Recuperación automatizada de sistemas físicos para la resistencia operativa | Estudio de caso Cristie

Un banco británico confía en Cristie Software para la recuperación automatizada de sistemas físicos Cuando un importante banco global con sede en el Reino Unido necesitó demostrar su preparación para la recuperación ante desastres y mantener el cumplimiento de las estrictas normativas financieras, seleccionó a Cristie Software para implementar la recuperación automatizada de sistemas físicos para la resiliencia operativa a escala empresarial. El objetivo del banco era claro: conseguir una resistencia operativa total reduciendo el tiempo de recuperación de más de 8.000 servidores físicos de días a sólo horas. El reto: garantizar una rápida recuperación del sistema en más de 8.000 servidores físicos El banco necesitaba mejorar y demostrar sus capacidades de recuperación del sistema para cumplir las normativas del sector, en más de 8.000 servidores físicos, con plataformas Windows y Linux. Lograr una recuperación tan amplia de sistemas físicos dispares en cuestión de horas, algo que antes llevaba días, suponía un reto importante. Recuperación automatizada de sistemas a escala para instituciones financieras Los sistemas financieros implican complejas configuraciones interdependientes de servidores y almacenamiento, y la recuperación de sistemas físicos a escala es difícil debido a la necesidad de intervención manual y de reinstalación y configuración de sistemas y software de aplicación. El software de recuperación Cristie automatiza completamente todo el proceso para recuperar sistemas completos que comprenden tanto máquinas físicas como virtuales. Este nivel de automatización de la recuperación es fundamental en un sector en el que el cumplimiento de normativas como DORA y SOX es obligatorio. Recuperación validada sin tiempo de inactividad: Cumplimiento de la normativa financiera Cristie Software desplegó Cristie RBMR para Rubrik con el fin de proporcionar la capacidad de recuperar miles de sistemas físicos en paralelo. Las recuperaciones de sistemas también se pueden verificar sin tiempo de inactividad y sin interferir con los servicios bancarios en vivo. Principales características de la solución: Rápida automatización paralela de la recuperación de sistemas físicos Simulación de recuperación sin afectar a los sistemas de producción Cobertura agnóstica de plataformas (Windows, Linux, AIX, Solaris) Informes listos para auditoría para el cumplimiento de normativas "Ayudamos al cliente a validar la recuperabilidad de más de 8.000 sistemas sin tiempo de inactividad. Fue un verdadero testimonio de la escalabilidad y fiabilidad de Cristie" - Cristie Project Lead Cristie RBMR: Integración perfecta con Rubrik para garantizar la recuperación El software de recuperación Cristie se integra perfectamente con las principales soluciones de copia de seguridad para facilitar la recuperación de sistemas operativos, aplicaciones, configuración de usuario y datos a cualquier punto de recuperación disponible en el tiempo. No se requiere infraestructura o gestión adicional, todas las operaciones de recuperación se pueden configurar y controlar a través de la consola Cristie VA. Cristie Recovery se integra perfectamente con las soluciones de copia de seguridad de Rubrik, Cohesity, IBM y Dell Technologies. Cristie Recovery también puede funcionar como una solución independiente de copia de seguridad y recuperación. Resultados: Preparación reglamentaria y resistencia operativa en la banca La exitosa implantación aportó beneficios cuantificables: Flujo de trabajo de recuperación simplificado para sistemas físicos Validación de recuperación a escala completa completada sin tiempo de inactividad Fortalecimiento de la postura de cumplimiento con documentación lista para auditoría Capacidad probada para resistir y recuperarse de fallos catastróficos Tranquilidad para la continuidad del negocio en todas las operaciones globales Por qué es importante la recuperación física automatizada en el sector financiero En el sector financiero, la resistencia operativa es esencial. Los marcos normativos como DORA, SOX y PRA/FRA exigen una planificación demostrable de la recuperación ante desastres. Con Cristie, el banco dispone ahora de una solución de confianza para cumplir tanto las normas de riesgo internas como las auditorías de cumplimiento externas. Software Cristie : Recuperación probada para industrias reguladas Este caso demuestra la capacidad de Cristiepara ofrecer recuperación de sistemas a gran escala y plataforma agnóstica y validación de recuperación sin problemas y de forma segura. Para cualquier institución financiera u otra industria que necesite resiliencia operativa, Cristie Software ofrece una recuperación verificada en la que puede confiar. ✅ ¿Está preparado su plan de recuperación ante desastres para una auditoría? Descubra cómo la recuperación automatizada del sistema físico de Cristieayuda a las instituciones financieras a satisfacer las demandas de cumplimiento y recuperarse con confianza. Explore la suite de recuperación Cristie o póngase en contacto con nosotros para obtener una demostración personalizada. Póngase en contacto con el equipo de Cristie Software si está buscando mejorar la recuperación y replicación del sistema dentro de su organización, o para obtener más información sobre la replicación del sistema y nuestra integración de recuperación del sistema con las principales soluciones de copia de seguridad de proveedores como IBM, Dell Technologies, Rubrik y Cohesity. Por último, descubra cómo estamos ayudando a otras empresas a modernizar la recuperación de sistemas en nuestras páginas de casos de uso.
Tendencias en la recuperación de sistemas: Tecnologías emergentes e innovaciones

System Recovery Trends: Emerging Technologies and Innovations In today’s rapidly evolving digital landscape, the stakes for data protection and system recovery have never been higher. As organizations face increasing cyber threats, hardware failures, and human errors, the need for robust and automated system recovery solutions has become paramount. But what does the future hold for system recovery, and how is Cristie Software paving the way for innovation? In this article, we’ll explore system recovery trends shaping the future of disaster recovery and highlight how Cristie Software’s cutting-edge solutions are empowering businesses to stay resilient. 1. The Rise of AI and Machine Learning in Automated Recovery Solutions Artificial intelligence (AI) and machine learning (ML) are transforming the way recovery solutions operate. By analyzing patterns of failures and predicting potential risks, AI-driven tools can preemptively address vulnerabilities before they lead to downtime. Cristie Software integrates intelligent automation into its solutions, enabling proactive automated system recovery that streamlines complex recovery workflows. This innovation reduces the margin for error and speeds up the recovery process. Key Benefits of AI-Powered Recovery Solutions: Predictive Recovery: Early detection of system anomalies including potential malware. Self-Healing Systems: Automated response protocols to fix issues. Faster Recovery Times: Reduced reliance on manual intervention. Cristie Software’s Innovation: Cristie Software harnesses AI to enhance its recovery solutions with predictive analytics and intelligent decision-making capabilities. The platform continually learns from historical recovery scenarios, optimizing future processes. By integrating advanced automation tools and ML-driven workflows, Cristie’s solutions not only identify vulnerabilities but also take proactive measures to mitigate potential failures. 2. Cloud-Native and Hybrid Recovery Models The future of system recovery is closely linked to the rise of cloud-native and hybrid environments. Organizations are increasingly adopting hybrid IT strategies to ensure flexibility and scalability. Cristie Software’s solutions support seamless recovery across on-premises, cloud, and hybrid infrastructures. Whether recovering critical workloads from a private data center or restoring systems in the cloud, Cristie’s technology ensures consistent, secure, and efficient recovery processes. Emerging Trends in Cloud-Based Recovery: Multi-Cloud Resilience: Support for multiple cloud service providers. Cloud Automation: Orchestration tools to automate failover and failback. Disaster Recovery as a Service (DRaaS): Scalable recovery services for greater agility. Cristie Software’s Innovation: Cristie Software provides cloud-optimized recovery solutions that integrate seamlessly with leading cloud providers, ensuring rapid recovery regardless of the deployment environment. By leveraging advanced orchestration, Cristie’s technology enables smooth transitions between on-premises and cloud resources, allowing organizations to implement hybrid recovery strategies without compromising performance or security. 3. Bare-Metal Recovery for Diverse Platforms As IT environments grow more diverse, encompassing physical, virtual, and cloud-native systems, the demand for platform-agnostic bare-metal recovery solutions is rising. Key Advancements: Support for dissimilar hardware recovery. Integration with containerized and microservices-based environments. Cristie Software’s Innovation: Cristie Software’s BMR (Bare Machine Recovery) supports full system recovery across physical, virtual, and cloud platforms, ensuring hardware-independent restorations and compatibility with evolving infrastructure. 4. Real-Time System Replication and Continuous Data Protection (CDP) Organizations are moving from traditional backup schedules to continuous data protection (CDP) to minimize Recovery Point Objectives (RPOs) and ensure that data loss is virtually eliminated. Key Advancements: Continuous system snapshots to maintain up-to-date replicas. Real-time replication to ensure synchronized recovery points. Cristie Software’s Innovation: With CloneManager, Cristie enables real-time replication of systems, allowing businesses to maintain consistent recovery points and quickly fail over to backup systems during disruptions. 5. Recovery Solutions Tailored for Compliance and Regulation Regulatory frameworks like GDPR, DORA, SOX, HIPAA, and NIST mandate stringent data protection and recovery practices. As regulations evolve, system recovery solutions must adapt to ensure compliance without sacrificing performance. Cristie Software provides comprehensive audit trails and reporting features to support regulatory compliance. Its automated system recovery solutions are designed to meet the needs of highly regulated industries, ensuring that recovery processes align with legal and industry standards. Key Compliance Features: Automated Documentation: Detailed recovery logs for compliance reporting. Data Sovereignty: Control over where recovery data is stored. Testing and Validation: Regular, automated recovery tests to ensure preparedness. Cristie Software’s Innovation: Cristie Software’s compliance-focused solutions simplify regulatory adherence by automating recovery documentation and validation processes. Detailed logs and audit trails provide visibility into every recovery event, supporting compliance reporting with minimal effort. Furthermore, Cristie’s solutions include customizable testing schedules to ensure that recovery plans remain effective and compliant. 6. Disaster Recovery as a Service (DRaaS) The rise of DRaaS is reshaping how businesses approach disaster recovery. DRaaS offers a cost-effective, subscription-based model that offloads the complexity of maintaining recovery infrastructure. Key Advancements: On-demand system recovery services. Reduced capital expenses and simplified DR operations. Cristie Software’s Innovation: Cristie’s solutions integrate seamlessly with managed service providers, enabling organizations to leverage DRaaS capabilities for flexible, scalable disaster recovery options. 7. Cybersecurity-Driven Recovery Strategies Cyberattacks, particularly ransomware, have highlighted the importance of recovery solutions that are not just fast but secure. The next wave of innovation in system recovery focuses on integrating robust security protocols directly into recovery plans. Cristie Software’s solutions prioritize cyber-resilient recovery, with secure automated system recovery workflows that ensure minimal risk of reinfection during restoration. By combining encryption, multi-factor authentication (MFA), and tamper-proof recovery points, Cristie helps organizations bounce back from cyber incidents with confidence. Security-Focused Recovery Features: Immutable Backups: Prevent unauthorized changes to backup data. Zero-Trust Architecture: Verify every recovery action to mitigate insider threats. Ransomware Rollback: Rapid recovery to pre-attack states. Cristie Software’s Innovation: Cristie Software integrates end-to-end security measures into every stage of the recovery process. From encrypted backups to automated validation protocols, Cristie ensures that recovery workflows meet zero-trust standards. Additionally, Cristie’s solutions provide automated ransomware detection features, enabling businesses to recover quickly and securely from even the most sophisticated cyberattacks. 8. Faster Recovery Through Automation and Orchestration The demand for faster recovery times is driving the adoption of advanced automation and orchestration platforms. Manual recovery processes are slow, error-prone, and resource-intensive, making them unsuitable for modern enterprises. Cristie Software has long been at the forefront of automated system recovery, offering solutions that reduce downtime
Cómo pueden las empresas mejorar su postura de ciberseguridad en 2025: Perspectivas a partir de las tendencias de 2024

How Businesses Can Improve Their Cybersecurity Posture in 2025: Insights from 2024 Trends In an increasingly interconnected world, improving cybersecurity remains a critical priority for businesses of all sizes. The year 2024 has seen a surge in cyberattacks, with threat actors leveraging more sophisticated methods to exploit vulnerabilities. As we look to 2025, it’s clear that a proactive and adaptive approach to improving cybersecurity is essential. Drawing from 2024 trends, this article explores key recommendations for improving cybersecurity posture in the year ahead. 1.Improving cybersecurity with AI-Driven Threat Detection During 2024, AI-driven cyberattacks became more prevalent, with adversaries using AI to craft more convincing phishing attempts and automate attacks at scale. Businesses can fight fire with fire by adopting AI-driven threat detection tools. These systems analyze vast datasets in real-time, identifying anomalies that may signal a breach. Recommendation:• Invest in AI-powered security platforms which provide real-time detection and automated responses. Cristie Software included Advanced Anomaly Detection driven by machine learning (ML) algorithms. This can be run at any time to compare snapshots of system backups to detect and provide early warning of suspicious file encryption.• Ensure staff receive training to understand and operate these systems effectively. 2024 Insight: According to a report by Gartner, AI-driven security solutions have reduced threat response times by up to 60%. 2. Zero Trust Architecture (ZTA) Implementation “Trust no one” became a fundamental principle for improving cybersecurity in 2024. The Zero Trust model verifies every user and device attempting to access a network, reducing the risk of insider threats and compromised credentials. Recommendation:• Adopt Zero Trust principles by segmenting networks, enforcing multi-factor authentication (MFA), and continually verifying user identity.• Utilize solutions like Microsoft’s Zero Trust framework and tools from companies like Zscaler and Okta. 2024 Insight: In a survey by Forrester, organizations that implemented ZTA reported a 45% reduction in security incidents. 3. Strengthen Endpoint Security with Extended Detection and Response (XDR) Endpoints (laptops, mobile devices, and IoT devices) remain one of the primary targets for attackers. In 2024, the integration of Extended Detection and Response (XDR) tools helped consolidate endpoint, network, and server security into a single cohesive system for improving cybersecurity. Recommendation:• Deploy XDR solutions like SentinelOne, Sophos, or Trend Micro to achieve unified threat detection and response.• Regularly update endpoint security protocols and conduct frequent security audits.• Incorporate system recovery solutions from Cristie Software to ensure quick recovery from endpoint failures or cyber incidents, minimizing downtime and data loss. 2024 Insight: IBM Security’s X-Force Threat Intelligence Index indicated that endpoint-related breaches accounted for 48% of all incidents in 2024. 4. Focus on Awareness Training to Improve Cybersecurity Human error remains one of the leading causes of security breaches. In 2024, phishing and social engineering attacks increased by 30%, underscoring the need for robust employee training to improve cybersecurity awareness. Recommendation:• Conduct regular cybersecurity awareness training sessions to help employees recognize phishing attempts, ransomware, and social engineering tactics.• Use platforms like KnowBe4 or Proofpoint for simulated phishing campaigns and educational modules. 2024 Insight: A Verizon Data Breach Investigations Report found that 68% of breaches involved a non-malicious human element, like a person falling victim to a social engineering attack or making an error. 5. Adopt Continuous Monitoring and Incident Response Plans Continuous monitoring of your IT environment ensures that threats are detected early. An effective Incident Response (IR) plan ensures quick action when breaches occur, improving cybersecurity resilience. Recommendation:• Implement 24/7 Security Operations Center (SOC) monitoring through in-house teams or Managed Security Service Providers (MSSPs) like Arctic Wolf and Rapid7.• Develop a comprehensive IR plan and conduct regular tabletop exercises to ensure readiness.• Utilize Cristie Software’s system recovery solutions to enable swift recovery in the aftermath of a cyber incident. The simulated recovery feature of our software enables organizations to ensure correct functionality of their recovery jobs without interrupting ongoing protection. In addition, our isolated network recovery mechanism allows systems to be recovered into a cleanroom environment for cyber forensics and integrity verification following an attack. 2024 Insight: Companies with well-documented IR plans reduced breach recovery times by 35%, according to a Ponemon Institute study. 6. Enhance Cloud Security Measures With cloud adoption increasing, cloud security breaches in 2024 highlighted the importance of improving cybersecurity measures for data stored in cloud environments. Recommendation:• Use cloud security solutions such as those offered by AWS, Microsoft Azure, and Google Cloud Platform (GCP) to enforce strong access controls, encryption, and threat detection.• Ensure compliance with frameworks like the Cloud Security Alliance (CSA) Cloud Controls Matrix.• Integrate Cristie Software’s recovery solutions to ensure cloud workloads can be restored quickly in the event of data loss or a breach. Our recovery and replication software provides the capability to recovery or replicate system to a variety of cloud platforms. CloneManager our replication software provides a simple way to automate and accelerate cloud onboarding or to utilize the cloud as a failover target. 2024 Insight: According to Cloud Security Alliance’s 2024 report, 67% of cloud security breaches were caused by misconfigurations. 7. Regularly Update and Patch Systems Unpatched vulnerabilities remain a favorite entry point for cybercriminals. In 2024, attacks exploiting known vulnerabilities increased dramatically, emphasizing the importance of improving cybersecurity through timely updates. Recommendation:• Implement an automated patch management system.• Prioritize patching critical vulnerabilities and ensure all software and firmware are up-to-date.• Consider using Cristie Software’s system recovery solutions to quickly revert to secure states in case of a compromised patch. 2024 Insight: CISA’s Known Exploited Vulnerabilities Catalog reported a 52% rise in attacks targeting unpatched systems in 2024. Conclusion As we move into 2025, businesses must adapt to an evolving threat landscape shaped by the trends of 2024. By investing in AI-driven detection, implementing Zero Trust, enhancing endpoint security, and prioritizing cybersecurity awareness, organizations can focus on improving cybersecurity posture. Incorporating system recovery solutions from Cristie Software ensures businesses can recover swiftly and efficiently from potential cyber incidents. Proactive measures and continuous improvement will be key to protecting assets, maintaining customer trust, and ensuring business continuity in the
La importancia de la recuperación automática de sistemas: Perspectivas respaldadas por los informes de Cohesity
The Importance of Automated System Recovery: Insights Backed by the 2024 Cohesity Global Cyber Resilience Report In today’s increasingly hostile cyber landscape, the ability to quickly recover systems after an attack or failure is more crucial than ever. Subsequently Automated system recovery is not just a convenience—it’s a necessity for maintaining business continuity, minimizing downtime, and protecting critical data. At Cristie Software, we understand that fast, reliable system recovery can mean the difference between a minor disruption and a catastrophic business failure. Recent reports from Cohesity highlight the rising challenges organizations face in managing system recovery after a cyber incident. These insights underline why automation is key to ensuring resilience and recovery readiness. Therefore let’s explore the importance of automated system recovery and how it can protect your business from costly disruptions. The Growing Threat of Cyberattacks and Downtime According to the 2024 Cohesity Global Cyber Resilience Report, an alarming 67% of organizations have experienced ransomware attacks in the past year. More troubling is the fact that many of these organizations struggle to recover efficiently after such incidents. Recovery delays can result in: • Prolonged Downtime: Businesses can take anywhere from 1 to 3 days or more to fully recover operations, leading to financial losses and reputational damage. • Data Loss: Inefficient recovery processes can lead to incomplete restoration, resulting in lost data that can be critical for operations. • Increased Costs: The longer the downtime, the higher the cost. Accordingly the report estimates that downtime can cost enterprises thousands of dollars per minute. This underscores the need for a robust, automated system recovery solution that can restore operations quickly and accurately, mitigating these risks. Why Manual Recovery Processes Are No Longer Viable Traditional, manual recovery processes are time-consuming, error-prone, and often incapable of meeting the demands of modern IT environments. Manual recovery typically involves: 1. Locating and Validating Backups: Ensuring that the backups are current, uncorrupted, and usable. 2. Manual Reconfiguration: Rebuilding servers, re-installing operating systems, and reconfiguring applications. 3. Coordination Challenges: Synchronizing various teams to execute recovery steps in the correct sequence. Cohesity’s research shows that 78% of IT professionals believe that manual recovery processes are a major bottleneck during disaster recovery. In an environment where every second counts, manual methods simply cannot keep up. The Benefits of Automated System Recovery Automated system recovery provides a streamlined, reliable, and efficient solution to these challenges. Here’s why automation is critical: 1. Speed and Efficiency When recovery processes are automated recovery times can be reduced from hours or days to mere minutes. By leveraging tools that automate the restoration of systems, applications, and configurations, businesses can resume operations faster, minimizing the impact of downtime. 2. Accuracy and Consistency Automation eliminates human error by following pre-defined recovery workflows. Each step of the recovery process is executed consistently, ensuring that systems are restored accurately every time. 3. Regular Testing and Validation Cristie Software automated recovery solutions allow for regular testing without disrupting production systems. Consequently this ensures that your recovery plans are always up-to-date and ready for deployment. Cohesity’s reports emphasize the importance of frequent testing to maintain recovery readiness. 4. Scalability As IT environments grow more complex, automated recovery solutions can scale to handle multiple systems simultaneously, whether on-premises, in the cloud, or in hybrid environments. This ensures comprehensive protection regardless of infrastructure size. 5. Reduced Costs By minimizing downtime and the resources needed for manual intervention, automated recovery reduces the overall cost of system recovery. Faster recovery means fewer losses and lower risk of compliance penalties. How Cristie Software Delivers Automated System Recovery We provide advanced recovery solutions designed to meet the needs of modern businesses. Our automated system recovery tools offer: • Bare Metal Recovery: Recover entire systems, including operating systems, applications, and configurations, directly to new hardware or virtual environments. Our Bare Metal recovery for Cohesity (CoBMR) works seamlessly to provide automated recovery for any machine within Cohesity Data Protect. • Cross-Platform Compatibility: Support for physical, virtual, and cloud-based infrastructures. • Regular Testing and Validation: Automated testing capabilities ensure your recovery plans are always ready for deployment. • Integration with Leading Data Management Solutions: Our solutions seamlessly integrate with platforms like Cohesity to enhance your overall cyber resilience. Cohesity’s Insights: The Need for Resilient Automated System Recovery The research from Cohesity paints a clear picture: cyber threats are not going away, and businesses must be prepared to respond effectively. Automated system recovery is a cornerstone of resilience, enabling organizations to recover faster, reduce errors, and maintain business continuity. By combining Cristie Software’s automated recovery solutions with robust data protection platforms like Cohesity, businesses can achieve a comprehensive defense strategy that ensures they can recover swiftly from any incident. Conclusion In conclusion, backups are essential, but without automated system recovery, they fall short of providing true business resilience. As cyber threats grow more sophisticated and downtime becomes more costly, automation is no longer optional—it’s a necessity. At Cristie Software, we’re committed to helping businesses safeguard their critical systems and data with automated recovery solutions that work when you need them most. Don’t leave your recovery to chance. Learn how Cristie Software can enhance your resilience by visiting www.cristie.com/solutions/ today. Be resilient. Be ready. Automate your recovery. Contact the Cristie Software team if you are looking to improve system recovery and replication within your organization, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity. Finally, learn how we are helping companies modernize system recovery in our Use Case pages.
Las 5 causas principales de los fallos de recuperación del sistema y cómo evitarlas
The Top 5 Causes of System Recovery Failure and How to Avoid Them In today’s always-on business environment, system recovery is more than just a technical safeguard, it’s a critical component of business continuity. When a system recovery plan fails, the consequences can include extended downtime, lost revenue, and damaged reputation. At Cristie Software, we specialize in providing advanced recovery solutions that minimize these risks. To help you strengthen your recovery strategy, let’s examine the top five causes of system recovery failure and how to address them effectively. 1. Lack of Regular System Recovery Testing The most common reason for system recovery failure is insufficient testing. Even a meticulously designed recovery plan can fall short if it hasn’t been tested under realistic conditions. Without testing, unforeseen issues, such as misconfigured backups or incompatible systems, often remain undetected. How to Avoid This: • Test Regularly: Schedule routine recovery drills to ensure that your system recovery plan is functional and up-to-date.• Simulate Real-World Scenarios: Use tools like Cristie Software’s recovery testing solutions to simulate disaster events and verify system behavior.• Document Results: Record the outcomes of tests to identify weak points and fine-tune the recovery process. 2. Outdated System Recovery Plans A system recovery plan that doesn’t account for changes in IT infrastructure or business operations is a recipe for failure. Many organizations fail to update their recovery plans after implementing new software, expanding storage capacities, or adopting hybrid cloud environments. How to Avoid This: • Establish a Review Schedule: Update your system recovery plan whenever there’s a significant change in your IT environment.• Centralize Documentation: Use Cristie’s solutions to automate system recovery and centralize the documentation of system configurations, ensuring alignment with the latest setup.• Assign Ownership: Designate a recovery team responsible for maintaining and updating the plan. 3. Incomplete or Corrupt System Backups System recovery depends on the availability of accurate and complete backups. Partial backups or data corruption during the backup process can make recovery impossible, leading to prolonged downtime and data loss. How to Avoid This: • Automate Backups: Leverage automated backup tools that ensure consistency and completeness across all systems.• Use Backup Validation: Cristie’s solutions offer system recovery simulation to confirm that data is intact and accessible before an issue arises.• Adopt Redundancy: Store backups across multiple locations, including offsite and cloud-based storage, to mitigate risks. The 3-2-1 backup rule is a widely recognized data protection strategy that recommends maintaining three copies of your data: the original and two backups. These copies should be stored on two different types of media, with one copy kept off-site to safeguard against data loss due to hardware failures, cyberattacks, or natural disasters 4. Hardware and Software Incompatibility When recovering systems, hardware and software incompatibilities can create bottlenecks. For example, legacy recovery tools may struggle with modern IT environments, causing delays or outright failures. Problems very often arise when recovering to dissimilar hardware due to device driver incompatibilities. Cristie Software system recovery tools can overcome this issue with Dissimilar Hardware Technology that can automatically insert missing or alternative device drivers during the recovery process, eliminating the need for manual intervention. How to Avoid This: • Upgrade Tools Regularly: Use Cristie’s state-of-the-art recovery solutions, which are designed to handle modern, hybrid, and legacy systems seamlessly.• Standardize Your Environment: Reduce variability by standardizing hardware and software configurations wherever possible.• Test Compatibility: Test your recovery tools with existing and updated systems to avoid surprises during critical recovery operations. 5. Human Error Leading to System Recovery Failure Even the most robust recovery plans can be derailed by human error. Missteps such as skipping critical steps, applying incorrect configurations, or misunderstanding recovery procedures can result in significant delays. How to Avoid This: • Provide Training: Ensure that your IT staff is trained in executing the system recovery plan effectively.• Create Step-by-Step Guides: Use Cristie’s tools to generate clear and automated recovery workflows, minimizing reliance on manual input.• Embrace Automation: Cristie Software recovery tools can automate repetitive recovery tasks to reduce the risk of mistakes and accelerate recovery times. For more complex recovery workflows our software offers recovery orchestration which allows specific recovery tasks to be defined and processed in a user defined sequence. How Cristie Software Enhances System Recovery At Cristie Software, we understand the complexities of system recovery and have built our solutions to help businesses avoid the pitfalls that lead to recovery failures. Our tools focus on: • Rapid Recovery: Minimize downtime with solutions that restore systems in minutes, not hours.• Comprehensive Testing: Simulate recovery scenarios to validate your plan without disrupting daily operations.• Cross-Platform Compatibility: Seamlessly recover systems across diverse IT environments, including physical, virtual, and cloud. Whether you’re recovering a single server or an entire data center, Cristie Software provides the confidence and reliability you need to protect your business. Conclusion Avoiding system recovery failures requires proactive planning, regular testing, and the right tools. By addressing common pitfalls such as outdated plans, incomplete backups, and human error, businesses can ensure resilience and continuity in the face of disruptions. At Cristie Software, we’re here to help you build and maintain a recovery strategy that works when you need it most. Learn more about our advanced recovery solutions by visiting www.cristie.com/solutions/ Secure your business, minimize downtime, and ensure operational continuity with Cristie Software. Contact the Cristie Software team if you are looking to improve system recovery and replication within your organization, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity. Learn how we are helping companies modernize system recovery in our Use Case pages.
El alcance de la ciberdelincuencia en la industria farmacéutica estadounidense

El alcance de la ciberdelincuencia en la industria farmacéutica estadounidense La ciberdelincuencia en la industria farmacéutica es muy destacada en Estados Unidos debido a su propiedad intelectual (PI) de gran valor, los datos sensibles de los pacientes y su papel esencial en la atención sanitaria. El alcance de la ciberdelincuencia en este sector es significativo, como demuestran varios factores e incidentes clave: Prevalencia de ciberataques en el sector farmacéutico y sanitario Alta incidencia de brechas: Los informes han mostrado un notable aumento de las violaciones de datos en las empresas farmacéuticas estadounidenses. La exposición de datos confidenciales se ha vinculado tanto a ciberataques malintencionados como a filtraciones accidentales, lo que a menudo ha dado lugar a un importante escrutinio normativo y a multas. El informe 2024 Cost of a Data Breach Report de IBM Security destaca el impacto financiero de las filtraciones de datos en los sectores, incluidos el sanitario y el farmacéutico. Los sectores sanitario y farmacéutico estadounidenses ocupan el primer y sexto lugar, respectivamente, en cuanto a los costes más elevados por filtración. (Lea el informe de IBM Cost of a Data Breach Report 2024) Vulnerabilidades generalizadas: Una investigación realizada por Reposify en 2021 descubrió que el 92% de las organizaciones farmacéuticas encuestadas tenían al menos una base de datos expuesta, y el 99% tenían al menos una plataforma de acceso remoto expuesta a Internet, lo que indica vulnerabilidades significativas. Tipos de ciberamenazas para las empresas farmacéuticas Robo de propiedad intelectual: Las empresas farmacéuticas estadounidenses, que invierten mucho en investigación y desarrollo, son con frecuencia el blanco de ciberdelincuentes que pretenden robar fórmulas de medicamentos patentadas, datos de ensayos clínicos e investigaciones. Este robo de propiedad intelectual puede provocar graves pérdidas financieras y erosionar las ventajas competitivas. Ataques de ransomware: Este tipo de ataque es especialmente preocupante en Estados Unidos, donde los incidentes de ransomware se han dirigido a importantes empresas farmacéuticas, interrumpiendo las operaciones mediante el cifrado de datos esenciales y exigiendo un pago para su liberación. Phishing e ingeniería social: Muchos empleados de empresas farmacéuticas con sede en Estados Unidos han sido víctimas de ataques de ingeniería social, que los ciberdelincuentes utilizan para obtener acceso no autorizado a sistemas y datos confidenciales. Impacto financiero de la ciberdelincuencia en el sector farmacéutico Elevado coste de las filtraciones: El coste medio de una violación de datos en el sector farmacéutico estadounidense es uno de los más altos de cualquier industria, con costes que a menudo superan los 5 millones de dólares. La necesidad de una respuesta y recuperación rápidas aumenta las presiones financieras, especialmente para las empresas que participan activamente en ensayos clínicos y aprobaciones de medicamentos. Incidentes de ciberseguridad notables en el sector farmacéutico estadounidense Ataque NotPetya a Merck (2017): Este ataque de ransomware tuvo un profundo impacto en Merck, una importante empresa farmacéutica estadounidense, causando interrupciones operativas y pérdidas financieras estimadas en unos 870 millones de dólares. El ataque afectó a las capacidades de producción y distribución de Merck, subrayando la vulnerabilidad del sector a las ciberinterrupciones a gran escala. Ataques de phishing a Pfizer y Moderna (2020): Durante el periodo de desarrollo de la vacuna COVID-19, tanto Pfizer como Moderna, dos actores clave en el panorama farmacéutico estadounidense, fueron blanco de ataques de phishing e intentos de violación. El objetivo de estos ataques era comprometer datos relacionados con vacunas, lo que pone de relieve los riesgos que rodean a la investigación crítica y sensible al tiempo. Factores que contribuyen a la ciberdelincuencia en el sector farmacéutico estadounidense Transformación digital: El cambio a sistemas digitales y la mayor interconectividad dentro de las empresas farmacéuticas estadounidenses han ampliado la superficie de ataque, creando más puntos de entrada para las ciberamenazas. Riesgos de terceros: La dependencia de terceros proveedores y socios de la cadena de suministro puede introducir vulnerabilidades. Por ejemplo, los ataques a proveedores estadounidenses han afectado indirectamente a las operaciones farmacéuticas. Retos normativos: Las empresas farmacéuticas estadounidenses deben cumplir múltiples normativas de ciberseguridad y privacidad en constante evolución, como la HIPAA. Cualquier incumplimiento o infracción de la normativa puede acarrear sanciones y una mayor vulnerabilidad a los ciberataques. En nuestro artículo anterior destacamos las secciones de la HIPPA que detallan específicamente los requisitos de recuperación de sistemas para las empresas que se rigen por la normativa. Conclusión En resumen, las empresas farmacéuticas con sede en Estados Unidos se enfrentan a un riesgo elevado y creciente de ciberdelincuencia. Para hacer frente a esta amenaza, deben aplicar medidas de ciberseguridad rigurosas y emprender una modernización de las soluciones de recuperación de sistemas para proteger sus datos confidenciales, garantizar la continuidad operativa y salvaguardar la salud pública. Póngase en contacto con el equipo de Cristie Software si desea mejorar la recuperación y replicación de sistemas en el sector farmacéutico y sanitario, o para obtener más información sobre la replicación de sistemas y nuestra integración de recuperación de sistemas con las principales soluciones de copia de seguridad de proveedores como IBM, Dell Technologies, Rubrik y Cohesity. Descubra cómo ayudamos a las empresas farmacéuticas y sanitarias a modernizar la recuperación de sistemas en nuestras páginas de casos de uso.
Las nuevas amenazas para la fabricación conectada

Manufacturing is facing a new era of cybercrime Ransomware in manufacturing is rising fast. Manufacturing companies face a growing array of challenges related to cybercrime, largely due to the evolving nature of their IT systems and their reliance on operational technology (OT). These challenges stem from the convergence of IT and OT environments, the complexity of supply chains, and the shift towards more digital and connected manufacturing processes (Industry 4.0). In many cases, there is a need for modernization of system recovery and data protection technologies to combat threats that have emerged for a more connected OT environment. Below are some key challenges: 1. Convergence of IT and OT IT/OT Integration: In modern manufacturing, IT systems (information technology) handle business functions like finance, inventory, and communications, while OT (operational technology) systems control physical processes such as machinery, robotics, and production lines. These two environments are increasingly integrated for improved efficiency, but they have different security requirements. OT systems are often older and not designed with cybersecurity in mind, making them vulnerable when connected to the broader IT network. Extended Lifecycle OT Systems: Many manufacturing plants use equipment with extended lifecycles that cannot be easily updated or patched. These systems, while operationally critical, were often designed without consideration for modern cyber threats, leading to vulnerabilities. Cristie Software system recovery provides support for legacy operating systems including Windows 7 desktop systems and Windows Server 2008 R2 enterprise platforms. Microsoft’s virtualization platform Hyper-V is supported from Hyper-V 2012 plus all editions of Microsoft Azure and Microsoft Azure Stack HCI. Cristie Software system recovery and replication solutions for Red Hat Linux platforms cater for the very latest editions with support extending back to Red Hat Enterprise Linux 5. 2. Ransomware and Disruptions to Production Ransomware Attacks: Ransomware has become a major threat to manufacturers. Attackers can lock down critical systems or encrypt data, halting production processes and causing significant financial losses. For instance, if a ransomware attack disables a factory’s production control systems, it could lead to downtime, missed deadlines, and reputational damage. Production Downtime: Even brief production stoppages can have a large financial impact, particularly in industries where just-in-time (JIT) manufacturing is crucial. Cyberattacks that disrupt OT systems can lead to costly downtime as plants scramble to restore operations. 3. Supply Chain Vulnerabilities Third-Party Risk: Manufacturing companies often rely on extensive global supply chains, working with multiple suppliers and contractors. These third-party relationships can introduce vulnerabilities, as cybercriminals may target less secure suppliers to gain access to larger manufacturers. The attack on Target in 2013, for example, occurred when hackers accessed the company’s systems through a third-party HVAC vendor. Supply Chain Attacks: Cybercriminals may inject malware into software or hardware components within the supply chain, compromising the final product delivered to customers. Supply chain attacks are difficult to detect and can propagate through an entire ecosystem of partners. 4. Intellectual Property Theft Targeting Trade Secrets: Manufacturing companies often possess valuable intellectual property (IP), including patents, product designs, and proprietary production methods. Cybercriminals, particularly those engaging in corporate espionage or state-sponsored attacks, seek to steal this IP for competitive or geopolitical advantage. For example, hackers may target a company’s R&D department to access confidential product designs. Data Breaches: Cybercriminals may breach IT systems to steal sensitive information about products, processes, and customers. Loss of intellectual property can result in competitive disadvantages and legal consequences, especially in highly competitive industries like automotive or aerospace. 5. Vulnerabilities in Industrial IoT (IIoT) Devices Increased Attack Surface: The rise of Industrial Internet of Things (IIoT) devices has introduced new vulnerabilities. Connected sensors, controllers, and devices in factories can be exploited if not properly secured. Many IIoT devices lack built-in security features or use default passwords, making them prime targets for cyberattacks. Real-Time Monitoring and Control Risks: IIoT enables real-time data collection and monitoring, improving operational efficiency. However, it also means that an attack on these devices could disrupt real-time control systems, potentially leading to unsafe conditions, equipment damage, or production errors. 6. Phishing and Social Engineering Targeted Phishing Attacks: Manufacturing companies are not immune to phishing, and employees in these organizations may be targeted through deceptive emails designed to steal login credentials or introduce malware into the system. Spear-phishing attacks may be highly customized, impersonating suppliers or partners to trick recipients into clicking malicious links. Human Error: Social engineering attacks, such as phishing, exploit human vulnerabilities, often bypassing even well-established cybersecurity protocols. In environments where employees are managing both IT and OT systems, a single mistake could lead to a system-wide breach. 7. Lack of Cybersecurity Awareness and Training Skill Gaps: Many manufacturing employees, especially those working in OT environments, may lack sufficient training in cybersecurity. The focus is often on ensuring the smooth operation of machinery and production lines, with less emphasis on understanding how cybersecurity impacts these systems. This creates an environment where staff may not recognize the signs of a cyberattack. Cybersecurity Culture: Some manufacturing environments may prioritize production efficiency over security practices, leading to a culture of neglect when it comes to cybersecurity. This can manifest as poor password management, delayed system patches, and a lack of proper network segmentation. 8. Regulatory and Compliance Challenges Compliance with Security Standards: Depending on the industry and the countries they operate in, manufacturers must comply with various cybersecurity standards and regulations. These can include the NIST Cybersecurity Framework in the U.S. or ISO 27001 globally. In the EU, regulations like the General Data Protection Regulation (GDPR) can come into play if the cyberattack results in the loss of personal data. Managing Multiple Standards: The challenge for manufacturing companies is that they often have to comply with multiple cybersecurity and safety regulations across different regions. Maintaining compliance can be difficult, particularly when IT and OT systems have different requirements. Conclusion Manufacturing companies must navigate a new and complex cybersecurity landscape where threats come from many directions. The integration of IT and OT systems, increased use of IIoT, and reliance on third-party suppliers make the sector highly vulnerable
El doloroso coste de la ciberdelincuencia para el sector sanitario estadounidense

The painful cost of Cybercrime to the US Healthcare Sector In February 2024, UnitedHealth Group’s subsidiary, Change Healthcare, suffered a significant cybersecurity breach, which has had far-reaching consequences across the U.S. healthcare system. The attack, attributed to the ALPHV/BlackCat ransomware group, compromised both personally identifiable information (PII) and protected health information (PHI) for many individuals. Early estimates suggest that the breach affected a substantial portion of the U.S. population, with roughly 4 terabytes of data stolen. This breach disrupted UnitedHealth Group key operations, including the processing of medical claims and payments, which in turn affected hospitals, pharmacies, and other healthcare providers nationwide. As a result, some individuals were unable to use their insurance to access prescriptions, and healthcare providers faced financial strain due to frozen payments. UnitedHealth Group confirmed that the attack caused major outages, which they expected to fully resolve by the end of March 2024. In response to the attack, Change Healthcare resorted to manual processes to maintain business operations while working to restore its digital systems. The company paid an initial ransom of $22 million, but the costs related to recovery, system reconstitution, and business disruption could exceed $2.9 billion. Why Healthcare sector System Recovery needs an urgent upgrade This breach has raised broader concerns about the vulnerabilities within the healthcare sector, prompting discussions about the need for stricter cybersecurity regulations. Lawmakers are considering new policies to strengthen defenses and ensure that healthcare providers are better equipped to handle such attacks in the future. Although the HIPAA (Health Insurance Portability and Accountability Act) regulations outline specific requirements for System Recovery which we covered in a previous article, the act itself dates to 1996 with HIPAA’s Privacy Rule and Security Rule, which focus on the protection of personal health information (PHI) and electronic PHI (ePHI), being implemented several years after the act was introduced. The Privacy Rule became effective in 2003, and the Security Rule in 2005. Of course, much has changed in the world of cybercrime and data protection over the two decades since these rules became effective, but many healthcare organizations are still maintaining legacy systems supported by legacy backup and cybersecurity tools. Cristie Software can modernize System Recovery for the Healthcare sector Traditional backup and restore applications were originally designed to protect against system outages caused by hardware failures and natural disasters, they did not offer specific protection against cybercrime, or tools to assist with cyber recovery following an attack. Modern data protection applications have been designed from the ground up to secure data and aid cyber recovery with features such as immutable storage and isolated recovery. Cristie Software integrates seamlessly with modern data protection applications and takes cyber recovery many steps further by adding features such as multi-cloud disaster recovery support, advanced anomaly detection and cleanroom recovery to facilitate cyber forensics and backup integrity verification. Our system recovery software integrates with backup solutions from leading providers such as Rubrik, Cohesity, Dell Technologies and IBM. What should the US Healthcare sector focus on to improve Cyber Resilience? To reduce cybercrime, the U.S. healthcare sector must focus on strengthening its cybersecurity infrastructure, adopting mandatory standards, and investing in advanced technology. Key strategies include implementing robust encryption, multi-factor authentication, and a zero-trust architecture, which limits access to sensitive data unless explicitly verified. Regular vulnerability assessments and third-party risk management are also critical to addressing gaps in security. Additionally, comprehensive cybersecurity training for healthcare employees is essential to prevent human errors that can lead to breaches. Cyber Resilience through the adoption of AI and improved collaboration Healthcare providers should invest in AI-driven security tools and automation to detect and respond to threats in real-time. Cristie Software has incorporated features driven by Machine Learning (ML) into their software suite to provide early warning of malicious file encryption plus intelligent automated system recovery remediation which can solve many common system recovery failure scenarios without manual intervention. Collaboration between government agencies, like the Cybersecurity and Infrastructure Security Agency (CISA), and private sector organizations can improve information sharing and coordinated responses to attacks. Public-private partnerships, coupled with federal regulations that enforce minimum cybersecurity standards, could significantly strengthen defenses against cybercrime. Such measures would not only protect patient data but also ensure continuity in critical healthcare services. Conclusion In conclusion, reducing cybercrime in the U.S. healthcare sector requires a comprehensive approach involving a modernization of data security infrastructures, regular audits, and mandatory cybersecurity standards. By investing in AI-driven tools and enhancing collaboration between public and private entities, the sector can better protect sensitive data and maintain operational resilience. Implementing these strategies will be critical to safeguarding patient information, preventing disruptions in care, and ensuring the long-term security of the healthcare system against evolving cyber threats. Contact the Cristie Software team if you are looking to improve system recovery and replication for critical healthcare systems, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
Cristie Software sanitario

Cristie Software in Healthcare: Balancing Patient Data Security with Rapid Recovery The healthcare industry faces a unique challenge: safeguarding sensitive patient data while ensuring rapid system recovery in the event of failures or cyber incidents. With healthcare providers increasingly reliant on digital systems to manage patient records, treatment plans, and communication, the need to maintain uninterrupted access while protecting sensitive information is paramount. This is where Cristie Software solutions come into play, offering a comprehensive approach to both data security and system recovery that aligns with HIPAA (Health Insurance Portability and Accountability Act) compliance. Cristie Software supporting HIPAA Compliance and Data Security: The Cornerstone of Patient Trust HIPAA sets strict standards for protecting patient health information (PHI). Healthcare providers must ensure that all systems handling PHI are secure, with measures in place to prevent unauthorized access, breaches, or data loss. Non-compliance can result in heavy fines and reputational damage, making compliance not only a legal obligation but also a fundamental part of maintaining patient trust. Cristie Software solutions directly support HIPAA compliance by providing robust system recovery measures to safeguard systems holding PHI. Cristie CloneManager® and Cristie Recovery software integrate seamlessly with existing healthcare IT infrastructures to ensure that PHI systems as fully protected. These tools automate backup processes, ensure data encryption both in transit, provide early warning of malicious file encryption and provide audit trails to prove compliance during regulatory assessments. The Crucial Role of System Recovery In a healthcare environment, downtime can be life-threatening. Access to critical systems, including electronic health records (EHR) and patient management systems, must be restored as quickly as possible in the event of an outage or disaster. Whether it’s caused by hardware failure, cyberattacks, or human error, healthcare providers need to recover systems rapidly to minimize the impact on patient care. Cristie Software’s solutions are designed to provide automated and efficient recovery for these critical systems. Cristie recovery and replication software offers near-instant recovery of entire systems, allowing healthcare organizations to return to full operation without losing vital data. The suite’s replication and recovery capabilities ensure minimal downtime, allowing for a seamless transition to backup systems while the primary systems are restored. With Cristie’s Bare Machine Recovery (BMR) solutions, healthcare providers can restore entire servers in a matter of minutes, ensuring that patient services continue uninterrupted. BMR capabilities allow IT teams to recover not just data, but entire operating environments, including the configurations and settings necessary to bring systems back online without additional setup. Cristie Software – Combining HIPPA Compliance with Speed One of the most valuable aspects of Cristie Software’s solutions is the ability to balance HIPAA compliance with efficient recovery processes. Cristie CloneManager® allows healthcare organizations to create synchronized, real-time system clones that can be activated when the primary system goes down. These clones replicate not only the data but also system configurations, ensuring a complete, compliant backup that can be easily restored. The synchronization data transmitted between primary and secondary systems can also be encrypted during transit for added security. This functionality means healthcare IT teams can test and validate their recovery processes, ensuring they meet the stringent data security and availability requirements mandated by HIPAA. Staying Ahead with Regular Audits and Testing Cristie Software’s focus on continuous testing and validation further strengthens compliance efforts. HIPAA mandates regular risk assessments, including testing the effectiveness of backup and disaster recovery systems. Cristie’s tools enable healthcare providers to regularly test recovery procedures without disturbing the live environment, offering real-time verification that their recovery plans meet both regulatory requirements and internal service level agreements (SLAs). These proactive measures not only provide peace of mind but also help healthcare providers avoid costly downtime and potential HIPAA violations. The ability to perform live tests without impacting system availability is particularly valuable, as it allows organizations to validate their recovery processes without disrupting ongoing patient care. Conclusion Cristie Software solutions empower healthcare providers to strike a balance between data security and rapid recovery, ensuring that they remain compliant with HIPAA regulations while also minimizing system downtime. With automated, efficient recovery tools and robust data protection features, Cristie Software helps healthcare organizations maintain the availability and security of critical patient data—key to delivering high-quality care in today’s digital healthcare landscape. Contact the Cristie Software team if you are looking to improve system recovery and replication for critical healthcare systems, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
Recuperación en caso de catástrofe basada en la nube

Cloud-Based Disaster Recovery with Cristie Software: Benefits and Considerations In today’s digital-first world, disaster recovery (DR) is no longer an afterthought for organizations—it’s a critical component of business continuity. Whether it’s natural disasters, cyberattacks, or hardware failures, unforeseen events can have devastating effects on company operations. Cloud-based disaster recovery (DR) has emerged as a reliable solution, providing organizations with a flexible, scalable, and cost-effective approach to safeguarding their data and systems. However, as with any technology, it comes with both benefits and considerations. In this article, we’ll explore the advantages and potential limitations of cloud-based disaster recovery and discuss how Cristie Software helps clients leverage these solutions to ensure uninterrupted business operations. The Advantages of Cloud-Based Disaster Recovery & Cristie Software Cloud-based DR solutions have transformed the way organizations approach disaster preparedness. Here are some key benefits: Cost Efficiency One of the main advantages of cloud-based disaster recovery is cost efficiency. Traditional DR solutions often require significant investments in duplicate hardware, data centers, and infrastructure. By moving DR to the cloud, organizations can eliminate the need for maintaining costly secondary sites. Instead, they only pay for the cloud resources they use, typically on a pay-as-you-go basis. Cristie Software’s solutions provide clients with a predictable, cost-effective pricing model, ensuring they only pay for the recovery, replication or migration licences they need, while still having access to a full suite robust disaster recovery features. Scalability and Flexibility Cloud-based DR solutions are inherently scalable. As organizations grow and their data needs expand, they can easily increase their storage capacity in the cloud without worrying about hardware constraints. This flexibility allows organizations to customize their disaster recovery solutions based on their evolving needs. Cristie Software’s solutions are designed to integrate with a wide range of cloud platforms, enabling clients to scale their disaster recovery plans effortlessly. Whether a business is expanding rapidly or undergoing periods of change, Cristie ensures that DR capabilities keep pace with operational demands. Faster Recovery Times The goal of any disaster recovery plan is to minimize downtime, and cloud-based DR solutions excel in this area. Cloud infrastructure allows organizations to replicate their systems offsite, ensuring they can recover their data and applications within minutes after a disruption. This rapid recovery capability is essential for businesses that need to maintain high availability and minimize the risk of lost revenue or productivity. Cristie Software provides clients with solutions that offer near-instant recovery, ensuring that systems can be up and running quickly in the event of a failure. Fast recovery capabilities are particularly critical for industries such as healthcare, finance, and manufacturing, where downtime can lead to significant operational and reputational damage. Automation and Reduced Complexity Traditional disaster recovery processes can be labor-intensive, requiring manual intervention and frequent testing. Cloud-based DR solutions simplify this by automating many of the processes involved in data backup, replication, and recovery. This reduces the risk of human error and ensures that businesses can maintain a high level of readiness without dedicating excessive resources to managing their DR environments. Cristie’s recovery solutions provide powerful automation features such as automated cloud target system provisioning which can save significant time when migrating multiple systems to the cloud for redundancy as part of a DR strategy. Geographic Redundancy A key advantage of cloud-based DR is the ability to store data across geographically dispersed locations. This geographic redundancy ensures that even if a disaster impacts a particular region, data remains safe and accessible from another location. By spreading data across multiple cloud data centers, organizations significantly reduce the risk of complete data loss in the event of a localized disaster. Cristie Software is used by many clients to ensure that their cloud-based DR solutions include geographic redundancy, guaranteeing that data is available no matter where a disaster may strike. Considerations for Cloud-Based Disaster Recovery with Cristie Software While cloud-based disaster recovery offers numerous advantages, there are important considerations that organizations need to account for when implementing these solutions. Data Transfer Speeds and Bandwidth One of the potential limitations of cloud-based DR is the reliance on network connectivity for data transfer. Large volumes of data may require significant bandwidth, and slow data transfer speeds could impact the efficiency of the backup and recovery process. Organizations need to ensure that they have sufficient bandwidth to handle their data replication and recovery needs, especially during a disaster. Cristie Software can help clients to optimize data transfer speeds with features such as changed block tracking, file compression and bandwidth throttling, ensuring that recovery and replication processes are efficient and effective, even when large datasets are involved. Security and Compliance While cloud providers often offer robust security measures, organizations are still responsible for ensuring that their disaster recovery strategies meet industry-specific compliance requirements. Data encryption, access controls, and regulatory compliance (such as HIPAA, GDPR, or PCI DSS) must be incorporated into any cloud-based DR plan. Cristie Software helps clients navigate these security and compliance challenges by providing end-to-end encryption for replica synchronization, secure access controls, and solutions that comply with industry regulations. This ensures that client data remains protected throughout the disaster recovery process. Vendor Lock-In Choosing a cloud provider for disaster recovery can sometimes lead to vendor lock-in, where switching providers becomes difficult or costly due to proprietary formats or systems. Organizations should carefully evaluate their options and seek flexible solutions that allow for portability between different cloud platforms. Cristie’s recovery solutions integrate with a wide range of virtual and cloud platforms, giving clients the freedom to choose or switch between cloud providers as their needs change, without being tied to a specific vendor. Ongoing Management and Monitoring While cloud-based DR solutions reduce much of the complexity of traditional DR, organizations still need to manage and monitor their systems to ensure they’re functioning correctly. Regular testing and monitoring are essential to ensure that the recovery process will work as expected when disaster strikes. Cristie Software provides clients with tools for ongoing monitoring, testing, and reporting, ensuring that their DR environments are always ready for deployment.
Servicios financieros: Recuperación en caso de catástrofe en la era de FinTech
Financial Services: Disaster Recovery for the Age of FinTech The financial services industry has undergone a digital revolution driven by FinTech (financial technology). With innovations like blockchain, mobile banking, AI-powered financial tools, and payment gateways, the sector has become more efficient but also more vulnerable to disruptions, including cyberattacks, system failures, and natural disasters. The rise of real-time transactions and digital ecosystems means that downtime can be devastating, both financially and reputationally. This highlights the critical importance of a reliable disaster recovery (DR) strategy. Exploring Unique Challenges and Solutions for System Recovery in the Evolving FinTech Landscape. In the financial services industry, disaster recovery isn’t just a safeguard—it’s a legal and operational requirement. Regulatory standards such as DORA, GDPR, NIS2, SOX, PCI-DSS, and FCA/PRA Operational Resilience directives in the UK mandate strict guidelines on data protection and recovery, with severe penalties for non-compliance. As FinTech accelerates innovation, firms must adapt their DR strategies to ensure business continuity, maintain data integrity, and comply with these regulations. Cristie Software provides a robust solution for this challenge through its recovery and replication software, helping financial firms protect their critical data. Key Challenges in FinTech Disaster Recovery. Real-time Transactions and 24/7 Availability In the FinTech era, consumers expect 24/7 access to financial services, whether for mobile banking, online payments, or stock trading. Any disruption, even for a few minutes, can lead to massive financial losses and a loss of customer trust. This poses a unique challenge in disaster recovery. Traditional backup systems, which perform nightly backups or periodic data snapshots, may not be sufficient. Cristie Software’s continuous data replication and near-instant recovery capabilities address this challenge by enabling real-time protection. This ensures that, in the event of a disaster, businesses can restore their operations rapidly minimizing real-time data loss, downtime and financial risk. Complex IT Infrastructures FinTech companies often operate on complex, hybrid IT infrastructures that include on-premises systems, cloud platforms, and third-party services. These infrastructures are often interwoven, making it difficult to coordinate disaster recovery efforts across multiple environments. Any failure in these systems could disrupt workflows and customer service. Cristie’s DR solutions are designed to work across heterogeneous environments, offering seamless recovery for both cloud-based and on-premises systems. Our server replication and recovery software helps ensure that both primary and secondary systems are synchronized, enabling organizations to recover quickly across all environments. Regulatory Compliance In financial services, regulatory compliance is non-negotiable. Financial firms must adhere to strict data protection laws, such as the General Data Protection Regulation (GDPR), DORA, NIS2, Sarbanes-Oxley Act (SOX), and Payment Card Industry Data Security Standard (PCI-DSS), all of which mandate stringent disaster recovery procedures to protect sensitive customer data. Cristie Software’s automated system recovery testing capabilities allow financial institutions to regularly validate their recovery plans without manual intervention. This ensures compliance with regulatory requirements while also providing audit-ready reports, ensuring firms remain in full control of their data protection strategies. Cybersecurity and Ransomware Threats The increase in cybercrime, particularly ransomware attacks, is a significant concern for the financial services industry. FinTech firms are prime targets due to the sensitive nature of the data they handle. If an attack compromises core systems, it could take days or weeks to fully recover unless the firm has a robust cybersecurity and DR plan in place. Cristie’s data protection solutions advanced anomaly detection providing early warning of malicious file encryption plus cleanroom recovery to facilitate cyber forensics within an isolated environment. Additionally, point-in-time recovery options available within the backup solutions we support from vendors such as IBM, Rubrik, Cohesity and Dell Technologies allow firms to restore data to an exact moment before the attack occurred, avoiding further disruption. Client Trust and Reputation Management Any downtime or data breach can significantly damage a financial institution’s reputation. In the world of FinTech, where competition is fierce, maintaining client trust is crucial. Customers expect seamless service and absolute protection of their personal and financial data. Cristie Software helps mitigate the risk of reputation damage by offering rapid recovery and replication solutions that ensure continuous uptime and data integrity. Our bare-metal recovery capabilities enable organizations to restore entire systems, including applications and databases, in minutes, allowing firms to minimize client impact and maintain service continuity during disasters. Key Solutions from Cristie Software for FinTech Disaster Recovery. 1. Automated Recovery and TestingCristie offers automated disaster recovery testing without interrupting live systems. This feature allows financial firms to test their DR plans frequently, ensuring their systems are ready to respond to any crisis. Regular DR testing helps businesses meet regulatory compliance standards while providing peace of mind that systems can be recovered swiftly in the event of a disaster. 2. Bare Metal Recovery (BMR)One of Cristie Software’s standout features is bare metal recovery (BMR). This technology allows organizations to recover entire systems, from hardware configurations to software applications, onto entirely new hardware. This is especially useful in the financial sector where physical machines are prevalent, and where a failed server could contain critical trading applications or transaction logs. Cristie’s BMR enables rapid restoration to minimize downtime, even on dissimilar hardware. 3. Continuous ReplicationTo handle the high availability demands of FinTech, Cristie’s continuous replication feature allows for near-instantaneous recovery points. By continuously replicating data to secondary systems, financial firms can be assured that their backup data is always up-to-date. This level of real-time protection is essential in minimizing data loss and ensuring fast failover. 4. Scalable and Flexible SolutionsCristie Software’s recovery solutions are designed to be scalable and flexible, meeting the needs of both small FinTech startups and large financial enterprises. Whether a firm is using on-premises infrastructure, cloud-based environments, or a hybrid of both, Cristie’s solutions ensure seamless integration and compatibility across all platforms. The scalability of these solutions means that as the firm grows, its DR capabilities can grow with it. Conclusion: Future-Proofing Disaster Recovery in the FinTech Era. The FinTech revolution has created both opportunities and challenges for financial services. While technology has introduced innovative services, it has also heightened the
El estado de la recuperación ante catástrofes y la ciberrecuperación, 2024-2025

IDC/Zerto – The State of Disaster Recovery and Cyber-Recovery, 2024–2025. IDC recently published the white paper “The State of Disaster Recovery and Cyber-Recovery, 2024–2025: Factoring in AI” sponsored by Zerto which highlights current trends in disaster protection strategies in the face of growing cybercrime. The paper also presents survey results regarding the adoption of artificial intelligence (AI) within data protection and cyber-resilience solutions. Here we examine the key findings of this report and discuss how system recovery solutions from Cristie Software can help users of backup solutions such as Zerto to address the gaps reported by the respondents to this report. Backup and recovery alone are insufficient for fast, effective Disaster Recovery (DR) or Cyber Recovery (CR). While backup and recovery (B/R) are foundational to data recovery, a complete disaster recovery solution needs to include the recovery of systems and underlying infrastructure, which in a modern IT environment, invariably involves a hybrid of physical, virtual and cloud platforms. Effective DR may involve moving application services and data to a second site using asynchronous or synchronous data replication, replicated infrastructure, plus application failover/failback processes between these diverse operating environments. CR builds upon B/R and DR processes with additional requirements for malware detection, forensic analysis, cleanroom recovery, and more. For this reason, backup modernization was among the top 3 IT initiatives for respondents to the survey over the next 12 months. When asked about the most important criteria when selecting backup and DR tools, the top response was “breadth of solution” indicating that companies are looking to modernize their entire B/R and DR toolset and processes. How does Cristie Software help with B/R, DR and CR modernization? Cristie Software recovery and replication solutions complement B/R solutions like Zerto and other leading solutions from vendors such as IBM, Dell Technologies, Rubrik and Cohesity. Our software works seamlessly with B/R solutions to deliver many benefits. Physical system recovery automation: Physical systems present the biggest system recovery administration overhead due to the frequent need for manual intervention. Cristie Software can automate the physical system recovery workflow eliminating manual intervention and facilitating automated physical system recovery at scale. Physical, virtual or cloud recovery & replication, in any direction: Although modern B/R solutions can utilize both on-prem and cloud targets, the addition of Cristie Software provides complete omni-directional system recovery between physical, virtual and cloud targets with features such as automated resource provisioning and dissimilar hardware technology. With many companies looking to move DR to the cloud, having complete flexibility over source and target system direction is a vital feature to include in any B/R modernization plan. Cleanroom recovery: The addition of Cristie Software allows recovery to isolated networks to assist cyber forensics or facilitate backup integrity verification in isolation from the production environment. Human factors impacting B/R, DR and CR: Staff availability, skills shortages and human error. The IDC survey highlights that IT personnel time and resource availability plus IT skills are in the top 3 biggest challenges organizations face with respect to disaster recovery. Human error was shown to be the biggest reason for data loss. Cristie Software can help to address each of these human factors through features such as automation, recovery orchestration, and the ongoing use of predictive AI. Recovery automation: By eliminating manual intervention IT resources can be spared and at the same time human error can be reduced. Recovery orchestration: More complex recovery workflows can be implemented through orchestration jobs further reducing IT administration overhead. Recovery failure remediation through machine learning (ML) and AI: Cristie are implementing ML and AI to provide automated recovery job failure remediation plus AI driven administrator guidance within the Cristie Virtual Appliance (VA) to reduce the need for specialist IT system recovery skills. Organizations need solutions to meet SLAs and provide the fastest recovery with the least data loss. System recovery time objectives (RTO) differ between organizations and business applications but rarely does system downtime does not equate to revenue loss, therefore the desire to reduce system recovery times featured highly in the survey responses. Meeting internal and external SLAs may require very specific RTOs with regulated industries such as financial services and healthcare having SLAs that incur may penalties if not met. To ensure that system recovery processes are capable of meeting SLAs testing should be a core component of every DR plan. Cristie Software provides several features to assist in recovery testing and verification. Recovery simulations: The simulation of any recovery job can be scheduled to provide a clear indication of the recovery time that the supporting infrastructure is able to deliver. This can provide early warning of network, storage and processing resources that may need need upgrades to meet specific RTOs. Recovery reporting: The Cristie VA serves as the single interface for all tasks and provides comprehensive reporting on recovery and replication job status. These extensive reports can help meet self-assessment and testing requirements that are often mandatory within industry regulations. Summary The findings within this report correlate with our experience as customers look to modernize their B/R solutions to support hybrid cloud architectures and multi-cloud environments. Despite the widespread adoption of virtualization, physical systems are still prevalent where application performance is vital, or to support legacy applications, therefore the automation of physical system recovery is an essential feature that organizations should include in their modernization plan. Read the full IDC report sponsored by Zerto here. Contact the Cristie Software team if you are in the process of addressing any of the challenges highlighted in this article, or to learn more about system replication and our system recovery integration with leading B/R solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
El verdadero coste de la ciberdelincuencia en el sector manufacturero estadounidense

The True Cost of Cybercrime in the Manufacturing Sector: Impact, Case Studies, and Mitigation Ransomware is a rapidly growing threat causing the cost of cybercrime to US manufacturing to extend far beyond financial losses. As more manufacturing companies embrace digital transformation, they expose themselves to vulnerabilities in their IT and operational technology (OT) systems. The economic impact of cyberattacks on this industry includes direct costs from ransom payments, lost productivity, disrupted operations, and reputational harm, alongside indirect costs such as regulatory fines and increased security expenses. This article explores the cost of cybercrime in the manufacturing sector, highlighting specific examples from the United States and outlining strategies manufacturers can adopt to mitigate these risks. 1. The Financial Burden of Cybercrime on Manufacturing Manufacturers face considerable financial losses from cyberattacks. According to a recent report by IBM, the average cost of a data breach in the manufacturing industry is approximately $4.24 million. Costs associated with cyber incidents include: Direct Financial Losses: Immediate costs such as ransom payments and recovery expenses can quickly amount to millions. Operational Downtime: Attacks on critical systems can halt production, leading to significant losses in productivity and delayed orders. Legal and Compliance Costs: Manufacturers may face fines for breaches that expose customer or supplier data, particularly under regulations such as GDPR and CCPA. Reputational Damage: Customer trust and brand reputation can suffer after an attack, potentially resulting in lost contracts and diminished market share. Security Costs: Companies often face increased costs for enhanced cybersecurity measures and insurance following a breach. 2. High-Profile Cyberattacks on U.S. Manufacturers Several recent cyber incidents in the United States reveal the devastating impact of cybercrime on manufacturing: Norsk Hydro (2019): Although Norsk Hydro is based in Norway, its U.S. operations suffered from a ransomware attack that disrupted production for days, costing the company nearly $50 million. The attack impacted IT systems and OT environments, forcing the company to switch to manual operations temporarily. Honda (2020): A cyberattack on Honda’s U.S. manufacturing systems halted production at several plants. The attack, reportedly carried out by a ransomware group, caused significant downtime and affected Honda’s ability to meet market demand. While Honda did not disclose exact figures, such disruptions likely resulted in millions of dollars in lost productivity and recovery costs. JBS USA (2021): The world’s largest meat supplier, JBS, fell victim to a ransomware attack that forced the company to shut down plants across the United States. JBS paid an $11 million ransom to resume operations, highlighting the high-stakes nature of attacks on critical manufacturing infrastructure. Kaseya Supply Chain Attack (2021): Although Kaseya itself is not a manufacturer, the ripple effects of the attack impacted numerous U.S. manufacturers who relied on its IT management software. This supply chain attack affected thousands of companies, underscoring the vulnerabilities in interconnected manufacturing supply chains. 3. Why the Manufacturing Sector is Vulnerable Several factors make manufacturing particularly susceptible to cybercrime: Convergence of IT and OT Systems: The integration of IT systems with OT creates vulnerabilities, as OT systems were not originally designed with cybersecurity in mind. Complex Supply Chains: Manufacturers rely on a web of suppliers, making them vulnerable to third-party risks from compromised partners or software. Aging Infrastructure: Many manufacturers still use legacy systems that are difficult to secure, making them attractive targets for cybercriminals. Industry 4.0 Adoption: As manufacturers move toward digital and automated processes, including the Internet of Things (IoT) and robotics, they introduce additional entry points for attackers. 4. The Indirect Costs of Cybercrime in Manufacturing While direct costs such as ransom payments and repair expenses are substantial, the indirect costs of cybercrime are equally significant: Supply Chain Disruptions: A cyberattack can halt operations for days, leading to delayed shipments and disrupted supply chains. These disruptions create ripple effects, affecting downstream customers and other suppliers. Customer and Partner Trust: Breaches can erode trust with clients and partners who expect secure handling of proprietary information. Increased Insurance Premiums: After a cyberattack, companies may face higher insurance premiums or additional costs for cyber insurance. 5. Mitigating Cyber Risks in Manufacturing Manufacturers can protect themselves from cybercrime by adopting a multi-layered security approach, leveraging advanced technologies, and ensuring ongoing employee training. Here are a few best practices: Do no overlook full System Recovery: Having a regular backup schedule for application data is commonplace for most organizations, but many overlook the steps needed to achieve full system recovery in the event of a disaster or cyberattack. Physical systems are inherently more time consuming to recover following an incident, especially if systems need to be recovered to dissimilar hardware. Cristie Software recovery solutions can overcome these challenges with advanced automation features, reducing recovery times and eliminating user intervention. Invest in Endpoint Protection and Network Monitoring: Protecting endpoint devices and continuously monitoring network traffic can help detect anomalies early, enabling rapid response to potential threats. Adopt a Zero Trust Model: Zero Trust requires all users and devices to be authenticated and authorized continuously, minimizing risks from compromised credentials. Segment IT and OT Networks: By separating IT from OT environments, manufacturers can reduce the chances of a single attack spreading across both systems. Regular Security Audits and Penetration Testing: Conducting routine security assessments can help identify vulnerabilities before attackers exploit them. Employee Training on Phishing and Social Engineering: Employees are often targeted through phishing emails and other tactics; regular training can improve awareness and reduce the chances of successful attacks. Looking Forward: Strengthening Resilience in Manufacturing As cyber threats continue to grow, the manufacturing sector must prioritize cybersecurity alongside other operational needs. With cybercriminals becoming more sophisticated and targeting critical industries, investment in cybersecurity and system recovery is not just a defensive measure but a strategic imperative. By adopting stronger security practices, manufacturers can better protect their operations and maintain resilience in the face of evolving cyber threats. Investing in cybersecurity is essential to safeguarding the future of manufacturing and ensuring the industry can continue to innovate without the shadow of cybercrime undermining its progress. Contact the Cristie Software team
No deje su Plan de Recuperación del Sistema para cuando más lo necesite

No deje su plan de recuperación de sistemas para cuando más lo necesite La recuperación de sistemas suele pasarse por alto. Muchas organizaciones no se dan cuenta de la importancia de contar con un sólido plan de recuperación de sistemas junto con las copias de seguridad de los datos de sus aplicaciones hasta que es demasiado tarde. Los accidentes, los desastres naturales, los fallos de hardware y los ataques de malware pueden ocurrir en cualquier momento y, sin un plan de recuperación de sistemas adecuado, estos incidentes pueden provocar una pérdida de datos y un tiempo de inactividad significativos. He aquí algunas razones por las que a menudo se pasa por alto la recuperación de sistemas: Falta de concienciación: Muchas organizaciones simplemente no son conscientes de los riesgos que implica no tener un plan de recuperación del sistema junto con su copia de seguridad de datos regular. Exceso de confianza: Algunas organizaciones pueden creer que sus sistemas son demasiado seguros para verse afectados por problemas. Complejidad: Crear y mantener un plan de recuperación de sistemas además de la copia de seguridad periódica de los datos puede parecer complejo y llevar mucho tiempo. Sin embargo, las consecuencias de descuidar la recuperación del sistema pueden ser graves. El tiempo de inactividad del sistema y la pérdida de datos pueden tener un impacto significativo en las personas y las empresas, provocando pérdidas financieras, problemas de productividad y daños a la reputación. Es esencial dar prioridad a la recuperación del sistema y tomar medidas proactivas para proteger la infraestructura vital que aloja sus datos. Esto significa crear copias de seguridad periódicas del sistema, además de los datos de sus aplicaciones, probar su plan de recuperación del sistema y mantenerse al día con los parches de seguridad. Cómo simplifica Cristie Software la recuperación de sistemas informáticos Cristie Software ofrece un conjunto de herramientas diseñadas para agilizar y automatizar los procesos de recuperación de sistemas informáticos. He aquí 10 formas en que simplificamos la recuperación de sistemas: Copia de seguridad y recuperación automatizadas: Cristie Software automatiza el proceso de recuperación de sistemas, reduciendo los pasos manuales implicados y minimizando el tiempo de inactividad. Nuestras soluciones permiten la rápida recuperación de sistemas completos, aplicaciones y datos tras un fallo o desastre. Recuperación Bare Metal (BMR): Las soluciones BMR de Cristiepermiten la recuperación de sistemas completos, incluidos sistemas operativos, configuraciones, aplicaciones y datos, en hardware diferente o entornos virtuales. Esto elimina la necesidad de reinstalar manualmente el software, ahorrando tiempo y reduciendo errores. Compatibilidad con las principales soluciones de copia de seguridad: Las herramientas de Cristiese integran perfectamente con las soluciones de copia de seguridad más populares de proveedores líderes como Cohesity, Rubrik, Dell Technologies e IBM, proporcionando un enfoque unificado para la protección y recuperación de datos. Soporte multiplataforma: Cristie Software admite la recuperación a través de diferentes plataformas, como entornos físicos, virtuales y en la nube. Esta flexibilidad facilita la adaptación a una amplia variedad de infraestructuras de TI. Recuperación de Hardware Disímil: Nuestra tecnología permite la recuperación en diferentes plataformas de hardware sin intervención manual, lo que garantiza la flexibilidad y la continuidad. Migraciones virtuales y a la nube: Las soluciones Cristie facilitan la migración de sistemas entre entornos físicos, virtuales y en la nube sin problemas, lo que facilita el mantenimiento de la continuidad del negocio y la adaptación a las necesidades cambiantes de la infraestructura. Pruebas y validación: El software de Cristiepermite probar fácilmente y sin interrupciones los planes de recuperación. Los usuarios pueden verificar sus capacidades de recuperación ante desastres sin afectar a los sistemas activos, lo que garantiza la preparación sin tiempo de inactividad. Tiempo de recuperación rápido: Al agilizar el proceso de restauración de los entornos de TI, Cristie ayuda a las empresas a reducir los tiempos de recuperación (RTO), minimizando el impacto en las operaciones y mejorando la capacidad de recuperación. Gestión centralizada: La consola de gestión de Cristieproporciona una única interfaz para gestionar las copias de seguridad, las migraciones y los procesos de recuperación, simplificando la gestión general y la supervisión de los sistemas de TI. Detección avanzada de anomalías: Nuestro software puede detectar el inicio del cifrado de archivos de malware, proporcionando una advertencia anticipada de la actividad de ransomware. En esencia, Cristie Software simplifica la recuperación de los sistemas de TI proporcionando soluciones automatizadas, integradas y eficientes que ayudan a las empresas a proteger sus infraestructuras y datos y a minimizar el impacto de las interrupciones. Explore nuestras soluciones y casos de uso para descubrir cómo otros están simplificando la implementación de la recuperación de sistemas de TI con la recuperación y replicación de Cristie . Póngase en contacto con el equipo de Cristie Software para obtener más información sobre la recuperación del sistema, la replicación y cómo podemos automatizar la recuperación del sistema para mejorar los tiempos de recuperación y simplificar todo su flujo de trabajo de recuperación de desastres ...
Recuperación de ransomware: Una guía completa

Recuperación de ransomware: Una guía completa Los ataques de ransomware son una amenaza creciente que paraliza empresas y organizaciones de todos los tamaños. Estos programas maliciosos encriptan los datos y los hacen inaccesibles hasta que se paga un rescate para recuperar el control. Por desgracia, el pago del rescate no garantiza la recuperación de los datos y alimenta la industria de la ciberdelincuencia. Esta completa guía explora las estrategias para prevenir los ataques de ransomware y cómo Cristie Software permite a las organizaciones recuperarse rápidamente en caso de ataque. Prevención de ataques de ransomware: Su primera línea de defensa Eduque a los empleados: Los correos electrónicos de phishing son un punto de entrada común para el ransomware. Forme a los empleados para que reconozcan los intentos de phishing y eviten hacer clic en enlaces o archivos adjuntos sospechosos. Parchee los sistemas con regularidad: Las vulnerabilidades sin parchear pueden proporcionar a los hackers puertas traseras a su red. Actualice regularmente el software y los sistemas operativos con los últimos parches de seguridad. Utilice contraseñas seguras y autenticación multifactor (MFA): Dificulte el acceso de los piratas informáticos a su sistema exigiendo contraseñas seguras y activando la autenticación multifactor, que añade una capa adicional de seguridad. Haga copias de seguridad periódicas: Mantenga copias de seguridad periódicas de sus datos en un sistema independiente y seguro. Esto le permitirá recuperar sus datos rápidamente en caso de un ataque de ransomware. Segmente su red: Limitar el acceso a los datos críticos segmentando tu red puede minimizar el impacto de un ataque de ransomware en caso de que eluda las defensas iniciales. Utilice software antivirus y antimalware: Emplee un software de seguridad de confianza que pueda detectar y evitar que el malware infecte sus sistemas. Cristie Software: su socio en la recuperación de ransomware Incluso con las mejores estrategias de prevención, un ataque de ransomware con éxito sigue siendo una posibilidad. Ahí es donde entra Cristie Software: Recuperación más rápida del sistema: La solución Bare Metal Recovery (BMR) de Cristieautomatiza la recuperación de máquinas físicas y virtuales, minimizando el tiempo de inactividad y consiguiendo que su negocio vuelva a estar en línea rápidamente. Recuperación de datos segura y verificable: Las soluciones de recuperación de Cristie pueden ayudar a garantizar que los datos recuperados estén completos y seguros antes de que los sistemas vuelvan a estar en línea. A través de nuestra función de recuperación de red aislada, se pueden recuperar sistemas completos en un entorno de sala blanca para probar la integridad de los datos antes de restaurar las máquinas de producción al entorno activo. Recuperación y replicación completas integradas con su entorno de copia de seguridad: Las soluciones de Cristiese integran perfectamente con las principales soluciones de copia de seguridad de proveedores como Cohesity, Rubrik, Dell Technologies e IBM, lo que le permite restaurar sistemas y datos de manera eficiente sin gastos adicionales. Orquestación de recuperación ante desastres: Cristie automatiza los flujos de trabajo de recuperación ante desastres, reduciendo los errores humanos y garantizando una respuesta coordinada y rápida ante un ataque. Informes detallados y auditoría: Genere informes completos sobre las actividades de recuperación, facilitando las investigaciones forenses y el análisis posterior al ataque. Ventajas del uso de Cristie Software: Tiempo de inactividad minimizado: Consiga que su empresa vuelva a funcionar rápidamente con una rápida recuperación del sistema. Mantenimiento de la seguridad de los datos: Garantice la integridad y seguridad de sus datos durante el proceso de recuperación. Costes reducidos: Evite la carga financiera que supone pagar un rescate recuperando sus datos de forma rápida y eficaz. Tranquilidad: Gane confianza sabiendo que dispone de una solución sólida para responder a un ataque de ransomware. Explore nuestras soluciones y casos de uso para descubrir cómo otros están impulsando su ciberrecuperación y ciberresiliencia con la recuperación y replicación Cristie . Póngase en contacto con el equipo de Cristie Software para obtener más información sobre la recuperación del sistema, la replicación y funciones como la recuperación en sala blanca y la detección avanzada de anomalías que pueden ayudar a prevenir y recuperarse de los ciberataques.
Sectores con estrictos requisitos de recuperación de sistemas y recuperación de desastres

Industries with Stringent DR and System Recovery Requirements Several industries face stringent regulations regarding disaster recovery and computer system recovery time objectives. These regulations aim to ensure business continuity and protect sensitive data in the event of disruptions. Here are some prominent examples: Financial Services Banking: Banks are subject to strict regulations, such as the Dodd-Frank Act in the US and the Digital Operational Resilience Act (DORA) and Second Payment Services Directive (PSD2) in the EU, which mandate robust disaster recovery plans. Insurance: Insurance companies must comply with regulations like Solvency II (EU) and the NAIC Cybersecurity Model Law (US), requiring strong data protection and business continuity measures. Capital Markets: Stock exchanges and other financial market participants face regulatory oversight through bodies such as the Securities Commission, often requiring specific data recovery and business continuity standards. Healthcare HIPAA: The Health Insurance Portability and Accountability Act (HIPAA) in the US imposes strict data privacy and security rules, including requirements for disaster recovery planning. GDPR: The General Data Protection Regulation (GDPR) in the EU mandates data protection and recovery measures, especially for healthcare organizations handling sensitive patient data. Energy FERC: The Federal Energy Regulatory Commission (FERC) in the US requires electric power companies to maintain reliable operations and have robust cyber security and recovery plans. NCPA: The National Cybersecurity Preparedness Act (NCPA) in the US mandates critical infrastructure entities, including energy companies, to implement cybersecurity best practices. Transportation FAA: The Federal Aviation Administration (FAA) in the US has strict regulations governing the cybersecurity and resilience of aviation systems. DOT: The Department of Transportation (DOT) in the US imposes cybersecurity requirements on various transportation modes, including railways and highways. Government NIST: The National Institute of Standards and Technology (NIST) provides cybersecurity frameworks and guidelines that government agencies must follow. CISA: The Cybersecurity and Infrastructure Security Agency (CISA) in the US mandates critical infrastructure organizations, including government agencies, to implement cybersecurity best practices. These are just a few examples of industries with stringent disaster recovery and system recovery requirements. The specific regulations and standards vary by jurisdiction and industry sector. Industries with Stringent DR and System Recovery Requirements: How Cristie Software Can Help Several industries face stringent regulations regarding disaster recovery and computer system recovery time objectives (RTOs) and system recovery verification (SRV). These regulations aim to ensure business continuity and protect sensitive data in the event of disruptions. We explored above certain key industries facing such regulations. Now, let’s delve into how Cristie Software empowers organizations in these sectors to improve their system recovery capabilities and meet regulatory compliance. Strengthening System Recovery in Regulated Industries Challenges Faced: Organizations in regulated industries often struggle with: Meeting RTOs: Ensuring critical systems are back online within regulatory timeframes can be challenging. Data Security and Integrity: Balancing rapid recovery with data security and verification procedures can be complex. Compliance Management: Keeping pace with evolving regulations and demonstrating compliance can be time-consuming and resource-intensive. Cristie Software Solutions: Cristie Software offers a comprehensive suite of solutions to address these challenges and enhance system recovery capabilities: Cristie BMR (Bare Metal Recovery): This software automates physical and virtual machine recovery, streamlining the process and minimizing downtime. Backup Integration: Cristie BMR seamlessly integrates with leading backup solutions from vendors such as Cohesity, Rubrik, Dell Technologies and IBM, enabling efficient data restoration and recovery. Automated Disaster Recovery Orchestration: Cristie’s solutions automate disaster recovery workflows, reducing human error and facilitating faster response times. Data Verification and Validation: Cristie software ensures recovered data is complete and consistent before bringing systems back online, meeting regulatory requirements for data integrity. Comprehensive Reporting and Auditing: Cristie provides detailed reports on recovery activities, facilitating compliance audits and demonstrating adherence to regulations. Benefits for Regulated Businesses By leveraging Cristie Software, organizations can: Achieve Faster RTOs: Faster system restoration with automation translates to minimized downtime and improved operational resilience. Ensure Data Security and Integrity: Robust data verification procedures safeguard sensitive data during recovery, meeting regulatory compliance. Simplify Compliance Management: Detailed reports and automated workflows streamline compliance efforts and reduce administrative burdens. Industry-Specific Solutions Cristie Software caters to diverse industry needs: Financial Services: Cristie’s solutions help financial institutions meet regulations like DORA, PSD2, and Solvency II, ensuring business continuity and data security. Healthcare: Cristie helps healthcare providers comply with HIPAA and GDPR, protecting patient data and ensuring rapid recovery of critical systems. Government and Critical Infrastructure: Cristie empowers government agencies and critical infrastructure entities to adhere to NIST, CISA, and other regulations, safeguarding sensitive data and national security. Ready to take control of your system recovery process and achieve regulatory compliance? Investing in Cristie Software solutions not only enhances system recovery capabilities but also positions organizations within regulated industries for long-term success by meeting compliance requirements and achieving optimal business continuity. Explore our solutions and use cases to discover how they can help your organization navigate the complexities of disaster recovery in today’s regulatory landscape. Contact the Cristie Software team to learn more about system recovery, replication and recovery testing to meet the requirements of industry regulation.
NIS2: Subiendo el listón de la recuperación de sistemas informáticos para organizaciones

NIS2: La Directiva 2 de la UE sobre seguridad de las redes y sistemas de información (NIS2) sube el listón de la ciberseguridad en varios sectores. Un área crítica de atención es la recuperación de sistemas informáticos, que exige un enfoque más proactivo y sólido por parte de las organizaciones. Este artículo explora cómo NIS2 afecta a la recuperación del sistema de TI y cómo Cristie Software ayuda a las organizaciones a superar estos retos. NIS2 y el imperativo de recuperación del sistema de TI NIS2 obliga a las organizaciones de todos los sectores esenciales a dar prioridad a la resistencia operativa. Esto se traduce en garantizar que los servicios esenciales permanezcan operativos durante y después de ciberataques o fallos del sistema. A continuación se explica cómo afecta NIS2 específicamente a la recuperación de los sistemas de TI: Planes obligatorios de respuesta y recuperación de incidentes: Los planes detallados que describen los procedimientos para responder a incidentes y recuperar los sistemas afectados ya no son opcionales. Pruebas y preparación: Las pruebas periódicas de estos planes garantizan su funcionamiento eficaz en situaciones reales. Copia de seguridad y recuperación del sistema: Las copias de seguridad frecuentes y fiables del sistema son cruciales para su rápida restauración. Gestión de la continuidad del negocio: Las organizaciones deben contar con estrategias para mantener las operaciones críticas durante las interrupciones. Seguridad de la cadena de suministro: La resistencia de los sistemas informáticos se extiende a las dependencias de terceros proveedores. Cristie Software: su socio en el cumplimiento de NIS2 Cristie Software equipa a las organizaciones con las herramientas y la experiencia necesarias para superar estos retos relacionados con NIS2: Recuperación racionalizada del sistema: Las soluciones de Cristieofrecen sólidas funcionalidades de protección y recuperación de sistemas, garantizando la continuidad del negocio durante las interrupciones. Orientación experta: Obtenga acceso a profesionales de recuperación de sistemas que proporcionan un asesoramiento inestimable para lograr la recuperación de sistemas a escala e implementar estrategias de prueba de recuperación para ayudar a lograr el cumplimiento de NIS2. Ventaja de la automatización: La automatización de los procesos de recuperación de sistemas minimiza los errores humanos y agiliza las operaciones, garantizando la eficiencia. Cumplimiento de las exigencias de NIS2 con Cristie Software Al asociarse con Cristie Software, las organizaciones pueden: Fortalecer la recuperación de sistemas de TI: Implementar estrategias de recuperación sólidas que cumplan o superen los requisitos de NIS2. Mejorar la resistencia general: Aumentar la capacidad de su organización para soportar ciberataques y fallos del sistema con confianza. Simplificar el cumplimiento: Benefíciese de la experiencia y las soluciones de Cristie, simplificando el camino hacia el cumplimiento de NIS2. ¿Listo para tomar el control de la recuperación de su sistema de TI? Cristie Software permite a las organizaciones navegar por las complejidades de NIS2 y emerger con una infraestructura de TI más resistente. Explore nuestras soluciones y casos de uso para descubrir cómo puede abordar eficazmente los requisitos normativos y salvaguardar sus sistemas de TI. Póngase en contacto con el equipo de Cristie Software para obtener más información sobre recuperación de sistemas, replicación y pruebas de recuperación para cumplir los requisitos de NIS2.
Los MSP simplifican la migración de sistemas multiusuario con CloneManager
Afrontar los retos de la migración de sistemas para los MSP con Cristie Software Las complejidades de la migración de sistemas para los MSP pueden mitigarse significativamente utilizando las herramientas de replicación y migración de sistemas de Cristie Software. El software CloneManager de Cristiepermite a los MSP ofrecer fácilmente migración de sistemas como servicio a sus clientes. He aquí cómo las soluciones de Cristieabordan desafíos específicos: Entornos de TI diversos: Plataforma agnóstica: Las herramientas de Cristieadmiten varios sistemas, incluidos entornos físicos, virtuales y en la nube. Esto elimina la necesidad de múltiples soluciones de migración a través de diversas infraestructuras de clientes. Evaluaciones previas a la migración: Las herramientas pueden analizar los sistemas de origen, identificando posibles problemas de compatibilidad antes de que comience la migración. Migración y seguridad de datos: Replicación automatizada: El software de Cristieautomatiza la replicación de datos, garantizando una transferencia de datos coherente y segura al tiempo que minimiza la intervención manual. Soporte multi-tenant: Es fácil crear múltiples inquilinos dentro del dispositivo virtual (VA) Cristie . Los inquilinos están totalmente aislados y no pueden interactuar ni ver los datos de otro inquilino. Transferencias cifradas: Los protocolos seguros de transmisión de datos protegen la información sensible durante la migración. Compatibilidad de aplicaciones: Entornos de prueba en vivo: A través de Cristie VA, los MSP pueden crear entornos de prueba aislados para evaluar la funcionalidad de las aplicaciones en el sistema de destino antes de la migración completa. Adaptación de aplicaciones: Los desarrolladores pueden aplicar correcciones para adaptar las aplicaciones a fin de que funcionen en los nuevos entornos, reduciendo así la necesidad de realizar grandes modificaciones. Por ejemplo, la función de adaptación de aplicaciones del marco/infraestructura de compatibilidad de aplicaciones de Microsoft Windows permite a los desarrolladores aplicar correcciones a las aplicaciones (sin reescribir el código) creadas para Windows XP para que funcionen con versiones posteriores de Windows. Dentro del marco, se crean shims que actúan como amortiguador entre el programa y el sistema operativo Windows. La migración de red aislada mediante el CloneManager de Cristiey el VA de Cristie proporciona un entorno para probar la funcionalidad y la seguridad de los shimmers de las aplicaciones. Gestión del tiempo de inactividad: Tiempo de inactividad mínimo: Las soluciones de Cristiea menudo permiten una migración con tiempo de inactividad casi nulo, minimizando las interrupciones del servicio para los clientes. Migración por fases: Las herramientas pueden facilitar enfoques de migración por fases, lo que permite una transición gradual y controlada al nuevo sistema. Optimización de costes Automatización y eficiencia: Los procesos automatizados y los flujos de trabajo racionalizados conducen a migraciones más rápidas, reduciendo los costes generales del proyecto. Reducción del consumo de recursos: Minimice la dependencia del trabajo manual aprovechando las capacidades de automatización del software. Personal y experiencia: Herramientas fáciles de usar: Las soluciones de Cristieestán diseñadas para ser fáciles de usar, lo que reduce la dependencia de conocimientos especializados de migración dentro del equipo de MSP. Formación y asistencia: Cristie ofrece recursos de formación y asistencia para ayudar a los MSP a adquirir destreza en el uso de sus herramientas de migración. Comunicación y gestión de clientes: Informes detallados: Las herramientas proporcionan informes detallados sobre el progreso de la migración, lo que permite una comunicación clara con los clientes durante todo el proceso. Supervisión en tiempo real: Supervise el proceso de migración en tiempo real, lo que permite la solución proactiva de problemas y la comunicación con los clientes. Resumen En conclusión, Cristie Software equipa a los MSP con un sólido conjunto de herramientas para navegar por las complejidades de la migración de sistemas de forma eficiente y segura. Al aprovechar las soluciones de Cristie, los MSP pueden ofrecer a los clientes una transición más suave a las nuevas tecnologías, agilizar la incorporación a la nube, todo ello al tiempo que minimizan el tiempo de inactividad y optimizan los costes, fortaleciendo en última instancia su propuesta de valor. Aprenda cómo los MSP están utilizando CloneManager de Cristieen nuestros ejemplos de casos de uso de migración de sistemas. Póngase en contacto con el equipo de Cristie Software para obtener más información sobre la migración de sistemas, la automatización y las pruebas de compatibilidad aislada con CloneManager.
Por qué es crucial actualizar a la última versión de Windows
Mantener los servidores basados en Windows actualizados a la última versión suele pasarse por alto, pero es crucial para mantener la seguridad, el rendimiento y la funcionalidad general del sistema. Las actualizaciones del sistema operativo Windows pueden automatizarse con el software de replicación y migración CloneManager de Cristie, que simplifica el proceso de actualización entre las principales versiones del sistema operativo y proporciona un entorno de pruebas para evaluar la compatibilidad de las aplicaciones. Profundicemos inicialmente en por qué es tan importante actualizar a la última versión del sistema operativo. Protección de seguridad mejorada contra amenazas: Las amenazas modernas como el ransomware, el malware y los virus evolucionan constantemente. Microsoft publica periódicamente actualizaciones para hacer frente a estas amenazas, protegiendo su sistema y sus datos. Cierre de brechas de seguridad: Las versiones anteriores de Windows pueden tener vulnerabilidades que se han corregido en las nuevas. Al actualizar, está tapando eficazmente estas lagunas de seguridad. Rendimiento mejorado optimizado para hardware más reciente: Las nuevas versiones de Windows están diseñadas para aprovechar el hardware más reciente, lo que se traduce en tiempos de arranque más rápidos, un rendimiento más fluido y una mayor compatibilidad con las aplicaciones. Gestión de recursos: Las actualizaciones suelen incluir optimizaciones para la gestión de la memoria, el uso de la CPU y otros recursos del sistema, lo que se traduce en un sistema más ágil. Acceso a nuevas funciones Innovación al alcance de la mano: Las actualizaciones de Windows introducen nuevas características y funcionalidades para mejorar su experiencia de usuario. Esto puede abarcar desde herramientas de productividad mejoradas hasta innovadoras capacidades multimedia. Compatibilidad con aplicaciones modernas: Muchas aplicaciones modernas requieren la última versión de Windows para funcionar de forma óptima. La actualización garantiza la compatibilidad y evita posibles problemas. Soporte y compatibilidad Soporte ampliado: Microsoft proporciona soporte y actualizaciones durante un periodo determinado. Los sistemas obsoletos pueden perderse parches críticos y correcciones de seguridad. Compatibilidad de hardware y software: Las versiones más recientes de Windows ofrecen una mayor compatibilidad con el hardware y el software más recientes, lo que garantiza una integración perfecta. Cómo actualizar con seguridad y hacer copias de seguridad sistemáticas del sistema: Antes de actualizar, cree una copia de seguridad completa del sistema para evitar posibles pérdidas de datos. Compruebe la compatibilidad: Asegúrese de que su hardware y software son compatibles con la nueva versión de Windows. Actualice los controladores: Actualice los controladores después de la actualización para garantizar un rendimiento y una compatibilidad óptimos. Simplifique las actualizaciones del sistema operativo Windows y las pruebas de compatibilidad con CloneManager CloneManager® de Cristiele permite probar de forma segura las actualizaciones del sistema operativo Windows en un entorno sandbox basado en la nube. Esto garantiza la compatibilidad antes de desplegar la imagen actualizada en los sistemas de producción. CloneManager® automatiza las actualizaciones del SO Microsoft Windows tras la migración de la imagen inicial CloneManager® ofrece la posibilidad de actualizar automáticamente el SO Microsoft Windows tras transferir la imagen inicial al sistema de destino. Al seleccionar esta opción, se establece un sandbox de replicación dentro del sistema de destino, creando una instantánea de la imagen migrada para una capa thin-provisioned copy-on-write que puede recibir cambios y servir como instancia de prueba arrancable. Una vez arrancado el sistema, se inicia el proceso de actualización del sistema operativo de Microsoft. El usuario debe aplicar las licencias de SO necesarias tras la actualización. Una vez finalizada la actualización del sistema, se pueden producir dos resultados: el sistema puede arrancar en el nuevo sistema operativo para la validación de la aplicación o, si es necesario, se pueden realizar más actualizaciones para alcanzar la última versión. Las actualizaciones automáticas pueden hacer avanzar el sistema hasta el sistema operativo Windows más reciente, eliminando la necesidad de intervención manual. Sin embargo, cualquier actualización necesaria de las aplicaciones debe aplicarse manualmente a la imagen final. Resumen En conclusión, actualizar a la última versión de Windows no consiste sólo en obtener nuevas funciones; se trata de proteger el sistema, mejorar el rendimiento y garantizar la compatibilidad con la tecnología más reciente. Si da prioridad a estas actualizaciones, estará invirtiendo en la salud y seguridad a largo plazo de sus sistemas. Recuerde: Aunque es esencial mantenerse actualizado, realice siempre una imagen de copia de seguridad completa del sistema antes de emprender cualquier cambio importante en el mismo. Póngase en contacto con el equipo de Cristie Software para obtener más información sobre la automatización de actualizaciones del sistema operativo y las pruebas de compatibilidad aislada con CloneManager.
La recuperación rápida de CrowdStrike debería ser una realidad para los usuarios del software de recuperación del sistema

Fast CrowdStrike Recovery should be a reality for users of System Recovery software CrowdStrike recovery is an activity and topic of focus for many organizations following the CrowdStrike bug that caused a global IT outage on July 18th and 19th, 2024. The number of users effected is unknown, however, we can glean some insights from news reports: Widespread Disruption: News articles describe the outage as widespread, disrupting airlines, financial institutions, hospitals, and businesses. Large Organizations: The affected entities suggest a significant number of users, potentially impacting thousands or even millions of devices. It is clear the CrowdStrike update bug caused significant disruption for many organizations. What caused the CrowdStrike Falon update outage? The outage was caused by a faulty update for the Windows version of their Falcon sensor.Here’s a breakdown of the issue: Falcon Sensor: This is a core component of the CrowdStrike Falcon platform that runs locally on user devices and scans them for potential malware threats. Faulty Update: A specific update for the Windows version of the Falcon sensor contained a defect. System Crash: This defect triggered a “logic error” that caused the affected systems to crash and enter a continuous restart loop, often referred to as the “Blue Screen of Death” (BSOD) on Windows machines. Here’s some additional information: Limited Scope: The issue only affected the Windows version of the Falcon sensor, not Mac or Linux systems. Recovery: CrowdStrike identified the issue and deployed a fix. However, restarting the affected systems multiple times might have been necessary to complete the recovery process. It’s important to note that CrowdStrike has not released any official reports detailing the exact cause of the bug within the update. However, based on the available information, it appears to be a software error within the update itself that caused the system crashes. How would Cristie Software customers recover faster from the CrowdStrike update crash? CrowdStrike recovery presents a perfect use case for automated system recovery. In this explainer video, Sky News business correspondent Paul Kelso outlines the laborious manual process required to recover systems to a state that allows for deletion of the disruptive CrowdStrike driver file. Users with large server estates that do not utilize automated system recovery or boot management tools would face a significant amount of manual intervention and downtime in order to facilitate driver removal from all effected machines. Cristie Software bare machine recovery (BMR) provides system recovery from leading backup solutions such as Rubrik Security Cloud, Cohesity DataProtect, IBM Storage Protect and Dell Technologies backup solutions Avamar and Networker. Using Cristie recovery software automation, the following steps would be required to recover effected machines to a point before the disruptive CrowdStrike driver was applied: Reboot in DR environment: Reboot systems into DR environment (this can be automated using boot management tools with our web-boot ISOs). Recover systems to last known good point in time: Trigger recovery from backup server (Rubrik, Cohesity, IBM or Dell). Reboot system: Machines would reboot to the last known good state prior to the application of the disruptive driver. What is the manual CrowdStrike update recovery process? The recovery process for the CrowdStrike Falcon update bug depended on the severity of the issue and your access to the affected system. Here are the two main approaches taken from online research. Users effected by the CrowdStrike update bug should conduct their own due diligence and refer to CrowdStrike support services to verify the procedure for their specific environment: Booting into Safe Mode or Windows Recovery Environment (WinRE):This method was recommended by CrowdStrike for situations where the system continuously rebooted into a loop (BSOD). Here’s how it worked:• Boot into Safe Mode: This can be achieved through various methods depending on your system configuration. One common approach is to repeatedly press the F8 key during system startup.• OR Boot into WinRE: If Safe Mode is inaccessible, you can try booting into the Windows Recovery Environment (WinRE). This may involve using a bootable USB drive or recovery media provided by your system manufacturer.• Navigate to the Target Directory: Once in Safe Mode or WinRE, locate the folder containing the problematic CrowdStrike files. The specific path might vary, but it’s typically something like C:WindowsSystem32driversCrowdStrike.• Delete the Faulty File: Look for a file named “C-00000291*.sys” (the asterisk represents any wildcard characters) and delete it.• Reboot Normally: After deleting the file, attempt to reboot your system normally. If the issue was resolved, the system should boot up successfully. Detaching the Disk from a Virtual Server (Advanced Users):This option was suitable for virtualized environments where the affected system was running on a virtual machine (VM). It’s important to note that this method requires technical expertise and should only be attempted by experienced users. Here’s a simplified overview:1. Detach Disk: Detach the virtual disk volume from the impacted virtual server. Create a backup or snapshot of the disk volume as a precaution.2. Mount Disk on Another Server: Attach or mount the detached disk volume to a separate virtual server with a working CrowdStrike installation.3. Access and Delete File: Follow steps similar to the Safe Mode method to access the C:WindowsSystem32driversCrowdStrike directory and delete the “C-00000291*.sys” file.4. Reattach Disk and Reboot: Detach the disk from the temporary server, reattach it to the original impacted virtual server, and attempt a normal reboot. Additional Tips: Consult CrowdStrike Support: If you are unsure about the recovery process or encounter difficulties, it’s advisable to reach out to CrowdStrike support for assistance. Test Functionality: Once your system boots up successfully, verify that your CrowdStrike Falcon sensor is functioning correctly. Remember: These are general guidelines taken from online resources. The specific steps may vary depending on your system configuration and the severity of the issue. It’s always best to consult with a qualified IT professional if you are unsure about any of the recovery procedures. Conclusion The CrowdStrike driver update failure has demonstrated how vulnerable enterprises are to system level driver changes that have the ability to disrupt the boot process of any operating system. Most companies invest
Orquestando su regreso: Cómo la automatización agiliza la recuperación del sistema

Orquestando su regreso: Cómo la automatización agiliza la recuperación del sistema En el panorama digital actual, el tiempo de inactividad puede ser devastador. Cada minuto que un sistema está fuera de servicio se traduce en una pérdida de productividad, ingresos y, potencialmente, de confianza de los clientes. Las organizaciones buscan constantemente formas de minimizar el tiempo de inactividad y garantizar una rápida recuperación en caso de desastre, caída del sistema o ciberataque. Aquí es donde entran en juego la automatización y la orquestación de los procesos de recuperación. ¿Qué son la automatización y la orquestación en la recuperación de sistemas? Imagine una orquesta bien ensayada, en la que cada instrumento toca su parte en perfecta armonía. Esto es similar a la recuperación automatizada. Las tareas individuales dentro del proceso de recuperación, como notificar al personal de TI, aislar el sistema afectado e iniciar la restauración de datos, se automatizan utilizando flujos de trabajo predefinidos. La orquestación va un paso más allá, coordinando la ejecución de estas tareas automatizadas en la secuencia correcta para lograr una recuperación fluida y eficaz. Ventajas de automatizar y orquestar los procesos de recuperación: - Tiempos de recuperación más rápidos Al automatizar las tareas rutinarias, se minimiza la intervención humana, lo que conlleva tiempos de recuperación significativamente más rápidos. Esto minimiza el tiempo de inactividad y permite que los sistemas críticos vuelvan a estar en línea más rápidamente. - Reducción de errores Los procesos de recuperación manuales son propensos a errores humanos. La automatización elimina estos errores, garantizando una recuperación consistente y fiable en todo momento. - Eficiencia mejorada El personal de TI se libera de tareas repetitivas, lo que le permite centrarse en iniciativas más estratégicas como investigar la causa raíz de la interrupción e implementar medidas preventivas. - Mayor coherencia Los flujos de trabajo automatizados garantizan que los procedimientos de recuperación se sigan de forma coherente, independientemente de la persona que realice la recuperación. - Reducción de costes Los tiempos de recuperación más rápidos y la mejora de la eficacia pueden traducirse en un importante ahorro de costes. - Escalabilidad Los procesos de recuperación automatizados se pueden escalar fácilmente para adaptarse a entornos de TI cambiantes, conjuntos de servidores a gran escala y volúmenes de datos crecientes. - Cumplimiento mejorado La automatización puede ayudar a las organizaciones a cumplir los requisitos de recuperación de datos y preparación ante desastres. Cómo poner la automatización a su servicio: - Antes de automatizar los procesos de recuperación, es fundamental contar con un plan de recuperación bien definido. Este plan debe describir los pasos necesarios para recuperarse de distintos tipos de interrupciones y catástrofes. - Identifique oportunidades de automatización Analice sus procedimientos de recuperación actuales e identifique las tareas que pueden automatizarse. Suelen ser tareas manuales repetitivas con pasos bien definidos. - Invierta en las herramientas adecuadas Elija una solución que se integre perfectamente con su infraestructura informática actual y que ofrezca las funciones que necesita. Las soluciones de recuperación de sistemas de Cristie Software se integran con las principales soluciones de copia de seguridad de Rubrik, Cohesity, IBM y Dell Technologies, además de ofrecer recuperación de sistemas automatizada independiente si es necesario. - Pruebe y perfeccione Pruebe periódicamente sus flujos de trabajo de recuperación automatizada para asegurarse de que funcionan como se espera. Esto le permite identificar y abordar cualquier problema potencial antes de que se produzca un desastre real. Conclusión En el vertiginoso mundo digital actual, el tiempo de inactividad no es una opción. Al automatizar y orquestar sus procesos de recuperación, puede garantizar una recuperación más rápida, eficiente y fiable en caso de interrupción o ataque. Esto se traduce en una reducción del tiempo de inactividad, una mejora de la eficiencia y, en última instancia, una infraestructura de TI más resistente. No espere a que se produzca un desastre: empiece hoy mismo a automatizar sus procesos de recuperación y orqueste su regreso con éxito. Póngase en contacto con el equipo de Cristie Software para saber cómo incluir la automatización y orquestación de la recuperación del sistema en su estrategia de recuperación de desastres y cibernética.
Requisitos HIPPA para la recuperación de sistemas

HIPAA (Health Insurance Portability and Accountability Act) specific requirements for System Recovery HIPAA has specific regulations regarding system recovery within the healthcare sector, particularly under the Security Rule, which focuses on safeguarding electronic protected health information (ePHI). While HIPAA doesn’t prescribe specific technical solutions, it establishes guidelines that healthcare providers and related entities must follow to ensure the confidentiality, integrity, and availability of ePHI during system recovery scenarios. Here are the key components relevant to system recovery: Contingency Planning Requirements The HIPAA Security Rule mandates that covered entities (healthcare providers, health plans, clearinghouses) and their business associates (including IT service providers handling ePHI) develop a Contingency Plan to ensure the continuity of access to ePHI during emergencies, including system failures. This is outlined in 45 CFR § 164.308(a)(7) and includes five key implementation specifications: Data Backup Plan – Requirement: Covered entities must establish a data backup plan that includes creating and maintaining retrievable, exact copies of ePHI. This ensures that, in the event of a system failure, ePHI can be recovered and restored from secure backups. – Purpose: To prevent data loss and ensure ePHI is available for patient care and other essential functions after an emergency or system malfunction. Disaster Recovery Plan – Requirement: A disaster recovery plan must be in place to restore any loss of data due to an emergency or disaster (such as hardware failure, cyberattacks, or natural disasters). – Focus on System Recovery: This plan specifically addresses how to restore and recover ePHI and essential systems to operational status after a disruption. Healthcare organizations must ensure their systems can recover within a reasonable time frame to avoid prolonged downtime, which could affect patient care. Emergency Mode Operation Plan – Requirement: This involves establishing procedures to ensure the continuation of critical business processes and security measures to protect ePHI while operating in emergency mode. – Relevance to System Recovery: If a system failure occurs, healthcare providers need to continue functioning in a secure manner, which could involve alternative methods for accessing or handling ePHI while the primary systems are restored. Testing and Revision Procedures – Requirement: HIPAA mandates regular testing and updating of the contingency plans to ensure they work effectively when needed. – System Recovery Testing: Healthcare organizations should routinely test their backup and recovery systems to confirm that they can successfully recover ePHI, and that the recovery processes are efficient and reliable. Any weaknesses identified during testing should be addressed and revised in the plan. Applications and Data Criticality Analysis – Requirement: Organizations must assess and prioritize the most critical systems and data that need to be restored first in the event of a system failure. – Recovery Prioritization: This analysis helps determine which systems must be recovered first, ensuring that the most important functions (e.g., patient care applications) are prioritized during the recovery process. Risk Management Under HIPAA’s Security Rule (45 CFR § 164.306(b)(2)), healthcare entities must conduct risk assessments to identify vulnerabilities that could impact the availability of ePHI and implement appropriate security measures to mitigate those risks. System recovery is a crucial component of managing the risk of potential data loss or breaches due to system failure. Encryption and Safeguards HIPAA encourages the use of encryption for ePHI, particularly in transit and at rest. While not mandatory, if ePHI is encrypted and inaccessible during a breach or system failure, it provides an additional layer of protection. If encrypted systems are being recovered, encryption keys and security protocols must be part of the recovery process to ensure that data remains secure. Business Associate Agreements (BAAs) If a healthcare provider outsources data hosting, backup, or disaster recovery services, the provider must ensure that the business associate complies with HIPAA’s system recovery and contingency plan requirements. This is outlined in the Business Associate Agreement (BAA), which specifies the responsibilities of third-party vendors in protecting ePHI, including system backup and recovery. Reporting and Breach Notification If a system failure results in the unauthorized access, use, or disclosure of ePHI, HIPAA requires that it be treated as a breach. This could trigger the Breach Notification Rule (45 CFR § 164.400-414), which mandates that covered entities notify affected individuals, the U.S. Department of Health and Human Services (HHS), and possibly the media, depending on the scale of the breach. Effective system recovery can help minimize the likelihood and impact of such breaches. Conclusion Under HIPAA, system recovery is a critical component of ensuring the security and availability of ePHI. Healthcare organizations must have contingency plans in place, including data backup, disaster recovery, and emergency mode operations, to ensure that ePHI can be quickly restored and securely managed after a system failure or disaster. These processes are essential not only for compliance but also for protecting patient information and maintaining the continuity of care during unforeseen events. Contact the Cristie Software team if you are looking to improve system recovery and replication for critical healthcare systems, or to learn more about system replication and our system recovery integration with leading backup solutions from vendors including IBM, Dell Technologies, Rubrik and Cohesity.
Atrapado en el limbo: Por qué recuperarse de un ciberataque puede llevar una eternidad
Atrapado en el limbo: Por qué recuperarse de un ciberataque puede llevar una eternidad Los ciberataques son una dura realidad de la era digital. Aunque la conmoción inicial de una brecha ya es bastante mala, el verdadero dolor puede venir después: el tiempo prolongado de inactividad del sistema. Esto puede paralizar a las empresas, erosionar la confianza de los clientes y costar millones en ingresos perdidos. Pero, ¿por qué a veces se tarda tanto en volver a estar en línea después de un ciberataque? He aquí un desglose de los principales culpables: 1. Infraestructura dañada: Los ciberataques suelen dirigirse contra infraestructuras críticas, servidores, redes y bases de datos. Estos sistemas esenciales pueden resultar dañados, encriptados o incluso destruidos, lo que requiere reparaciones extensas o reconstrucciones completas. 2. Verificación de datos: La restauración a partir de copias de seguridad es una estrategia de recuperación habitual, pero no es infalible. Los piratas informáticos pueden manipular las copias de seguridad, por lo que es necesario verificar a fondo la integridad de los datos antes de volver a poner en línea los sistemas. Este laborioso proceso puede ser insoportablemente lento. Además, muchas empresas descuidan la recuperación de sistemas en los planes de RD y se centran desproporcionadamente en la copia de seguridad de los datos de las aplicaciones. Los datos no sirven de nada sin los sistemas y la infraestructura subyacentes. 3. La reacción en cadena: Los entornos informáticos modernos son intrincadas redes de sistemas interconectados. Un ataque a un sistema puede tener efectos en cascada, provocar una interrupción generalizada y requerir un complejo proceso de restauración paso a paso para garantizar que todo vuelva a funcionar correctamente. La recuperación aislada de la red es esencial si se sospecha la presencia de malware en cualquier imagen de recuperación del sistema o copia de seguridad de datos de aplicaciones. 4. Preocupación por la seguridad: El temor a que persista el malware es una de las principales causas de retraso. Las organizaciones necesitan estar absolutamente seguras de que sus sistemas están limpios antes de volver a conectarlos a la red. Esto suele implicar exhaustivas auditorías y análisis de seguridad, que añaden valiosas horas (o días) al plazo de recuperación. La recuperación de los sistemas a un entorno de sala limpia es una característica vital para permitir que el análisis ciberforense se lleve a cabo sin riesgo continuo de contaminación a sistemas y redes adicionales. 5. Falta de preparación: La desafortunada verdad es que muchas organizaciones simplemente no están preparadas para un ciberataque. Las copias de seguridad inadecuadas, la falta de herramientas completas de recuperación del sistema, los planes de recuperación obsoletos y la escasez de personal informático cualificado pueden ralentizar considerablemente el proceso de respuesta y recuperación. Conclusión Los ciberataques son inevitables, pero la duración del tiempo de inactividad no tiene por qué serlo. Si se da prioridad a la seguridad de los datos, se aplican estrategias sólidas de copia de seguridad y recuperación de sistemas y se prueban periódicamente los planes de recuperación, las organizaciones pueden mejorar significativamente su resistencia y recuperarse más rápidamente de los ataques. Después de todo, en el mundo digital, cada minuto fuera de línea puede significar una fortuna perdida. Póngase en contacto con el equipo de Cristie Software para saber cómo incluir la recuperación de sistemas, la recuperación en sala blanca y la detección avanzada de anomalías en archivos en su estrategia de recuperación cibernética.
La recuperación en un mundo híbrido: Sistemas físicos frente a máquinas virtuales

Navigating Recovery in a Hybrid World: Physical Systems vs. Virtual Machines In the aftermath of a cyberattack or system outage, restoring critical systems quickly and effectively is paramount for minimizing downtime and returning to business as usual. However, modern IT infrastructures often include a blend of physical servers and virtual machines (VMs). This hybrid environment presents unique challenges when it comes to disaster recovery strategies. Physical System Recovery: Hardware Headaches Hardware Dependencies: Physical servers are inextricably linked to their underlying hardware components. In a recovery scenario, hardware might need to be sourced, configured, and have an operating system installed before restoring data. This process can be time-consuming, especially if specific hardware models are required. Legacy Systems: Older physical systems may rely on outdated operating systems or specialized software configurations, adding complexity to the recovery. Restoring these systems often needs meticulous planning and compatibility testing. Single Point of Failure: Physical servers represent a single point of failure. If the hardware itself is damaged or compromised, recovery becomes even more challenging, potentially requiring a complete rebuild from scratch. Virtual Machine Recovery: Flexibility with Caveats Virtualization Benefits: VMs offer inherent advantages in disaster recovery. They are encapsulated files that can be moved, copied, and restored with greater ease than their physical counterparts. Snapshots and backups also simplify point-in-time restoration. Resource Competition: During a widespread outage, the very resources that VMs rely on (compute, storage, networking) may be strained. Recovery of numerous VMs can put additional stress on an already compromised infrastructure, slowing down restoration efforts. Hypervisor Vulnerabilities: While virtualization offers flexibility, it’s not impervious. Vulnerabilities in the hypervisor (the software layer managing VMs) can expose multiple virtual machines to compromise. Robust hypervisor security and patching are essential. A Tailored Approach to Recovery The best approach to disaster recovery in a hybrid environment is a multi-faceted one, considering the specific needs of both physical and virtual systems. Here’s a breakdown of key areas to focus on: Prioritization: Identify mission-critical systems, regardless of whether they are physical or virtual. These should be prioritized in your recovery plans. Backup Strategies: Maintain comprehensive backups for both physical and virtual systems. Consider off-site or cloud-based backups for resilience against localized disasters. Hardware Compatibility: If recovering critical physical systems, maintain a spare hardware inventory or have established relationships with suppliers to expedite replacements when necessary. VM Resource Planning: Have a clear understanding of resource requirements for restoring large numbers of VMs. Build in redundancy and scalability to avoid resource bottlenecks during recovery. Testing and Drills: Regularly test your recovery procedures for both physical and virtual systems. Identify and address any shortcomings proactively. 10 Ways Cristie Software Solves Hybrid System Recovery Challenges Dissimilar Hardware Technology: Cristie recovery software can automate the insertion of drivers when restoring systems to dissimilar platforms. This removes manual intervention to ensure that recovery can take place without interruptions. Legacy System Support: With system support back to Windows 2000 and many early editions of popular Linux distributions customers can confidently protect legacy systems. Bulk System Discovery: System recovery at scale presents many challenges including bulk system discovery which the Cristie Virtual Appliance (VA) can support in many ways including CSV input and API integration. Physical, Virtual & Cloud Recovery in any Direction: Cristie recovery and replication offers complete platform type flexibility between source and targets machines. Automated Provisioning: Systems can me migrated to new target platforms with automatic resource provisioning based on source machine parameters or adapted within the Cristie VA. Elimination of Manual Intervention: Cristie recovery automation features can eliminate manual interventions from the recovery workflow which are the most common cause of prolonged downtime following any disaster recovery scenario. Recovery Direct from Native Backups: Cristie recovery provides full system recovery directly from Rubrik, Cohesity, IBM and Dell Technologies native backups. Cost Effective Offline Replication: Cristie CloneManager replication software offers the choice of replicating systems to live running systems or to offline virtual machine image files which only require storage space. Offline system images can be mounted in the event of a disaster providing cost-effective protection for systems that do not need real-time failover. Cleanroom Recovery: The ability to restore systems to an isolated compute and network environment is a vital asset during a suspected cyberattack as it provides a cleanroom for cyber forensics and recovery image integrity testing, without risk of potential spread of malware to other production systems. Simulated Recovery Testing: Disaster recovery testing is vital to ensure you have confidence that your system recovery process will work when you need it most. Simulated recoveries can be scheduled through the Cristie VA to both monitor recovery success and measure recovery times to ensure that Recovery Time Objectives (RTO) can be met. The Evolving Landscape of Recovery As IT landscapes continue their shift towards cloud-based and highly virtualized environments, recovery strategies must also adapt. However, physical systems will continue to have their place in many organizations due to performance, legacy requirements, or security concerns. Understanding the distinct challenges of recovering both physical and virtual machines is crucial for ensuring effective disaster response in modern IT environments. It’s about preparedness, adaptability, and thorough understanding of your system’s unique dependencies that will pave the way for a swift and successful recovery, no matter the nature of the disruption. With Cristie Software many of these challenges can be resolved with advanced automation and recovery orchestration features within the Cristie VA. Download a free software trial to see the capabilities first hand for your backup environment.
Cómo subsanar las 5 principales deficiencias de los planes de recuperación en caso de catástrofe

How to close the Top 5 Disaster Recovery Plan Gaps. A disaster recovery (DR) plan is an essential part of any organization’s risk management strategy. It outlines the steps that need to be taken in order to recover from natural disasters, cyber-attacks, or any other unexpected event that could disrupt normal operations. However, even with the best intentions, many disaster recovery plans often contain gaps that can hinder the organization’s ability to effectively respond to a crisis. Here are the top five gaps commonly found in disaster recovery plans with guidance on effective ways to ensure these gaps are closed for your organization: 1. Insufficient backup procedures: Data is often an organization’s most valuable asset, yet many disaster recovery plans have insufficient data backup procedures in place. Organizations should regularly back up their data and ensure that it is stored in a secure location. Without adequate data backup procedures, an organization’s ability to recover from a disaster is severely compromised. However, data is of little value without the supporting infrastructure and systems that enable critical business applications to utilize that data. Many organizations take regular data backups but overlook the protection and recovery of the underlying systems that must be recovered before any data can be processed. It is system recovery that very often presents the biggest challenge and primary reason for downtime following any DR scenario. The recovery of physical systems is inherently more complex and likely to involve manual intervention than virtual systems. Cristie Software recovery and replication solutions can eliminate manual intervention from physical system recovery and facilitate automated recovery at scale regardless of platform type. 2. Lack of regular testing: One of the most common gaps in disaster recovery plans is the lack of regular testing. Many organizations create a plan and then never revisit it until a disaster strikes. Without regular testing, it is impossible to know if the plan will work in a real-life scenario. Regular testing helps identify weaknesses in the plan and allows for adjustments to be made before a disaster occurs. The Cristie Virtual Appliance (VA) provides the ability to schedule regular simulated recoveries of complete systems to check recovery image and recovery process integrity. Simulated recovery will also verify recovery time performance to ensure that the recovery infrastructure can support Recovery Time Objectives (RTO). In addition, simulated recoveries can be made within a Cleanroom Recovery environment using the Isolated Networks Recovery feature of the VA. This provides a secure and safe environment for system recovery testing which is vital if a cyberattack is suspected. Systems can be analysed in the cleanroom recovery environment without risk of any contaminating production systems and networks. 3. Failure to account for cyber-attacks: While many disaster recovery plans focus on natural disasters, cyber-attacks are becoming increasingly common and can have a major impact on an organization’s operations. A gap in many plans is the failure to adequately address the potential for cyber-attacks and how to respond to them. The main attack vector involves encryption of vital data files and can take place rapidly once a malware payload is executed. Early detection of malicious file encryption is vital to limit damage and the spread of malware to other machines on the network. Cristie Software system recovery provides Advanced Anomaly Detection through the VA which can analyse the file structure of running systems against their last backup and detect any file structure changes which are characteristic of malicious encryption. This feature can be scheduled to run at any time and is external to the main system recovery workflow. If Advanced Anomaly Detection indicates that a system or systems have been compromised, effected systems can be restored to a cleanroom environment for cyber forensic analysis. 4. Inadequate communication protocols: Communication is key during a disaster, yet many plans fail to outline clear communication protocols. This can lead to confusion and delays in getting the appropriate information to the necessary stakeholders. Organizations should establish clear channels of communication and ensure that all employees are aware of the protocols. Identifying and understanding the various audiences that need to be reached during a DR scenario is a key aspect of developing a crisis communication strategy. This includes communicating with employees, IT staff, customers, vendors, suppliers, investors, government officials, industry regulators, and media throughout the event and recovery phases. The communication plan should outline the specific needs of each audience and designate appropriate spokespersons within the organization to effectively communicate with them. 5. Lack of stakeholder engagement: A successful disaster recovery plan requires the engagement of all stakeholders, including employees, customers, suppliers, and regulatory agencies. Many plans fail to adequately engage all stakeholders, leading to confusion and delays in the response to a disaster. Organizations should involve all relevant parties in the planning process and ensure that everyone understands their role in the event of a crisis. In conclusion, it is important for organizations to regularly review and update their disaster recovery plans to ensure that they are comprehensive and effective. The recovery of infrastructure and in particular physical systems is an area often overlooked and omitted from regular testing plans. By addressing these common gaps, organizations can better prepare themselves to respond to any unexpected event that may arise. Contact the Cristie Software team for more information on system recovery and replication to ensure that your organization has the best possible DR protection.
Pruebas proactivas de ransomware con detección avanzada de anomalías y recuperación en sala blanca
Proactive ransomware testing with Advanced Anomaly Detection & Cleanroom Recovery Having early warning of malicious file encryption is vital to limit the damage potential from a ransomware attack. Cristie Software Advanced Anomaly Detection can identify suspicious file structure changes by comparing live systems against meta data held from the most recent backup. Any changes that resemble malware encryption are flagged through the Cristie Virtual Appliance (VA) allowing system images for both physical, virtual, or cloud-based machines to be restored within a cleanroom environment for further analysis. Advanced Anomaly Detection runs separately to ongoing system recovery and replication schedules. Isolated Network Recovery for physical, virtual and cloud system integrity verification Cristie Software provide the ability to perform cleanroom recovery for any physical, virtual, or cloud-based system to an isolated network so that testing can be performed without impacting production systems and networks. This functionality is provided through the Cristie VA which implements an intermediary virtual machine to route traffic between the production network and any VLAN networks configured on the Isolated Networks Gateway within the VA. In the unfortunate event of a suspected cyber-attack, recovering system images to an isolated network established as a cleanroom environment becomes a critical step in the cyber forensic investigation process. This isolation serves several vital purposes, ensuring the integrity of the investigation and aiding in the identification and analysis of the attack. Preventing Further Damage with Cleanroom Recovery Cyber-attacks often involve malware or other malicious code designed to spread and cause further damage. By recovering systems to an isolated network, the risk of inadvertently activating or spreading the malware is minimized. This isolation prevents any potential reinfection of the network, protecting other systems and data from further harm. Enhancing Incident Response The recovery of systems to an isolated network also plays a crucial role in the incident response process. By analyzing the recovered system images, organizations can identify the root cause of the attack, assess the extent of the damage, and develop effective remediation strategies. This information is invaluable for preventing future attacks and strengthening overall cybersecurity measures. Physical machine recovery with Dissimilar Hardware technology The recovery of physical systems following an incident is often more challenging than virtual machines due to the tight coupling with underlying hardware. Differences between source and target physical machines can present device driver discrepancies that may hinder the boot process and require manual intervention. Cristie Software recovery solves this challenge with Dissimilar Hardware technology which automates the insertion of necessary drivers eliminating manual intervention. Physical machines can also be recovered to virtual or cloud targets and vice versa providing complete flexibility. Validating Recovery Time Objectives (RTO) An additional function of isolated network recovery is the measurement of RTO for specific systems to ensure that the current recovery infrastructure and processes can meet internal or external system recovery time objectives. This form of testing is particularly important within highly regulated industries such as financial services where critical business services may have maximum permitted outage periods before penalties are incurred. Simulated recoveries for RTO confidence and recovery image integrity testing Within the Cristie VA simulated recoveries can be scheduled automatically with comprehensive reporting on recovery performance plus notification of any irregularities which may impact system recovery during a disaster recovery scenario. The Cristie VA applies machine learning algorithms to analyze recovery log files to provide automated problem resolution where possible, and resolution guidance through the VA dashboard. Non-intrusive operating system and application upgrade verification Aside from measuring recovery performance, the use of an isolated network provides a test environment to verify operating system (OS) and application patches without impacting the production environment. Conclusion Recovering systems to an isolated network is an essential practice for organizations that need to ensure RTOs for critical systems meet internal and external benchmarks. For cyber forensics it provides a cleanroom recovery environment which ensures the integrity of the investigation, prevents further damage, facilitates thorough analysis, and enhances incident response. By following this best practice, organizations can effectively meet regulatory compliance, verify system upgrades outside of the production environment, respond to cyber-attacks, and strengthen their overall cybersecurity posture. Contact the Cristie Software team for a live demo of isolated network recovery and testing.
El efecto dominó de la caída del sistema: Cómo se desmoronan las industrias cuando falla la tecnología

El efecto dominó de la caída del sistema: Cómo se desmoronan las industrias cuando falla la tecnología En el mundo interconectado de hoy, las empresas dependen en gran medida de la tecnología para sus operaciones, transacciones y comunicaciones. Cuando estos sistemas vitales se detienen, las consecuencias pueden ser graves y polifacéticas. El impacto de la inactividad de un sistema va mucho más allá de la mera incomodidad y se extiende por diversos sectores de formas únicas. Sanidad: Vidas en juego Atención al paciente interrumpida: Las historias clínicas electrónicas (HCE), los dispositivos médicos y los sistemas de comunicación son esenciales en la atención sanitaria. Los tiempos de inactividad pueden dificultar el acceso a datos cruciales de los pacientes, retrasar los diagnósticos y comprometer los planes de tratamiento. Caos operativo: Desde la programación de citas hasta la gestión de inventarios de medicamentos, los centros sanitarios dependen de sistemas informáticos funcionales. Los periodos de inactividad dificultan estos procesos y pueden poner en peligro la seguridad. Finanzas: Mercados agitados Operaciones perdidas y oportunidades desaprovechadas: Los mercados financieros se mueven a la velocidad del rayo. El tiempo de inactividad puede provocar la pérdida de oportunidades comerciales, información financiera imprecisa y, en última instancia, importantes pérdidas económicas. Cumplimiento de la normativa: Los reguladores del sector esperan que los servicios críticos funcionen dentro de unas tolerancias de impacto predefinidas. Las interrupciones prolongadas pueden infringir las directivas de resistencia operativa y acarrear multas. Confianza erosionada: Los inversores y clientes esperan un acceso seguro y permanente a sus fondos y carteras. Las interrupciones prolongadas del sistema pueden dañar gravemente la reputación de una entidad financiera y provocar la pérdida de clientes. Comercio minorista y electrónico: Ventas que desaparecen Ingresos perdidos: Cuando fallan los escaparates en línea o los sistemas de punto de venta (TPV), los minoristas pierden valiosas transacciones, lo que se traduce en pérdidas financieras directas y clientes frustrados. Interrupciones en la cadena de suministro: La gestión de inventarios, el seguimiento de pedidos y la programación de envíos suelen depender de sistemas integrados. El tiempo de inactividad crea cuellos de botella en la cadena de suministro, lo que provoca escasez de productos y retrasos en las entregas. Fabricación: Líneas de producción paradas Retrasos costosos: Los fabricantes suelen utilizar sistemas muy automatizados para la producción, el montaje y el control de calidad. Los tiempos de inactividad pueden detener las líneas de montaje, provocando costosos retrasos y el incumplimiento de plazos. Mantenimiento predictivo obstaculizado: Muchas fábricas modernas utilizan sistemas de mantenimiento predictivo que programan las reparaciones antes de que fallen los equipos. El tiempo de inactividad interrumpe estas medidas preventivas, aumentando el riesgo de averías inesperadas. Transporte: Caos en el tránsito Retrasos y cancelaciones de vuelos: Las aerolíneas dependen en gran medida de sistemas informáticos para las reservas, la facturación de pasajeros y el funcionamiento de los aviones. Las interrupciones del sistema pueden dejar en tierra a los aviones, dejando varados a los pasajeros y alterando los horarios de los vuelos en todo el mundo. Bloqueo de la logística: Las empresas de logística utilizan sofisticados sistemas de seguimiento de envíos, optimización de rutas y gestión de inventarios. Los tiempos de inactividad crean puntos ciegos que provocan retrasos, envíos mal dirigidos y clientes insatisfechos. El efecto dominó y los costes ocultos El tiempo de inactividad del sistema no existe en un silo. Sus efectos suelen extenderse a todos los sectores, interrumpiendo las cadenas de suministro y provocando un efecto dominó en toda la economía. Además, las empresas se enfrentan a costes ocultos, como: Daños a la marca: Las interrupciones pueden erosionar la confianza del público y dañar la reputación de una empresa. Moral de los empleados: Los periodos de inactividad pueden generar frustración y reducir la productividad de los trabajadores. Vulnerabilidad a la ciberseguridad: Los esfuerzos de recuperación de desastres pueden a veces abrir nuevas vulnerabilidades que los ciberdelincuentes pueden explotar. El imperativo de la resiliencia El tiempo de inactividad del sistema es un riesgo omnipresente para todas las empresas. Invertir en soluciones fiables de recuperación de sistemas, infraestructuras de TI resistentes, mantenimiento proactivo y sólidos planes de recuperación ante desastres ya no es opcional: es vital para salvaguardar las operaciones, minimizar las pérdidas y garantizar una ventaja competitiva en un entorno digital. Hable con el equipo de Cristie Software para obtener más información sobre nuestras soluciones de recuperación y replicación de sistemas para mitigar el tiempo de inactividad.
Resistencia operativa: La recuperación del sistema como principal garantía de cumplimiento de la normativa
Resistencia operativa: La recuperación de sistemas como salvaguarda clave del cumplimiento La resistencia operativa se ha convertido en la piedra angular de la normativa moderna del sector financiero. Ahora se exige a las empresas no sólo que eviten las interrupciones, sino también que se aseguren de poder recuperar rápidamente las funcionalidades críticas cuando surjan problemas inevitables. Aquí es donde una sólida estrategia de recuperación de sistemas ocupa un lugar central. Por qué la recuperación de sistemas es importante para el cumplimiento Tolerancia al impacto: Los reguladores esperan que las empresas establezcan estrictos Objetivos de Tiempo de Recuperación (RTO) y Objetivos de Punto de Recuperación (RPO) para sus servicios más esenciales. Las soluciones de recuperación de sistemas son cruciales para cumplir estos plazos, a menudo difíciles, y minimizar la pérdida de datos. Complejidad del sistema: Los sistemas financieros modernos son una red de aplicaciones, plataformas y redes interconectadas. Una recuperación eficaz del sistema garantiza que todos los componentes críticos se restauren en el orden correcto y que se tengan en cuenta las dependencias. Pruebas de recuperación: No basta con tener un plan. Los reguladores insisten en pruebas concretas de que sus procedimientos de recuperación funcionan. Para demostrarlo, es imprescindible disponer de herramientas de recuperación de sistemas con capacidad de prueba y simulación. Riesgo de terceros: la dependencia de los proveedores es una realidad en el sector financiero. Su estrategia de recuperación de sistemas debe extenderse a los proveedores externos, garantizando que puedan cumplir sus requisitos de resistencia. Cómo su solución de recuperación de sistemas garantiza la resistencia A continuación se indican algunas características clave que debe buscar en una solución de recuperación de sistemas para lograr el cumplimiento de la resistencia operativa: Automatización: Los procesos manuales de recuperación son lentos, propensos a errores y, sencillamente, inviables para entornos informáticos complejos. Las soluciones que automatizan los pasos críticos de recuperación garantizan una respuesta rápida y resultados fiables. Flexibilidad: Un enfoque único no es suficiente. Busque soluciones que le permitan adaptar los procesos de recuperación a las necesidades específicas de cada servicio crítico, garantizando que sus sistemas más importantes reciban atención prioritaria. Cobertura: Su solución de recuperación debe ser compatible con una amplia gama de plataformas (físicas, virtuales, en la nube), sistemas heredados y sistemas operativos para adaptarse a la diversidad de su entorno. Informes y documentación: Los registros e informes detallados son cruciales para demostrar a los reguladores que está cumpliendo los objetivos de recuperación y realizando pruebas de forma proactiva. Más allá del cumplimiento: Recupere su tranquilidad Puede que el cumplimiento sea la fuerza motriz, pero la recuperación de sistemas ofrece ventajas que van más allá del mero cumplimiento de la normativa: Tiempo de inactividad minimizado: Cuanto más rápido se recupere, antes podrá volver a atender a sus clientes, proteger su reputación y evitar pérdidas. Reducción del riesgo cibernético: las opciones de recuperación en entornos aislados le permiten verificar de forma segura los sistemas después de un ataque, minimizando el riesgo de reinfección. Continuidad del negocio: La recuperación de sistemas es el eje de su estrategia más amplia de recuperación ante desastres. Conclusión clave: Invertir en una solución sólida de recuperación de sistemas no es sólo cumplir la normativa, sino preparar a su organización para el futuro frente a cualquier tipo de interrupción. ¿Desea obtener más información sobre cómo alinear la recuperación de sistemas con sus objetivos de resistencia operativa? Póngase en contacto con nosotros hoy mismo.
BMR vs. Replicación: Elección de la ruta de recuperación ante desastres en función de los RTO

BMR vs. Replicación: Elección de la ruta de recuperación ante desastres en función de los RTO Cuando se trata de la recuperación ante desastres, la velocidad a la que puede recuperar los sistemas, a menudo definida como su objetivo de tiempo de recuperación (RTO), es crucial para minimizar el tiempo de inactividad y sus costes asociados. Cristie Software ofrece dos potentes herramientas para alcanzar sus objetivos de RTO: Bare Machine Recovery (BMR): Restaura sistemas completos a partir de copias de seguridad basadas en imágenes, incluidos el sistema operativo, las aplicaciones y los datos. BMR puede añadirse a su solución de copia de seguridad existente de Rubrik, Cohesity, Dell Technologies o IBM; alternativamente, nuestra opción independiente (CBMR) puede proporcionar una solución completa de copia de seguridad y recuperación. Replicación CloneManager: Replica sistemas en ejecución de forma continua, proporcionando copias casi en tiempo real para una rápida conmutación por error. Los sistemas de origen y destino pueden ser de cualquier tipo de plataforma, física, virtual o en la nube. ¿Cuál es la mejor opción para usted? La mejor opción depende de sus RTO específicos y de sus prioridades empresariales: Cuándo elegir BMR: RTO menos agresivos: Si puede tolerar cierto tiempo de inactividad durante la recuperación (minutos en lugar de segundos). Preocupación por los costes: La BMR puede ser una opción más económica en comparación con las soluciones de replicación continua, aunque ofrecemos replicación fuera de línea que no requiere un sistema en espera en funcionamiento. Flexibilidad: Restaure en hardware o plataformas diferentes si es necesario, lo que le proporciona versatilidad durante el proceso de recuperación. Cuándo elegir la replicación de CloneManager: RTOs exigentes: Cuando cada segundo de inactividad importa, la replicación ofrece conmutación por error casi en tiempo real, garantizando la continuidad del negocio. Sistemas críticos: Proteja los sistemas de alta prioridad que no pueden permitirse un tiempo de inactividad prolongado. Conmutación por error automatizada: Minimice la intervención manual y acelere la recuperación con funciones de conmutación por error automatizada. Consideraciones: Tolerancia a la pérdida de datos: La replicación suele tener un objetivo de punto de recuperación (RPO) más bajo, lo que minimiza la pérdida de datos durante un desastre. Coste frente a tiempo de inactividad: Sopese el coste de la replicación continua frente al impacto financiero potencial de un tiempo de inactividad prolongado. Enfoque híbrido: Muchas organizaciones utilizan BMR para la recuperación de sistemas a gran escala junto con la replicación para los sistemas más críticos, logrando un equilibrio entre protección y rentabilidad. Los sistemas físicos suelen requerir intervención manual durante la recuperación, lo que puede prolongar considerablemente el tiempo de inactividad cuando se intenta recuperar sistemas físicos a gran escala. Cristie Software ha resuelto este reto mediante funciones de automatización que pueden eliminar la intervención manual de la recuperación de sistemas físicos. La diferencia de Cristie : Ambas soluciones de Cristieofrecen ventajas que incluyen: Amplio soporte de plataformas: Recuperación en entornos físicos, virtuales y en la nube. Flujos de trabajo automatizados: Simplifique sus procesos de recuperación con capacidades de automatización y orquestación. Pruebas y verificación: Asegúrese de que sus planes de recuperación ante desastres funcionan con herramientas de prueba integradas. ¿Qué camino tomará? Al comprender sus necesidades de recuperación, puede tomar una decisión informada entre las sólidas capacidades de BMR y la velocidad de replicación del sistema. Cristie Software tiene soluciones para satisfacer sus objetivos específicos. Programe una llamada informal para discutir cómo podemos diseñar una solución de recuperación que se alinee con sus RTO y objetivos de negocio.
¿Cuál es el principal agujero del 80% de los planes de RD?
¿Cuál es el principal agujero en el 80% de los planes de RD? La computación en nube domina el panorama informático empresarial y está llamada a seguir protegiéndolo. Un informe reciente de HashiCorp indicaba que el 90% de las grandes empresas había adoptado una infraestructura multicloud. Sin embargo, este enfoque en la virtualización está dejando de lado muchos planes de recuperación de desastres (DR) cuando se trata de la recuperación del sistema. Cristie Software ofrece una solución integral a una brecha importante que nuestros socios tecnológicos ven en el 80% de los planes de DR de sus clientes. ¿Está causando la virtualización una distracción en su planificación de recuperación de sistemas? El auge de la computación en nube es un factor clave que impulsa el crecimiento del mercado de máquinas virtuales. Aunque los contenedores están asumiendo ciertas funciones que tradicionalmente desempeñaban las máquinas virtuales, como el funcionamiento de aplicaciones ligeras o microservicios, las máquinas virtuales siguen siendo esenciales para ejecutar tareas que consumen muchos recursos o aplicaciones heredadas que requieren un entorno de sistema operativo completo. Según la firma de investigación Global Market Insights, el tamaño del mercado de máquinas virtuales superó los 9.500 millones de dólares en 2023 y se prevé que crezca a una CAGR de alrededor del 12% entre 2024 y 2023. Quizás no sorprenda que muchas soluciones de copia de seguridad modernas se centren únicamente en la protección de máquinas virtuales. Desafortunadamente, independientemente de si está implementando máquinas virtuales o contenedores, estas tecnologías dependen de máquinas físicas subyacentes que necesitan una solución de recuperación eficiente en caso de desastre. La recuperación de máquinas físicas a escala sigue siendo un reto importante para la recuperación de infraestructuras empresariales. Es un placer trabajar con máquinas virtuales cuando se trata de recuperación y replicación. Pueden replicarse a escala a un entorno alternativo en la nube con relativa facilidad desde la comodidad de su escritorio. Por el contrario, las máquinas físicas ofrecen mucha menos automatización cuando se trata de recuperación y, en muchos casos, requerirán intervención manual para garantizar que los sistemas vuelvan a estar en línea rápidamente. Si se requiere una recuperación de máquina física a máquina física (P2P), esto puede presentar conflictos de controladores de dispositivos a menos que las máquinas de origen y destino se construyan a partir de hardware idéntico. Las máquinas físicas necesitarán una imagen de arranque disponible, ya sea desde un almacenamiento conectado directamente o a través de un recurso compartido de red. Cualquier forma de intervención manual lleva tiempo, lo que puede ser aceptable para un solo sistema, pero en muchas empresas o centros de datos el número de servidores físicos puede ascender a cientos o más. Por lo tanto, la recuperación del sistema físico puede ser el principal culpable de la prolongación del tiempo de inactividad tras cualquier forma de interrupción del sistema. Acelere la recuperación de máquinas físicas a escala con el software de recuperación de sistemas Cristie Software. Cristie Software se ha centrado mucho en la automatización de la recuperación de máquinas físicas ayudando a muchas organizaciones a mejorar enormemente su flujo de trabajo de recuperación eliminando la necesidad de intervención manual. Nuestro software se integra con soluciones comunes de gestión de hardware Intelligent Platform Management Interface (IPMI) como iDRAC (Dell) e iLO (HP). Para la gestión de sistemas fuera de banda (OOB) ofrecemos bibliotecas estándar de cliente DMTF Redfish® para gestionar sistemas físicos con el mismo nivel de automatización disponible para máquinas virtuales. El software de recuperación Cristie funciona directamente con las soluciones de copia de seguridad de Rubrik, Cohesity, Dell e IBM para proporcionar una extensión de recuperación de sistemas sin problemas que no requiere una sobrecarga adicional de gestión de copias de seguridad. Cristie Virtual Appliance (VA) proporciona una única interfaz para gestionar la recuperación y replicación de servidores físicos, virtuales y basados en la nube. La replicación y recuperación del sistema puede configurarse para que tenga lugar en cualquier dirección entre objetivos físicos, virtuales y en la nube, con escenarios de hardware diferentes, como discrepancias en los controladores de dispositivos, que se solucionan automáticamente. En resumen Si usted ha adoptado las ventajas de la computación en nube y los beneficios de las máquinas virtuales y la contenedorización, tómese el tiempo para considerar su proceso de recuperación si las máquinas físicas dentro de su infraestructura se vieran comprometidas por un ataque cibernético u otra forma de interrupción. Los desafíos de la recuperación del sistema físico a escala pueden resultar en un tiempo de inactividad prolongado que a su vez tiene impactos financieros y el potencial de daño a las relaciones con los clientes y la reputación de la marca. Póngase en contacto con el equipo de Cristie Software para obtener más información sobre nuestras funciones de recuperación de sistemas físicos y sobre cómo ayudamos a las organizaciones a resolver el reto de la recuperación de sistemas físicos a escala.
Simplificación de la migración desde VMware
Simplificación de la migración desde VMware Cristie Software ofrece una ruta de migración sencilla desde VMware para los clientes que buscan pasar a entornos alternativos. A pesar del dominio de VMware en virtualización, gestión de la nube, informática de usuario final y tecnologías de infraestructura hiperconvergente, la casa de análisis líder Forrester predice que el 20 por ciento de los clientes actuales de VMware buscarán una alternativa en 2024. Migre fácilmente de VMware a una amplia gama de entornos con Cristie Software El software de replicación y migración Cristie CloneManager, junto con el dispositivo virtual Cristie (VA), proporciona una migración automatizada sencilla para máquinas de origen VMware a una gama de entornos alternativos. El aprovisionamiento de máquinas de destino dentro del nuevo entorno se puede automatizar basándose en las especificaciones de la máquina de origen, aunque el escalado de recursos del sistema también se puede aplicar fácilmente durante el proceso de migración. Automatice la migración de varios sistemas desde una única interfaz. La migración de múltiples sistemas puede gestionarse desde una única interfaz a destinos físicos, virtuales y en la nube, con soporte multiinquilino también proporcionado dentro de Cristie VA. Las plataformas de destino compatibles incluyen Amazon AWS, Microsoft Azure, Microsoft Azure Stack HCI, Oracle Cloud, Nutanix AHV, Kubernetes, además de Amazon S3 y objetivos compatibles. Se admite una amplia gama de sistemas operativos Windows y Linux; para consultar la lista de compatibilidad más reciente, visite nuestra Matriz de compatibilidad de productos. Migre y replique sistemas a destinos en línea y fuera de línea. CloneManager admite objetivos de migración y replicación "en línea" y "fuera de línea". Los destinos se denominan "en línea" cuando están ejecutando máquinas listas para tomar el relevo al instante del sistema de origen. Los destinos en línea tienen la ventaja de que están listos para funcionar y pueden asumir las operaciones muy rápidamente. Existe una alternativa en forma de archivos de imagen de disco virtual. Las máquinas virtuales pueden capturarse como una imagen completa de la misma forma que una unidad de sistema en una máquina física puede capturarse como una imagen de disco única. El archivo de imagen contiene todo, incluida la configuración del sistema operativo, las aplicaciones y los datos. La replicación o migración del sistema puede realizarse a un archivo de imagen de disco virtual almacenado en un entorno de nube privada o pública en lugar de a una máquina en funcionamiento. Esto tiene una ventaja de coste significativa, ya que sólo se requiere el coste de almacenamiento en la nube para mantener estos archivos de imagen en lugar de almacenamiento más recursos informáticos. La replicación fuera de línea puede ser una solución rentable cuando los objetivos de tiempo de recuperación (RTO) son menos exigentes. Los cambios de red posteriores a la replicación también pueden programarse para migraciones tanto en línea como fuera de línea. En resumen Si está evaluando pasar de VMware a una plataforma alternativa, solicite una prueba gratuita de CloneManager para conocer de primera mano nuestras funciones de migración. Para obtener más información sobre las capacidades de CloneManager y Cristie VA, póngase en contacto con el equipo de Cristie Software, que siempre está disponible para proporcionar una demostración en vivo y responder a cualquier pregunta.
Reducción del riesgo para la transformación digital del sector de los seguros.
Reducing risk for Insurance industry digital transformation. Cristie Software work with many insurance industry firms to provide system recovery and migration solutions to support disaster recovery and aid the move towards full digitalization. 2024 marks a period of significant change for the insurance industry with digital transformation and cyber resilience a key focus. Regulations such as DORA and NIS2 within the EU and similar Operational Resilience directives from the Bank of England require firms to overhaul their cyber resilience with full compliance by 2025. In the UK the Lloyds Blueprint Two initiative is driving digital transformation with all firms required to use phase one digital services from 1 July 2024. Supporting the transition from legacy systems. To remain competitive many firms are aiming to migrate legacy systems which may be up to 30 years old to new digital cloud-based platforms. This is necessary to remain relevant alongside the many Insurtech startups who have fully embraced a personalised digital experience and are rapidly acquiring market share. Legacy systems present maintenance challenges due to end-of-life components which often incur high support costs. Cristie Software system migration tools offer extensive support for legacy operating platforms and can assist the migration from physical systems to virtual or cloud-based targets. Once a replica has been made within a new modern operating environment, applications can be fully tested for compatibility before any cut-over is made. Digitalization and operational resilience in the insurance sector, two potentially opposing forces. The cloud comes with many advantages, but it is not without risk. Exposing digital services to the public internet serves to increase the attack surface for any firm. As AI technologies progress rapidly, attackers will gain the ability to develop larger-scale phishing and disinformation campaigns that are even more convincing. These threat actors will increasingly focus on targeting cloud environments to establish persistence and navigate between different segments of victim environments hosted across multiple clouds. Firms should consider hybrid solutions combining public and private cloud architectures to provide resilience and security. Private cloud solutions may also be vital where data sovereignty is important for regulatory compliance. Cristie Software system recovery and replication solutions offer the ability to recover systems in any direction between physical, virtual and cloud platforms, or set in place local replication targets that can offer fail-over in the event of a cloud service outage. What does the Lloyds Blueprint Two initiative mean to insurance firms in 2024? The Lloyds Blueprint Two initiative in partnership with Velonetic is delivering a new digital platform transforming the journey of placing risk and making claims for open market and delegated authority business for both brokers and insurers. Blueprint Two digital services will be delivered in two phases. From 1 July 2024, all market firms must use phase one digital services. By April 2025, the launch of phase two digital processing services will take place, marking a significant milestone for the market as it transitions into a completely digital environment. This transition will be further facilitated with the implementation of the Digital Gateway risk service, also scheduled to go live in April 2025. Once operational, both these initiatives will enable the market to fully support digital placement of risk, providing the necessary capabilities to operate in an entirely digital setting. How are compliance regulations impacting insurance firms in 2024? The Digital Operational Resilience Act (DORA) was finalized by EU authorities in November and is set to take effect from January 2025. DORA primarily focuses on financial firms including insurance companies. Furthermore, certain “critical” third-party Information Communication Technology (ICT) service providers will also be directly subject to some provisions of DORA. Any ICT service providers working with the financial sector can also expect to comply with regulatory requirements. DORA aims to enhance the resilience of businesses against technology-related risks, including disruptions to operations and data breaches caused by cybercriminals.Additionally, organizations operating in various sectors should carefully assess the applicability of the upcoming EU Network and Information Security Directive (NIS2) which became effective in January. All EU member states have until October 17, 2024, to incorporate it into their national frameworks. NIS2 strengthens the existing cybersecurity requirements faced by organizations covered under the original NIS Directive. Many organizations that were previously not subject to these rules will now find themselves bound by the new regulations. These regulations emphasize board-level governance of cyber risk and the need for adequate cybersecurity standards across the supply chain. This applies even to organizations based in the UK. How can Cristie Software help meet compliance directives? Cristie Software provides system recovery solutions designed for automated system recovery orchestration for both physical and virtual machines with the ability to undertake detailed system recovery simulations to assist with regulatory compliance. Cristie’s system recovery software can create fully functional copies of production systems within an isolated sandbox environment in minutes without the need for additional infrastructure. These sandboxes are easily accessible for multi-disciplinary teams to optimize workflows, validate change management procedures, and collect evidence of cybersecurity capabilities or weaknesses. In Summary System recovery can present challenges for insurance firms with physical systems often lacking the automation features that are taken for granted within virtual environments. Cristie recovery solutions can help overcome these limitations while providing complete flexibility to restore to and from any platform environment. Very often firms place disproportionate investment in cyber detection and prevention tools neglecting the last line of defense which is reliable system recovery. Cyberattacks are unfortunately an inevitability since many attack methods will gain access to user credentials. Contact our team to learn more about simplifying key aspects of infrastructure recovery, legacy system migration, and cyber resilience to meet the requirements of current operational resilience legislations.
Simplificación de la migración de sistemas a Microsoft Azure Stack HCI

Simplificación de la migración de sistemas a Microsoft Azure Stack HCI Azure Stack HCI (Hyper-Converged Infrastructure) es una solución ofrecida por Microsoft que reúne tecnologías de Windows Server con servicios de Azure para permitir escenarios de nube híbrida. Hemos notado un aumento en los proyectos de migración a Azure Stack HCI dentro de nuestra base empresarial, particularmente con clientes que buscan construir soluciones de HCI privada y nube híbrida por razones como la soberanía de datos. La migración de múltiples sistemas a Azure Stack HCI ha demostrado ser hasta ahora una tarea difícil y lenta para los administradores de sistemas dentro de la comunidad de TI debido a la falta de herramientas de automatización. Migrar múltiples sistemas a Microsoft Azure Stack HCI con el Cristie Virtual Appliance Cristie Software ha resuelto los desafíos de la migración a través de nuevas capacidades dentro del Cristie Virtual Appliance (VA) que ofrecen una integración perfecta y un aprovisionamiento automatizado al migrar sistemas a Azure Stack HCI. El Cristie VA ahora puede aprovisionar fácilmente múltiples sistemas dentro de Azure Stack HCI desde una amplia gama de plataformas de origen, incluyendo VMware, Nutanix, Amazon EC2, Oracle Cloud, Hyper-V o directamente desde máquinas físicas. Los sistemas se pueden aprovisionar automáticamente basándose en las especificaciones de la plataforma de origen o ajustarse dentro de la VA ahorrando muchas horas de configuración manual. Factores que contribuyen al interés y la adopción de Azure Stack HCI Para evaluar la popularidad actual y las tendencias de adopción de Microsoft Azure Stack HCI, recomendamos a nuestros clientes que revisen informes recientes del sector, estudios de casos de clientes y encuestas tecnológicas. Además, consultar los anuncios oficiales de Microsoft y los foros de usuarios puede proporcionar información sobre el compromiso de la comunidad con la plataforma. Varios factores contribuyen al interés y la adopción de Azure Stack HCI: Adopción de la nube híbrida: Azure Stack HCI se alinea con la tendencia de adopción de la nube híbrida, permitiendo a las organizaciones construir una infraestructura consistente a través de centros de datos locales y la nube de Azure. Esta flexibilidad es valiosa para las empresas con requisitos de cumplimiento específicos o preocupaciones de residencia de datos.Integración perfecta con los servicios de Azure: La integración de Azure Stack HCI con los servicios Azure ofrece una plataforma unificada para gestionar las cargas de trabajo tanto en las instalaciones como en la nube. Esta integración simplifica las operaciones y permite una experiencia de nube híbrida sin fisuras.Escalabilidad y flexibilidad: Azure Stack HCI proporciona escalabilidad y flexibilidad, lo que permite a las organizaciones escalar los recursos en función de la evolución de sus necesidades. Esta adaptabilidad resulta atractiva para empresas con cargas de trabajo y requisitos de recursos variables.Operaciones híbridas con Azure Management Tools: Azure Stack HCI permite a las organizaciones utilizar las herramientas de gestión de Azure para operaciones consistentes a través de entornos híbridos. Esto facilita la gestión racionalizada y la supervisión de los recursos.Capacidades de Edge Computing: Azure Stack HCI es adecuado para escenarios de Edge Computing, por lo que es una solución relevante para las organizaciones que despliegan aplicaciones en el borde para capacidades de baja latencia y fuera de línea.Virtualización Integrada: Aprovechando Hyper-V para la virtualización, Azure Stack HCI proporciona una plataforma de virtualización familiar y robusta para ejecutar máquinas virtuales.Seguridad y Cumplimiento: La integración con Azure Security Center y otros servicios de Azure mejora las capacidades de seguridad y cumplimiento, abordando las preocupaciones de las organizaciones con estrictos requisitos de seguridad.Mejoras y Actualizaciones: Microsoft lanza regularmente actualizaciones y mejoras para Azure Stack HCI, introduciendo nuevas características, mejoras y compatibilidad con las últimas tecnologías. En resumen Si actualmente está trabajando en proyectos de migración hacia o desde Microsoft Azure Stack HCI, o planea hacerlo en el futuro, entonces póngase en contacto con el equipo de Cristie Software para obtener más información sobre nuestras capacidades de automatización de la migración. Nuestra solución de migración de sistemas CloneManager® junto con Cristie VA puede simplificar enormemente la migración a Azure Stack HCI ahorrando muchas horas de intervención manual.
¿Ha llegado el momento de abordar su balance de ciberseguridad para centrarse más en la recuperación?

Is it time to address your cybersecurity balance to deliver greater focus on recovery? Protecting your critical business data from cyber threats is more important now than ever. With the rise of ransomware and other cyberattacks, it could be time to address your cybersecurity balance. The National Institute of Standards (NIST) Cybersecurity Framework offers a comprehensive assessment model for companies to evaluate their cybersecurity posture based upon 5 core functions; 1. Identify, 2. Protect, 3. Detect, 4. Respond and 5. Recover. NIST recommend a balanced investment across all five functions, however, cybersecurity assessments often reveal that companies are investing 85% of their cybersecurity budget on functions 1 through 3 leaving only 15% for Respond and Recovery procedures. If we analyse the current top cybersecurity threats, it becomes clear that having solid recovery tools and processes in place is vital for all organizations. Introduction: Why It’s Urgent to Address Your Cybersecurity Balance There is no doubt that cybersecurity tools designed to Identify, Protect and Detect cyber threats are very important, but if we consider the range of threats common today it becomes clear that a cyber attack which can circumnavigate early detection will become a reality for most organizations. In these cases, a system recovery solution that can restore vital business systems and application data to a known clean point in time is vital to prevent lost revenue, maintain customer service, and avoid paying extortionate ransomware demands. Let’s now consider 6 common threat categories and their likelihood of evading early detection. Social Engineering. Social engineering persists as one of the most dangerous hacking methods utilized by cybercriminals, primarily because it exploits human mistakes rather than technical weaknesses. This heightened danger stems from the fact that deceiving a human is considerably simpler than breaching a security system. In 2023, social engineering tactics have featured prominently as a primary means of acquiring employee data and credentials. High profile cases such as the attack on MGM Resorts International where MGM’s hotel and casino operations were disrupted for several days resulting in losses of over $100 million is just one such example. Over 75% of targeted cyberattacks start with an email, phishing is one of the top causes of data breaches, followed use of any credentials successfully stolen. If cybercriminals have obtained employee credentials their actions can remain undetected until they are in a very strong position to present ransom demands. A solid recovery solution then becomes your only line of defense. Third-partly exposure. Cyber attackers can bypass security systems by infiltrating less-secured networks of third-party entities that hold privileged access to the primary target of the hacker. A significant instance of such a third-party breach occurred in early 2021 when hackers exposed personal information from more than 214 million accounts on Facebook, Instagram, and Linkedin. The hackers gained access to this data by compromising a third-party contractor named Socialarks, which was engaged by all three companies and held privileged access to their networks. Configuration Errors. Configuration errors can pose a significant cybersecurity threat. Configuration errors occur when settings or configurations of software, hardware, or network components are improperly configured, leaving vulnerabilities that attackers can exploit. These errors may result from oversight, misconfigurations, or lack of adherence to security best practices. A 2019 study by the Ponemon Institute Research Report Sponsored by AttackIQ revealed that 50% of IT professionals acknowledge a lack of understanding regarding the effectiveness of the cybersecurity tools they have implemented. This indicates that a significant portion of IT experts may not be consistently conducting internal testing and maintenance of their cybersecurity measures. Again, configuration errors leave the gates wide open with system recovery the only option for a successful resolution. Poor Cyber Hygiene. Poor cyber hygiene refers to the lack of good practices and behaviors related to online security. It involves neglecting fundamental steps and precautions that individuals or organizations should take to protect their digital assets and data. The possibilities for bad practice are wide ranging but common indicators of poor cyber hygiene include: Weak Passwords: Using easily guessable passwords or reusing passwords across multiple accounts without regular updates. Outdated Software: Failing to regularly update operating systems, applications, and security software, leaving vulnerabilities unpatched. Lack of Security Software: Not having antivirus or anti-malware software installed, or not keeping it up to date. Unsecured Networks: Using unsecured Wi-Fi networks without encryption or using default router credentials. Clicking on Suspicious Links: Falling for phishing attacks by clicking on links or opening attachments from unknown or suspicious sources. Ignoring Software Updates: Disregarding prompts to update software or delaying updates, leaving systems exposed to known vulnerabilities. No Data Backups: Neglecting to regularly back up important data, making it vulnerable to loss in case of ransomware or hardware failure. Sharing Sensitive Information: Sharing personal or sensitive information online without considering privacy settings or the security of the platform. Using Unauthorized Software: Installing and using unapproved or unauthorized software, which may contain security risks. No Employee Training: Failing to educate employees or users about cybersecurity best practices, making them more susceptible to social engineering attacks. Poor Access Controls: Allowing excessive user privileges, not implementing the principle of least privilege, and not revoking access promptly for former employees. Neglecting Physical Security: Ignoring physical security measures for devices, such as leaving computers or mobile devices unattended in public spaces. The list above serves to highlight the vast range of human factor vulnerabilities that can be classified as poor cyber hygiene, all of which have the potential of bypassing investments in tools related to functions 1 to 3 of the NIST Cybersecurity Framework. Cloud Vulnerabilities. A recent Forbes article sharing research from Oracle states that 98% of enterprises using public cloud have adopted a multi-cloud infrastructure provider strategy. A multi-cloud strategy offers several benefits such as removing single points of failure and preventing vendor lock-in, however, leveraging multiple cloud vendors widens the attack surface to the risk of security flaws and vulnerabilities. Forbes recommend that companies utilizing the cloud for infrastructure services pay particular attention to the following
Cristie Recovery RBMR para Rubrik ahora con integración completa de Rubrik Security Cloud
Cristie Recovery RBMR para Rubrik ahora con integración completa de Rubrik Security Cloud. Cristie Software System Recovery for Rubrik (RBMR) proporciona integración Rubrik Security Cloud con descubrimiento automático de todos los archivos, volúmenes y máquinas protegidos por Rubrik Cloud Data Management (CDM). Los clientes pueden combinar las ventajas de la seguridad de datos de confianza cero de Rubrik con la completa flexibilidad de la recuperación de sistemas de Cristie Software. A través de Cristie Virtual Appliance (VA), cualquier objeto de copia de seguridad Rubrik se puede restaurar a cualquier punto disponible en el tiempo en la plataforma de recuperación de su elección. Esta perfecta integración permite que las potentes funciones de automatización y orquestación de la recuperación del sistema dentro de Cristie VA se apliquen a cualquier trabajo de copia de seguridad compatible con Rubrik Security Cloud. Rubrik Security Cloud - El futuro de la resiliencia cibernética para todos los clientes de Rubrik. Rubrik anunció la disponibilidad general de Rubrik Security Cloud en agosto de 2022 como el tablero unificado para que todos los clientes de Rubrik supervisen, administren y protejan los recursos del sistema en entornos empresariales, de nube y SaaS. Rubrik Security Cloud (RSC) proporciona control para todos los recursos de protección de datos, incluidos los clústeres de Rubrik. Dado que RSC está basado en SaaS, los clientes obtienen acceso instantáneo a las últimas funciones y servicios tan pronto como están disponibles. RSC funciona con Rubrik CDM para proporcionar una vista y un control universales de todos los objetos protegidos por CDM dentro de la infraestructura de un cliente. RSC es la interfaz predeterminada para todas las nuevas implementaciones de Rubrik y se convertirá en la solución de gestión única para todas las instalaciones de Rubrik después de junio de 2024. Cristie Software RBMR para Rubrik: combina la protección de datos de confianza cero con la recuperación avanzada de infraestructuras. Rubrik Security Cloud se diseñó basándose en los principios de confianza cero para disuadir proactivamente las amenazas a nivel de los datos. La implementación de Rubrik de inmutabilidad incorporada, protocolos seguros, aislamiento lógico, encriptación, controles de acceso basados en roles, autenticación multifactor y servicios integrados trabajan en conjunto para mantener la integridad y accesibilidad de los datos. La incorporación de la recuperación de sistemas Cristie Software RBMR para Rubrik añade una gama completa de herramientas de recuperación de sistemas que permiten recuperar sistemas en tan solo 10 minutos en cualquier destino físico, virtual o en la nube. Las potentes capacidades de automatización y orquestación de recuperación de RBMR pueden eliminar cientos de horas de gastos administrativos en comparación con los métodos tradicionales de recuperación de sistemas. Tener la capacidad de recuperar sistemas rápidamente y a un estado limpio después de cualquier ciberataque es vital para garantizar la resistencia operativa, evitar la pérdida de ingresos y mantener la experiencia del cliente. Cristie RBMR funciona junto con Rubrik Security Cloud sin necesidad de administración adicional de copias de seguridad dentro de Rubrik Security Cloud para proporcionar una protección completa de recuperación del sistema. La integración completa de RSC está disponible con Cristie VA versión 4.8.1 y superior. Póngase en contacto con Cristie Software para obtener más información sobre las ventajas de incluir Cristie Software RBMR dentro de su infraestructura Rubrik Security Cloud. Cristie Software proporciona soluciones de recuperación de sistemas que ofrecen una recuperación de sistemas rápida y eficiente para cualquier entorno de TI. La recuperación de sistemas a gran escala se puede lograr con el clic de un botón. Las funciones de orquestación de recuperación de Cristie garantizan que las complejas arquitecturas por niveles puedan recuperarse lo más rápidamente posible con una intervención mínima. Además, la capacidad de realizar simulaciones detalladas de recuperación de sistemas permite a los clientes de Cristie confiar en sus capacidades de RTO y RPO para cumplir los SLA o los requisitos de autoevaluación del cumplimiento normativo. Póngase en contacto con nuestro equipo para saber cómo funciona RBMR junto con Rubrik Security Cloud y dar los primeros pasos hacia la implantación del proceso de recuperación de sistemas más eficaz para su organización.
El papel de la inteligencia artificial (IA) y el aprendizaje automático (AM) en la ciberseguridad del sector financiero.
The role of artificial intelligence (AI) and machine learning (ML) in financial sector cybersecurity. The banking industry has been an early adopter of AI (Artificial Intelligence) and machine learning (ML) employing the technology in many applications to enhance operations and customer experiences. Areas to improve customer service such as document verification and processing, voice and speech recognition, chatbots and virtual assistants, plus predictive analytics and personalization have been in use and gaining sophistication for some time. AI has also been an established business tool in a security context to assist in the identification of irregular transactions indicating potential fraud. These types of high-volume, less sophisticated crimes lend themselves to the use of AI due to its strength in spotting patterns in large datasets. AI presents an effective means to tackle low-level crime quickly and efficiently for the scale that banks and payment businesses operate on. It also can play a key role in identifying suspicious (phishing) emails. However, it is the extended application of AI and ML in the fight against cybercrime which is gaining significant attention. The application of AI and ML in anomaly detection. AI and ML can continuously monitor network and system activities to detect unusual or suspicious behavior. When deviations from established baselines are identified, alerts can be generated for further investigation. The development team at Cristie Software has utilized ML technologies to offer an advanced system for detecting unusual file activity during the system recovery and replication phases. System backups are a critical defense against ransomware, and the backup procedure presents an excellent chance to compare the structure of files between successive backup images. While some files regularly change as part of normal business operations performed within their associated applications, the malicious encryption of files typically follows identifiable patterns. It is these patterns that Cristie Software’s anomaly detection technology aims to recognize, providing an early warning of a potential cyber attack in progress. Learn more in our earlier article covering our application of ML in advanced file anomaly detection. AI and ML have a significant and evolving role in financial sector cybersecurity. AI and Ml play a significant and evolving role in cybersecurity; anomaly detection is just one key area where the strength of these technologies come to the fore. Here are 10 additional key roles and applications of AI and ML in the field of financial sector cybersecurity: Threat Detection and Prevention: AI-powered systems can analyze vast amounts of data to identify patterns and anomalies indicative of potential cyber threats that might go unnoticed by traditional rule-based systems. AI and ML driven threat detection tools can recognize known malware and viruses and can also identify zero-day vulnerabilities by analyzing behavior patterns. User and Entity Behavior Analytics (UEBA): AI can analyze user and entity behavior to identify unauthorized or suspicious activities. It can spot unusual login patterns, access to sensitive data, or deviations from established usage patterns. Phishing Detection: AI can help in identifying phishing attempts by analyzing email content, sender behavior, and other indicators. It can reduce false positives and improve the accuracy of identifying phishing emails. Automated Incident Response: AI can automate incident response processes by providing real-time threat analysis and immediate actions to mitigate threats. This can help organizations respond to threats faster and reduce the impact of security incidents. Predictive Analysis: AI can use historical data to predict future security threats and vulnerabilities, enabling proactive measures to be taken to prevent attacks. Vulnerability Management: AI can assist in identifying and prioritizing vulnerabilities within a network or system, helping security teams focus their efforts on critical areas. Security Automation: AI can automate routine security tasks, freeing up security personnel to focus on more complex and strategic aspects of cybersecurity. Natural Language Processing (NLP): NLP-powered AI can help in analyzing and understanding unstructured data, such as security logs and reports, to extract actionable insights. Security Analytics: AI-driven security analytics platforms can provide a holistic view of an organization’s security posture by aggregating and analyzing data from various sources, facilitating better decision-making. Adaptive Security: AI can adapt security measures based on evolving threats and changing network conditions, providing a more dynamic and responsive defense mechanism. Financial sector regulatory interest in AI and ML. Regulators are also becoming increasingly interested in the risks and benefits presented by AI and ML technology. In 2020 the Bank of England (BoE) and the Financial Conduct Authority (FCA) launched the Artificial Intelligence Public-Private Forum (AIPPF) and issued their final report which represents the results of more than a year’s worth of meetings, workshops, and discussions focused on Data, Model Risk and Governance aspects of AI adoption. The BoE followed in October 2022 with the discussion paper DP5/22 – Artificial Intelligence and Machine Learning which aims to respond to the AI Public-Private Forum final report and gather further feedback on the regulators’ views of the risks and benefits of the use of AI, as well as how the current regulatory framework applies to AI and ML The UK FCA/PRA regulations governing Operational Resilience and the European Union (EU) Digital Operational Resilience Act (DORA) are both comprehensive operational resilience regulations that are seen as significant drivers of substantial investments in financial sector cybersecurity. They are regarded as the most extensive and impactful operational and cybersecurity regulations globally. Learn how Cristie Software can complement Operational Resilience and Cybersecurity practices for the Financial Sector. It is important to note that while AI has many benefits in financial sector cybersecurity, it’s not a panacea. It should be used in conjunction with other data security practices and technologies to create a comprehensive cybersecurity strategy. Moreover, AI systems themselves need to be protected from adversarial attacks to maintain their effectiveness in defending against cyber threats. Since its inception, Cristie Software has been dedicated to automating system recovery, replication, and migration using cutting-edge techniques and the latest computing advancements. Incorporating ransomware detection driven by Machine Learning (ML) is a seamless expansion of our disaster recovery capabilities and represents a unique strength of our system recovery tools.
La importancia de la resistencia operativa en el sector financiero estadounidense
The importance of Operational Resilience in the U.S. financial sector. Operational resilience is a critically important topic for the financial sector. It refers to a financial institution’s ability to withstand and adapt to disruptions such as cyberattacks, natural disasters and pandemics while continuing to provide essential services to its customers and meet regulatory obligations. We have recently highlighted regulatory activity in the UK and APAC, however governing bodies worldwide are drafting their own equivalents or adding new legislation to extend and enforce existing regulations. The U.S. is no exception with all three federal banking regulators simultaneously issuing the Supervisory Letter SR 20-24: Interagency Paper on Sound Practices to Strengthen Operational Resilience to the officer in charge of supervision at every federal reserve bank in November 2020. Although the practices outlined in this initial letter were directed to the largest and most complex domestic US financial firms, it is important for all financial firms to strengthen their operational resilience as new directives are being drafted for many additional FINSERV jurisdictions. Operational resilience remains a top priority for regulators as illustrated by the inclusion of Information Security and Operational Resiliency within the 2023 Examination Priorities announced by the U.S. Securities and Exchange Commission. Cristie Software has broad experience working with financial institutions to deliver automated large scale system recovery with the ability to orchestrate detailed recovery simulations and support the self-assessment requirements of regulatory compliance. Of course, operational resilience has implications extending way beyond meeting regulatory compliance. Below we highlight 10 key areas that illustrate how important improving operational resilience is for all firms in the U.S. financial sector. 10 key reasons why Operational Resilience is crucial in the U.S. financial sector: Protecting Customers and Investors: Financial institutions handle the money and investments of individuals and businesses. Operational failures can result in financial losses for customers and investors, erode trust, and damage a financial institution’s reputation. Maintaining Market Stability: The financial sector plays a central role in the stability of the broader economy. Disruptions in financial operations can have cascading effects on other sectors, potentially leading to systemic crises. Regulatory Requirements: Regulatory agencies impose strict requirements on financial institutions to ensure they have robust operational resilience measures in place. Non-compliance can lead to fines, legal consequences, and reputational damage. Cybersecurity Threats: Financial institutions are prime targets for cyberattacks. Operational resilience includes cybersecurity measures to protect sensitive customer data and financial systems from breaches and cyber threats. Complexity of Financial Services: The financial industry is highly complex, involving various products, services, and interconnected systems. Ensuring operational resilience is a way to manage this complexity and reduce the risk of operational failures. System recovery following any disruption will need to be orchestrated to ensure complex tiered systems are recovered in the correct sequence. Cristie System Recovery automation and orchestration tools can help to facilitate system recovery within complex financial systems. Customer Expectations: In the digital age, customers expect uninterrupted access to financial services. Operational resilience is crucial to meet these expectations, especially with the increasing reliance on online and mobile banking. Customer Experience (CX) is a major area of focus in the competitive FINSERV market. Global Interconnectedness: Financial institutions often operate on a global scale, making them vulnerable to disruptions in different parts of the world. Operational resilience helps mitigate the impact of global disruptions. Legal and Regulatory Reporting: Financial institutions are required to report their financial status and operations accurately and transparently. Operational resilience ensures that they can fulfil these reporting requirements even in challenging circumstances. Cristie Recovery and Replication software provides detailed reporting to assist with regulatory self-assessment plus the ability to perform regular recovery simulations to validate disaster recovery processes and recovery time expectations. Competitive Advantage: Institutions with strong operational resilience can differentiate themselves in the market. Customers and investors are more likely to trust and do business with institutions that demonstrate a high level of resilience. Risk Management: Operational resilience is a fundamental aspect of overall risk management in the financial sector. It helps identify, assess, and mitigate operational risks effectively. Learn how Cristie Software can simplify Operational Resilience for the U.S. financial sector. In summary, operational resilience is a foundational element of the U.S. financial sector. It encompasses strategies, processes, and technologies designed to ensure that financial institutions can continue to operate effectively and protect the interests of their stakeholders in the face of various threats and disruptions. It’s not just a regulatory requirement; it’s a key component of business continuity and long-term success in the industry. Contact our team to learn more about simplifying key aspects of your system recovery to help meet the requirements of operational resilience legislation. Visit the CloneManager® and System Recovery product pages for more information regarding the Cristie Software suite of solutions for system recovery, replication, migration, and ransomware protection.
Cómo conseguir una recuperación rápida y eficaz del sistema

How to achieve fast and efficient System Recovery. Keeping system recovery time to a minimum following any outage is vital for many reasons; loss of revenue, poor customer experience, and diminished brand reputation are high on the list. There are several factors that affect system recovery time which are common to all outage scenarios, but there are additional factors that impact recovery time significantly if the outage is a result of cybercrime. We will consider here several scenarios impacting system recovery time and highlight ways in which Cristie Recovery solutions can reduce or mitigate these factors. Storage and network selection for optimum System Recovery performance. System recovery time in every scenario will be dependent upon the type of storage used to store the recovery image and the speed of the network connecting the storage device to the target system. Locally attached solid state storage such as a flash drive connected directly to the target system, or a flash-based storage array connected over a high-speed storage area network (SAN) will generally offer the fastest possible recovery. At the opposite end of the performance scale will be recovery images based on tape media and/or cloud-based images where recovery time will be governed by network connection bandwidth, and the performance of the cloud infrastructure serving the files. Careful consideration must therefore be made to ensure the chosen storage platform and network performance will meet Recovery Time Objectives (RTO). System readiness and preparation for System Recovery. The next major factor to consider is the recovery target type and the speed with which different target machines can be provisioned. At the most basic level, there are three target machine options; physical machines dedicated to a specific application or application sets, virtual machines (VMs) that can be configured with specific compute, network and storage resources from their underlying architecture, and cloud-based targets which can be thought of as VMs hosted by a 3rd party provider outside of the corporate network. Physical machines will typically be the slowest to provision as standby machines may need additional configuration to meet application requirements unless machines have been configured in advance. Physical standby machines may be located at a hosting facility which can introduce additional provisioning delays and/or travel time to the co-location site. Virtual machines hosted locally or in the cloud are typically much faster to provision, however, recovering to dissimilar platforms can introduce several compatibility issues that can extend recovery times significantly. Many of the complications encountered when recovering systems to dissimilar platforms can be overcome without the need for manual intervention using Cristie Recovery software automation features. Realistic System Recovery times without dedicated recovery software. In the absence of a complete and up-to-date system configuration image, system recovery for even a single system can easily extend from hours into days. Building a standby system from scratch will require physical configuration followed by operating system (OS) installation and most likely critical OS updates and security patches before applications can be installed. Likewise, applications may require patch updates ahead of installing any operational data and user configurations. For this process to run as smoothly and quickly as possible, all required OS and application installation files need to be readily available, either as physical media or via an external source such as an installation package manager. After the entire OS and application stack have been successfully installed there will often be a need for further configuration to add the target machine to the appropriate networks, and potential security configurations for any firewall and cybersecurity tools deployed. If this recovery process must be repeated for multiple systems, then clearly a large support team would be required to ensure RTOs are kept to a minimum. Installing and using a reliable and efficient system recovery solution which can automate recovery steps is therefore vital to avoid recovery times escalating into days or even weeks of downtime. Customers using Cristie Recovery software indicate real world recovery times as low as 10 minutes, assuming all best practices are followed. Eliminating manual intervention, the biggest cause of System Recovery delay and RTO failure. Let us assume we have complete and up-to-date system configuration images for the systems we wish to recover. We are at great advantage in comparison to the scenario where we must build the recovery targets from scratch. However, there are still many opportunities for configuration issues to cause system recovery delays, especially when source machines and recovery targets are using dissimilar hardware. Generally, these issues will require manual intervention, extending recovery delays, and adding additional overhead to the total cost of downtime. Cristie Recovery software excels in eliminating manual intervention as much as possible through a range of powerful and intelligent recovery automation features that enable systems to be recovered, to and from, dissimilar platforms quickly and easily. System recoveries can be performed efficiently between physical, virtual and cloud platforms in any direction. Automating system recovery with driver insertion and pre- & post- boot operations. When migrating a system to a dissimilar platform there will inevitably be subtle differences in the underlying hardware that will require platform specific device drivers to enable the target machine to boot successfully. Traditionally these vital driver files would require manual intervention to complete installation plus additional reboot cycles before the target is ready to boot the recovery image without exceptions. Cristie Recovery software overcomes this time-consuming barrier by automatically inserting boot critical drivers for many common operating platforms, in addition to providing the ability to pre-configure custom driver configurations for target systems. Cristie Recovery software also provides extensive automation for additional pre- boot tasks such as automatic resource sizing and provisioning when migrating from physical to virtual machines, and post-boot actions such as automating network configuration changes and performing custom startup scripts for recovery systems. Implications for System Recovery following a cyber-attack. If a system outage has resulted from a physical failure or natural disaster, you can generally assume that your operational data is free from malicious corruption. There may be incomplete transactions prior to the
Resistencia operativa en el sector financiero de Asia y el Pacífico

Resistencia operativa en el sector financiero de Asia-Pacífico. La resistencia operativa seguirá siendo un aspecto clave de la regulación del sector financiero de Asia-Pacífico (AP) a lo largo de 2023 y más allá. Todas las empresas y reguladores de la zona siguen haciendo cada vez más hincapié en la resistencia operativa y la gestión de las interrupciones de los servicios financieros críticos. Aunque algunas jurisdicciones de AP pueden ir a la zaga de los avances logrados en otras geografías, vemos que el ritmo está aumentando con la presión reguladora que obliga a la región a poner más énfasis en todos los aspectos de la resiliencia operativa y cibernética. Tendencias que impulsan la normativa sobre resistencia operativa en la región de Asia-Pacífico. Hay varios factores que impulsan la necesidad de mejorar la resistencia operativa en la región de Asia-Pacífico. La aceleración de la digitalización que tuvo lugar durante la pandemia de COVID-19 es muy significativa, ya que dio lugar a un aumento de las asociaciones entre empresas financieras y operadores terceros. Esto ha impulsado la dependencia de una gama mucho más amplia de proveedores y partes interesadas; sin embargo, las directivas de resiliencia operativa hacen hincapié en la mitigación de todos los riesgos de terceros para los operadores financieros. Además, el complicado entorno geopolítico reciente y la posible recesión económica que podría derivarse de cualquier perturbación significativa de los servicios financieros en las jurisdicciones de la AP son también factores clave que impulsan la necesidad de centrarse más en la resistencia operativa y la mejora de la regulación. Un hervidero de actividad reguladora del sector financiero en la región Asia-Pacífico. Desde que el Comité de Supervisión Bancaria de Basilea (BCBS) publicó sus Principios para la Resistencia Operativa en marzo de 2021, hemos visto cómo varios reguladores de la región AP publicaban versiones oficiales o consultivas de materiales de control que aplican los principios del BCBS. En 2022, la Autoridad Monetaria de Hong Kong (HKMA) publicó un nuevo Manual de Políticas de Supervisión (SPM) y dos SPM revisados para aplicar los principios de sostenibilidad operativa de las directrices del BCBS de 2021. En el último mes, la Autoridad de los Mercados Financieros de Nueva Zelanda - Te Mana Tātai Hokohoko (FMA) ha publicado un documento de consulta en el que propone la introducción de nuevas condiciones estándar para los titulares de licencias de mercados financieros adicionales, centradas en la continuidad operativa y los sistemas tecnológicos. Estamos asistiendo a un hervidero de actividad en toda la región de Asia-Pacífico, lo que indica un enorme esfuerzo por cumplir los objetivos y plazos reglamentarios. ¿Cuándo entrarán en vigor las directivas reguladoras de la Resiliencia Operativa en Asia-Pacífico? Aunque hay variaciones regionales, marzo de 2024 es un plazo común para que muchas directivas reguladoras de la región AP entren plenamente en vigor. La Ley de Infraestructuras del Mercado Financiero (FMA) de 2021 de Nueva Zelanda es solo un ejemplo que sigue este calendario. Hemos visto que muchas otras directivas siguen el mismo camino. Por ejemplo, las normas para las Infraestructuras de Mercados Financieros (FMI) designadas que fueron publicadas el 27 de julio de 2023 en virtud del artículo 31 de la Ley de Infraestructuras de Mercados Financieros de 2021 por el Banco de la Reserva de Nueva Zelanda y la Autoridad de Mercados Financieros también entran en vigor a partir del 1 de marzo de 2024. Es evidente que existe un sentido de urgencia en toda la región destinado a garantizar que las empresas afectadas hayan implantado todos los procedimientos necesarios para facilitar la resistencia operativa dentro de este plazo. Cristie Software puede simplificar el cumplimiento de la Resiliencia Operativa para las empresas financieras de Asia Pacífico. Cristie Software puede simplificar aspectos clave de la recuperación de infraestructuras de sistemas financieros para ayudar a cumplir los requisitos de las nuevas directivas de resistencia operativa. Los sistemas financieros implican complejas configuraciones de TI interdependientes construidas con redundancia para proporcionar la máxima disponibilidad. La implantación, el soporte y la seguridad de estos sistemas presentan retos debido a su enorme escala. Por ejemplo, un servicio aislado como los pagos puede estar soportado por varias empresas financieras con miles de instancias de servidor en muchas geografías diferentes. Las soluciones de recuperación y replicación de Cristie Software ofrecen una serie de métodos para facilitar la asignación y recuperación masiva de servidores, lo que garantiza que los despliegues a gran escala puedan recuperarse en la secuencia correcta y dentro de los plazos previstos. Póngase en contacto con Cristie Software para hablar de sus retos de resistencia operativa. Aunque marzo de 2024 se acerca rápidamente, no es demasiado tarde para mejorar sus procedimientos de recuperación de sistemas. Cristie Software proporciona soluciones de recuperación de sistemas diseñadas para la orquestación automatizada de recuperación de sistemas a gran escala con la capacidad de realizar simulaciones detalladas de recuperación de sistemas y apoyar los requisitos de autoevaluación del cumplimiento normativo. Póngase en contacto con nuestro equipo para obtener más información sobre cómo simplificar los aspectos clave de la recuperación de infraestructuras para ayudar a cumplir los requisitos de todas las nuevas directivas regionales sobre resistencia operativa.
Recuperación bare-metal (RBMR) para usuarios de Rubrik
Recuperación bare-metal (RBMR) para usuarios de Rubrik. La ciberseguridad y la recuperación ante desastres (DR) requieren un enfoque por capas para garantizar la protección de todos los elementos de la infraestructura de TI de una empresa. Los clientes pueden confiar en Rubrik para proteger cibernéticamente los datos de su empresa en sistemas físicos y máquinas virtuales con copias de seguridad protegidas, inmutables y de acceso controlado que pueden proteger datos críticos para el negocio como bases de datos, sistemas de archivos, contenedores y más. La adición de Cristie Software RBMR bare-metal recovery a cualquier instalación Rubrik amplía las capacidades de recuperación del sistema para restaurar sistemas completos, incluyendo todas las especificaciones del sistema operativo, usuario, aplicación y partición de disco a cualquier destino de recuperación físico, virtual o en la nube. Realice una recuperación completa del sistema directamente desde las copias de seguridad de Rubrik. RBMR proporciona una recuperación completa del sistema a partir de sus trabajos de copia de seguridad Rubrik existentes sin necesidad de configurar ninguna tarea de copia de seguridad adicional. Sin embargo, las ventajas no terminan con la recuperación perfecta del sistema. La incorporación de RBMR también proporciona potentes funciones de automatización de la recuperación del sistema y orquestación de DR que pueden proporcionar un salvavidas esencial en caso de ciberataque u otra interrupción del sistema. Además, estas funciones ofrecen una variedad de técnicas para ayudar a restaurar conjuntos de servidores a gran escala de la manera más eficiente y sin esfuerzo. Automatización de la recuperación de sistemas en plataformas distintas para los usuarios de Rubrik. La integración de Rubrik con RBMR permite a Rubrik realizar la recuperación bare-metal en cualquier sistema operativo compatible con RBMR. RBMR funciona arrancando un "entorno de recuperación" que contiene una imagen del sistema operativo con todas las herramientas y scripts de RBMR necesarios para facilitar el proceso de recuperación. No es necesario que los objetivos de recuperación sean del mismo tipo de plataforma. La tecnología Dissimilar HardWare (DHW) de Cristiepuede ocuparse de cualquier discrepancia de controladores críticos para el arranque proporcionando automáticamente una ruta a los controladores adicionales necesarios para arrancar correctamente el sistema de destino. Esto puede eliminar los pasos de intervención manual típicos de la migración de sistemas entre plataformas distintas. La recuperación bare-metal (BMR) debe formar parte de cualquier estrategia sólida de recuperación ante desastres. Contar con una estrategia de recuperación ante desastres fiable que incluya la recuperación bimetal garantiza que los sistemas vuelvan al mismo estado en el que se encontraban antes de la copia de seguridad, sin tener que realizar parches adicionales, configuraciones previas a la recuperación ni correcciones posteriores a la recuperación. Los retos típicos de la BMR incluyen: Encontrar la versión correcta del sistema operativo (SO). Volver a aplicar los parches del sistema operativo y de las aplicaciones al nivel correcto. Encontrar y reinstalar controladores para hardware específico. Reinstalar el agente de copia de seguridad. Recordar y volver a crear configuraciones de partición de disco. Orquestación de recuperación RBMR Rubrik para una personalización completa del proceso de DR. RBMR puede resolver todos los retos típicos de BMR, pero también llevar su proceso de DR al siguiente nivel a través de las amplias funciones de automatización y orquestación de recuperación que pueden facilitar la recuperación de sistemas por niveles con tantos pasos previos y posteriores a la recuperación como necesite. Las tareas de orquestación de RMBR permiten un ajuste fino en profundidad de las recuperaciones y réplicas del sistema, incluidos los reinicios, los scripts posteriores a la recuperación, las tareas manuales y las opciones personalizadas para las acciones en caso de fallos de etapa. La guía Cristie VA-Orchestration Guide proporciona información detallada sobre la configuración de tareas y las capacidades de automatización inherentes a RBMR para Rubrik. Cristie Rubrik Bare-metal Recovery (RBMR) for Linux/Unix Hosts - Documento técnico. Rubrik y Cristie Software han desarrollado un Libro Blanco Técnico ideal para ingenieros de campo y de soporte técnico, arquitectos de clientes e ingenieros de soluciones que deseen comprender mejor cómo funciona Cristie recuperación RBMR bare-metal de Cristie Rubrik para Linux/Unix. Este documento de inmersión profunda describe cómo aprovechar RBMR en escenarios específicos de recuperación de servidores físicos y recuperación de desastres e incluye muchas mejores prácticas para la configuración. En resumen. La combinación de la seguridad de datos de confianza cero Rubrik y la recuperación bare-metal RBMR de Cristie Software garantizará que sus operaciones empresariales sean realmente imparables en caso de ciberataque o cualquier otro escenario de desastre. Póngase en contacto con nuestro equipo para obtener más información sobre RMBR para Rubrik y nuestras capacidades para ayudarle a restaurar nuestra infraestructura de TI independientemente de la escala.
Simplificar la resistencia operativa en el sector financiero
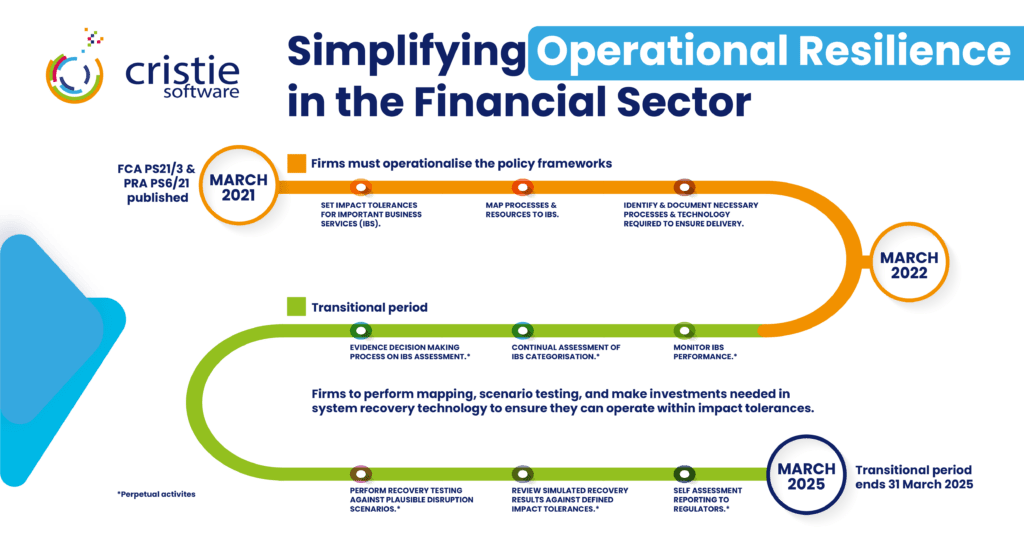
Simplifying Operational Resilience in the Financial Sector. The Financial Conduct Authority (FCA) and Prudential Regulation Authority (PRA) respective policy statements PS21/3 & PS6/21 published in March 2021 established the frameworks for relevant firms within the financial sector to implement measures that would ensure Operational Resilience for important business services. The practical implications of achieving compliance with these directives present far-reaching obligations for applicable firms and prescribe a significant investment in planning, processes, and technologies. At the highest level the directives required firms to operationalize the following fundamental parameters during the period from March 2021 to March 2022. Set customer, firm, and market impact tolerances for important business services in severe but plausible scenarios. Impact tolerance: means the maximum tolerable level of disruption to an important business service, including the maximum tolerable duration of a disruption. Map processes and underlying resources to important business services. Identify important business services and document the necessary processes, people, facilities, technology, and other resources required to deliver the important business services. March 2022 onwards marks the transition period during which firms must set in place all measures required to be compliant with the directives when the policies come fully into force in March 2025 Setting impact tolerances, scenario testing and self-assessment reporting. Disaster recovery (DR) planning, testing, and reporting are core components of achieving operational resilience and these functions map directly into the policy tasks of setting impact tolerances, scenario testing and self-assessment reporting. Cristie Software system recovery and replication solutions can simplify these tasks significantly through the recovery automation, orchestration, and reporting features of our products. Cristie Software BMR Recovery can act standalone or as an extension to leading backup solutions. Cristie bare machine recovery (BMR) software provides high performance system recovery as a standalone solution or as an extension to leading backup solutions from Dell EMC, IBM, Cohesity and Rubrik. System Recovery, Orchestration, and Automation at scale. Financial systems involve complex interdependent server and storage configurations that are built with redundancy to provide the utmost resilience. The deployment, maintenance, and protection of these systems presents specific challenges due to scale. For instance, a single service such as payments may be supported by thousands of server instances across multiple geographies for many financial firms. Recovery and replication solutions from Cristie Software offer several mechanisms to facilitate bulk server mapping and recovery: Direct bulk system mapping through the Cristie Virtual Appliance (VA) and/or from CSV file import. Optional bulk mapping and recovery actions using the Cristie SDK API based on the Swagger OpenAPI specification which can be used to generate an SDK client in the programming language of your choice. The Cristie recovery boot environment can easily be incorporated with common Intelligent Platform Management Interface (IPMI) implementations such as iDRAC (Dell) and iLO (HP). For Out-of-Band (OOB) systems management we offer DMTF Redfish® client standard libraries to manage physical systems with the same level of automation available for virtual machines. Recovery orchestration to facilitate tiered financial system recovery. Within any financial services infrastructure there will be a system recovery hierarchy necessary to accommodate system interdependencies. Cristie Software can help facilitate tiered system recovery through the system recovery orchestration features provided within the VA. Orchestration tasks allow for detailed fine tuning of system recoveries and replications including reboots, post recovery scripts, manual tasks, plus customisable options for actions following any stage failures. Full details can be found in the VA-Orchestration Guide. Scenario Testing with Cristie Software Recovery Simulation. The PRA Supervisory Statement SS1/21 section 6 describes the expected scenario testing firms should undertake to ensure they can remain within impact tolerances for important business services. The nature and frequency of a firm’s testing should be proportionate to the potential impact that disruption could cause and whether the operational resources supporting an important business service have materially changed. Recovery simulation can be scheduled within the VA to test recoveries of any supported Cristie BMR product backups. Recovery of selected machines can be simulated within a simulate recovery job. The recovery destination can be any physical, virtual or cloud target. With a simulation job created, and at least one recovery machine added to the job, the VA will continue to restore simulations indefinitely until either manually booted, the job is suspended, or the target machine is deleted. It is possible to add multiple simulation machines to the same job. Simplifying operational resilience with automated system recovery to dissimilar platforms. The machines within a recovery job do not need to be the same platform type. If the recovery target is of dissimilar hardware to the source system, then Cristie’s Dissimilar HardWare (DHW) technology can be enabled which automatically provides a path to additional drivers that may be required to successfully boot the target system. RPO/RTO testing and reporting with Cristie Software. The machines within a recovery job do not need to be the same platform type. If the recovery target is of dissimilar hardware to the source system, then Cristie’s Dissimilar HardWare (DHW) technology can be enabled which automatically provides a path to additional drivers that may be required to successfully boot the target system. In summary. Although March 2025 may sound far off, regulators will expect incremental progress during the transition period, so firms should be prepared to demonstrate this when the next impact events occur. Cristie Software provides system recovery solutions designed for automated large scale system recovery orchestration with the ability to undertake detailed system recovery simulations to assist self-assessment and regulatory compliance. Contact our team to learn more about simplifying key aspects of infrastructure recovery to help meet the requirements of operational resilience legislation. Visit the CloneManager® and System Recovery product pages for more information regarding the Cristie Software suite of solutions for system recovery, replication, migration, and ransomware protection.
Reduzca el RPO con CloneManager Changed Block Tracking
Reduce RPO with CloneManager changed block tracking. The Recovery Point Objective (RPO) is a crucial concept in disaster recovery and business continuity planning. It represents the maximum amount of data loss that an organization is willing to tolerate in the event of a system failure and is expressed as an amount of time. RPO can be reduced by increasing the frequency that system images are taken and stored in a backup environment to facility recovery when an outage occurs. Systems which host data intensive applications will require a low RPO to minimize data loss. Cristie’s CloneManager replication software fulfils this objective through the addition of Changed Block Tracking for offline replication which is now available with our VA 4.7.1 release. This provides an efficient mechanism to track filesystem changes and allows near continuous real-time replication. Large databases can now be synchronized with minimal data throughput and RPOs are reduced to seconds rather than hours. Changed block tracking with offline replication. Changed block tracking is deployed through a lightweight filesystem driver which continuously scans the source system under protection for file changes. Every file change is communicated to a target environment where an offline system image is maintained. In the event of a disaster scenario the system image stored in the target system is processed against the log of all filesystem changes since the time of creation, producing a bootable image which is a replica of the source system before the failure occurred. Previously, filesystem tracking had to be scheduled to a predefined frequency. Now with changed block tracking the process is fully automated so that the changelog is updated whenever filesystem changes occur. This ensures that the offline bootable image is as current as possible in the event of a system outage. The benefits of offline replication. Cristie’s CloneManager supports both ‘online’ and ‘offline’ replication targets. Targets are termed ‘online’ when they are running machines ready to instantly take over from the primary system. Online replication targets have the advantage that they are ready to run and can takeover operations very quickly. The downside is that they are consuming physical or virtual compute resources continuously while merely waiting for an incident to happen. To overcome this resource overhead an alternative exists in the form of virtual disk image files. Virtual machines can be captured as a complete image in the same way that a system drive in a physical machine can be captured as a single disk image. The image file contains everything including the OS configuration, applications, and data. System replication can be performed to a virtual disk image file stored within a private or public cloud environment rather than to a running machine. This has a significant cost advantage as only the cost of cloud storage is required to maintain these image files rather than storage plus compute resources. The disadvantage is the time taken to boot the image and bring the machine on-line, but for many DR scenarios the Recovery Time Objective (RTO) they provide can be measured in a few minutes which is often sufficient. Cristie replication solutions provide both online and offline replication capabilities with support for all common system image standards including .vhdx, .qcow2 and .vmdk file formats via the Cristie VA. How can I take advantage of changed block tracking today? The initial release of changed block tracking supports the Windows OS only, and replication to Amazon EC2, Oracle BLOB, or any S3 compliant storage including MinIO. Future releases will support Azure and VMware plus additional operating systems. The importance and benefits of reducing RPO. Here are some reasons why the Recovery Point Objective is important: Minimizing data loss: This ensures that critical data is protected and minimizes the potential impact of data loss on business operations. Compliance requirements: Many industries and regulatory bodies have specific data protection and recovery requirements. Adhering to these regulations is essential to avoid legal penalties, reputational damage, and loss of customer trust. The RPO helps organizations align their data recovery practices with compliance standards and demonstrate their commitment to data protection. Operational continuity: Data is a vital asset for organizations, and its loss or unavailability can severely impact day-to-day operations. By defining an RPO, organizations can establish recovery timeframes and implement measures to ensure that data is consistently backed up and recoverable. Financial implications: Data loss can have significant financial consequences for organizations. The cost of recovering lost data, rebuilding systems, and compensating for the disruption can be substantial. By setting an appropriate RPO, organizations can assess the cost-effectiveness of their data protection strategies and allocate resources accordingly. This allows them to strike a balance between investment in data recovery and the potential financial impact of data loss. Customer trust and satisfaction: In today’s data-driven world, customers expect organizations to safeguard their information. If an organization experiences a data breach or loss, it can erode customer trust and damage its reputation. By implementing robust data protection measures, including meeting RPO objectives, organizations can assure customers that their data is secure and instill confidence in their ability to handle potential disruptions. In summary. Recovery Point Objective is hugely important and safeguards many aspects of business operations as highlighted above. The new changed block tracking feature from Cristie adds an additional layer of automation for our customers to ensure their vital business systems are protected. Visit the CloneManager® and System Recovery product pages or contact the Cristie Software team for more information regarding the Cristie Software suite of solutions for system recovery, replication, migration, and ransomware protection.
Detección temprana de ransomware incluida en la cartera de software Cristie

Early ransomware detection incorporated into your system recovery process. When cybercriminals orchestrate a human led cyberattack, they may have spent months identifying and overcoming defences to maximise the impact of their attack. Early ransomware detection is therefore vital to ensure damage limitation. Regardless of whether their entry was through commodity malware, or the exploitation of an outdated or misconfigured web server, the ultimate end goal will be file encryption to hold vital operational data to ransom. Hackers will typically use asymmetric encryption. This is cryptography that uses a pair of keys to encrypt and decrypt a file. The public-private pair of keys is uniquely generated by the attacker for the victim, with the private key to decrypt the files stored on the attacker’s server. Human led attacks attempt to spread laterally within an organization’s infrastructure, and when the encryption payload is executed, files can be encrypted at an alarmingly fast rate. Rapid detection of anomalies in file structure and naming can provide the earliest warning of an active cyberattack and this capability has now been introduced into Cristie Software’s portfolio of system recovery and replication solutions. Applying patented file analysis techniques to combat ransomware. We recently announced our UK patent award for the automatic self-healing of errors or failures encountered during a system restore or replication. This technology is built upon algorithms which analyse run-time log files to provide automatic system restore failure resolution through machine learning. The Cristie Software development team have applied these technologies to provide advanced file anomaly detection which can take place within the system recovery and replication process. System backups are a vital defence against ransomware and the backup process provides an ideal opportunity to compare file structure between subsequent backup job images. Certain files will be changing regularly throughout normal business operations due of actions being undertaken within their associated applications; however, the process of malicious file encryption will follow one of several detectable patterns. It is these patterns that the Cristie Software anomaly detection technology will seek to identify and provide the earliest possible warning that an attack is in process. Detecting ransomware encryption patterns. To be effective, ransomware must encrypt files, that means it must read file contents from disk and then write encrypted file contents to disk. The way this is done will vary, some ransomware payloads will write to a different file, and then delete the original file. Some will write into the original file, and possibly rename the file after it has been encrypted. Therefore, watching for mass deletes and renames is part of the process, but this is just the tip of the iceberg. The actual encryption process also varies with some payloads encrypting fragments of files while others may encrypt the entire file. File encryption is detected by calculating the entropy of a file. File entropy measures the randomness of the data in a file and is used to determine whether a file contains hidden data or suspicious scripts. The scale of randomness ranges from 0, not random, to 8, totally random, such as an encrypted file. Of course, any backup process that is using encryption and/or data compression will also exhibit these properties including the renaming of files with an extension such as ‘.bak’ plus a subsequent increase in file entropy. Any file anomaly detection algorithm must therefore be able to determine between suspicious and expected behaviours to avoid presenting false positive alerts. Typical ransomware attacks will display characteristics which can be detected by Cristie’s anomaly detection algorithms through comparison against known patterns. The detection process can be run following every system backup. File activity reports and graded alerts are then presented via a security dashboard within the Cristie Virtual Appliance (VA) user interface. Alerts can also be provided by email and recorded in event logs. How quickly can ransomware encrypt your data? A recent article published by technology news platform ZDNET reported that researchers had tested how quickly 10 major ransomware strains could encrypt networks. At the time of writing, they found the fastest form of ransomware to be a malware strain called LockBit, which took a median time of just 5 minutes and 50 seconds to encrypt 100,000 files. In a subsequent test, it took LockBit only 4 minutes and 9 seconds to encrypt 53.83 GB of files across different Windows operating systems and hardware specifications. These figures demonstrate how quickly ransomware can become a major cybersecurity crisis for the victim of an attack. The ability to detect and alert on file activity which may be suspicious means that potential ransomware attacks can be identified in motion and immediate action taken. Determining your safe recovery point following a ransomware attack. Given the speed at which ransomware encryption can spread through an infected network, it is highly likely that system backups will contain malware encrypted files. This scenario would usually require an amount of cyber forensic investigation to determine the ‘last known clean’ copy of backup data that could provide a safe restore point. This can be a timely exercise resulting in extended downtime and potential loss of revenue. Cristie Software’s anomaly detection capability can help reduce this time since backup files can also be scanned for anomalies by comparison against multiple snapshots of previous backups which the VA can reference as part of normal operations. Extending a holistic approach to cybersecurity. Cyber threats come in many forms so for that reason a holistic approach is required to tackle them. Cybersecurity can seem a daunting task with so many loopholes to plug, but with a systematic approach you can achieve a great level of protection for your backup environment. Traditional antivirus software still plays a vital role although by its nature it is always on the back foot since it can only detect malware codes that are already known and present within virus definition files which require constant updates. Advanced techniques that employ machine learning, such as the file anomaly detection included within Cristie Software’s recovery and replication solutions, offer a powerful additional layer
Migración a la nube con modernización automatizada del sistema operativo
\n Cloud migration presents a great opportunity to move applications to a more modern operating system (OS). In some cases, an OS update may be mandatory to meet the minimum supported cloud platform OS image versions. For example, Oracle Cloud currently offers Windows Server 2012 R2 Standard, Datacenter as the earliest available platform image level. \n\n Migrating applications to cloud instances running an up-to-date version of Windows is the right approach from an ongoing support perspective and maximizes the flexibility and reliability of the cloud platform. However, certain legacy applications may have OS version limitations and this needs to be verified to confirm compatibility. \n\n Cristie’s latest CloneManager® release offers the ability to perform a Windows OS upgrade in a sandbox test system within the cloud environment. This test system can then be checked for compatibility before committing the upgraded image to the target system. \n\n Cristie VA Cloud migration with automatic Windows OS updates \n\n CloneManager® provides the option of performing automatic Microsoft Windows OS updates following an initial image migration to the target system. If this option is selected a replication sandbox is created within the target system and a snapshot of the migrated image is taken to obtain a thin-provisioned copy-on-write layer that can accept changes and subsequently be used as a bootable test instance. Once booted, the upgrade procedure is initiated which will initiate the Microsoft OS upgrade process. Any OS licenses required following the upgrade process must then be applied by the user. \n\n When system upgrades have completed, one of two things can happen; the system can be booted into the new operating system for validations to be run against applications on the system, or (if applicable) further upgrades can be run to bring the system up to the latest version. Automatic upgrades can be performed right through to the very latest Windows OS release, saving the labour overheads of a manual intervention. However, any application upgrades will need to be applied manually to the final image if required . \n\n What can I do if my application has legacy OS dependencies? \n\n Legacy applications that are OS-dependent or require a specific environment such as server and network hardware, databases, and storage resources can be problematic during a lift-and-shift cloud migration. Many cloud platforms offer a Bring Your Own Image (BYOI) capability which will allow certain legacy OS versions to run if the underlying platform infrastructure can support it. This will usually require the customer to supply a ‘cloud ready’ image that does not rely on unavailable 3rd party dependencies. If the lift-and-shift migration approach presents too many problems, you may be able to identify pieces of the application to transition to the cloud. This method, known as Application Evolution, allows users to migrate to the cloud in steps, rather than all at once, but this approach may cost more to operate. \n\n Another approach known as Application Re-Architecting breaks down applications and then rebuilds them in a more scalable, modern design. With this scenario you are not completely starting from scratch, but merely eliminating any code that constrains your ability to migrate to a modern OS version, while preserving and potentially enhancing business-relevant functionality in the process. Application re-Architecting is best for legacy applications that are business-critical and provide competitive differentiation, as completely reworking an application for the cloud can be a big undertaking. \n\n In summary \n\n The automatic Windows upgrade feature introduced with the Cristie Software VA 4.5.1 release offers a hybrid lift-and-shift cloud migration environment that greatly simplifies legacy application testing and reduces the time and effort required when Windows OS updates are required to meet cloud platform requirements. CloneManager® and the Cristie VA support cloud migration to many platforms including Oracle Cloud, Azure and AWS for both physical servers, VMs, and containerized applications. Visit the CloneManager® product pages or contact the Cristie Software team for more information on system replication & migration. \n
Cristie Software Guide to Disaster Recovery Planning and System Recovery Processes (Guía de software para la planificación de la recuperación en caso de catástrofe y los procesos de recuperación de sistemas)

El tiempo de inactividad de los sistemas informáticos críticos afectará de algún modo al flujo normal de los procesos empresariales y, en casi todos los casos, supondrá una pérdida de ingresos.


