이점을 제공합니다: 광범위한 플랫폼 지원: 물리적, 가상, 클라우드 환경 전반에서 복구할 수 있습니다. 자동화된 워크플로: 자동화 및 오케스트레이션 기능으로 복구 프로세스를 간소화하세요. 테스트 및 검증: 기본 제공 테스트 도구로 DR 계획이 제대로 작동하는지 확인하세요. 어떤 길을 택하시겠습니까? 복구 요구 사항을 이해하면 강력한 BMR 기능과 시스템 복제 속도 중에서 정보에 입각한 선택을 할 수 있습니다. Cristie 소프트웨어는 특정 목표를 달성할 수 있는 솔루션을 제공합니다. 비공식 통화를 예약하여 RTO 및 비즈니스 목표에 부합하는 복구 솔루션을 설계하는 방법에 대해 논의하세요!
DR 플랜의 80%에서 가장 큰 구멍은 무엇인가요?
DR 계획의 80%에서 가장 큰 허점은 무엇인가요? 클라우드 컴퓨팅은 엔터프라이즈 컴퓨팅 환경을 지배하고 있으며 앞으로도 이러한 추세는 계속될 것입니다. 해시코프의 최근 보고서에 따르면 대기업의 90%가 멀티 클라우드 인프라를 도입한 것으로 나타났습니다. 그러나 가상화에 대한 이러한 집중은 시스템 복구와 관련하여 많은 재해 복구(DR) 계획을 소홀히 하고 있습니다. Cristie 소프트웨어는 기술 파트너가 고객의 DR 계획 중 80%에서 발견한 주요 격차를 해소할 수 있는 포괄적인 솔루션을 제공합니다. 가상화가 시스템 복구 계획에 방해가 되나요? 클라우드 컴퓨팅 도입의 급증은 가상 머신 시장의 성장을 이끄는 핵심 요인으로 작용하고 있습니다. 경량 애플리케이션이나 마이크로서비스 운영과 같이 가상 머신이 전통적으로 수행하던 특정 역할을 컨테이너가 대신하고 있지만, 리소스 집약적인 작업이나 전체 운영 체제 환경이 필요한 레거시 애플리케이션을 실행하는 데 가상 머신은 여전히 필수적입니다. 리서치 회사인 Global Market Insights에 따르면 가상 머신 시장 규모는 2023년에 95억 달러를 돌파했으며 2023년부터 2024년까지 약 12%의 연평균 성장률로 확장될 것으로 예상됩니다. 많은 최신 백업 솔루션이 가상 머신 보호에만 초점을 맞추고 있는 것은 어쩌면 당연한 일입니다. 안타깝게도 가상 머신을 배포하든 컨테이너를 배포하든 관계없이 이러한 기술은 모두 재해 발생 시 효율적인 복구 솔루션이 필요한 기본 물리적 머신에 의존합니다. 대규모 물리적 머신 복구는 엔터프라이즈 인프라 복구의 주요 과제로 남아 있습니다. 가상 머신은 복구와 복제에 있어 매우 유용합니다. 데스크톱에서 비교적 손쉽게 대체 클라우드 환경으로 대규모로 복제할 수 있기 때문입니다. 반면, 물리적 머신은 복구와 관련하여 자동화가 훨씬 덜 이루어지며 시스템을 빠르게 온라인 상태로 되돌리기 위해 수동 개입이 필요한 경우가 많습니다. P2P(물리적 머신 간) 복구가 필요한 경우, 소스 머신과 대상 머신이 동일한 하드웨어로 구축되지 않은 경우 장치 드라이버 충돌이 발생할 수 있습니다. 물리적 머신은 직접 연결된 스토리지 또는 네트워크 공유를 통해 부팅 이미지를 사용할 수 있어야 합니다. 모든 형태의 수동 개입은 단일 시스템에서는 허용될 수 있는 시간이 걸리지만, 많은 기업이나 데이터센터의 경우 물리적 서버 자산이 수백 개 이상에 달할 수 있습니다. 따라서 물리적 시스템 복구는 모든 형태의 시스템 중단에 따른 다운타임을 연장시키는 주범이 될 수 있습니다. Cristie 소프트웨어 시스템 복구 소프트웨어로 물리적 시스템 복구를 대규모로 가속화하세요. Cristie 소프트웨어는 물리적 시스템 복구 자동화에 중점을 두고 많은 조직이 수동 개입의 필요성을 제거하여 복구 워크플로를 크게 개선할 수 있도록 지원하고 있습니다. 당사의 소프트웨어는 iDRAC(Dell) 및 iLO(HP)와 같은 일반적인 IPMI(지능형 플랫폼 관리 인터페이스) 하드웨어 관리 솔루션과 통합됩니다. 대역 외(OOB) 시스템 관리의 경우, 가상 머신과 동일한 수준의 자동화를 통해 물리적 시스템을 관리할 수 있는 DMTF Redfish® 클라이언트 표준 라이브러리를 제공합니다. Cristie 복구 소프트웨어는 Rubrik, Cohesity, Dell, IBM의 백업 솔루션과 직접 작동하여 추가적인 백업 관리 오버헤드 없이도 원활한 시스템 복구 확장을 제공합니다. Cristie 가상 어플라이언스(VA)는 물리적, 가상, 클라우드 기반 서버 복구 및 복제를 모두 관리할 수 있는 단일 인터페이스를 제공합니다. 시스템 복제 및 복구는 물리적, 가상, 클라우드 대상 간에 어떤 방향으로든 수행되도록 구성할 수 있으며, 장치 드라이버 불일치 등 서로 다른 하드웨어 시나리오가 자동으로 처리됩니다. 요약 클라우드 컴퓨팅의 장점과 가상 머신 및 컨테이너화의 이점을 수용했다면, 인프라 내의 물리적 시스템이 사이버 공격이나 다른 형태의 중단으로 인해 손상된 경우 복구 프로세스를 고려해 보시기 바랍니다. 대규모 물리적 시스템 복구의 어려움으로 인해 다운타임이 장기화될 수 있으며, 이로 인해 재정적 영향과 고객 관계 및 브랜드 평판이 손상될 가능성이 있습니다. Cristie 소프트웨어 팀에 문의하여 물리적 시스템 복구 기능과 조직이 대규모 물리적 시스템 복구 문제를 해결하도록 지원하는 방법에 대해 자세히 알아보세요.
VMware에서 마이그레이션 간소화
VMware Cristie 소프트웨어는 대체 환경으로 이전하려는 고객을 위해 VMware에서 쉽게 마이그레이션할 수 있는 경로를 제공합니다. 가상화, 클라우드 관리, 엔드유저 컴퓨팅, 하이퍼 컨버지드 인프라 기술 분야에서 VMware가 우위를 점하고 있지만, 선도적인 분석 기관인 Forrester는 2024년에 기존 VMware 고객의 20%가 대안을 찾을 것으로 예측하고 있습니다. Cristie 소프트웨어로 VMware에서 다양한 환경으로 손쉽게 마이그레이션 Cristie 가상 어플라이언스(VA)와 결합된 크리스티 CloneManager 복제 및 마이그레이션 소프트웨어는 VMware 소스 머신을 다양한 대체 환경으로 간편하게 자동 마이그레이션할 수 있도록 지원합니다. 새로운 환경 내에서 대상 머신의 프로비저닝은 소스 머신 사양에 따라 자동화할 수 있으며, 마이그레이션 프로세스 중에 시스템 리소스 확장도 쉽게 적용할 수 있습니다. 단일 인터페이스에서 여러 시스템의 마이그레이션을 자동화하세요. 여러 시스템의 마이그레이션을 단일 인터페이스에서 물리적, 가상, 클라우드 타깃으로 관리할 수 있으며, Cristie VA 내에서 멀티테넌트 지원도 제공됩니다. 지원되는 대상 플랫폼에는 Amazon AWS, Microsoft Azure, Microsoft Azure Stack HCI, Oracle Cloud, Nutanix AHV, Kubernetes, Amazon S3 및 호환되는 대상이 포함됩니다. 최신 호환성 목록을 보려면 제품 지원 매트릭스를 참조하세요. 시스템을 온라인 및 오프라인 타깃으로 마이그레이션하고 복제하세요. CloneManager는 '온라인' 및 '오프라인' 마이그레이션 및 복제 대상을 모두 지원합니다. 타깃이 소스 시스템에서 즉시 인계할 준비가 된 시스템을 실행 중인 경우 '온라인'이라고 합니다. 온라인 대상은 실행할 준비가 되어 있고 작업을 매우 빠르게 인수인계할 수 있다는 장점이 있습니다. 가상 디스크 이미지 파일이라는 대안이 있습니다. 가상 머신은 물리적 머신의 시스템 드라이브를 단일 디스크 이미지로 캡처하는 것과 같은 방식으로 완전한 이미지로 캡처할 수 있습니다. 이미지 파일에는 OS 구성, 애플리케이션, 데이터를 포함한 모든 것이 포함됩니다. 시스템 복제 또는 마이그레이션은 실행 중인 머신이 아닌 프라이빗 또는 퍼블릭 클라우드 환경 내에 저장된 가상 디스크 이미지 파일로 수행할 수 있습니다. 이러한 이미지 파일을 유지 관리하는 데 스토리지와 컴퓨팅 리소스가 아닌 클라우드 스토리지 비용만 필요하므로 상당한 비용 이점이 있습니다. 오프라인 복제는 복구 시간 목표(RTO)가 덜 까다로운 경우 비용 효율적인 솔루션이 될 수 있습니다. 복제 후 네트워크 변경은 온라인 및 오프라인 마이그레이션 모두에 대해 스크립트로 작성할 수도 있습니다. 요약 VMware에서 다른 플랫폼으로의 마이그레이션을 검토하고 있다면 CloneManager 무료 평가판을 요청하여 마이그레이션 기능을 직접 검토해 보세요. CloneManager 및 Cristie VA의 기능에 대한 자세한 내용은 언제든지 라이브 데모를 제공하고 질문에 답변해 드릴 수 있는 Cristie 소프트웨어 팀에 문의하세요.
보험 업계의 디지털 트랜스포메이션을 위한 위험 감소.
Reducing risk for Insurance industry digital transformation. Cristie Software work with many insurance industry firms to provide system recovery and migration solutions to support disaster recovery and aid the move towards full digitalization. 2024 marks a period of significant change for the insurance industry with digital transformation and cyber resilience a key focus. Regulations such as DORA and NIS2 within the EU and similar Operational Resilience directives from the Bank of England require firms to overhaul their cyber resilience with full compliance by 2025. In the UK the Lloyds Blueprint Two initiative is driving digital transformation with all firms required to use phase one digital services from 1 July 2024. Supporting the transition from legacy systems. To remain competitive many firms are aiming to migrate legacy systems which may be up to 30 years old to new digital cloud-based platforms. This is necessary to remain relevant alongside the many Insurtech startups who have fully embraced a personalised digital experience and are rapidly acquiring market share. Legacy systems present maintenance challenges due to end-of-life components which often incur high support costs. Cristie Software system migration tools offer extensive support for legacy operating platforms and can assist the migration from physical systems to virtual or cloud-based targets. Once a replica has been made within a new modern operating environment, applications can be fully tested for compatibility before any cut-over is made. Digitalization and operational resilience in the insurance sector, two potentially opposing forces. The cloud comes with many advantages, but it is not without risk. Exposing digital services to the public internet serves to increase the attack surface for any firm. As AI technologies progress rapidly, attackers will gain the ability to develop larger-scale phishing and disinformation campaigns that are even more convincing. These threat actors will increasingly focus on targeting cloud environments to establish persistence and navigate between different segments of victim environments hosted across multiple clouds. Firms should consider hybrid solutions combining public and private cloud architectures to provide resilience and security. Private cloud solutions may also be vital where data sovereignty is important for regulatory compliance. Cristie Software system recovery and replication solutions offer the ability to recover systems in any direction between physical, virtual and cloud platforms, or set in place local replication targets that can offer fail-over in the event of a cloud service outage. What does the Lloyds Blueprint Two initiative mean to insurance firms in 2024? The Lloyds Blueprint Two initiative in partnership with Velonetic is delivering a new digital platform transforming the journey of placing risk and making claims for open market and delegated authority business for both brokers and insurers. Blueprint Two digital services will be delivered in two phases. From 1 July 2024, all market firms must use phase one digital services. By April 2025, the launch of phase two digital processing services will take place, marking a significant milestone for the market as it transitions into a completely digital environment. This transition will be further facilitated with the implementation of the Digital Gateway risk service, also scheduled to go live in April 2025. Once operational, both these initiatives will enable the market to fully support digital placement of risk, providing the necessary capabilities to operate in an entirely digital setting. How are compliance regulations impacting insurance firms in 2024? The Digital Operational Resilience Act (DORA) was finalized by EU authorities in November and is set to take effect from January 2025. DORA primarily focuses on financial firms including insurance companies. Furthermore, certain “critical” third-party Information Communication Technology (ICT) service providers will also be directly subject to some provisions of DORA. Any ICT service providers working with the financial sector can also expect to comply with regulatory requirements. DORA aims to enhance the resilience of businesses against technology-related risks, including disruptions to operations and data breaches caused by cybercriminals.Additionally, organizations operating in various sectors should carefully assess the applicability of the upcoming EU Network and Information Security Directive (NIS2) which became effective in January. All EU member states have until October 17, 2024, to incorporate it into their national frameworks. NIS2 strengthens the existing cybersecurity requirements faced by organizations covered under the original NIS Directive. Many organizations that were previously not subject to these rules will now find themselves bound by the new regulations. These regulations emphasize board-level governance of cyber risk and the need for adequate cybersecurity standards across the supply chain. This applies even to organizations based in the UK. How can Cristie Software help meet compliance directives? Cristie Software provides system recovery solutions designed for automated system recovery orchestration for both physical and virtual machines with the ability to undertake detailed system recovery simulations to assist with regulatory compliance. Cristie’s system recovery software can create fully functional copies of production systems within an isolated sandbox environment in minutes without the need for additional infrastructure. These sandboxes are easily accessible for multi-disciplinary teams to optimize workflows, validate change management procedures, and collect evidence of cybersecurity capabilities or weaknesses. In Summary System recovery can present challenges for insurance firms with physical systems often lacking the automation features that are taken for granted within virtual environments. Cristie recovery solutions can help overcome these limitations while providing complete flexibility to restore to and from any platform environment. Very often firms place disproportionate investment in cyber detection and prevention tools neglecting the last line of defense which is reliable system recovery. Cyberattacks are unfortunately an inevitability since many attack methods will gain access to user credentials. Contact our team to learn more about simplifying key aspects of infrastructure recovery, legacy system migration, and cyber resilience to meet the requirements of current operational resilience legislations.
Microsoft Azure 스택 HCI로의 시스템 마이그레이션 간소화

Microsoft Azure Stack HCI로의 시스템 마이그레이션 간소화 Azure Stack HCI(하이퍼 컨버지드 인프라)는 하이브리드 클라우드 시나리오를 지원하기 위해 Windows Server 기술과 Azure 서비스를 결합한 Microsoft에서 제공하는 솔루션입니다. 특히 데이터 주권 등의 이유로 프라이빗 HCI 및 하이브리드 클라우드 솔루션을 구축하려는 고객과 함께 엔터프라이즈 기반 내에서 Azure Stack HCI 마이그레이션 프로젝트가 증가하고 있는 것으로 나타났습니다. 지금까지는 자동화 도구의 부족으로 인해 IT 커뮤니티 내 시스템 관리자에게 여러 시스템을 Azure Stack HCI로 마이그레이션하는 것은 어렵고 시간이 많이 소요되는 작업으로 여겨져 왔습니다. Cristie 가상 어플라이언스를 사용하여 여러 시스템을 Microsoft Azure Stack HCI로 마이그레이션 Cristie 소프트웨어는 시스템을 Azure Stack HCI로 마이그레이션할 때 원활한 통합과 자동화된 프로비저닝을 제공하는 Cristie 가상 어플라이언스(VA) 내의 새로운 기능을 통해 마이그레이션의 문제를 해결했습니다. 이제 Cristie VA는 VMware, Nutanix, Amazon EC2, Oracle Cloud, Hyper-V를 비롯한 다양한 소스 플랫폼에서 또는 물리적 머신에서 직접 Azure Stack HCI 내에서 여러 시스템을 쉽게 프로비저닝할 수 있습니다. 소스 플랫폼 사양에 따라 시스템을 자동으로 프로비저닝하거나 VA 내에서 조정할 수 있으므로 수동 구성에 소요되는 많은 시간을 절약할 수 있습니다. Azure Stack HCI에 대한 관심 및 채택에 기여하는 요인 Microsoft Azure Stack HCI의 현재 인기와 채택 동향을 평가하려면 고객이 최근 업계 보고서, 고객 사례 연구 및 기술 설문조사를 검토하는 것이 좋습니다. 또한 Microsoft의 공식 발표 및 사용자 포럼을 확인하면 플랫폼에 대한 커뮤니티의 참여도에 대한 인사이트를 얻을 수 있습니다. Azure Stack HCI에 대한 관심과 채택에 기여하는 몇 가지 요소: 하이브리드 클라우드 채택: Azure Stack HCI는 하이브리드 클라우드 채택 추세에 맞춰 조직이 온-프레미스 데이터 센터와 Azure 클라우드에 걸쳐 일관된 인프라를 구축할 수 있도록 지원합니다. 이러한 유연성은 특정 규정 준수 요구 사항 또는 데이터 보존 문제가 있는 비즈니스에 유용합니다.Azure 서비스와의 원활한 통합: Azure Stack HCI와 Azure 서비스의 통합은 온-프레미스와 클라우드 모두에서 워크로드를 관리할 수 있는 통합 플랫폼을 제공합니다. 이 통합은 운영을 간소화하고 원활한 하이브리드 클라우드 환경을 지원합니다.확장성 및 유연성: Azure Stack HCI는 확장성과 유연성을 제공하여 조직이 변화하는 요구 사항에 따라 리소스를 확장할 수 있습니다. 이러한 적응성은 다양한 워크로드 및 리소스 요구 사항을 가진 비즈니스에 매력적입니다.Azure 관리 도구를 사용한 하이브리드 운영: Azure Stack HCI를 통해 조직은 하이브리드 환경 전반에서 일관된 운영을 위해 Azure 관리 도구를 사용할 수 있습니다. 이를 통해 리소스의 관리 및 모니터링을 간소화할 수 있습니다.에지 컴퓨팅 기능: Azure Stack HCI는 에지 컴퓨팅 시나리오에 적합하므로 짧은 대기 시간 및 오프라인 기능을 위해 에지에 애플리케이션을 배포하는 조직에 적합한 솔루션입니다.통합 가상화: 가상화를 위해 Hyper-V를 활용하는 Azure Stack HCI는 가상 머신 실행을 위한 친숙하고 강력한 가상화 플랫폼을 제공합니다.보안 및 규정 준수: Azure 보안 센터 및 기타 Azure 서비스와의 통합으로 보안 및 규정 준수 기능이 향상되어 엄격한 보안 요구 사항을 가진 조직의 문제를 해결.개선 및 업데이트: Microsoft는 Azure Stack HCI에 대한 업데이트 및 개선 사항을 정기적으로 릴리스하여 새로운 기능, 개선 사항 및 최신 기술과의 호환성을 도입합니다. 요약 현재 Microsoft Azure Stack HCI로의 마이그레이션 프로젝트를 진행 중이거나 향후 마이그레이션을 계획하고 있다면, Cristie 소프트웨어 팀에 문의하여 마이그레이션 자동화 기능에 대해 자세히 알아보세요. 시스템 마이그레이션 솔루션인 CloneManager®와 Cristie VA를 함께 사용하면 Azure Stack HCI 마이그레이션을 크게 간소화하여 많은 수동 개입 시간을 절약할 수 있습니다.
복구에 더 집중하기 위해 사이버 보안의 균형을 맞출 때가 되었나요?

Is it time to address your cybersecurity balance to deliver greater focus on recovery? Protecting your critical business data from cyber threats is more important now than ever. With the rise of ransomware and other cyberattacks, it could be time to address your cybersecurity balance. The National Institute of Standards (NIST) Cybersecurity Framework offers a comprehensive assessment model for companies to evaluate their cybersecurity posture based upon 5 core functions; 1. Identify, 2. Protect, 3. Detect, 4. Respond and 5. Recover. NIST recommend a balanced investment across all five functions, however, cybersecurity assessments often reveal that companies are investing 85% of their cybersecurity budget on functions 1 through 3 leaving only 15% for Respond and Recovery procedures. If we analyse the current top cybersecurity threats, it becomes clear that having solid recovery tools and processes in place is vital for all organizations. Introduction: Why It’s Urgent to Address Your Cybersecurity Balance There is no doubt that cybersecurity tools designed to Identify, Protect and Detect cyber threats are very important, but if we consider the range of threats common today it becomes clear that a cyber attack which can circumnavigate early detection will become a reality for most organizations. In these cases, a system recovery solution that can restore vital business systems and application data to a known clean point in time is vital to prevent lost revenue, maintain customer service, and avoid paying extortionate ransomware demands. Let’s now consider 6 common threat categories and their likelihood of evading early detection. Social Engineering. Social engineering persists as one of the most dangerous hacking methods utilized by cybercriminals, primarily because it exploits human mistakes rather than technical weaknesses. This heightened danger stems from the fact that deceiving a human is considerably simpler than breaching a security system. In 2023, social engineering tactics have featured prominently as a primary means of acquiring employee data and credentials. High profile cases such as the attack on MGM Resorts International where MGM’s hotel and casino operations were disrupted for several days resulting in losses of over $100 million is just one such example. Over 75% of targeted cyberattacks start with an email, phishing is one of the top causes of data breaches, followed use of any credentials successfully stolen. If cybercriminals have obtained employee credentials their actions can remain undetected until they are in a very strong position to present ransom demands. A solid recovery solution then becomes your only line of defense. Third-partly exposure. Cyber attackers can bypass security systems by infiltrating less-secured networks of third-party entities that hold privileged access to the primary target of the hacker. A significant instance of such a third-party breach occurred in early 2021 when hackers exposed personal information from more than 214 million accounts on Facebook, Instagram, and Linkedin. The hackers gained access to this data by compromising a third-party contractor named Socialarks, which was engaged by all three companies and held privileged access to their networks. Configuration Errors. Configuration errors can pose a significant cybersecurity threat. Configuration errors occur when settings or configurations of software, hardware, or network components are improperly configured, leaving vulnerabilities that attackers can exploit. These errors may result from oversight, misconfigurations, or lack of adherence to security best practices. A 2019 study by the Ponemon Institute Research Report Sponsored by AttackIQ revealed that 50% of IT professionals acknowledge a lack of understanding regarding the effectiveness of the cybersecurity tools they have implemented. This indicates that a significant portion of IT experts may not be consistently conducting internal testing and maintenance of their cybersecurity measures. Again, configuration errors leave the gates wide open with system recovery the only option for a successful resolution. Poor Cyber Hygiene. Poor cyber hygiene refers to the lack of good practices and behaviors related to online security. It involves neglecting fundamental steps and precautions that individuals or organizations should take to protect their digital assets and data. The possibilities for bad practice are wide ranging but common indicators of poor cyber hygiene include: Weak Passwords: Using easily guessable passwords or reusing passwords across multiple accounts without regular updates. Outdated Software: Failing to regularly update operating systems, applications, and security software, leaving vulnerabilities unpatched. Lack of Security Software: Not having antivirus or anti-malware software installed, or not keeping it up to date. Unsecured Networks: Using unsecured Wi-Fi networks without encryption or using default router credentials. Clicking on Suspicious Links: Falling for phishing attacks by clicking on links or opening attachments from unknown or suspicious sources. Ignoring Software Updates: Disregarding prompts to update software or delaying updates, leaving systems exposed to known vulnerabilities. No Data Backups: Neglecting to regularly back up important data, making it vulnerable to loss in case of ransomware or hardware failure. Sharing Sensitive Information: Sharing personal or sensitive information online without considering privacy settings or the security of the platform. Using Unauthorized Software: Installing and using unapproved or unauthorized software, which may contain security risks. No Employee Training: Failing to educate employees or users about cybersecurity best practices, making them more susceptible to social engineering attacks. Poor Access Controls: Allowing excessive user privileges, not implementing the principle of least privilege, and not revoking access promptly for former employees. Neglecting Physical Security: Ignoring physical security measures for devices, such as leaving computers or mobile devices unattended in public spaces. The list above serves to highlight the vast range of human factor vulnerabilities that can be classified as poor cyber hygiene, all of which have the potential of bypassing investments in tools related to functions 1 to 3 of the NIST Cybersecurity Framework. Cloud Vulnerabilities. A recent Forbes article sharing research from Oracle states that 98% of enterprises using public cloud have adopted a multi-cloud infrastructure provider strategy. A multi-cloud strategy offers several benefits such as removing single points of failure and preventing vendor lock-in, however, leveraging multiple cloud vendors widens the attack surface to the risk of security flaws and vulnerabilities. Forbes recommend that companies utilizing the cloud for infrastructure services pay particular attention to the following
이제 완전한 Rubrik 보안 클라우드 통합 기능을 갖춘 Rubrik용 Cristie 복구 RBMR
이제 완전한 Rubrik 보안 클라우드 통합 기능을 갖춘 Rubrik용 Cristie 복구 RBMR. Cristie 소프트웨어 시스템 복구 RBMR(Rubrik용)은 모든 Rubrik 클라우드 데이터 관리(CDM)로 보호되는 파일, 볼륨 및 머신의 자동 검색을 통해 Rubrik 보안 클라우드 통합 기능을 제공합니다. 고객은 Rubrik 제로 트러스트 데이터 보안의 이점과 Cristie 소프트웨어 시스템 복구의 완벽한 유연성을 결합할 수 있습니다. Cristie 가상 어플라이언스(VA)를 통해 모든 Rubrik 백업 개체를 원하는 복구 플랫폼으로 사용 가능한 시점으로 복원할 수 있습니다. 이러한 원활한 통합을 통해 Cristie VA의 강력한 시스템 복구 자동화 및 오케스트레이션 기능을 Rubrik Security Cloud에서 지원되는 모든 백업 작업에 적용할 수 있습니다. Rubrik 보안 클라우드 - 모든 Rubrik 고객을 위한 사이버 회복탄력성의 미래. Rubrik은 모든 Rubrik 고객이 엔터프라이즈, 클라우드 및 SaaS 환경 전반에서 시스템 리소스를 모니터링, 관리 및 보호할 수 있는 통합 대시보드로서 2022년 8월에 Rubrik Security Cloud의 일반 제공을 발표했습니다. Rubrik Security Cloud(RSC)는 Rubrik 클러스터를 포함한 모든 데이터 보호 리소스에 대한 제어 기능을 제공합니다. RSC는 SaaS 기반이므로 고객은 최신 기능과 서비스가 제공되는 즉시 즉시 액세스할 수 있습니다. RSC는 Rubrik CDM과 함께 작동하여 고객 인프라 내의 모든 CDM 보호 개체에 대한 범용 보기 및 제어 기능을 제공합니다. RSC는 모든 신규 Rubrik 배포의 기본 인터페이스이며 2024년 6월 이후에는 모든 Rubrik 설치를 위한 단일 관리 솔루션이 될 것입니다. Cristie 소프트웨어 Rubrik용 RBMR - 제로 트러스트 데이터 보호와 고급 인프라 복구를 결합한 솔루션입니다. Rubrik 보안 클라우드는 제로 트러스트 원칙을 기반으로 설계되어 데이터 수준에서 위협을 사전에 억제합니다. Rubrik의 기본 제공 불변성, 보안 프로토콜, 논리적 격리, 암호화, 역할 기반 액세스 제어, 다단계 인증 및 통합 서비스 구현은 모두 함께 작동하여 데이터의 무결성과 접근성을 유지합니다. Cristie 소프트웨어의 Rubrik용 RBMR 시스템 복구가 추가되면서 모든 물리적, 가상 또는 클라우드 대상에 대해 단 10분 만에 시스템을 복구할 수 있는 다양한 시스템 복구 도구가 추가되었습니다. RBMR의 강력한 자동화 및 복구 오케스트레이션 기능은 기존 시스템 복구 방식에 비해 관리 오버헤드를 100시간이나 줄일 수 있습니다. 사이버 공격 후 시스템을 신속하게 깨끗한 상태로 복구할 수 있는 능력은 운영 복원력을 보장하고 매출 손실을 방지하며 고객 경험을 유지하는 데 필수적입니다. Cristie RBMR은 Rubrik 보안 클라우드와 함께 작동하며, Rubrik 보안 클라우드 내에서 추가적인 백업 관리가 필요하지 않아 완벽한 시스템 복구 보호 기능을 제공합니다. 전체 RSC 통합은 Cristie VA 릴리스 4.8.1 이상에서 사용할 수 있습니다. Cristie 소프트웨어에 문의하여 Rubrik Security Cloud 인프라에 Cristie 소프트웨어 RBMR을 포함할 때의 이점에 대해 자세히 알아보세요. Cristie Software는 모든 IT 환경에 빠르고 효율적인 시스템 복구를 제공하는 시스템 복구 솔루션을 제공합니다. 버튼 클릭 한 번으로 대규모 시스템 복구를 수행할 수 있습니다. Cristie 복구 오케스트레이션 기능은 최소한의 개입으로 복잡한 계층형 아키텍처를 최대한 빠르게 복구할 수 있도록 보장합니다. 또한, 상세한 시스템 복구 시뮬레이션을 수행할 수 있는 기능을 통해 Cristie 고객은 SLA 또는 규정 준수에 대한 자체 평가 요건을 충족할 수 있는 RTO 및 RPO 기능에 대한 확신을 가질 수 있습니다. 저희 팀에 연락하여 RBMR이 Rubrik Security Cloud와 함께 작동하는 방법을 알아보고 조직에 가장 효율적인 시스템 복구 프로세스를 배포하기 위한 첫걸음을 내딛으세요.
금융 부문 사이버 보안에서 인공지능(AI)과 머신러닝(ML)의 역할.
The role of artificial intelligence (AI) and machine learning (ML) in financial sector cybersecurity. The banking industry has been an early adopter of AI (Artificial Intelligence) and machine learning (ML) employing the technology in many applications to enhance operations and customer experiences. Areas to improve customer service such as document verification and processing, voice and speech recognition, chatbots and virtual assistants, plus predictive analytics and personalization have been in use and gaining sophistication for some time. AI has also been an established business tool in a security context to assist in the identification of irregular transactions indicating potential fraud. These types of high-volume, less sophisticated crimes lend themselves to the use of AI due to its strength in spotting patterns in large datasets. AI presents an effective means to tackle low-level crime quickly and efficiently for the scale that banks and payment businesses operate on. It also can play a key role in identifying suspicious (phishing) emails. However, it is the extended application of AI and ML in the fight against cybercrime which is gaining significant attention. The application of AI and ML in anomaly detection. AI and ML can continuously monitor network and system activities to detect unusual or suspicious behavior. When deviations from established baselines are identified, alerts can be generated for further investigation. The development team at Cristie Software has utilized ML technologies to offer an advanced system for detecting unusual file activity during the system recovery and replication phases. System backups are a critical defense against ransomware, and the backup procedure presents an excellent chance to compare the structure of files between successive backup images. While some files regularly change as part of normal business operations performed within their associated applications, the malicious encryption of files typically follows identifiable patterns. It is these patterns that Cristie Software’s anomaly detection technology aims to recognize, providing an early warning of a potential cyber attack in progress. Learn more in our earlier article covering our application of ML in advanced file anomaly detection. AI and ML have a significant and evolving role in financial sector cybersecurity. AI and Ml play a significant and evolving role in cybersecurity; anomaly detection is just one key area where the strength of these technologies come to the fore. Here are 10 additional key roles and applications of AI and ML in the field of financial sector cybersecurity: Threat Detection and Prevention: AI-powered systems can analyze vast amounts of data to identify patterns and anomalies indicative of potential cyber threats that might go unnoticed by traditional rule-based systems. AI and ML driven threat detection tools can recognize known malware and viruses and can also identify zero-day vulnerabilities by analyzing behavior patterns. User and Entity Behavior Analytics (UEBA): AI can analyze user and entity behavior to identify unauthorized or suspicious activities. It can spot unusual login patterns, access to sensitive data, or deviations from established usage patterns. Phishing Detection: AI can help in identifying phishing attempts by analyzing email content, sender behavior, and other indicators. It can reduce false positives and improve the accuracy of identifying phishing emails. Automated Incident Response: AI can automate incident response processes by providing real-time threat analysis and immediate actions to mitigate threats. This can help organizations respond to threats faster and reduce the impact of security incidents. Predictive Analysis: AI can use historical data to predict future security threats and vulnerabilities, enabling proactive measures to be taken to prevent attacks. Vulnerability Management: AI can assist in identifying and prioritizing vulnerabilities within a network or system, helping security teams focus their efforts on critical areas. Security Automation: AI can automate routine security tasks, freeing up security personnel to focus on more complex and strategic aspects of cybersecurity. Natural Language Processing (NLP): NLP-powered AI can help in analyzing and understanding unstructured data, such as security logs and reports, to extract actionable insights. Security Analytics: AI-driven security analytics platforms can provide a holistic view of an organization’s security posture by aggregating and analyzing data from various sources, facilitating better decision-making. Adaptive Security: AI can adapt security measures based on evolving threats and changing network conditions, providing a more dynamic and responsive defense mechanism. Financial sector regulatory interest in AI and ML. Regulators are also becoming increasingly interested in the risks and benefits presented by AI and ML technology. In 2020 the Bank of England (BoE) and the Financial Conduct Authority (FCA) launched the Artificial Intelligence Public-Private Forum (AIPPF) and issued their final report which represents the results of more than a year’s worth of meetings, workshops, and discussions focused on Data, Model Risk and Governance aspects of AI adoption. The BoE followed in October 2022 with the discussion paper DP5/22 – Artificial Intelligence and Machine Learning which aims to respond to the AI Public-Private Forum final report and gather further feedback on the regulators’ views of the risks and benefits of the use of AI, as well as how the current regulatory framework applies to AI and ML The UK FCA/PRA regulations governing Operational Resilience and the European Union (EU) Digital Operational Resilience Act (DORA) are both comprehensive operational resilience regulations that are seen as significant drivers of substantial investments in financial sector cybersecurity. They are regarded as the most extensive and impactful operational and cybersecurity regulations globally. Learn how Cristie Software can complement Operational Resilience and Cybersecurity practices for the Financial Sector. It is important to note that while AI has many benefits in financial sector cybersecurity, it’s not a panacea. It should be used in conjunction with other data security practices and technologies to create a comprehensive cybersecurity strategy. Moreover, AI systems themselves need to be protected from adversarial attacks to maintain their effectiveness in defending against cyber threats. Since its inception, Cristie Software has been dedicated to automating system recovery, replication, and migration using cutting-edge techniques and the latest computing advancements. Incorporating ransomware detection driven by Machine Learning (ML) is a seamless expansion of our disaster recovery capabilities and represents a unique strength of our system recovery tools.
미국 금융 부문에서 운영 회복탄력성의 중요성
The importance of Operational Resilience in the U.S. financial sector. Operational resilience is a critically important topic for the financial sector. It refers to a financial institution’s ability to withstand and adapt to disruptions such as cyberattacks, natural disasters and pandemics while continuing to provide essential services to its customers and meet regulatory obligations. We have recently highlighted regulatory activity in the UK and APAC, however governing bodies worldwide are drafting their own equivalents or adding new legislation to extend and enforce existing regulations. The U.S. is no exception with all three federal banking regulators simultaneously issuing the Supervisory Letter SR 20-24: Interagency Paper on Sound Practices to Strengthen Operational Resilience to the officer in charge of supervision at every federal reserve bank in November 2020. Although the practices outlined in this initial letter were directed to the largest and most complex domestic US financial firms, it is important for all financial firms to strengthen their operational resilience as new directives are being drafted for many additional FINSERV jurisdictions. Operational resilience remains a top priority for regulators as illustrated by the inclusion of Information Security and Operational Resiliency within the 2023 Examination Priorities announced by the U.S. Securities and Exchange Commission. Cristie Software has broad experience working with financial institutions to deliver automated large scale system recovery with the ability to orchestrate detailed recovery simulations and support the self-assessment requirements of regulatory compliance. Of course, operational resilience has implications extending way beyond meeting regulatory compliance. Below we highlight 10 key areas that illustrate how important improving operational resilience is for all firms in the U.S. financial sector. 10 key reasons why Operational Resilience is crucial in the U.S. financial sector: Protecting Customers and Investors: Financial institutions handle the money and investments of individuals and businesses. Operational failures can result in financial losses for customers and investors, erode trust, and damage a financial institution’s reputation. Maintaining Market Stability: The financial sector plays a central role in the stability of the broader economy. Disruptions in financial operations can have cascading effects on other sectors, potentially leading to systemic crises. Regulatory Requirements: Regulatory agencies impose strict requirements on financial institutions to ensure they have robust operational resilience measures in place. Non-compliance can lead to fines, legal consequences, and reputational damage. Cybersecurity Threats: Financial institutions are prime targets for cyberattacks. Operational resilience includes cybersecurity measures to protect sensitive customer data and financial systems from breaches and cyber threats. Complexity of Financial Services: The financial industry is highly complex, involving various products, services, and interconnected systems. Ensuring operational resilience is a way to manage this complexity and reduce the risk of operational failures. System recovery following any disruption will need to be orchestrated to ensure complex tiered systems are recovered in the correct sequence. Cristie System Recovery automation and orchestration tools can help to facilitate system recovery within complex financial systems. Customer Expectations: In the digital age, customers expect uninterrupted access to financial services. Operational resilience is crucial to meet these expectations, especially with the increasing reliance on online and mobile banking. Customer Experience (CX) is a major area of focus in the competitive FINSERV market. Global Interconnectedness: Financial institutions often operate on a global scale, making them vulnerable to disruptions in different parts of the world. Operational resilience helps mitigate the impact of global disruptions. Legal and Regulatory Reporting: Financial institutions are required to report their financial status and operations accurately and transparently. Operational resilience ensures that they can fulfil these reporting requirements even in challenging circumstances. Cristie Recovery and Replication software provides detailed reporting to assist with regulatory self-assessment plus the ability to perform regular recovery simulations to validate disaster recovery processes and recovery time expectations. Competitive Advantage: Institutions with strong operational resilience can differentiate themselves in the market. Customers and investors are more likely to trust and do business with institutions that demonstrate a high level of resilience. Risk Management: Operational resilience is a fundamental aspect of overall risk management in the financial sector. It helps identify, assess, and mitigate operational risks effectively. Learn how Cristie Software can simplify Operational Resilience for the U.S. financial sector. In summary, operational resilience is a foundational element of the U.S. financial sector. It encompasses strategies, processes, and technologies designed to ensure that financial institutions can continue to operate effectively and protect the interests of their stakeholders in the face of various threats and disruptions. It’s not just a regulatory requirement; it’s a key component of business continuity and long-term success in the industry. Contact our team to learn more about simplifying key aspects of your system recovery to help meet the requirements of operational resilience legislation. Visit the CloneManager® and System Recovery product pages for more information regarding the Cristie Software suite of solutions for system recovery, replication, migration, and ransomware protection.
빠르고 효율적인 시스템 복구 방법

How to achieve fast and efficient System Recovery. Keeping system recovery time to a minimum following any outage is vital for many reasons; loss of revenue, poor customer experience, and diminished brand reputation are high on the list. There are several factors that affect system recovery time which are common to all outage scenarios, but there are additional factors that impact recovery time significantly if the outage is a result of cybercrime. We will consider here several scenarios impacting system recovery time and highlight ways in which Cristie Recovery solutions can reduce or mitigate these factors. Storage and network selection for optimum System Recovery performance. System recovery time in every scenario will be dependent upon the type of storage used to store the recovery image and the speed of the network connecting the storage device to the target system. Locally attached solid state storage such as a flash drive connected directly to the target system, or a flash-based storage array connected over a high-speed storage area network (SAN) will generally offer the fastest possible recovery. At the opposite end of the performance scale will be recovery images based on tape media and/or cloud-based images where recovery time will be governed by network connection bandwidth, and the performance of the cloud infrastructure serving the files. Careful consideration must therefore be made to ensure the chosen storage platform and network performance will meet Recovery Time Objectives (RTO). System readiness and preparation for System Recovery. The next major factor to consider is the recovery target type and the speed with which different target machines can be provisioned. At the most basic level, there are three target machine options; physical machines dedicated to a specific application or application sets, virtual machines (VMs) that can be configured with specific compute, network and storage resources from their underlying architecture, and cloud-based targets which can be thought of as VMs hosted by a 3rd party provider outside of the corporate network. Physical machines will typically be the slowest to provision as standby machines may need additional configuration to meet application requirements unless machines have been configured in advance. Physical standby machines may be located at a hosting facility which can introduce additional provisioning delays and/or travel time to the co-location site. Virtual machines hosted locally or in the cloud are typically much faster to provision, however, recovering to dissimilar platforms can introduce several compatibility issues that can extend recovery times significantly. Many of the complications encountered when recovering systems to dissimilar platforms can be overcome without the need for manual intervention using Cristie Recovery software automation features. Realistic System Recovery times without dedicated recovery software. In the absence of a complete and up-to-date system configuration image, system recovery for even a single system can easily extend from hours into days. Building a standby system from scratch will require physical configuration followed by operating system (OS) installation and most likely critical OS updates and security patches before applications can be installed. Likewise, applications may require patch updates ahead of installing any operational data and user configurations. For this process to run as smoothly and quickly as possible, all required OS and application installation files need to be readily available, either as physical media or via an external source such as an installation package manager. After the entire OS and application stack have been successfully installed there will often be a need for further configuration to add the target machine to the appropriate networks, and potential security configurations for any firewall and cybersecurity tools deployed. If this recovery process must be repeated for multiple systems, then clearly a large support team would be required to ensure RTOs are kept to a minimum. Installing and using a reliable and efficient system recovery solution which can automate recovery steps is therefore vital to avoid recovery times escalating into days or even weeks of downtime. Customers using Cristie Recovery software indicate real world recovery times as low as 10 minutes, assuming all best practices are followed. Eliminating manual intervention, the biggest cause of System Recovery delay and RTO failure. Let us assume we have complete and up-to-date system configuration images for the systems we wish to recover. We are at great advantage in comparison to the scenario where we must build the recovery targets from scratch. However, there are still many opportunities for configuration issues to cause system recovery delays, especially when source machines and recovery targets are using dissimilar hardware. Generally, these issues will require manual intervention, extending recovery delays, and adding additional overhead to the total cost of downtime. Cristie Recovery software excels in eliminating manual intervention as much as possible through a range of powerful and intelligent recovery automation features that enable systems to be recovered, to and from, dissimilar platforms quickly and easily. System recoveries can be performed efficiently between physical, virtual and cloud platforms in any direction. Automating system recovery with driver insertion and pre- & post- boot operations. When migrating a system to a dissimilar platform there will inevitably be subtle differences in the underlying hardware that will require platform specific device drivers to enable the target machine to boot successfully. Traditionally these vital driver files would require manual intervention to complete installation plus additional reboot cycles before the target is ready to boot the recovery image without exceptions. Cristie Recovery software overcomes this time-consuming barrier by automatically inserting boot critical drivers for many common operating platforms, in addition to providing the ability to pre-configure custom driver configurations for target systems. Cristie Recovery software also provides extensive automation for additional pre- boot tasks such as automatic resource sizing and provisioning when migrating from physical to virtual machines, and post-boot actions such as automating network configuration changes and performing custom startup scripts for recovery systems. Implications for System Recovery following a cyber-attack. If a system outage has resulted from a physical failure or natural disaster, you can generally assume that your operational data is free from malicious corruption. There may be incomplete transactions prior to the
아시아 태평양 금융 부문의 운영 복원력

Operational Resilience in the Asia Pacific financial sector. Operational resilience will continue to be a key regulatory focus for the Asia Pacific (AP) financial sector throughout 2023 and beyond. All businesses and regulators in the area continue to place increased emphasis on operational resilience and the management of disruptions to critical financial services. Although some AP jurisdictions may lag the advancements achieved in other geographies, we see that the pace is increasing with regulatory pressure forcing the region to place more emphasis on all aspects of operational and cyber resilience. Trends driving Operational Resilience regulations within the Asia Pacific region. There are several factors driving the need to improve operational resilience in the Asia Pacific region. The acceleration of digitalisation which took place during the COVID-19 pandemic is very significant as it resulted in an increase in partnerships between financial firms and third-party operators. This has driven dependencies on a much wider range of suppliers and stakeholders; however, operational resilience directives place an emphasis on the mitigation of all 3rd party risks for financial operators. In addition, the recently complicated geopolitical environment, and the potential economic downturn that could result from any significant disruption to financial services within the AP jurisdictions are also key drivers of the need for an increased focus on operational resilience and improved regulation. A hive of financial sector regulatory activity in the Asia Pacific region. Since the Basel Committee on Banking Supervision (BCBS) issued their Principles for Operational Resilience in March 2021 we have seen several regulators in the AP region publishing official or consultive versions of control materials which implement the BCBS principles. In 2022, the Hong Kong Monetary Authority (HKMA) published one new Supervisory Policy Manual (SPM) and two revised SPMs to implement the operational sustainability principles of the 2021 BCBS directives. Within the past month the Financial Markets Authority of New Zealand – Te Mana Tātai Hokohoko (FMA) has released a consultation document proposing the introduction of new standard conditions for additional financial market licence holders, focused on business continuity and technology systems. We are seeing a hive of activity taking place across the entire AP region which indicates a huge drive towards meeting the regulatory goals and deadlines. When will the Asia Pacific Operational Resilience regulatory directives come into force? Although there are regional variations, March 2024 is a common deadline for many AP region regulatory directives to enter into full force. The FMA Financial Market Infrastructures Act 2021 of New Zealand is just one example which follows this timeline. We have seen many additional directives following suit. For instance, the standards for designated Financial Market Infrastructures (FMIs) which were issued on 27 July 2023 under section 31 of the Financial Market Infrastructures Act 2021 by the Reserve Bank of New Zealand and the Financial Markets Authority also come into effect starting from 1 March 2024. Clearly there is a sense of urgency across the region intended to ensure that affected firms have implemented all necessary procedures to facilitate operational resilience within this timeframe. Cristie Software can simplify Operation Resilience compliance for Asia Pacific financial firms. Cristie Software can simplify key aspects of financial system infrastructure recovery to help meet the requirements of new operational resilience directives. Financial systems involve complex interdependent IT configurations built with redundancy to provide maximum availability. Implementing, supporting, and securing these systems presents challenges due to their vast scale. For example, an isolated service such as payments may be supported by several financial companies with thousands of server instances across many different geographies. Cristie Software’s recovery and replication solutions provide a range of methods to facilitate bulk server mapping and recovery which ensures that large scale deployments can be recovered in the right sequence and within descried timeframes. Contact Cristie Software to discuss your Operational Resilience challenges. Although March 2024 is rapidly approaching, it is not too late to enhance your system recovery procedures. Cristie Software provides system recovery solutions designed for automated large scale system recovery orchestration with the ability to undertake detailed system recovery simulations and support the self-assessment requirements of regulatory compliance. Contact our team to learn more about simplifying key aspects of infrastructure recovery to help meet the requirements of all new regional operational resilience directives.
Rubrik 사용자를 위한 베어메탈 복구(RBMR)
Bare-metal recovery (RBMR) for Rubrik users. Cybersecurity and disaster recovery (DR) requires a layered approach to ensure all elements of a company’s IT infrastructure are protected. Customers can rely on Rubrik to cyber-proof their enterprise data on physical systems and virtual machines with air-gapped, immutable, access-controlled backups that can protect business critical data such as databases, file systems, containers and more. The addition of Cristie Software RBMR bare-metal recovery to any Rubrik installation extends system recovery capabilities to restore entire systems, including all operating system, user, application, and disk partitioning specifications to any physical, virtual or cloud recovery target. Perform complete system recovery direct from Rubrik backups. RBMR provides complete system recovery from your existing Rubrik backup jobs without the need to configure any additional backup tasks. However, the advantages do not stop with seamless system recovery. The addition of RBMR also provides powerful system recovery automation and DR orchestration features that can provide an essential lifeline in the event of a cyberattack or other system outage. Furthermore, these features offer a variety of techniques to help restore large scale server estates in the most labour free and time efficient manner. Automating system recovery to dissimilar platforms for Rubrik users. Rubrik integration with RBMR allows Rubrik to perform bare-metal recovery to any operating system that is supported by RBMR. RBMR works by booting a “recovery environment” which contains an operating system image with all required RBMR tools and scripts to facilitate the recovery process. Recovery targets do not need to be the same platform type. Cristie’s Dissimilar HardWare (DHW) technology can take care of any boot-critical driver discrepancies by automatically providing a path to additional drivers required to successfully boot the target system. This can eliminate the manual intervention steps that are typical when migrating systems between dissimilar platforms. Bare-metal recovery (BMR) should form part of any robust DR strategy. Having a dependable DR strategy in place including BMR ensures that you can get your system(s) back in the same state as they were before backup, without having to perform additional patches, pre-recovery setup or post-recovery remediation. Typical BMR challenges include: Finding the right operating system version (OS). Re-applying OS and application patches to the correct level. Finding and reinstalling drivers for specific hardware. Reinstalling the backup agent. Remembering and recreating disk partitioning configurations. RBMR Rubrik recovery orchestration for complete DR process customization. RBMR can resolve all typical BMR challenges but also take your DR process to the next level through the extensive automation and recovery orchestration features which can facilitate tiered system recovery with as many pre and post recovery steps as you require. In-depth fine tuning of system recoveries and replications, including reboots, post recovery scripts, manual tasks, and custom choices for actions in the event of stage failures, are made possible by RMBR orchestration tasks. The Cristie VA-Orchestration Guide provides detailed information on task configuration and the automation capabilities inherent within RBMR for Rubrik. Cristie Rubrik Bare-metal Recovery (RBMR) for Linux/Unix Hosts – Technical White Paper. Rubrik and Cristie Software have developed a Technical White Paper ideal for field and technical support engineers, customer architects and solution engineers who want to have a better understanding of how Cristie Rubrik Bare-metal RBMR Recovery for Linux/Unix works. This deep dive document describes how to leverage RBMR in specific physical server recovery and disaster recovery scenarios and includes many best practices for configuration. In summary. The combination of Rubrik zero-trust data security and RBMR bare-metal recovery from Cristie Software will ensure that your business operations are truly unstoppable in the event of a cyberattack of any other disaster scenario. Contact our team to learn more about RMBR for Rubrik and our capabilities to help you restore our IT infrastructure regardless of scale.
금융 부문의 운영 복원력 간소화
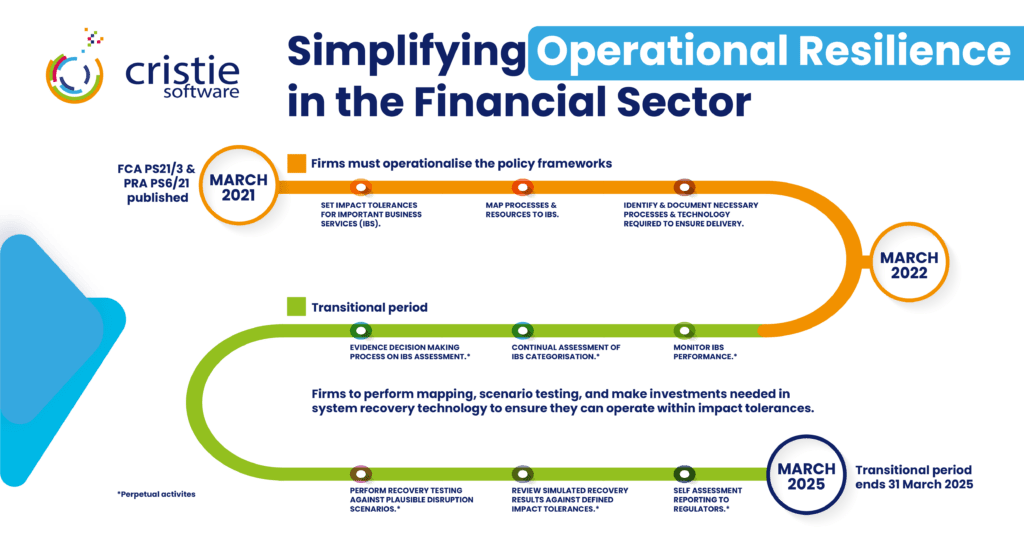
Simplifying Operational Resilience in the Financial Sector. The Financial Conduct Authority (FCA) and Prudential Regulation Authority (PRA) respective policy statements PS21/3 & PS6/21 published in March 2021 established the frameworks for relevant firms within the financial sector to implement measures that would ensure Operational Resilience for important business services. The practical implications of achieving compliance with these directives present far-reaching obligations for applicable firms and prescribe a significant investment in planning, processes, and technologies. At the highest level the directives required firms to operationalize the following fundamental parameters during the period from March 2021 to March 2022. Set customer, firm, and market impact tolerances for important business services in severe but plausible scenarios. Impact tolerance: means the maximum tolerable level of disruption to an important business service, including the maximum tolerable duration of a disruption. Map processes and underlying resources to important business services. Identify important business services and document the necessary processes, people, facilities, technology, and other resources required to deliver the important business services. March 2022 onwards marks the transition period during which firms must set in place all measures required to be compliant with the directives when the policies come fully into force in March 2025 Setting impact tolerances, scenario testing and self-assessment reporting. Disaster recovery (DR) planning, testing, and reporting are core components of achieving operational resilience and these functions map directly into the policy tasks of setting impact tolerances, scenario testing and self-assessment reporting. Cristie Software system recovery and replication solutions can simplify these tasks significantly through the recovery automation, orchestration, and reporting features of our products. Cristie Software BMR Recovery can act standalone or as an extension to leading backup solutions. Cristie bare machine recovery (BMR) software provides high performance system recovery as a standalone solution or as an extension to leading backup solutions from Dell EMC, IBM, Cohesity and Rubrik. System Recovery, Orchestration, and Automation at scale. Financial systems involve complex interdependent server and storage configurations that are built with redundancy to provide the utmost resilience. The deployment, maintenance, and protection of these systems presents specific challenges due to scale. For instance, a single service such as payments may be supported by thousands of server instances across multiple geographies for many financial firms. Recovery and replication solutions from Cristie Software offer several mechanisms to facilitate bulk server mapping and recovery: Direct bulk system mapping through the Cristie Virtual Appliance (VA) and/or from CSV file import. Optional bulk mapping and recovery actions using the Cristie SDK API based on the Swagger OpenAPI specification which can be used to generate an SDK client in the programming language of your choice. The Cristie recovery boot environment can easily be incorporated with common Intelligent Platform Management Interface (IPMI) implementations such as iDRAC (Dell) and iLO (HP). For Out-of-Band (OOB) systems management we offer DMTF Redfish® client standard libraries to manage physical systems with the same level of automation available for virtual machines. Recovery orchestration to facilitate tiered financial system recovery. Within any financial services infrastructure there will be a system recovery hierarchy necessary to accommodate system interdependencies. Cristie Software can help facilitate tiered system recovery through the system recovery orchestration features provided within the VA. Orchestration tasks allow for detailed fine tuning of system recoveries and replications including reboots, post recovery scripts, manual tasks, plus customisable options for actions following any stage failures. Full details can be found in the VA-Orchestration Guide. Scenario Testing with Cristie Software Recovery Simulation. The PRA Supervisory Statement SS1/21 section 6 describes the expected scenario testing firms should undertake to ensure they can remain within impact tolerances for important business services. The nature and frequency of a firm’s testing should be proportionate to the potential impact that disruption could cause and whether the operational resources supporting an important business service have materially changed. Recovery simulation can be scheduled within the VA to test recoveries of any supported Cristie BMR product backups. Recovery of selected machines can be simulated within a simulate recovery job. The recovery destination can be any physical, virtual or cloud target. With a simulation job created, and at least one recovery machine added to the job, the VA will continue to restore simulations indefinitely until either manually booted, the job is suspended, or the target machine is deleted. It is possible to add multiple simulation machines to the same job. Simplifying operational resilience with automated system recovery to dissimilar platforms. The machines within a recovery job do not need to be the same platform type. If the recovery target is of dissimilar hardware to the source system, then Cristie’s Dissimilar HardWare (DHW) technology can be enabled which automatically provides a path to additional drivers that may be required to successfully boot the target system. RPO/RTO testing and reporting with Cristie Software. The machines within a recovery job do not need to be the same platform type. If the recovery target is of dissimilar hardware to the source system, then Cristie’s Dissimilar HardWare (DHW) technology can be enabled which automatically provides a path to additional drivers that may be required to successfully boot the target system. In summary. Although March 2025 may sound far off, regulators will expect incremental progress during the transition period, so firms should be prepared to demonstrate this when the next impact events occur. Cristie Software provides system recovery solutions designed for automated large scale system recovery orchestration with the ability to undertake detailed system recovery simulations to assist self-assessment and regulatory compliance. Contact our team to learn more about simplifying key aspects of infrastructure recovery to help meet the requirements of operational resilience legislation. Visit the CloneManager® and System Recovery product pages for more information regarding the Cristie Software suite of solutions for system recovery, replication, migration, and ransomware protection.
CloneManager 변경된 블록 추적을 통한 RPO 감소
Reduce RPO with CloneManager changed block tracking. The Recovery Point Objective (RPO) is a crucial concept in disaster recovery and business continuity planning. It represents the maximum amount of data loss that an organization is willing to tolerate in the event of a system failure and is expressed as an amount of time. RPO can be reduced by increasing the frequency that system images are taken and stored in a backup environment to facility recovery when an outage occurs. Systems which host data intensive applications will require a low RPO to minimize data loss. Cristie’s CloneManager replication software fulfils this objective through the addition of Changed Block Tracking for offline replication which is now available with our VA 4.7.1 release. This provides an efficient mechanism to track filesystem changes and allows near continuous real-time replication. Large databases can now be synchronized with minimal data throughput and RPOs are reduced to seconds rather than hours. Changed block tracking with offline replication. Changed block tracking is deployed through a lightweight filesystem driver which continuously scans the source system under protection for file changes. Every file change is communicated to a target environment where an offline system image is maintained. In the event of a disaster scenario the system image stored in the target system is processed against the log of all filesystem changes since the time of creation, producing a bootable image which is a replica of the source system before the failure occurred. Previously, filesystem tracking had to be scheduled to a predefined frequency. Now with changed block tracking the process is fully automated so that the changelog is updated whenever filesystem changes occur. This ensures that the offline bootable image is as current as possible in the event of a system outage. The benefits of offline replication. Cristie’s CloneManager supports both ‘online’ and ‘offline’ replication targets. Targets are termed ‘online’ when they are running machines ready to instantly take over from the primary system. Online replication targets have the advantage that they are ready to run and can takeover operations very quickly. The downside is that they are consuming physical or virtual compute resources continuously while merely waiting for an incident to happen. To overcome this resource overhead an alternative exists in the form of virtual disk image files. Virtual machines can be captured as a complete image in the same way that a system drive in a physical machine can be captured as a single disk image. The image file contains everything including the OS configuration, applications, and data. System replication can be performed to a virtual disk image file stored within a private or public cloud environment rather than to a running machine. This has a significant cost advantage as only the cost of cloud storage is required to maintain these image files rather than storage plus compute resources. The disadvantage is the time taken to boot the image and bring the machine on-line, but for many DR scenarios the Recovery Time Objective (RTO) they provide can be measured in a few minutes which is often sufficient. Cristie replication solutions provide both online and offline replication capabilities with support for all common system image standards including .vhdx, .qcow2 and .vmdk file formats via the Cristie VA. How can I take advantage of changed block tracking today? The initial release of changed block tracking supports the Windows OS only, and replication to Amazon EC2, Oracle BLOB, or any S3 compliant storage including MinIO. Future releases will support Azure and VMware plus additional operating systems. The importance and benefits of reducing RPO. Here are some reasons why the Recovery Point Objective is important: Minimizing data loss: This ensures that critical data is protected and minimizes the potential impact of data loss on business operations. Compliance requirements: Many industries and regulatory bodies have specific data protection and recovery requirements. Adhering to these regulations is essential to avoid legal penalties, reputational damage, and loss of customer trust. The RPO helps organizations align their data recovery practices with compliance standards and demonstrate their commitment to data protection. Operational continuity: Data is a vital asset for organizations, and its loss or unavailability can severely impact day-to-day operations. By defining an RPO, organizations can establish recovery timeframes and implement measures to ensure that data is consistently backed up and recoverable. Financial implications: Data loss can have significant financial consequences for organizations. The cost of recovering lost data, rebuilding systems, and compensating for the disruption can be substantial. By setting an appropriate RPO, organizations can assess the cost-effectiveness of their data protection strategies and allocate resources accordingly. This allows them to strike a balance between investment in data recovery and the potential financial impact of data loss. Customer trust and satisfaction: In today’s data-driven world, customers expect organizations to safeguard their information. If an organization experiences a data breach or loss, it can erode customer trust and damage its reputation. By implementing robust data protection measures, including meeting RPO objectives, organizations can assure customers that their data is secure and instill confidence in their ability to handle potential disruptions. In summary. Recovery Point Objective is hugely important and safeguards many aspects of business operations as highlighted above. The new changed block tracking feature from Cristie adds an additional layer of automation for our customers to ensure their vital business systems are protected. Visit the CloneManager® and System Recovery product pages or contact the Cristie Software team for more information regarding the Cristie Software suite of solutions for system recovery, replication, migration, and ransomware protection.
Cristie 소프트웨어 포트폴리오에 포함된 랜섬웨어 조기 탐지 기능

Early ransomware detection incorporated into your system recovery process. When cybercriminals orchestrate a human led cyberattack, they may have spent months identifying and overcoming defences to maximise the impact of their attack. Early ransomware detection is therefore vital to ensure damage limitation. Regardless of whether their entry was through commodity malware, or the exploitation of an outdated or misconfigured web server, the ultimate end goal will be file encryption to hold vital operational data to ransom. Hackers will typically use asymmetric encryption. This is cryptography that uses a pair of keys to encrypt and decrypt a file. The public-private pair of keys is uniquely generated by the attacker for the victim, with the private key to decrypt the files stored on the attacker’s server. Human led attacks attempt to spread laterally within an organization’s infrastructure, and when the encryption payload is executed, files can be encrypted at an alarmingly fast rate. Rapid detection of anomalies in file structure and naming can provide the earliest warning of an active cyberattack and this capability has now been introduced into Cristie Software’s portfolio of system recovery and replication solutions. Applying patented file analysis techniques to combat ransomware. We recently announced our UK patent award for the automatic self-healing of errors or failures encountered during a system restore or replication. This technology is built upon algorithms which analyse run-time log files to provide automatic system restore failure resolution through machine learning. The Cristie Software development team have applied these technologies to provide advanced file anomaly detection which can take place within the system recovery and replication process. System backups are a vital defence against ransomware and the backup process provides an ideal opportunity to compare file structure between subsequent backup job images. Certain files will be changing regularly throughout normal business operations due of actions being undertaken within their associated applications; however, the process of malicious file encryption will follow one of several detectable patterns. It is these patterns that the Cristie Software anomaly detection technology will seek to identify and provide the earliest possible warning that an attack is in process. Detecting ransomware encryption patterns. To be effective, ransomware must encrypt files, that means it must read file contents from disk and then write encrypted file contents to disk. The way this is done will vary, some ransomware payloads will write to a different file, and then delete the original file. Some will write into the original file, and possibly rename the file after it has been encrypted. Therefore, watching for mass deletes and renames is part of the process, but this is just the tip of the iceberg. The actual encryption process also varies with some payloads encrypting fragments of files while others may encrypt the entire file. File encryption is detected by calculating the entropy of a file. File entropy measures the randomness of the data in a file and is used to determine whether a file contains hidden data or suspicious scripts. The scale of randomness ranges from 0, not random, to 8, totally random, such as an encrypted file. Of course, any backup process that is using encryption and/or data compression will also exhibit these properties including the renaming of files with an extension such as ‘.bak’ plus a subsequent increase in file entropy. Any file anomaly detection algorithm must therefore be able to determine between suspicious and expected behaviours to avoid presenting false positive alerts. Typical ransomware attacks will display characteristics which can be detected by Cristie’s anomaly detection algorithms through comparison against known patterns. The detection process can be run following every system backup. File activity reports and graded alerts are then presented via a security dashboard within the Cristie Virtual Appliance (VA) user interface. Alerts can also be provided by email and recorded in event logs. How quickly can ransomware encrypt your data? A recent article published by technology news platform ZDNET reported that researchers had tested how quickly 10 major ransomware strains could encrypt networks. At the time of writing, they found the fastest form of ransomware to be a malware strain called LockBit, which took a median time of just 5 minutes and 50 seconds to encrypt 100,000 files. In a subsequent test, it took LockBit only 4 minutes and 9 seconds to encrypt 53.83 GB of files across different Windows operating systems and hardware specifications. These figures demonstrate how quickly ransomware can become a major cybersecurity crisis for the victim of an attack. The ability to detect and alert on file activity which may be suspicious means that potential ransomware attacks can be identified in motion and immediate action taken. Determining your safe recovery point following a ransomware attack. Given the speed at which ransomware encryption can spread through an infected network, it is highly likely that system backups will contain malware encrypted files. This scenario would usually require an amount of cyber forensic investigation to determine the ‘last known clean’ copy of backup data that could provide a safe restore point. This can be a timely exercise resulting in extended downtime and potential loss of revenue. Cristie Software’s anomaly detection capability can help reduce this time since backup files can also be scanned for anomalies by comparison against multiple snapshots of previous backups which the VA can reference as part of normal operations. Extending a holistic approach to cybersecurity. Cyber threats come in many forms so for that reason a holistic approach is required to tackle them. Cybersecurity can seem a daunting task with so many loopholes to plug, but with a systematic approach you can achieve a great level of protection for your backup environment. Traditional antivirus software still plays a vital role although by its nature it is always on the back foot since it can only detect malware codes that are already known and present within virus definition files which require constant updates. Advanced techniques that employ machine learning, such as the file anomaly detection included within Cristie Software’s recovery and replication solutions, offer a powerful additional layer
자동화된 OS 현대화를 통한 클라우드 마이그레이션
\n Cloud migration presents a great opportunity to move applications to a more modern operating system (OS). In some cases, an OS update may be mandatory to meet the minimum supported cloud platform OS image versions. For example, Oracle Cloud currently offers Windows Server 2012 R2 Standard, Datacenter as the earliest available platform image level. \n\n Migrating applications to cloud instances running an up-to-date version of Windows is the right approach from an ongoing support perspective and maximizes the flexibility and reliability of the cloud platform. However, certain legacy applications may have OS version limitations and this needs to be verified to confirm compatibility. \n\n Cristie’s latest CloneManager® release offers the ability to perform a Windows OS upgrade in a sandbox test system within the cloud environment. This test system can then be checked for compatibility before committing the upgraded image to the target system. \n\n Cristie VA Cloud migration with automatic Windows OS updates \n\n CloneManager® provides the option of performing automatic Microsoft Windows OS updates following an initial image migration to the target system. If this option is selected a replication sandbox is created within the target system and a snapshot of the migrated image is taken to obtain a thin-provisioned copy-on-write layer that can accept changes and subsequently be used as a bootable test instance. Once booted, the upgrade procedure is initiated which will initiate the Microsoft OS upgrade process. Any OS licenses required following the upgrade process must then be applied by the user. \n\n When system upgrades have completed, one of two things can happen; the system can be booted into the new operating system for validations to be run against applications on the system, or (if applicable) further upgrades can be run to bring the system up to the latest version. Automatic upgrades can be performed right through to the very latest Windows OS release, saving the labour overheads of a manual intervention. However, any application upgrades will need to be applied manually to the final image if required . \n\n What can I do if my application has legacy OS dependencies? \n\n Legacy applications that are OS-dependent or require a specific environment such as server and network hardware, databases, and storage resources can be problematic during a lift-and-shift cloud migration. Many cloud platforms offer a Bring Your Own Image (BYOI) capability which will allow certain legacy OS versions to run if the underlying platform infrastructure can support it. This will usually require the customer to supply a ‘cloud ready’ image that does not rely on unavailable 3rd party dependencies. If the lift-and-shift migration approach presents too many problems, you may be able to identify pieces of the application to transition to the cloud. This method, known as Application Evolution, allows users to migrate to the cloud in steps, rather than all at once, but this approach may cost more to operate. \n\n Another approach known as Application Re-Architecting breaks down applications and then rebuilds them in a more scalable, modern design. With this scenario you are not completely starting from scratch, but merely eliminating any code that constrains your ability to migrate to a modern OS version, while preserving and potentially enhancing business-relevant functionality in the process. Application re-Architecting is best for legacy applications that are business-critical and provide competitive differentiation, as completely reworking an application for the cloud can be a big undertaking. \n\n In summary \n\n The automatic Windows upgrade feature introduced with the Cristie Software VA 4.5.1 release offers a hybrid lift-and-shift cloud migration environment that greatly simplifies legacy application testing and reduces the time and effort required when Windows OS updates are required to meet cloud platform requirements. CloneManager® and the Cristie VA support cloud migration to many platforms including Oracle Cloud, Azure and AWS for both physical servers, VMs, and containerized applications. Visit the CloneManager® product pages or contact the Cristie Software team for more information on system replication & migration. \n
재해 복구 계획 및 시스템 복구 프로세스에 대한 Cristie 소프트웨어 가이드

중요한 IT 시스템의 다운타임은 어떤 식으로든 비즈니스 프로세스의 정상적인 흐름에 영향을 미치며 거의 모든 경우에 매출 손실로 이어집니다.


